[Infographic] CYREN Q3 2015 Cyber Threat Report
•
1 like•399 views
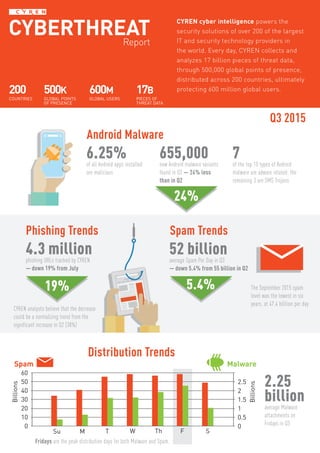
CYREN collects and analyzes 17 billion pieces of threat data daily through 500,000 global points of presence across 200 countries to protect 600 million global users. The report found that 6.25% of all Android apps installed are malicious and 655,000 new Android malware variants were discovered in Q3, with most being adware. Spam levels decreased 5.4% from the previous quarter to an average of 52 billion per day, with Fridays seeing the highest volume of both spam and malware.
Report
Share
Report
Share
Download to read offline
Recommended
State of cybersecurity report 2020- Post Covid 19

How strong is your cyber response? Post COVID-19 has changed how we work, shop, and interact. Lockdowns accelerated the rise of remote work, which was already gaining traction within many industries.
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Zimperium's presentation at Deutsche Telekom's Operator Partner Summit at Hub:Raum in Berlin, Germany.
Mobile Protect Pro - Powered by Zimperium

Zimperium's Mobile Protect Pro presentation at Deutsche Telekom's Magenta Security Summit in Frankfurt, Germany.
The state of mobile app security 

This infographic talks about the latest in mobile app security, the challenges and the best practices to tackle them by building secure mobile apps.
Istr number 23 internet security threat repor 2018 symantec

Istr number 23 internet security threat repor 2018 symantec
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Recommended
State of cybersecurity report 2020- Post Covid 19

How strong is your cyber response? Post COVID-19 has changed how we work, shop, and interact. Lockdowns accelerated the rise of remote work, which was already gaining traction within many industries.
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Zimperium's presentation at Deutsche Telekom's Operator Partner Summit at Hub:Raum in Berlin, Germany.
Mobile Protect Pro - Powered by Zimperium

Zimperium's Mobile Protect Pro presentation at Deutsche Telekom's Magenta Security Summit in Frankfurt, Germany.
The state of mobile app security 

This infographic talks about the latest in mobile app security, the challenges and the best practices to tackle them by building secure mobile apps.
Istr number 23 internet security threat repor 2018 symantec

Istr number 23 internet security threat repor 2018 symantec
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Let's hack your mobile device. Yes we can. And many other do.

Tommi Kallberg, Mobile security engineer, Checkpoint / Opticom https://dssitsec.eu
Symantec Internet Security Threat Report 2014 - Volume 19

The 2014 Internet Security Threat Report gives an overview of global threat activity for the past year based on data from Symantec’s Global Intelligence Network.
Digital Threat Landscape

This brief presentation gives you a quick overview on how the Cyber Threat Landscape is shaping up in 2017 for individuals and business owners alike. It puts forth some important trends and predictions.
State of Application Security Vol. 4

Arxan Technologies inforgraphic on the current state of application security.
Making Sense of Cybersecurity for Small Business

Attacks against small businesses are growing, yet most have no cyber response or crisis plan to deal with the aftermath if they are hacked. Learn about the risks.
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Private Sector, by John Bordwine
Cybersecurity Webinar for Small Business

In March of 2020 I presented a cybersecurity webinar to help educate businesses on the latest threats on the Internet today. This slide deck provides a visual overview of the 50 minute webinar.
Tackling the maze ransomware attack with security testing

Infiltration by the Maze malware is a two-way attack – a data breach and a ransomware attack. Read how security testing can help you tackle with the malicious ransomware attack.
13 Ransomware Statistics That Will Make You Rethink Data Protection 

Worksighted has partnered with Datto to bring you 13 Ransomware Statistics That Will Make You Rethink Data Protection
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Mobile Security

You may be surprised that nearly 2.2 billion smartphones and tablets will be sold to end users in 2014. With the number of smartphones and tablets on the increase and adoption of enterprise mobile computing on the rise, security breaches, malware attacks and exploitation of application vulnerability on mobile devices are maturing. By 2017, Gartner predicts that the focus of endpoint breaches will shift to tablets and smartphones. That indicates how important the subject of Mobile Security is and going to be in the future.
Top 15 security predictions for 2017

Here are some of the best guesses about what we will see in 2017 from several dozen vendors and analysts. There are many more than 15 predictions out there, of course, but these are the ones we heard most frequently.
Cyberattacks and Enterprise Risk Management

Join us as we dissect recent cyberattacks, examine vulnerabilities and go in-depth on risk management.
Vizru GDPR compliance framework

Vizru platform’s Watchdog is a workflow-based process intelligence that continuously monitors against a set of GDPR criteria and enforces conformity to those rules. It alerts and reports compliance anomalies and stops errant processes.
Infographic: The crippled state of network security

Data breaches have become the norm. Find out the alarming statistics around this trend.
Online financial fraud infographic

Hacking banks is difficult..which is why hackers are targeting customers...
Webinar: Insights from CYREN's 2015-Q3 Cyber Threat Report

Presentation Material of the Live Webinar Event on November 4, 2015: Preview the Findings from CYREN's Newest Cyber Threats Report
More Related Content
What's hot
Let's hack your mobile device. Yes we can. And many other do.

Tommi Kallberg, Mobile security engineer, Checkpoint / Opticom https://dssitsec.eu
Symantec Internet Security Threat Report 2014 - Volume 19

The 2014 Internet Security Threat Report gives an overview of global threat activity for the past year based on data from Symantec’s Global Intelligence Network.
Digital Threat Landscape

This brief presentation gives you a quick overview on how the Cyber Threat Landscape is shaping up in 2017 for individuals and business owners alike. It puts forth some important trends and predictions.
State of Application Security Vol. 4

Arxan Technologies inforgraphic on the current state of application security.
Making Sense of Cybersecurity for Small Business

Attacks against small businesses are growing, yet most have no cyber response or crisis plan to deal with the aftermath if they are hacked. Learn about the risks.
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Private Sector, by John Bordwine
Cybersecurity Webinar for Small Business

In March of 2020 I presented a cybersecurity webinar to help educate businesses on the latest threats on the Internet today. This slide deck provides a visual overview of the 50 minute webinar.
Tackling the maze ransomware attack with security testing

Infiltration by the Maze malware is a two-way attack – a data breach and a ransomware attack. Read how security testing can help you tackle with the malicious ransomware attack.
13 Ransomware Statistics That Will Make You Rethink Data Protection 

Worksighted has partnered with Datto to bring you 13 Ransomware Statistics That Will Make You Rethink Data Protection
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Mobile Security

You may be surprised that nearly 2.2 billion smartphones and tablets will be sold to end users in 2014. With the number of smartphones and tablets on the increase and adoption of enterprise mobile computing on the rise, security breaches, malware attacks and exploitation of application vulnerability on mobile devices are maturing. By 2017, Gartner predicts that the focus of endpoint breaches will shift to tablets and smartphones. That indicates how important the subject of Mobile Security is and going to be in the future.
Top 15 security predictions for 2017

Here are some of the best guesses about what we will see in 2017 from several dozen vendors and analysts. There are many more than 15 predictions out there, of course, but these are the ones we heard most frequently.
Cyberattacks and Enterprise Risk Management

Join us as we dissect recent cyberattacks, examine vulnerabilities and go in-depth on risk management.
Vizru GDPR compliance framework

Vizru platform’s Watchdog is a workflow-based process intelligence that continuously monitors against a set of GDPR criteria and enforces conformity to those rules. It alerts and reports compliance anomalies and stops errant processes.
Infographic: The crippled state of network security

Data breaches have become the norm. Find out the alarming statistics around this trend.
Online financial fraud infographic

Hacking banks is difficult..which is why hackers are targeting customers...
What's hot (19)
Let's hack your mobile device. Yes we can. And many other do.

Let's hack your mobile device. Yes we can. And many other do.
Symantec Internet Security Threat Report 2014 - Volume 19

Symantec Internet Security Threat Report 2014 - Volume 19
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...
Tackling the maze ransomware attack with security testing

Tackling the maze ransomware attack with security testing
13 Ransomware Statistics That Will Make You Rethink Data Protection 

13 Ransomware Statistics That Will Make You Rethink Data Protection
Infographic: The crippled state of network security

Infographic: The crippled state of network security
Viewers also liked
Webinar: Insights from CYREN's 2015-Q3 Cyber Threat Report

Presentation Material of the Live Webinar Event on November 4, 2015: Preview the Findings from CYREN's Newest Cyber Threats Report
Intel Cyber Security Briefing at the Cyberstrat14 Security Conference in Hels...

Intel® Cyber Security Briefing:
Trends, Challenges, and Leadership Opportunities. Matthew Rosenquist, Cyber Security Strategist, Intel Corp
In the digital world, the opportunities and risks coexist. To achieve and maintain a balanced Cyber Strategy by implementing a model of "connected security" has become a new imperative in business and society. Management can drive "cyber" leadership to create value and gain a competitive advantage in the digital world.
2016 Cyber Threat Defense Report

Security is top-of-mind for all IT pros. Here's a look at the biggest expectations & obstacles facing the industry.
Learn more: https://www.citrix.com/
Nr 7, a teoria e a prática

Abordagem lógica e sistemática da NR7: o que diz a teoria e o que acontece na prática.
PPRA - PROGRAMA DE PREVENÇÃO DE RISCOS AMBIENTAIS

Disponibilizo aqui o PPRA de uma empresa no ramo alimentício.
Todos os dados são fictícios criado e elaborado por mim, autora, porém toda a estrutura foi baseada de um PPRA validado.
Para elaborá-lo tive que ter em mãos o livro de NRs, conhece-lo e estudar sobre cada risco e informações. Deve ser feito minuciosamente, tendo que voltar à página anterior para coletar alguns dados importantes.
É um trabalho cansativo, mas se bem feito no final dá um certo orgulho!
Qualquer dúvida, estou a disposição. Na página ou através do e-mail contido no corpo do documento word.
Viewers also liked (18)
Webinar: Insights from CYREN's 2015-Q3 Cyber Threat Report

Webinar: Insights from CYREN's 2015-Q3 Cyber Threat Report
Intel Cyber Security Briefing at the Cyberstrat14 Security Conference in Hels...

Intel Cyber Security Briefing at the Cyberstrat14 Security Conference in Hels...
PCMSO - Programa de Controle Médico de Saúde Ocupacional

PCMSO - Programa de Controle Médico de Saúde Ocupacional
Similar to [Infographic] CYREN Q3 2015 Cyber Threat Report
Symantec Intelligence Report - Oct 2015

Explore this PDF to know Symantec intelligence report for OCT 2015 from Symantec Global Intelligence Network.
Enjoy this report and feel free to contact us with any comments or feedback.
Important points you have to note down from this report:
- The number of new malware
- Spam have been increasing over the last few month
- Finance, Insurance, & Real Estate sector was the most targeted sector in OCT month
2016 Symantec Internet Security Threat Report

2016 Symantec Internet Security Threat Report to dive into big data of website security.
Symantec Internet Security Threat Report Volume 2015

Symantec reveals that nearly 1 million or around one-third of all Android apps are actually malware | Full Article:
Cyber security olive green mint ppt .pdf

All about cyber security. What is cyber security. Terrifying stats. Pros and cons of using internet.
Symantec Intelligence Report November 2014

There was a significant jump in emails containing malicious URLs during the month of November, where 41 percent of emailborne malware contained a link to a malicious or compromised website. The last time we saw this level of activity was back in August of 2013. Since then, URL malware had been present in 3 to 16 percent of malicious emails each month, until this recent surge.
We have reason to believe that the Cutwail botnet is responsible for some of this increase. However, this botnet only makes up 3.7 percent of total botnet activity tracked in November. Kelihos and Gamut appear to be in the number one and two positions, comprising 19.2 and 18.8 percent respectively.
The topics in the campaigns we’ve seen so far include fake telecom billing notices, as well as fax and voicemail spam, and government levied fines. The URLs in the first two campaigns appear to be downloaders that will install further malware on a compromised computer, while the third campaign leads to fake captcha sites hosting crypto-ransomware.
Ransomware as a whole continues to decline as the year progresses. However, the amount of crypto-ransomware seen continues to comprise a larger portion of this type of malware. This particularly aggressive form of ransomware made up 38 percent of all ransomware in the month of November.
Cosmin Vilcu - Sonicwal - prezentare - Cyber Security Trends 2020

Cosmin Vilcu este expert în soluții de securitate IT, iar în prezent ocupă funcția de Regional Senior Sales Manager for Eastern Europe & CIS la SonicWall. Cosmin a pus bazele echipei SonicWall în România la începutul anului 2016. Întreaga experiență a fost construită în domeniul tehnologic, Cosmin lucrând în decursul anilor pentru companii precum Kaspersky, Omnilogic, Romtelecom, GTS Telecom, Telemobil sau Romservice. Este certificat SonicWall Network Security.
Symantec Cyber Security Intelligence Report

As reported in the ISTR Volume 19, 2013 saw a 500 percent increase in ransomware in the latter part of the year. Overall ransomware levels remained high through March 2014, and then slowly started to decline, in part due to the disruption of the GameOver Zeus botnet back in late May.
In contrast, crypto-style ransomware has seen a 700 percent-plus increase. These file-encrypting versions of ransomware began the year comprising 1.2 percent of all ransomware detec¬tions, but now make up 31 percent at the end of August. One variant known as Trojan.Cryptodefense began to appear in large numbers in early June. By the end of July, it made up 77 percent of all crypto-style ransomware for the year to date. This follows predictions in the ISTR saying this type of malware would become more common in 2014.
Over 31.5 million identities were reported exposed in August, from 12 incidents. The jump in exposed identities is due to a large breach in South Korea, comprising 27 million identities. In the last 12 months 53 percent of data breaches were caused by hacking and 21 percent were accidentally made public.
The average number of spear-phishing emails blocked each day for August was 20, compared with 54 in July and 88 in June. This is below the year-to-date average of 86, which is slightly higher than the daily average of 84 for all if 2013.
The most frequently used malicious file types in these email-based targeted attacks were .exe and .doc file types, with .exe attachments coming out on top this month at 31.8 percent. 29 percent of spear phishing emails were sent to Manufacturing, returning it to the top of the industries targeted.
One in 1,587 emails was identified as a phishing attempt, compared with one in 1,298 for July and one in 496 in June. While at first glance this looks like a big drop, it is not indica¬tive of a wider trend just yet, resulting in only a 0.01 percentage point decrease in the overall phishing rate.
We hope that you enjoy this month’s report and feel free to contact us with any comments or feedback.
Avast Q1 Security Report 2015

The Avast Threat Report provides an overview of global threat activity for Q1 2015.
Avast malware researchers and Avast customers work 24/7 to protect each other. Avast protects 230 million people worldwide in more than 186 different countries — we are present in more countries than McDonalds and protect more people than any other antivirus security provider.
The Q1 security report looks at the state of cyberthreats as it relates to Wi-Fi, PC threats, mobile threats, and the steady evolution of ransomware.
Symantec (ISTR) Internet Security Threat Report Volume 22

Symantec’s Internet Security Threat Report (ISTR) demonstrates how simple tactics and innovative cyber criminals led to unprecedented outcomes in global threat activity.
Symantec Website Security Threat Report 2014 - RapidSSLOnline

Symantec Website Security Threat Report 2014!
Internet Security Threat Report (ISTR) Government

Internet Security Threat Report (ISTR) details how simple tactics and innovative cyber criminals led to unprecedented outcomes in global threat activity. Credit - Symantec
About SSL Security -
https://www.sslrenewals.com
"Latest Android threats and their techniques" - Lukas Štefanko 

The number of Android devices, developers and applications is growing, making our lives even more convenient and connected. But there is also a dark side to the number of apps: malicious actors developing apps capable of stealing mobile banking credentials or even spying on unsuspecting users, ranging from simple phishing apps to much more advanced and stealthy threats. Such infiltrations are not just spread using social engineering or via alternative app stores, but also through Google Play, the official Android app store. As a result, dangerous malware, too, can be just a tap away. This presentation will give an overview of latest Android malware, focusing on banking malware and its go-to tricks and techniques. The talk will also include an analysis of a recently discovered family of Android banking malware that could make payments directly from the compromised device.
Symantec's Internet Security Threat Report for the Government Sector

Symantec has established the most comprehensive source of Internet threat data in the world through the Symantec Global Intelligence Network, which is made up of more than 41.5 million attack sensors and records thousands of events per second. This network monitors threat activity in over 157 countries and territories through a combination of Symantec products and services such as Symantec DeepSight Threat Management System, Symantec Managed Security Services, Norton consumer products, and other third-party data sources.
In addition, Symantec maintains one of the world’s most comprehensive vulnerability databases, currently consisting of more than 60,000 recorded vulnerabilities (spanning more than two decades) from over 19,000 vendors representing over 54,000 products.
Spam, phishing, and malware data is captured through a variety of sources including the Symantec Probe Network, a system of more than 5 million decoy accounts, Symantec.cloud, and a number of other Symantec security technologies. Skeptic, the Symantec.cloud proprietary heuristic technology, is able to detect new and sophisticated targeted threats before they reach customers’ networks. Over 8.4 billion email messages are processed each month and more than 1.7 billion web requests filtered each day across 14 data centers. Symantec also gathers phishing information through an extensive anti-fraud community of enterprises, security vendors, and more than 50 million consumers.
Symantec Trust Services provides 100 percent availability and processes over 6 billion Online Certificate Status Protocol (OCSP) look-ups per day, which are used for obtaining the revocation status of X.509 digital certificates around the world. These resources give Symantec analysts unparalleled sources of data with which to identify, analyze, and provide informed commentary on emerging trends in attacks, malicious code activity, phishing, and spam. The result is the annual Symantec Internet Security Threat Report, which gives enterprises, small businesses, and consumers essential information to secure their system effectively now and into the future.
Similar to [Infographic] CYREN Q3 2015 Cyber Threat Report (20)
Symantec Internet Security Threat Report Volume 2015

Symantec Internet Security Threat Report Volume 2015
Cosmin Vilcu - Sonicwal - prezentare - Cyber Security Trends 2020

Cosmin Vilcu - Sonicwal - prezentare - Cyber Security Trends 2020
A Joint Study by National University of Singapore and IDC

A Joint Study by National University of Singapore and IDC
Symantec (ISTR) Internet Security Threat Report Volume 22

Symantec (ISTR) Internet Security Threat Report Volume 22
Symantec Website Security Threat Report 2014 - RapidSSLOnline

Symantec Website Security Threat Report 2014 - RapidSSLOnline
"Latest Android threats and their techniques" - Lukas Štefanko 

"Latest Android threats and their techniques" - Lukas Štefanko
Symantec's Internet Security Threat Report for the Government Sector

Symantec's Internet Security Threat Report for the Government Sector
[Infographic] CYREN Q3 2015 Cyber Threat Report
- 1. 17 CYREN CYBER SECURITY AWARENESS REPORT CYREN cyber intelligence powers the security solutions of over 200 of the largest IT and security technology providers in the world. Every day, CYREN collects and analyzes 17 billion pieces of threat data, through 500,000 global points of presence, distributed across 200 countries, ultimately protecting 600 million global users. 6.25%of all Android apps installed are malicious 655,000new Android malware variants found in Q3 — 24% less than in Q2 7of the top 10 types of Android malware are adware related; the remaining 3 are SMS Trojans Android Malware Distribution Trends Q3 2015 Phishing Trends Spam Trends 24% 4.3 millionphishing URLs tracked by CYREN — down 19% from July Spam Trends 19% 5.4% CYREN analysts believe that the decrease could be a normalizing trend from the significant increase in Q2 (38%) 52 billionaverage Spam Per Day in Q3 — down 5.4% from 55 billion in Q2 The September 2015 spam level was the lowest in six years, at 47.4 billlion per day 60 50 40 30 20 10 0 2.5 2 1.5 1 0.5 0 SFThWTMSu Billions Billions Spam Malware Fridays are the peak distribution days for both Malware and Spam. CYBERTHREATReport 17B PIECES OF THREAT DATA 200 COUNTRIES 500K GLOBAL POINTS OF PRESENCE 600M GLOBAL USERS 2.25 billionaverage Malware attachments on Fridays in Q3