INFOGRAPHIC: Secure Computing as Threats Evolve
•
1 like•1,050 views
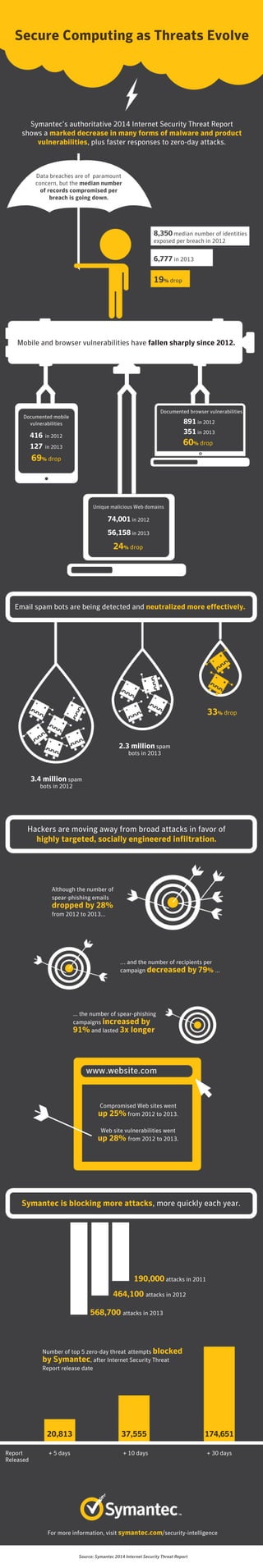
Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Report
Share
Report
Share
Download to read offline
Recommended
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Proofpoint Understanding Email Fraud in 2018 

Email fraud, also known as business email compromise (BEC), is one of today's greatest cyber threats. These highly targeted attacks, sent in low volumes, target people rather than technologies. As a result, they are difficult for traditional security solutions to detect.
To better understand how email fraud is affecting companies like yours, Proofpoint commissioned a survey of more than 2,250 IT decision makers across the U.S., the U.K., Australia, France, and Germany. This infographic highlights our findings.
Infographic - Three steps to stopping advanced email threats

Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Knowbe4 presentation

I am trying to tell about phishing attack and how we can train ourselves against through KnowBe4.
Md Mofijul Haque
Business Development Executive
Desh Cyber Limited
Security Awareness Training from KnowBe4

KnowBe4 helps you keep your network secure with Kevin Mitnick security awareness training. You are able to send simulated phishing attacks before and after the training. Created ‘by admins for admins’, a minimum of time is needed with visible proof the security awareness training works. Find out what your email attack footprint looks like and ask for our free Email Exposure Check.
Based on Kevin’s 30+ year unique first-hand hacking experience, you are now able to train employees with next-generation web-based training and testing, to quickly solve the increasingly urgent security problem of Social Engineering.
Recommended
Verizon Data Breach Investigations Report (DBIR) 2017

The Verizon Data Breach Investigation Report (DBIR) provides useful information related to information security. The information was obtained from a collaboration of many security organizations and vendors. The findings from the report confirm that phishing is a significant threat vector in today's environment. This presentations highlights key points from the DBIR related to phishing.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Proofpoint Understanding Email Fraud in 2018 

Email fraud, also known as business email compromise (BEC), is one of today's greatest cyber threats. These highly targeted attacks, sent in low volumes, target people rather than technologies. As a result, they are difficult for traditional security solutions to detect.
To better understand how email fraud is affecting companies like yours, Proofpoint commissioned a survey of more than 2,250 IT decision makers across the U.S., the U.K., Australia, France, and Germany. This infographic highlights our findings.
Infographic - Three steps to stopping advanced email threats

Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Knowbe4 presentation

I am trying to tell about phishing attack and how we can train ourselves against through KnowBe4.
Md Mofijul Haque
Business Development Executive
Desh Cyber Limited
Security Awareness Training from KnowBe4

KnowBe4 helps you keep your network secure with Kevin Mitnick security awareness training. You are able to send simulated phishing attacks before and after the training. Created ‘by admins for admins’, a minimum of time is needed with visible proof the security awareness training works. Find out what your email attack footprint looks like and ask for our free Email Exposure Check.
Based on Kevin’s 30+ year unique first-hand hacking experience, you are now able to train employees with next-generation web-based training and testing, to quickly solve the increasingly urgent security problem of Social Engineering.
Symantec Internet Security Threat Report 2014 - Volume 19

The 2014 Internet Security Threat Report gives an overview of global threat activity for the past year based on data from Symantec’s Global Intelligence Network.
Email Security Threats: IT Manager's Eyes Only 

Discover the latest confidential stats and facts charting the rise of Spam, Malware, Ransonware and Phishing in 2015. It makes for sobering reading for any responsible IT Manager.
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Private Sector, by John Bordwine
What is the Cybersecurity plan for tomorrow?

What have been done so far and what are the plans for tomorrow.
Symantec Website Security Threat Report - Insights

Part one of the Symantec Website Security Threat Report white paper is available here: http://bit.ly/17XOM54
These slides give insights from the Symantec Website Security's annual global threat report.We look at website malware, malvertising, targeted attacks, watering hole attacks, ransomware and website vulnerabilities.
Information Security Management System in the Banking Sector

Information Security Management System design. Information security governance approaches comparison. ISMS processes. ISMS implementation. The biggest threats in the Banking sector. The future of banking and payment systems. The challenges and future of banking. Cybersecurity solutions for Financial services.
Mobile Protect Pro - Powered by Zimperium

Zimperium's Mobile Protect Pro presentation at Deutsche Telekom's Magenta Security Summit in Frankfurt, Germany.
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Zimperium's presentation at Deutsche Telekom's Operator Partner Summit at Hub:Raum in Berlin, Germany.
Top 5 Cybersecurity Threats in Retail Industry

Retail industry is growing at a very fast pace. This slideshare takes you through the security threats in retail industry.
Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...

Business Has Changed. The Threat Landscape Has Changed. Are You Prepared?
Today’s workers have gone beyond the network, using multiple devices to conduct business, anywhere, any time. The move has resulted in greater productivity and collaboration—and a greater risk of attack by cyber criminals. How can you protect your business today?
Be careful what you click on!

We collaborated with MailGuard to present you with some facts around scam emails and the surprising amount of cybercrime that originates from them.
Visit our website at www.itro.com.au for more information.
Cybersecurity Challenges in Retail 2020: How to Prevent Retail Theft

While retailers keep opening new stores, hackers continue mastering their skills.
What cybersecurity challenges should the retail industry expect in 2020? It is time to reveal trends and prepare to fight upcoming attacks.
Learn the details: https://www.intellias.com/retail-security-challenges-in-2020-in-depth-security-coverage-to-prevent-retail-theft/
Web 2.0/Social Networks and Security

This slidecast provides information on the interrelationships between Web 2.0/social network applications and security. It explores the impacts that Web 2.0/social network applications have on security, provides examples of such security attacks, and offer potential solutions.
Internet Security Threat Report 2014 :: Volume 19 Appendices - The hardcore n...

Internet Security Threat Report 2014 :: Volume 19 :: Appendices
Hardcore data from Symantec’s Internet Security Threat Report.
Real number crunching on Threat Malicious Code, Fraud & Vulnerability trends including
Threat Activity Trends
• Malicious Activity by Source
• Malicious Web-Based Attack Prevalence
• Analysis of Malicious Web Activity by Attack Toolkits
• Analysis of Web-Based Spyware, Adware, and Potentially Unwanted Programs
• Analysis of Web Policy Risks from Inappropriate Use
• Analysis of Website Categories Exploited to Deliver Malicious Code
• Bot-Infected Computers
• Analysis of Mobile Threats
• Quantified Self – A Path to Self-Enlightenment or Just Another Security Nightmare?
• Data Breaches that could lead to Identity Theft
• Threat of the Insider
• Gaming Attacks
• The New Black Market
Malicious Code Trends
• Top Malicious Code Families
• Analysis of Malicious Code Activity
by Geography, Industry Sector, and Company Size
• Propagation Mechanisms
• Email-Targeted Spear-Phishing Attacks Intelligence
Spam and Fraud Activity Trends
• Analysis of Spam Activity Trends
• Analysis of Spam Activity by Geography, Industry Sector, and Company Size
• Analysis of Spam Delivered by Botnets
• Significant Spam Tactics
• Analysis of Spam by Categorization
• Phishing Activity Trends
• Analysis of Phishing Activity by Geography, Industry Sector, and Company Size
• New Spam Trend: BGP Hijacking
Vulnerability Trends
• Total Number of Vulnerabilities
• Zero-Day Vulnerabilities
• Web Browser Vulnerabilities
• Web Browser Plug-in Vulnerabilities
• Web Attack Toolkits SCADA Vulnerabilities
Can you predict who will win the US election?

Who would win the battle for the White House to become the next President of the United States was a topic of hot debate in 2012.
Much of that debate was taking place online, with plenty of people blogging, tweeting or updating social media with their thoughts on Mitt Romney versus Barack Obama.
Photo: usatoday.com
This provided us with a rich source of information about what people were thinking and feeling about the election race. So today I've decided to cover Techniques of Digital Data Analysis that are used to predict the US election. And perhaps the 2012 election will be remembered as the first election where big data analysis played a crucial role and had a tremendous impact on the outcome of the presidential election.
I am fairly familiar with the above mentioned techniques, because I had an opportunity to meet the CEO of EMC company on January 2013 in Singapore. EMC was one of a selected few companies that Twitter had entrusted to syndicate and provide access to the full Twitter feed for use in internal analytics applications for Obama's campaign in 2012. In my humble opinion that was the reason that in 2015 this company was sold to Dell for $67B in largest deal in Tech history.
The techniques of big data analysis remain the same, so let’s jump to year 2016 and see what social media data is used to predict the US election nowadays.
Read as an article: http://news.cybergates.org/en/articles/can-you-predict-who-will-win-the-us-election
ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks

See How Proofpoint Measures Up: Preventing, Detecting, and Responding to Advanced Email-based Attacks.
Email threats are evolving. Are your defenses?
Ransomware, Email Fraud, and email downtime threaten your business—and your bottom line. You need defenses to solve your entire email threat problem, not just parts of it.
Read what Enterprise Strategy Group (ESG) has to say about Proofpoint Advanced Email Security. Learn why you need a multilayered email security defense to stop the broadest range of threats targeting your organization:
- Quickly and simply identify and prioritize threats
- Gain visibility into every aspect of a threat
- Remediate potential threats before they can do harm
Download the report to for an in-depth review of how you can stop email attacks:
https://www.proofpoint.com/us/resources/analyst-reports/esg-proofpoint-advanced-email-security
Symantec's Internet Security Threat Report for the Government Sector

Symantec has established the most comprehensive source of Internet threat data in the world through the Symantec Global Intelligence Network, which is made up of more than 41.5 million attack sensors and records thousands of events per second. This network monitors threat activity in over 157 countries and territories through a combination of Symantec products and services such as Symantec DeepSight Threat Management System, Symantec Managed Security Services, Norton consumer products, and other third-party data sources.
In addition, Symantec maintains one of the world’s most comprehensive vulnerability databases, currently consisting of more than 60,000 recorded vulnerabilities (spanning more than two decades) from over 19,000 vendors representing over 54,000 products.
Spam, phishing, and malware data is captured through a variety of sources including the Symantec Probe Network, a system of more than 5 million decoy accounts, Symantec.cloud, and a number of other Symantec security technologies. Skeptic, the Symantec.cloud proprietary heuristic technology, is able to detect new and sophisticated targeted threats before they reach customers’ networks. Over 8.4 billion email messages are processed each month and more than 1.7 billion web requests filtered each day across 14 data centers. Symantec also gathers phishing information through an extensive anti-fraud community of enterprises, security vendors, and more than 50 million consumers.
Symantec Trust Services provides 100 percent availability and processes over 6 billion Online Certificate Status Protocol (OCSP) look-ups per day, which are used for obtaining the revocation status of X.509 digital certificates around the world. These resources give Symantec analysts unparalleled sources of data with which to identify, analyze, and provide informed commentary on emerging trends in attacks, malicious code activity, phishing, and spam. The result is the annual Symantec Internet Security Threat Report, which gives enterprises, small businesses, and consumers essential information to secure their system effectively now and into the future.
More Related Content
What's hot
Symantec Internet Security Threat Report 2014 - Volume 19

The 2014 Internet Security Threat Report gives an overview of global threat activity for the past year based on data from Symantec’s Global Intelligence Network.
Email Security Threats: IT Manager's Eyes Only 

Discover the latest confidential stats and facts charting the rise of Spam, Malware, Ransonware and Phishing in 2015. It makes for sobering reading for any responsible IT Manager.
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Private Sector, by John Bordwine
What is the Cybersecurity plan for tomorrow?

What have been done so far and what are the plans for tomorrow.
Symantec Website Security Threat Report - Insights

Part one of the Symantec Website Security Threat Report white paper is available here: http://bit.ly/17XOM54
These slides give insights from the Symantec Website Security's annual global threat report.We look at website malware, malvertising, targeted attacks, watering hole attacks, ransomware and website vulnerabilities.
Information Security Management System in the Banking Sector

Information Security Management System design. Information security governance approaches comparison. ISMS processes. ISMS implementation. The biggest threats in the Banking sector. The future of banking and payment systems. The challenges and future of banking. Cybersecurity solutions for Financial services.
Mobile Protect Pro - Powered by Zimperium

Zimperium's Mobile Protect Pro presentation at Deutsche Telekom's Magenta Security Summit in Frankfurt, Germany.
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Zimperium's presentation at Deutsche Telekom's Operator Partner Summit at Hub:Raum in Berlin, Germany.
Top 5 Cybersecurity Threats in Retail Industry

Retail industry is growing at a very fast pace. This slideshare takes you through the security threats in retail industry.
Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...

Business Has Changed. The Threat Landscape Has Changed. Are You Prepared?
Today’s workers have gone beyond the network, using multiple devices to conduct business, anywhere, any time. The move has resulted in greater productivity and collaboration—and a greater risk of attack by cyber criminals. How can you protect your business today?
Be careful what you click on!

We collaborated with MailGuard to present you with some facts around scam emails and the surprising amount of cybercrime that originates from them.
Visit our website at www.itro.com.au for more information.
Cybersecurity Challenges in Retail 2020: How to Prevent Retail Theft

While retailers keep opening new stores, hackers continue mastering their skills.
What cybersecurity challenges should the retail industry expect in 2020? It is time to reveal trends and prepare to fight upcoming attacks.
Learn the details: https://www.intellias.com/retail-security-challenges-in-2020-in-depth-security-coverage-to-prevent-retail-theft/
Web 2.0/Social Networks and Security

This slidecast provides information on the interrelationships between Web 2.0/social network applications and security. It explores the impacts that Web 2.0/social network applications have on security, provides examples of such security attacks, and offer potential solutions.
Internet Security Threat Report 2014 :: Volume 19 Appendices - The hardcore n...

Internet Security Threat Report 2014 :: Volume 19 :: Appendices
Hardcore data from Symantec’s Internet Security Threat Report.
Real number crunching on Threat Malicious Code, Fraud & Vulnerability trends including
Threat Activity Trends
• Malicious Activity by Source
• Malicious Web-Based Attack Prevalence
• Analysis of Malicious Web Activity by Attack Toolkits
• Analysis of Web-Based Spyware, Adware, and Potentially Unwanted Programs
• Analysis of Web Policy Risks from Inappropriate Use
• Analysis of Website Categories Exploited to Deliver Malicious Code
• Bot-Infected Computers
• Analysis of Mobile Threats
• Quantified Self – A Path to Self-Enlightenment or Just Another Security Nightmare?
• Data Breaches that could lead to Identity Theft
• Threat of the Insider
• Gaming Attacks
• The New Black Market
Malicious Code Trends
• Top Malicious Code Families
• Analysis of Malicious Code Activity
by Geography, Industry Sector, and Company Size
• Propagation Mechanisms
• Email-Targeted Spear-Phishing Attacks Intelligence
Spam and Fraud Activity Trends
• Analysis of Spam Activity Trends
• Analysis of Spam Activity by Geography, Industry Sector, and Company Size
• Analysis of Spam Delivered by Botnets
• Significant Spam Tactics
• Analysis of Spam by Categorization
• Phishing Activity Trends
• Analysis of Phishing Activity by Geography, Industry Sector, and Company Size
• New Spam Trend: BGP Hijacking
Vulnerability Trends
• Total Number of Vulnerabilities
• Zero-Day Vulnerabilities
• Web Browser Vulnerabilities
• Web Browser Plug-in Vulnerabilities
• Web Attack Toolkits SCADA Vulnerabilities
Can you predict who will win the US election?

Who would win the battle for the White House to become the next President of the United States was a topic of hot debate in 2012.
Much of that debate was taking place online, with plenty of people blogging, tweeting or updating social media with their thoughts on Mitt Romney versus Barack Obama.
Photo: usatoday.com
This provided us with a rich source of information about what people were thinking and feeling about the election race. So today I've decided to cover Techniques of Digital Data Analysis that are used to predict the US election. And perhaps the 2012 election will be remembered as the first election where big data analysis played a crucial role and had a tremendous impact on the outcome of the presidential election.
I am fairly familiar with the above mentioned techniques, because I had an opportunity to meet the CEO of EMC company on January 2013 in Singapore. EMC was one of a selected few companies that Twitter had entrusted to syndicate and provide access to the full Twitter feed for use in internal analytics applications for Obama's campaign in 2012. In my humble opinion that was the reason that in 2015 this company was sold to Dell for $67B in largest deal in Tech history.
The techniques of big data analysis remain the same, so let’s jump to year 2016 and see what social media data is used to predict the US election nowadays.
Read as an article: http://news.cybergates.org/en/articles/can-you-predict-who-will-win-the-us-election
ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks

See How Proofpoint Measures Up: Preventing, Detecting, and Responding to Advanced Email-based Attacks.
Email threats are evolving. Are your defenses?
Ransomware, Email Fraud, and email downtime threaten your business—and your bottom line. You need defenses to solve your entire email threat problem, not just parts of it.
Read what Enterprise Strategy Group (ESG) has to say about Proofpoint Advanced Email Security. Learn why you need a multilayered email security defense to stop the broadest range of threats targeting your organization:
- Quickly and simply identify and prioritize threats
- Gain visibility into every aspect of a threat
- Remediate potential threats before they can do harm
Download the report to for an in-depth review of how you can stop email attacks:
https://www.proofpoint.com/us/resources/analyst-reports/esg-proofpoint-advanced-email-security
What's hot (20)
Symantec Internet Security Threat Report 2014 - Volume 19

Symantec Internet Security Threat Report 2014 - Volume 19
RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...

RSA 2013 Session: Mobile Security Smackdown: How Government “Pwned” The Priva...
Symantec Website Security Threat Report - Insights

Symantec Website Security Threat Report - Insights
Information Security Management System in the Banking Sector

Information Security Management System in the Banking Sector
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Deutsche Telekom Partnering Operating Alliance Summit - Zimperium
Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...

Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...
Cybersecurity Challenges in Retail 2020: How to Prevent Retail Theft

Cybersecurity Challenges in Retail 2020: How to Prevent Retail Theft
Internet Security Threat Report 2014 :: Volume 19 Appendices - The hardcore n...

Internet Security Threat Report 2014 :: Volume 19 Appendices - The hardcore n...
ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks

ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks
Similar to INFOGRAPHIC: Secure Computing as Threats Evolve
Symantec's Internet Security Threat Report for the Government Sector

Symantec has established the most comprehensive source of Internet threat data in the world through the Symantec Global Intelligence Network, which is made up of more than 41.5 million attack sensors and records thousands of events per second. This network monitors threat activity in over 157 countries and territories through a combination of Symantec products and services such as Symantec DeepSight Threat Management System, Symantec Managed Security Services, Norton consumer products, and other third-party data sources.
In addition, Symantec maintains one of the world’s most comprehensive vulnerability databases, currently consisting of more than 60,000 recorded vulnerabilities (spanning more than two decades) from over 19,000 vendors representing over 54,000 products.
Spam, phishing, and malware data is captured through a variety of sources including the Symantec Probe Network, a system of more than 5 million decoy accounts, Symantec.cloud, and a number of other Symantec security technologies. Skeptic, the Symantec.cloud proprietary heuristic technology, is able to detect new and sophisticated targeted threats before they reach customers’ networks. Over 8.4 billion email messages are processed each month and more than 1.7 billion web requests filtered each day across 14 data centers. Symantec also gathers phishing information through an extensive anti-fraud community of enterprises, security vendors, and more than 50 million consumers.
Symantec Trust Services provides 100 percent availability and processes over 6 billion Online Certificate Status Protocol (OCSP) look-ups per day, which are used for obtaining the revocation status of X.509 digital certificates around the world. These resources give Symantec analysts unparalleled sources of data with which to identify, analyze, and provide informed commentary on emerging trends in attacks, malicious code activity, phishing, and spam. The result is the annual Symantec Internet Security Threat Report, which gives enterprises, small businesses, and consumers essential information to secure their system effectively now and into the future.
Symantec Website Security Threat Report 2014 - RapidSSLOnline

Symantec Website Security Threat Report 2014!
Cybersecurity Predictions For 2022.pdf

Everyone wants to know what the future holds. Those who are one step ahead of the rest can sense challenges ahead of time and avoid pitfalls or recognize opportunities and move towards success.
True Cost of Ransomware to Your Business

Global costs due to ransomware are projected to grow exponentially in the future. Read on to learn the damaging effects of ransomware attacks on your business and how to avoid them.
Cybercrime - Attack of the Cyber Spies

Globally cybercrime casused €83bn of damage, this presentation looks at the dangers and the measures you can take to stay safe. To view the webcast click here https://www.brighttalk.com/webcast/6331/90937
Symantec Internet Security Threat Report Volume 2015

Symantec reveals that nearly 1 million or around one-third of all Android apps are actually malware | Full Article:
Key Findings from the 2015 IBM Cyber Security Intelligence Index

View on-demand presentation: http://securityintelligence.com/events/ibm-2015-cyber-security-intelligence-index/
The cyber threat landscape is increasing in complexity and frequency. Organizations that have historically not been the target of cyber attacks now make headline news with large data losses and compromised transactions. Organizations need a clear point of view on how to respond to these threats, and one that incorporates not only the relevant technology but also the organizational changes needed.
Nick Bradley, Practice Leader of the IBM Threat Research Group and the X-Force Threat Analysis Team, and Nick Coleman, Global Head Cyber Security Intelligence Services outline what organizations need to do now and in the future to stay ahead of the growing cyber security threat.
11 Reasons Why Your Company Could Be In Danger

In today’s interconnected world, few things terrify CEOs and CTOs more than electronic security (well, a breach of that security, anyway). Most of our records, personal information, corporate information, and sensitive data exist online or on Internet-connected hardware. Mobile, with all it’s advantages for enterprises, actually poses one of the largest emerging threats to those enterprises’ data security. As such, we wanted to share some statistics that demonstrate the severity of the problem and highlight the importance of mobile security for your business.
Securing the Cloud

GGV Managing Partner Glenn Solomon reviews the current state of cybersecurity, the key targets and threats, and how the landscape is evolving.
Segurinfo2014 Santiago Cavanna

Presentacion realizada en Argentina y Paraguay Durante Marzo 2014.
En Argentina por Faustino Sanchez. En Paraguay por Santiago Cavanna.
Trata sobre el problema de la presencia de vulnerabilidades en aplicaciones, el impacto que tiene en las organizaciones y la forma que se encuentra disponible para descubrirlas en forma temprana y facilitar su remediacion
Links disponibles en
http://www.santiagocavanna.com/segurinfo-2014-el-costo-oculto-de-las-aplicaciones-vulnerables/
2021 Cybersecurity Recap: How Did We Fare Last Year? 

Cyberattacks, as it seems, are growing almost exponentially every year. the state of online attacks, c, and security flaws seem to be never-ending, and individuals and businesses have had to adopt regularly to combat these issues. the year 2021 has seen its fair share of cyberattacks and spying but, as the tech industry makes contingency plans to deal with them, we ought to know what the greater picture looked like and how to prepare in the new year.
Cyber Risk Management in the New Digitalisation Age - eSentinel™ 

Presentation slides from Webinar 11th Dec 2020 by Kenneth Wee, Commercial Director, Netpluz Asia Pte Ltd
CyberDen 2020

One afternoon. Nine pitches. Who will get your 'investment'?
Enter the CyberDen and take your place in the dragon's seat. We're sending in eight leading cyber security vendors who will pitch their solutions to try and pique your interest.
We've rounded up some of the biggest names in the industry and exciting new players to provide you with an informative and relaxed afternoon. The RSA Vaults act as the perfect setting to make you feel like you're stepping in the den. You can then vote to 'invest' in the pitches that impress you or excite your interest.
Four Network Security Challenges for the Cloud Generation

Users are everywhere and need quick access to data and cloud applications around the clock. Your network protection must balance security, performance, complexity, and cost. Symantec Web Security Services protects you with uncompromised network security, delivered from the cloud.
Similar to INFOGRAPHIC: Secure Computing as Threats Evolve (20)
Symantec's Internet Security Threat Report for the Government Sector

Symantec's Internet Security Threat Report for the Government Sector
Symantec Website Security Threat Report 2014 - RapidSSLOnline

Symantec Website Security Threat Report 2014 - RapidSSLOnline
Symantec Internet Security Threat Report Volume 2015

Symantec Internet Security Threat Report Volume 2015
Key Findings from the 2015 IBM Cyber Security Intelligence Index

Key Findings from the 2015 IBM Cyber Security Intelligence Index
2021 Cybersecurity Recap: How Did We Fare Last Year? 

2021 Cybersecurity Recap: How Did We Fare Last Year?
Cyber Risk Management in the New Digitalisation Age - eSentinel™ 

Cyber Risk Management in the New Digitalisation Age - eSentinel™
Four Network Security Challenges for the Cloud Generation

Four Network Security Challenges for the Cloud Generation
More from Symantec
Symantec Enterprise Security Products are now part of Broadcom

Symantec Enterprise Security Products are now part of Broadcom. The consumer division of Symantec Corp. is now NortonLifeLock Inc. -- a standalone company dedicated to consumer cyber safety.
Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...

Youth in foster care face unique risks to their identity.In this webinar we discuss the risks, as well as tips for better protection. Watch on demand here: https://symc.ly/2N8cELV.
Symantec Webinar | National Cyber Security Awareness Month: Protect IT

Learn how to protect your data during Symantec's National Cyber Security Awareness Month webinar with the Identity Theft Resource Center and Infolock.To watch on demand https://symc.ly/2VMMWQX.
Symantec Webinar | National Cyber Security Awareness Month: Secure IT

Symantec, TechSoup and the Michigan Small Business Development Center share how to apply added layers of security to your devices and online accounts. Watch on-demand recording here: https://symc.ly/33ifcxo.
Symantec Webinar | National Cyber Security Awareness Month - Own IT

View this webinar from Symantec and NCSAM partners, the National PTA, Connect Safety and the National Cyber Security Alliance, to learn how to protect the devices you use day to day.
Watch on demand here: https://symc.ly/2nLyXyB
Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)

On January 1, 2020, one of the strictest privacy laws in the US, the California Consumer Privacy Act (CCPA), will come into effect. What should governance, risk and compliance executives know in order to prepare for CCPA? Watch the on demand recording here: https://symc.ly/2Pn7tvW.
Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK

Experts from Symantec and MITRE explore the latest research and best practices for detecting targeted ransomware in your environment.
Watch on-demand webinar here: https://symc.ly/2L7ESFI.
Symantec Mobile Security Webinar

This webinar will explore the less-discussed topics of a mobile security strategy that everyone should understand – before it’s too late. Watch on-demand here: https://symc.ly/2z6hUsM.
Symantec Webinar Cloud Security Threat Report

Symantec 2019 Cloud Security Threat Report: Understand the Latest Cloud Security Trends. Watch the webinar on demand here: https://symc.ly/2Os8G4P.
Symantec Cloud Security Threat Report

Adapting to the New Reality of Evolving Cloud Threats. Download the complete report here: https://symc.ly/30DcSjd.
Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...

This Symantec Webinar shares best practices around network and cloud forensics and breach response. Stream here: https://symc.ly/2Livqld.
Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...

Symantec cloud security experts discuss implementing Zero Trust security policies across Web, email, and cloud application access. Watch recording here: https://symc.ly/2J3Htkf.
Symantec Webinar | Tips for Successful CASB Projects

There is an art to securely using cloud apps and services, including SaaS, PaaS, and IaaS. In this Symantec webcast, hear from Steve Riley, a Gartner senior director analyst who focuses on public cloud security, and Eric Andrews, Symantec’s vice president of cloud security, as they share best practices with practical tips for deploying CASB. Watch here: https://symc.ly/2QTyUec.
Symantec Webinar: What Cyber Threats Are Lurking in Your Network?

This webinar to shares insight into how an Advanced Threat Assessment does root analysis to uncover unknown, unique threats happening in your environment. Watch here: https://symc.ly/2W52MoA
Symantec Webinar: GDPR 1 Year On

Learn if you’ve got the right security strategy, and investment plan, to protect your organization and ensure regulatory compliance with the General Data Protection Regulation (GDPR). Watch now here: https://symc.ly/2VMNHIm
Symantec ISTR 24 Webcast 2019

2019 Symantec Internet Security Threat Report (ISTR): The New Threat Landscape presented by Kevin Haley, Director Product Management, Security Technology & Response, Symantec. Watch webinar recording here: https://symc.ly/2FJ9T18.
Symantec Best Practices for Cloud Security: Insights from the Front Lines

Download AWS Security Best Practices Guide with Cloud Configuration Checklist https://symc.ly/2FGNqC5.
Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...

Gain valuable insight whether you’re well on your way to Zero Trust implementation or are just considering it. Watch the original webinar here https://www.symantec.com/about/webcasts?commid=347274.
Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...

First-hand insights on the newest cloud-delivered endpoint security solutions. Hear from Joakim Liallias, Symantec and special guest speakers Sundeep Vijeswarapu from PayPal and top industry analyst Fernando Montenegro, 451 Research. Listen here: https://symc.ly/2UY2TlS.
Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear

Learn how Symantec Endpoint Protection & Response (EDR) and the MITRE ATT&CK framework can expose and thwart persistent adversaries like APT28 otherwise known as Fancy Bear. Watch Webinar here: https://symc.ly/2WyPD8I
More from Symantec (20)
Symantec Enterprise Security Products are now part of Broadcom

Symantec Enterprise Security Products are now part of Broadcom
Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...

Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...
Symantec Webinar | National Cyber Security Awareness Month: Protect IT

Symantec Webinar | National Cyber Security Awareness Month: Protect IT
Symantec Webinar | National Cyber Security Awareness Month: Secure IT

Symantec Webinar | National Cyber Security Awareness Month: Secure IT
Symantec Webinar | National Cyber Security Awareness Month - Own IT

Symantec Webinar | National Cyber Security Awareness Month - Own IT
Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)

Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)
Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK

Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK
Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...

Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...
Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...

Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...
Symantec Webinar | Tips for Successful CASB Projects

Symantec Webinar | Tips for Successful CASB Projects
Symantec Webinar: What Cyber Threats Are Lurking in Your Network?

Symantec Webinar: What Cyber Threats Are Lurking in Your Network?
Symantec Best Practices for Cloud Security: Insights from the Front Lines

Symantec Best Practices for Cloud Security: Insights from the Front Lines
Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...

Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...
Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...

Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...
Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear

Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear
Recently uploaded
一比一原版加拿大渥太华大学毕业证(uottawa毕业证书)如何办理

一模一样【q/微:1954292140】【加拿大渥太华大学毕业证(uottawa毕业证书)成绩单Offer】【q/微:1954292140】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【q/微:1954292140】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【q/微:1954292140】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
Meas_Dylan_DMBS_PB1_2024-05XX_Revised.pdf

Personal Brand Statement:
As an Army veteran dedicated to lifelong learning, I bring a disciplined, strategic mindset to my pursuits. I am constantly expanding my knowledge to innovate and lead effectively. My journey is driven by a commitment to excellence, and to make a meaningful impact in the world.
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account
Looking to buy verified PayPal accounts? Discover 7 expert tips for safely purchasing a verified PayPal account in 2024. Ensure security and reliability for your transactions.
PayPal Services Features-
🟢 Email Access
🟢 Bank Added
🟢 Card Verified
🟢 Full SSN Provided
🟢 Phone Number Access
🟢 Driving License Copy
🟢 Fasted Delivery
Client Satisfaction is Our First priority. Our services is very appropriate to buy. We assume that the first-rate way to purchase our offerings is to order on the website. If you have any worry in our cooperation usually You can order us on Skype or Telegram.
24/7 Hours Reply/Please Contact
usawebmarketEmail: support@usawebmarket.com
Skype: usawebmarket
Telegram: @usawebmarket
WhatsApp: +1(218) 203-5951
USA WEB MARKET is the Best Verified PayPal, Payoneer, Cash App, Skrill, Neteller, Stripe Account and SEO, SMM Service provider.100%Satisfection granted.100% replacement Granted.
The effects of customers service quality and online reviews on customer loyal...

The effects of customers service quality and online reviews on customer loyal...balatucanapplelovely
Research Sustainability: Balancing the Environment, Equity & Economy

[Note: This is a partial preview. To download this presentation, visit:
https://www.oeconsulting.com.sg/training-presentations]
Sustainability has become an increasingly critical topic as the world recognizes the need to protect our planet and its resources for future generations. Sustainability means meeting our current needs without compromising the ability of future generations to meet theirs. It involves long-term planning and consideration of the consequences of our actions. The goal is to create strategies that ensure the long-term viability of People, Planet, and Profit.
Leading companies such as Nike, Toyota, and Siemens are prioritizing sustainable innovation in their business models, setting an example for others to follow. In this Sustainability training presentation, you will learn key concepts, principles, and practices of sustainability applicable across industries. This training aims to create awareness and educate employees, senior executives, consultants, and other key stakeholders, including investors, policymakers, and supply chain partners, on the importance and implementation of sustainability.
LEARNING OBJECTIVES
1. Develop a comprehensive understanding of the fundamental principles and concepts that form the foundation of sustainability within corporate environments.
2. Explore the sustainability implementation model, focusing on effective measures and reporting strategies to track and communicate sustainability efforts.
3. Identify and define best practices and critical success factors essential for achieving sustainability goals within organizations.
CONTENTS
1. Introduction and Key Concepts of Sustainability
2. Principles and Practices of Sustainability
3. Measures and Reporting in Sustainability
4. Sustainability Implementation & Best Practices
To download the complete presentation, visit: https://www.oeconsulting.com.sg/training-presentations
The Parable of the Pipeline a book every new businessman or business student ...

The-Parable of the Pipeline a book every new businessman or business student must read before diving into real world of business.
Kseniya Leshchenko: Shared development support service model as the way to ma...

Kseniya Leshchenko: Shared development support service model as the way to make small projects with small budgets profitable for the company (UA)
Kyiv PMDay 2024 Summer
Website – www.pmday.org
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
falcon-invoice-discounting-a-premier-platform-for-investors-in-india

Falcon stands out as a top-tier P2P Invoice Discounting platform in India, bridging esteemed blue-chip companies and eager investors. Our goal is to transform the investment landscape in India by establishing a comprehensive destination for borrowers and investors with diverse profiles and needs, all while minimizing risk. What sets Falcon apart is the elimination of intermediaries such as commercial banks and depository institutions, allowing investors to enjoy higher yields.
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection -Introduction to Social Dreaming
#Systems Psychodynamics
#Innovation
#Creativity
#Consultancy
#Coaching
ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf

Implicitly or explicitly all competing businesses employ a strategy to select a mix
of marketing resources. Formulating such competitive strategies fundamentally
involves recognizing relationships between elements of the marketing mix (e.g.,
price and product quality), as well as assessing competitive and market conditions
(i.e., industry structure in the language of economics).
Memorandum Of Association Constitution of Company.ppt

www.seribangash.com
A Memorandum of Association (MOA) is a legal document that outlines the fundamental principles and objectives upon which a company operates. It serves as the company's charter or constitution and defines the scope of its activities. Here's a detailed note on the MOA:
Contents of Memorandum of Association:
Name Clause: This clause states the name of the company, which should end with words like "Limited" or "Ltd." for a public limited company and "Private Limited" or "Pvt. Ltd." for a private limited company.
https://seribangash.com/article-of-association-is-legal-doc-of-company/
Registered Office Clause: It specifies the location where the company's registered office is situated. This office is where all official communications and notices are sent.
Objective Clause: This clause delineates the main objectives for which the company is formed. It's important to define these objectives clearly, as the company cannot undertake activities beyond those mentioned in this clause.
www.seribangash.com
Liability Clause: It outlines the extent of liability of the company's members. In the case of companies limited by shares, the liability of members is limited to the amount unpaid on their shares. For companies limited by guarantee, members' liability is limited to the amount they undertake to contribute if the company is wound up.
https://seribangash.com/promotors-is-person-conceived-formation-company/
Capital Clause: This clause specifies the authorized capital of the company, i.e., the maximum amount of share capital the company is authorized to issue. It also mentions the division of this capital into shares and their respective nominal value.
Association Clause: It simply states that the subscribers wish to form a company and agree to become members of it, in accordance with the terms of the MOA.
Importance of Memorandum of Association:
Legal Requirement: The MOA is a legal requirement for the formation of a company. It must be filed with the Registrar of Companies during the incorporation process.
Constitutional Document: It serves as the company's constitutional document, defining its scope, powers, and limitations.
Protection of Members: It protects the interests of the company's members by clearly defining the objectives and limiting their liability.
External Communication: It provides clarity to external parties, such as investors, creditors, and regulatory authorities, regarding the company's objectives and powers.
https://seribangash.com/difference-public-and-private-company-law/
Binding Authority: The company and its members are bound by the provisions of the MOA. Any action taken beyond its scope may be considered ultra vires (beyond the powers) of the company and therefore void.
Amendment of MOA:
While the MOA lays down the company's fundamental principles, it is not entirely immutable. It can be amended, but only under specific circumstances and in compliance with legal procedures. Amendments typically require shareholder
Enterprise Excellence is Inclusive Excellence.pdf

Enterprise excellence and inclusive excellence are closely linked, and real-world challenges have shown that both are essential to the success of any organization. To achieve enterprise excellence, organizations must focus on improving their operations and processes while creating an inclusive environment that engages everyone. In this interactive session, the facilitator will highlight commonly established business practices and how they limit our ability to engage everyone every day. More importantly, though, participants will likely gain increased awareness of what we can do differently to maximize enterprise excellence through deliberate inclusion.
What is Enterprise Excellence?
Enterprise Excellence is a holistic approach that's aimed at achieving world-class performance across all aspects of the organization.
What might I learn?
A way to engage all in creating Inclusive Excellence. Lessons from the US military and their parallels to the story of Harry Potter. How belt systems and CI teams can destroy inclusive practices. How leadership language invites people to the party. There are three things leaders can do to engage everyone every day: maximizing psychological safety to create environments where folks learn, contribute, and challenge the status quo.
Who might benefit? Anyone and everyone leading folks from the shop floor to top floor.
Dr. William Harvey is a seasoned Operations Leader with extensive experience in chemical processing, manufacturing, and operations management. At Michelman, he currently oversees multiple sites, leading teams in strategic planning and coaching/practicing continuous improvement. William is set to start his eighth year of teaching at the University of Cincinnati where he teaches marketing, finance, and management. William holds various certifications in change management, quality, leadership, operational excellence, team building, and DiSC, among others.
Improving profitability for small business

In this comprehensive presentation, we will explore strategies and practical tips for enhancing profitability in small businesses. Tailored to meet the unique challenges faced by small enterprises, this session covers various aspects that directly impact the bottom line. Attendees will learn how to optimize operational efficiency, manage expenses, and increase revenue through innovative marketing and customer engagement techniques.
Skye Residences | Extended Stay Residences Near Toronto Airport

Experience unparalleled EXTENDED STAY and comfort at Skye Residences located just minutes from Toronto Airport. Discover sophisticated accommodations tailored for discerning travelers.
Website Link :
https://skyeresidences.com/
https://skyeresidences.com/about-us/
https://skyeresidences.com/gallery/
https://skyeresidences.com/rooms/
https://skyeresidences.com/near-by-attractions/
https://skyeresidences.com/commute/
https://skyeresidences.com/contact/
https://skyeresidences.com/queen-suite-with-sofa-bed/
https://skyeresidences.com/queen-suite-with-sofa-bed-and-balcony/
https://skyeresidences.com/queen-suite-with-sofa-bed-accessible/
https://skyeresidences.com/2-bedroom-deluxe-queen-suite-with-sofa-bed/
https://skyeresidences.com/2-bedroom-deluxe-king-queen-suite-with-sofa-bed/
https://skyeresidences.com/2-bedroom-deluxe-queen-suite-with-sofa-bed-accessible/
#Skye Residences Etobicoke, #Skye Residences Near Toronto Airport, #Skye Residences Toronto, #Skye Hotel Toronto, #Skye Hotel Near Toronto Airport, #Hotel Near Toronto Airport, #Near Toronto Airport Accommodation, #Suites Near Toronto Airport, #Etobicoke Suites Near Airport, #Hotel Near Toronto Pearson International Airport, #Toronto Airport Suite Rentals, #Pearson Airport Hotel Suites
Recently uploaded (20)
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account | Buy Google 5 Star Reviews
The effects of customers service quality and online reviews on customer loyal...

The effects of customers service quality and online reviews on customer loyal...
Sustainability: Balancing the Environment, Equity & Economy

Sustainability: Balancing the Environment, Equity & Economy
The Parable of the Pipeline a book every new businessman or business student ...

The Parable of the Pipeline a book every new businessman or business student ...
Kseniya Leshchenko: Shared development support service model as the way to ma...

Kseniya Leshchenko: Shared development support service model as the way to ma...
falcon-invoice-discounting-a-premier-platform-for-investors-in-india

falcon-invoice-discounting-a-premier-platform-for-investors-in-india
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection with Social Dreaming
ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf

ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf
The Influence of Marketing Strategy and Market Competition on Business Perfor...

The Influence of Marketing Strategy and Market Competition on Business Perfor...
Memorandum Of Association Constitution of Company.ppt

Memorandum Of Association Constitution of Company.ppt
Skye Residences | Extended Stay Residences Near Toronto Airport

Skye Residences | Extended Stay Residences Near Toronto Airport
INFOGRAPHIC: Secure Computing as Threats Evolve
- 1. Secure Computing as Threats Evolve Symantec’s authoritative 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Data breaches are of paramount concern, but the median number of records compromised per breach is going down. 8,350 median number of identities exposed per breach in 2012 6,777 in 2013 19% drop Mobile and browser vulnerabilities have fallen sharply since 2012. 416 in 2012 127 in 2013 Unique malicious Web domains 74,001 in 2012 56,158 in 2013 24% drop Email spam bots are being detected and neutralized more effectively. Hackers are moving away from broad attacks in favor of highly targeted, socially engineered infiltration. … and the number of recipients per campaign decreased by 79% ... Although the number of spear-phishing emails dropped by 28% from 2012 to 2013... Symantec is blocking more attacks, more quickly each year. 464,100 attacks in 2012 20,813 37,555 174,651 For more information, visit symantec.com/security-intelligence Source: Symantec 2014 Internet Security Threat Report 2.3 in 2013 3.4 million spam bots in 2012 33% drop 2.3 million spam bots in 2013 190,000 attacks in 2011 568,700 attacks in 2013 Number of top 5 zero-day threat attempts blocked by Symantec, after Internet Security Threat Report release date Report + 5 days Released + 10 days + 30 days Documented mobile vulnerabilities 69% drop Documented browser vulnerabilities 891 in 2012 351 in 2013 60% drop ... the number of spear-phishing campaigns increased by 91% and lasted 3x longer Compromised Web sites went up 25% from 2012 to 2013. Web site vulnerabilities went up 28% from 2012 to 2013.
