Android stats v6 for threat report - Sophos
•Download as PPTX, PDF•
0 likes•364 views
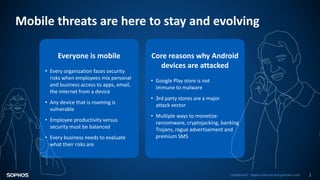
Mobile threats are evolving and growing, especially for Android devices. In 2017, SophosLabs analyzed over 4 million malware samples, the vast majority coming from outside of Google's Play store. While the Play store removed over 700,000 violating apps, 37% of all submitted apps were potentially harmful. Several malware families have been discovered on Google Play by SophosLabs infecting over 280 million users. The number of new Android malware and potentially unwanted apps continues to increase yearly, with ransomware and cryptominers being increasingly common monetization methods employed by cybercriminals.
Report
Share
Report
Share
Recommended
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Symantec Threat Report 2017 - SSLRenewals

The 2017 Internet Threat Report exemplifies various techniques employed by the hackers and fraudsters. The report includes statistics behind the looming dangers such as Malware, Spam, Phishing etc
Read more about encryption
https://www.sslrenewals.com/blog/need-encryption-for-cybersecurity
Malware detection techniques for mobile devices

Mobile devices have become very popular nowadays, due to is portability and high performance, a mobile device became a must device for persons using information and communication technologies. In addition to hardware rapid evolution, mobile applications are also increasing in their complexity and performance to cover most the needs of their users. Both software and hardware design focused on increasing performance and the working hours of a mobile device. Different mobile operating systems are being used today with different platforms and different market shares. Like all information systems, mobile systems are prone to malware attacks. Due to
the personality feature of mobile devices, malware detection is very important and is a must tool in each device to protect private data and mitigate attacks. In
this paper, we will study and analyze different malware detection techniques used for mobile operating systems. We will focus on the to two competing mobile operating systems – Android and iOS. We will asset each technique summarizing its advantages and disadvantages. The aim of the work is to establish a basis for developing a mobile malware detection tool based on user profiling.
MALWARE DETECTION TECHNIQUES FOR MOBILE DEVICES

Mobile devices have become very popular nowadays, due to is portability and high performance, a mobile
device became a must device for persons using information and communication technologies. In addition to
hardware rapid evolution, mobile applications are also increasing in their complexity and performance to
cover most the needs of their users. Both software and hardware design focused on increasing performance
and the working hours of a mobile device. Different mobile operating systems are being used today with
different platforms and different market shares. Like all information systems, mobile systems are prone to
malware attacks. Due to the personality feature of mobile devices, malware detection is very important and
is a must tool in each device to protect private data and mitigate attacks. In this paper, we will study and
analyze different malware detection techniques used for mobile operating systems. We will focus on the to
two competing mobile operating systems – Android and iOS. We will asset each technique summarizing its
advantages and disadvantages. The aim of the work is to establish a basis for developing a mobile malware
detection tool based on user profiling.
Recommended
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Symantec Threat Report 2017 - SSLRenewals

The 2017 Internet Threat Report exemplifies various techniques employed by the hackers and fraudsters. The report includes statistics behind the looming dangers such as Malware, Spam, Phishing etc
Read more about encryption
https://www.sslrenewals.com/blog/need-encryption-for-cybersecurity
Malware detection techniques for mobile devices

Mobile devices have become very popular nowadays, due to is portability and high performance, a mobile device became a must device for persons using information and communication technologies. In addition to hardware rapid evolution, mobile applications are also increasing in their complexity and performance to cover most the needs of their users. Both software and hardware design focused on increasing performance and the working hours of a mobile device. Different mobile operating systems are being used today with different platforms and different market shares. Like all information systems, mobile systems are prone to malware attacks. Due to
the personality feature of mobile devices, malware detection is very important and is a must tool in each device to protect private data and mitigate attacks. In
this paper, we will study and analyze different malware detection techniques used for mobile operating systems. We will focus on the to two competing mobile operating systems – Android and iOS. We will asset each technique summarizing its advantages and disadvantages. The aim of the work is to establish a basis for developing a mobile malware detection tool based on user profiling.
MALWARE DETECTION TECHNIQUES FOR MOBILE DEVICES

Mobile devices have become very popular nowadays, due to is portability and high performance, a mobile
device became a must device for persons using information and communication technologies. In addition to
hardware rapid evolution, mobile applications are also increasing in their complexity and performance to
cover most the needs of their users. Both software and hardware design focused on increasing performance
and the working hours of a mobile device. Different mobile operating systems are being used today with
different platforms and different market shares. Like all information systems, mobile systems are prone to
malware attacks. Due to the personality feature of mobile devices, malware detection is very important and
is a must tool in each device to protect private data and mitigate attacks. In this paper, we will study and
analyze different malware detection techniques used for mobile operating systems. We will focus on the to
two competing mobile operating systems – Android and iOS. We will asset each technique summarizing its
advantages and disadvantages. The aim of the work is to establish a basis for developing a mobile malware
detection tool based on user profiling.
State of Application Security Vol. 4

Arxan Technologies inforgraphic on the current state of application security.
Symantec intelligence report august 2015

August was a big month for zero-day vulnerabilities, in which a total of 11 were reported. This is by far the largest number disclosed in a given month to-date.
Six of these zero-day vulnerabilities impact industrial control systems, devices used in industrial sectors and critical infrastructures, across five vendors. The vulnerabilities cover a wide range of possible attacks, including remote code execution and denial of service attacks.
Two further zero-day vulnerabilities were discovered in the Apple OS X operating system. When used in tandem, these two vulnerabilities can cause memory corruption in the OS X kernel and gain the attacker escalated privileges on the compromised computer.
These vulnerabilities come on the heels of a new OS X threat called OSX.Sudoprint. This threat exploits a local privilege escalation vulnerability in the OS X operating system, which was patched by Apple at the beginning of August. This threat comprised over 77 percent of the OS X threats we saw on OS X endpoints this month.
Istr number 23 internet security threat repor 2018 symantec

Istr number 23 internet security threat repor 2018 symantec
How to Protect Mobile Banking Users from BankBot

BankBot is Android-targeting malware using fake overlay screens to mimic existing banking apps to fool users and steal credentials. The newest BankBot variants target over 150 legitimate apps from banks based in 27 different countries. BankBot has evolved to intelligently target users based on geography, apps, and advanced Two-Factor Authentication in order to mislead users.
2013 Threat Report

Cyberthreats broke new ground with mobile devices, while reaching deeper into social media. Online criminals also stepped up attacks via email, web and other traditional vectors.
Infographic - Three steps to stopping advanced email threats

Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Symantec Internet Security Threat Report Volume 2015

Symantec reveals that nearly 1 million or around one-third of all Android apps are actually malware | Full Article:
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Malware and the Cost of Inactivity

Breaches happen every day. The culprit? Malware. It’s no longer a question of “if” you’ll be breached, but “when”. Don’t become another statistic. Protect your organization today. Learn more here >> http://cs.co/ampvodvepg
Your Data Is Under Siege: Fortify Your Endpoints

1 in 5 businesses suffered a security breach in 2016. See the trends and learn how you can stop malware in its tracks.
McAFEE LABS THREATS REPORT - Fourth Quarter 2013

• Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
More Related Content
What's hot
State of Application Security Vol. 4

Arxan Technologies inforgraphic on the current state of application security.
Symantec intelligence report august 2015

August was a big month for zero-day vulnerabilities, in which a total of 11 were reported. This is by far the largest number disclosed in a given month to-date.
Six of these zero-day vulnerabilities impact industrial control systems, devices used in industrial sectors and critical infrastructures, across five vendors. The vulnerabilities cover a wide range of possible attacks, including remote code execution and denial of service attacks.
Two further zero-day vulnerabilities were discovered in the Apple OS X operating system. When used in tandem, these two vulnerabilities can cause memory corruption in the OS X kernel and gain the attacker escalated privileges on the compromised computer.
These vulnerabilities come on the heels of a new OS X threat called OSX.Sudoprint. This threat exploits a local privilege escalation vulnerability in the OS X operating system, which was patched by Apple at the beginning of August. This threat comprised over 77 percent of the OS X threats we saw on OS X endpoints this month.
Istr number 23 internet security threat repor 2018 symantec

Istr number 23 internet security threat repor 2018 symantec
How to Protect Mobile Banking Users from BankBot

BankBot is Android-targeting malware using fake overlay screens to mimic existing banking apps to fool users and steal credentials. The newest BankBot variants target over 150 legitimate apps from banks based in 27 different countries. BankBot has evolved to intelligently target users based on geography, apps, and advanced Two-Factor Authentication in order to mislead users.
2013 Threat Report

Cyberthreats broke new ground with mobile devices, while reaching deeper into social media. Online criminals also stepped up attacks via email, web and other traditional vectors.
Infographic - Three steps to stopping advanced email threats

Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Symantec Internet Security Threat Report Volume 2015

Symantec reveals that nearly 1 million or around one-third of all Android apps are actually malware | Full Article:
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Malware and the Cost of Inactivity

Breaches happen every day. The culprit? Malware. It’s no longer a question of “if” you’ll be breached, but “when”. Don’t become another statistic. Protect your organization today. Learn more here >> http://cs.co/ampvodvepg
Your Data Is Under Siege: Fortify Your Endpoints

1 in 5 businesses suffered a security breach in 2016. See the trends and learn how you can stop malware in its tracks.
McAFEE LABS THREATS REPORT - Fourth Quarter 2013

• Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
What's hot (20)
Istr number 23 internet security threat repor 2018 symantec

Istr number 23 internet security threat repor 2018 symantec
Infographic - Three steps to stopping advanced email threats

Infographic - Three steps to stopping advanced email threats
Symantec Internet Security Threat Report Volume 2015

Symantec Internet Security Threat Report Volume 2015
Verizon Data Breach Investigations Report (DBIR) 2017

Verizon Data Breach Investigations Report (DBIR) 2017
Similar to Android stats v6 for threat report - Sophos
Internet Security Threat Report (ISTR) Government

Internet Security Threat Report (ISTR) details how simple tactics and innovative cyber criminals led to unprecedented outcomes in global threat activity. Credit - Symantec
About SSL Security -
https://www.sslrenewals.com
F-Secure Mobile Threat Report Quarter 1 2012

Since its debut, Android has quickly claimed significant market share in the mobile market. Unfortunately, such popularity (amongst other factors) makes Android a lucrative target for malware authors. New families and variants of malware keep cropping up each quarter, and this trend shows no sign of slowing down. In Q1 2011, 10 new families and variants were discovered. A year later, this number has nearly quadrupled with 37 new
families and variants discovered in Q1 2012 alone.
Protect Your Enterprise - Check Point SandBlast Mobile

Prezentace ze semináře Check Point CPX Highlights
Praha, 13.6.2017
Symantec (ISTR) Internet Security Threat Report Volume 22

Symantec’s Internet Security Threat Report (ISTR) demonstrates how simple tactics and innovative cyber criminals led to unprecedented outcomes in global threat activity.
Mobile Ad Fraud Deep Dive With AppsFlyer

Why working with mobile fraud is so important? How to deal with that challenge? Hands on approach to fight with mobile ad fradu.
AndRadar: Fast Discovery of Android Applications in Alternative Markets

Compared to traditional desktop software, Android applica- tions are delivered through software repositories, commonly known as application markets. Other mobile platforms, such as Apple iOS and BlackBerry OS also use the marketplace model, but what is unique to Android is the existence of a plethora of alternative application markets. This complicates the task of detecting and tracking Android malware. Identifying a malicious application in one particular market is simply not enough, as many instances of this application may exist in other markets. To quantify this phenomenon, we exhaustively crawled 8 markets between June and November 2013. Our findings indicate that alternative markets host a large number of ad-aggressive apps, a non-negligible amount of mal- ware, and some markets even allow authors to publish known malicious apps without prompt action.
Motivated by these findings, we present AndRadar, a framework for dis- covering multiple instances of a malicious Android application in a set of alternative application markets. AndRadar scans a set of markets in parallel to discover similar applications. Each lookup takes no more than a few seconds, regardless of the size of the marketplace. Moreover, it is modular, and new markets can be transparently added once the search and download URLs are known.
Using AndRadar we are able to achieve three goals. First, we can discover malicious applications in alternative markets, second, we can expose app distribution strategies used by malware developers, and third, we can moni- tor how different markets react to new malware. During a three-month eval- uation period, AndRadar tracked over 20,000 apps and recorded more than 1,500 app deletions in 16 markets. Nearly 8% of those deletions were related to apps that were hopping from market to market. The most established markets were able to react and delete new malware within tens of days from the malicious app publication date while other markets did not react at all.
Adaptive Mobile Malware Detection Model Based on CBR

Today, the mobile phones can maintain lots of sensitive information. With the increasing capabilities of such phones, more and more malicious software malware targeting these devices have emerged. However there are many mobile malware detection techniques, they used specified classifiers on selected features to get their best accuracy. Thus, an adaptive malware detection approach is required to effectively detect the concept drift of mobile malware and maintain the accuracy. An adaptive malware detection approach is proposed based on case based reasoning technique in this paper to handle the concept drift issue in mobile malware detection. To demonstrate the design decision of our approach, several experiments are conducted. Large features set with 1,065 features from 10 different categories are used in evaluation. The evaluation includes both accuracy and efficiency of the model. The experimental results prove that our approach achieves acceptable performance and accuracy for the malware detection. Kyaw Soe Moe | Mya Mya Thwe "Adaptive Mobile Malware Detection Model Based on CBR" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-3 | Issue-6 , October 2019, URL: https://www.ijtsrd.com/papers/ijtsrd28088.pdf Paper URL: https://www.ijtsrd.com/computer-science/computer-security/28088/adaptive-mobile-malware-detection-model-based-on-cbr/kyaw-soe-moe
A Systematic Review of Android Malware Detection Techniques

Malware detection is a significant key to Android application security. Malwares threat to Android users is increasing day by day. End users need security because they use mobile device to communicate information. Therefore, developing malware detection and control technology should be a priority. This research has extensively explored various state of the art techniques and mechanisms to detect malwares in Android applications by systematic literature review. It categorized the current researches into static, dynamic and hybrid approaches. This research work identifies the limitation and strength current research work. According to the restrictions of current malware detection technologies, it can conclude that detection technologies that use statistical analysis consume more time, energy and resources as compare to machine learning techniques. The results obtained from this research work reinforce the assertion that detection approaches designed for Android malware do not produce 100% efficient detection accuracy.
Android-manifest extraction and labeling method for malware compilation and d...

Malware is a nuisance for smartphone users. The impact is detrimental to smartphone users if the smartphone is infected by malware. Malware identification is not an easy process for ordinary users due to its deeply concealed dangers in application package kit (APK) files available in the Android Play Store. In this paper, the challenges of creating malware datasets are discussed. Long before a malware classification process and model can be built, the need for datasets with representative features for most types of malwares has to be addressed systematically. Only after a quality data set is available can a quality classification model be obtained using machine learning (ML) or deep learning (DL) algorithms. The entire malware classification process is a full pipeline process and sub processes. The authors purposefully focus on the process of building quality malware datasets, not on ML itself, because implementing ML requires another effort after the reliable dataset is fully built. The overall step in creating the malware dataset starts with the extraction of the Android Manifest from the APK file set and ends with the labeling method for all the extracted APK files. The key contribution of this paper is on how to generate datasets systematically from any APK file.
Securing Mobile Apps - Appfest Version

The goal of this is to raise awareness about application security by
identifying some of the most critical risks facing organizations.
Mobile Security

You may be surprised that nearly 2.2 billion smartphones and tablets will be sold to end users in 2014. With the number of smartphones and tablets on the increase and adoption of enterprise mobile computing on the rise, security breaches, malware attacks and exploitation of application vulnerability on mobile devices are maturing. By 2017, Gartner predicts that the focus of endpoint breaches will shift to tablets and smartphones. That indicates how important the subject of Mobile Security is and going to be in the future.
Similar to Android stats v6 for threat report - Sophos (20)
Protect Your Enterprise - Check Point SandBlast Mobile

Protect Your Enterprise - Check Point SandBlast Mobile
Symantec (ISTR) Internet Security Threat Report Volume 22

Symantec (ISTR) Internet Security Threat Report Volume 22
AndRadar: Fast Discovery of Android Applications in Alternative Markets

AndRadar: Fast Discovery of Android Applications in Alternative Markets
Adaptive Mobile Malware Detection Model Based on CBR

Adaptive Mobile Malware Detection Model Based on CBR
A Systematic Review of Android Malware Detection Techniques

A Systematic Review of Android Malware Detection Techniques
Android-manifest extraction and labeling method for malware compilation and d...

Android-manifest extraction and labeling method for malware compilation and d...
More from ITSitio.com
ITSitio.com - Projecto Ninja 

Proyecto Ninja es una nueva sección de nuestro portal donde ofreceremos a los Canales IT de LATAM la oportunidad de validar sus habilidades sobre diversos verticales, soluciones o productos de marcas destacadas de la Industria para que puedan obtener certificados y medallas que avalen sus conocimentos y que luego podrán ser compartidas para fortalecer y potenciar su reputación profesional en el mercado.
Más info: www.itsitio.com/nosotros
Presentacion Consultora D Alessio Irol

Presentacion compartida por Nora D Alessio en el #liveevent de ITSitio.com/live realizado el martes 28/04/2020
Proyecto Ley de Economia del Conocimiento modificado 

Este es el texto del proyecto de reforma de la Ley de Economía del Conocimiento que el Ministerio de Producción presentó este mediodía en la Cámara de Diputados
Technology, Media, and Telecommunications Predictions 2020

Informe de Deloitte Insights
Copyright © 2019 Deloitte Development LLC. All rights reserved. Member of Deloitte Touche Tohmatsu Limited
Cisco Visual Networking Index: Forecast and Trends, 2017–2022

Cisco Visual Networking
Index: Forecast and Trends,
2017–2022
#ITSitioMexico - Presentacion Desayuno CDMX 

Presentacion compartida en el desayuno con empresas en CDMX el 11-12-2018
Desayuno ITSitio.com Colombia 2018 

Presentacion de ITSitio.com realizada en Bogota en el evento conjunto con Portavoz.Co el 16-11-2018
Presentación de IDC Evento SOPHOS See The Future Buenos Aires Sep2018

Presentación de IDC Evento SOPHOS See The Future Buenos Aires Sep2018
NVdia Argentina Press Deck - Mayo 2018

Presentacion de la conferencia de prensa en Argentina de David Bullit de NViia
Logitech - Presentacion de Video Collaboration

Introduccion a las soluciones de video colaboración de Logitech - Año 2018
AMD Latam Press Tour Buenos Aires Mayo 2018

Presentación de Don Woligroski, Desktop Processor Business Development and Technical Marketing Manager, sobre AMD Ryzen 2018
#ITSitioEnRSA - Presentacion de Jeef Reed de Cisco 

Presentacion de Jeff Reed de Cisco dentro del RSA Conference 2018
Martin Tetaz - Economía 2018

Presentacion compartida por el economista Martin Tetaz en el evento de Ceven Connect en Marzo 2018
Desayuno marketing 3.0

Presentacion de Matias Balaclav en el desayuno de gerentes de marketing de distribuidores IT Argentina
Desayuno mayoristas IT 

Presentacion de Sebastian Magnarelli en el desayuno de Gerentes de Marketing de Distribuidores de Argentina
More from ITSitio.com (20)
Proyecto Ley de Economia del Conocimiento modificado 

Proyecto Ley de Economia del Conocimiento modificado
Technology, Media, and Telecommunications Predictions 2020

Technology, Media, and Telecommunications Predictions 2020
Cisco Visual Networking Index: Forecast and Trends, 2017–2022

Cisco Visual Networking Index: Forecast and Trends, 2017–2022
Presentación de IDC Evento SOPHOS See The Future Buenos Aires Sep2018

Presentación de IDC Evento SOPHOS See The Future Buenos Aires Sep2018
#ITSitioEnRSA - Presentacion de Jeef Reed de Cisco 

#ITSitioEnRSA - Presentacion de Jeef Reed de Cisco
Recently uploaded
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Recently uploaded (20)
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Android stats v6 for threat report - Sophos
- 1. Confidential - Sophos internal and partners only 1 Mobile threats are here to stay and evolving Everyone is mobile • Every organization faces security risks when employees mix personal and business access to apps, email, the internet from a device • Any device that is roaming is vulnerable • Employee productivity versus security must be balanced • Every business needs to evaluate what their risks are Core reasons why Android devices are attacked • Google Play store is not immune to malware • 3rd party stores are a major attack vector • Multiple ways to monetize: ransomware, cryptojacking, banking Trojans, rogue advertisement and premium SMS
- 2. Mobile Threat Data Points Confidential - Sophos internal and partners only 2 iOS THREATS <10 ANDROID THREATS 4 Million+ VS. 2017 SophosLabs Analyzation Vast majority of 4 Million Malware Samples came from outside Google’s walled garden In 2017, Google Play reported 35 different threat families Google took down 700,000 packages violating Google Play policies A continuing trend: 47 threat families so far 6 of 37 malware families discovered at SophosLabs
- 3. Android apps removed from Google Play 3 37% potentially harmful applications removed from Google Play in 2017 – SophosLabs Total apps submitted to Google Play in 2017: 2,144,733 Free Apps: 2,012,893 Paid Apps: 131,840 37% - Removed from Google Play app store Free Apps: 681,241 Paid Apps: 109,897 Left in Google Play: Free Apps: 1,331,652 Paid Apps: 21,943 14.2 billion installs Built by 184,852 developers
- 4. Malware on Google Play found by SophosLabs 4 Cumulative number of malicious apps on Google Play from July 2017 till September 2018 0 2000 1800 1600 1400 1200 1000 800 600 200 400 (number of unique applications) July 2017 January 2018 September 2018 SonicSpy CPUMiner ExpensiveWall BankBot AsiaHitGroup Tizi LightsOut MyEtherWallet 47 New Malware Families 280 Million Downloads 6 out of 37 Malware Families Discovered in 2018 Were Discovered by Sophos
- 5. Android Malware Growth, 2015-2018 5 Annual rate of new Android malware and PUA collected by SophosLabs 0 500,000 1,000,000 1,500,000 2,000,000 2,500,000 3,000,000 3,500,000 4,000,000 4,500,000 2012 2013 2014 2015 2016 2017 2018 Malware PUA Source: SophosLabs, 2017 100% increase in new malware sightings expected, as compared to 2015 projected
- 6. Android Ransomware: No sign of going away 6 0 50,000 100,000 150,000 200,000 250,000 300,000 350,000 400,000 450,000 500,000 2013 2014 2015 2016 2017 2018 Jan- Aug New Android ransomware samples collected by SophosLabs, per year SophosLabs: Cryptojacking is replacing ransomware as a preferred monetization route. But ransomware shows no sign of going away
- 7. Cryptominers: On The Rise Confidential - Sophos internal and partners only 7 SophosLabs: • Discovered 25 cryptomining apps on Google Play disguised as games and educational applications on September 24, installed more than 120,000 times LINK • Observed more than 20,000 different variants of the Loapi cryptomining malware in the second half of 2017 function startMiner(n, id) { if (isAlreadyStarted) return; isAlreadyStarted=true; var miner = new CoinHive.Anonymous(id, { threads: n-1, autoThreads: true, throttle: 0.5 }); miner.start(); } Generates cryptocurrency for cybercriminals
- 8. Resources Confidential - Sophos internal and partners only 8 SophosLabs Uncut “Android” o Research straight from SophosLabs Naked Security News o Industry security news SophosLabs on Twitter o Follow for breaking news and updates Sophos Mobile Security o Technology innovations and protection
Editor's Notes
- https://news.sophos.com/en-us/2018/06/18/what-makes-a-mobile-threat-researcher-tick/ SS: #3: the line below is unnecessary – the graph already reflects that, too much text
- In 2017, the iOS threats SophosLabs analyzed numbered in the single digits. In comparison, SophosLabs processed more than 4 million malicious Android samples, many of them found in the wild The vast majority of the 4 million Android malware samples SophosLabs classified last year came from outside Google’s walled garden Even on Google Play, 35 different threat families were reported in 2017, and Google itself took down 700,000 packages for violating Google Play policies That trend is continuing – 47 threat families have been seen on Google Play 6 out of 37 malware familes discovered in 2018 were by SophosLabs
- Ransomware was rampant on mobile devices even before it became a plague on desktop and laptop computers, although in the early days it didn’t scramble your files, but just tried to freeze you out of your phone. More recently, file-scrambling malware has become more and more widespread on Android, though mobile ransomware doesn’t yet seem to be causing the same pain that it has on Windows computers. Typical ransomware on Android devices is either full-blown crypto ransomware that encrypts files on your device or lock screen ransomware that “locks” your device and then asks you for money to unlock it.
- Mobile cryptojacking is when crooks try to “borrow” your phone’s processor to mine for cryptocurrency SophosLabs saw more than 20,000 different variants of the Loapi cryptomining malware in the second half of 2017 In early 2018, SophosLabs saw Coinhive-based miners added to tampered copies of popular apps, like Netflix and Instagram, as well as soccer apps and other apps based on web frameworks such as Cordova Most of these were distributed through third party stores, but SophosLabs did identify a number on Google Play
