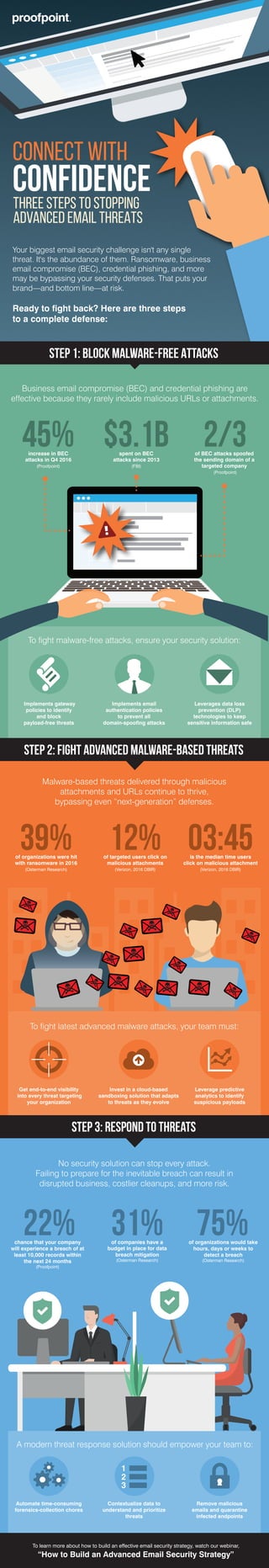
Infographic - Three steps to stopping advanced email threats
•
1 like•15,802 views
Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Report
Share
Report
Share
Download to read offline
Recommended
Reinforcing the Revolution: The Promise and Perils of Digital Transformation

Digital transformation is changing the way we do business. More than ever, your success hinges on the strength and reliability of your connections— between your workers, with your business partners, and to your customers.
ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks

See How Proofpoint Measures Up: Preventing, Detecting, and Responding to Advanced Email-based Attacks.
Email threats are evolving. Are your defenses?
Ransomware, Email Fraud, and email downtime threaten your business—and your bottom line. You need defenses to solve your entire email threat problem, not just parts of it.
Read what Enterprise Strategy Group (ESG) has to say about Proofpoint Advanced Email Security. Learn why you need a multilayered email security defense to stop the broadest range of threats targeting your organization:
- Quickly and simply identify and prioritize threats
- Gain visibility into every aspect of a threat
- Remediate potential threats before they can do harm
Download the report to for an in-depth review of how you can stop email attacks:
https://www.proofpoint.com/us/resources/analyst-reports/esg-proofpoint-advanced-email-security
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Adapted from an ESG report - Outnumbered, Outgunned. 

The document discusses how Proofpoint helps security teams address skills shortages through advanced threat protection products. It notes that threats are evolving across multiple vectors while security skills are hard to find. Proofpoint provides threat intelligence and tools to help security teams block attacks, detect threats, and respond to breaches without requiring expert skills. Through products like Targeted Attack Protection and the Nexus Threat Graph, Proofpoint aggregates data to identify attackers and campaigns in order to help security teams prioritize and resolve risks.
Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...

Business Has Changed. The Threat Landscape Has Changed. Are You Prepared?
Today’s workers have gone beyond the network, using multiple devices to conduct business, anywhere, any time. The move has resulted in greater productivity and collaboration—and a greater risk of attack by cyber criminals. How can you protect your business today?
Proofpoint Understanding Email Fraud in 2018 

Email fraud, also known as business email compromise (BEC), is one of today's greatest cyber threats. These highly targeted attacks, sent in low volumes, target people rather than technologies. As a result, they are difficult for traditional security solutions to detect.
To better understand how email fraud is affecting companies like yours, Proofpoint commissioned a survey of more than 2,250 IT decision makers across the U.S., the U.K., Australia, France, and Germany. This infographic highlights our findings.
The Cost of Inactivity: Malware Infographic

As the cost and likelihood of a breach grows you can't afford "good enough" protection before, during, AND after an attack. Protect your brand and data with Cisco email and web security.
Learn more: http://cs.co/9003hKu3, http://cs.co/9003hKu9
CSS Trivia

The document contains a series of questions and statements about cybersecurity threats and vulnerabilities. Some key facts presented include:
- 400,000 Facebook accounts are compromised by hackers every day
- The September 2016 Yahoo breach affected 500 million user accounts
- The fastest spreading email worm, MyDoom, caused $480 million in financial damage
- The average annualized cost of crime incurred by US organizations is $28.5 million
- The Pentagon reports receiving 5-10 million cyber attack attempts per day
Recommended
Reinforcing the Revolution: The Promise and Perils of Digital Transformation

Digital transformation is changing the way we do business. More than ever, your success hinges on the strength and reliability of your connections— between your workers, with your business partners, and to your customers.
ESG Validates Proofpoint’s Ability to Stop Advanced Email-based Attacks

See How Proofpoint Measures Up: Preventing, Detecting, and Responding to Advanced Email-based Attacks.
Email threats are evolving. Are your defenses?
Ransomware, Email Fraud, and email downtime threaten your business—and your bottom line. You need defenses to solve your entire email threat problem, not just parts of it.
Read what Enterprise Strategy Group (ESG) has to say about Proofpoint Advanced Email Security. Learn why you need a multilayered email security defense to stop the broadest range of threats targeting your organization:
- Quickly and simply identify and prioritize threats
- Gain visibility into every aspect of a threat
- Remediate potential threats before they can do harm
Download the report to for an in-depth review of how you can stop email attacks:
https://www.proofpoint.com/us/resources/analyst-reports/esg-proofpoint-advanced-email-security
Proofpoint Q3 - 2017 Email Fraud Threat Report

Proofpoint has a comprehensive solution to fight email fraud
Email fraud continues to expand its reach and attackers continue to shift in their approach. Proofpoint helps organizations stop all forms of email fraud with a comprehensive multi-layered solution.
To learn more about the email fraud landscape, read the full quarterly threat update here: www.proofpoint.com/us/resources/threat-reports/quarterly-email-fraud-report
For more information about how to stop impostor email attacks before they reach the inbox, please visit: www.proofpoint.com/us/solutions/email-fraud
Adapted from an ESG report - Outnumbered, Outgunned. 

The document discusses how Proofpoint helps security teams address skills shortages through advanced threat protection products. It notes that threats are evolving across multiple vectors while security skills are hard to find. Proofpoint provides threat intelligence and tools to help security teams block attacks, detect threats, and respond to breaches without requiring expert skills. Through products like Targeted Attack Protection and the Nexus Threat Graph, Proofpoint aggregates data to identify attackers and campaigns in order to help security teams prioritize and resolve risks.
Adapted from an ESG report - Seeing Is Securing - Protecting Against Advanced...

Business Has Changed. The Threat Landscape Has Changed. Are You Prepared?
Today’s workers have gone beyond the network, using multiple devices to conduct business, anywhere, any time. The move has resulted in greater productivity and collaboration—and a greater risk of attack by cyber criminals. How can you protect your business today?
Proofpoint Understanding Email Fraud in 2018 

Email fraud, also known as business email compromise (BEC), is one of today's greatest cyber threats. These highly targeted attacks, sent in low volumes, target people rather than technologies. As a result, they are difficult for traditional security solutions to detect.
To better understand how email fraud is affecting companies like yours, Proofpoint commissioned a survey of more than 2,250 IT decision makers across the U.S., the U.K., Australia, France, and Germany. This infographic highlights our findings.
The Cost of Inactivity: Malware Infographic

As the cost and likelihood of a breach grows you can't afford "good enough" protection before, during, AND after an attack. Protect your brand and data with Cisco email and web security.
Learn more: http://cs.co/9003hKu3, http://cs.co/9003hKu9
CSS Trivia

The document contains a series of questions and statements about cybersecurity threats and vulnerabilities. Some key facts presented include:
- 400,000 Facebook accounts are compromised by hackers every day
- The September 2016 Yahoo breach affected 500 million user accounts
- The fastest spreading email worm, MyDoom, caused $480 million in financial damage
- The average annualized cost of crime incurred by US organizations is $28.5 million
- The Pentagon reports receiving 5-10 million cyber attack attempts per day
Malware and the Cost of Inactivity

This document summarizes cybersecurity statistics from several reports published between 2013-2015. It finds that the average cost of a data breach rose to $5.9 million in 2014, with retail, financial services and healthcare being hit hardest. Mobile malware targeting Android devices increased, with web, network and email as the top infection vectors. The document also reports that 99% of cyberattacks are not detected in a timely manner, with over 2 years sometimes passing before a breach is discovered.
ISACA State of Cyber Security 2017

The document summarizes findings from ISACA's 2017 State of Cyber Security study regarding cyber security workforce trends and challenges. It reports that the cyber security skills gap persists, with many organizations receiving fewer than 5 applicants for open positions and the average time to fill positions being 3 months or more. Over half of organizations say practical hands-on experience is the most important candidate qualification, and only 70% require security certifications. The persistent skills shortage means about 1 in 5 organizations are unable to fill open cyber security roles.
Verizon Data Breach Investigations Report (DBIR) 2017

Phishing remains a significant threat according to the 2017 Verizon Data Breach Investigation Report. The report found that 28% of phishing attacks are targeted at specific individuals or groups, 66% of malware is installed via malicious email attachments, and 43% of security breaches involve social tactics like phishing. Phishing also played a role in 75% of ransomware attacks and 90% of social tactics used in breaches. The document recommends that businesses test their employees' ability to identify phishing attempts using available software tools.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Email: still the favourite route of attack

The document discusses how email continues to be the primary attack vector for cybercriminals. It notes that 78% of people claim to be aware of phishing risks but still click unknown links in emails. Various statistics are presented about increases in spear phishing attacks, ransomware attacks, and losses to business email compromise scams. The document advocates for implementing cloud-based email security solutions to help block these evolving threats through features like advanced threat protection, malware and spam filtering, sandboxing, and encryption. It outlines options for layered protection ranging from basic email filtering to more comprehensive advanced threat protection.
5 Key Findings on Advanced Threats

This document discusses the growing threat of advanced attacks and the limitations of current security prevention and detection methods. It finds that advanced threats and data breaches are increasing significantly year-over-year. Traditional security defenses are failing to detect many of these threats in a timely manner, allowing breaches to persist for months or years without discovery. The document advocates for a unified advanced threat protection solution that can better detect threats across networks, endpoints, and email through improved visibility, intelligence, and faster incident response capabilities. Such a solution aims to ease resource burdens on IT teams and help organizations more efficiently protect their businesses from advanced threats.
Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar

Join CTO and resident security expert, Matt Eshleman, for this webinar which will cover the basics a security plan should include, giving updates and a synthesis of our recent security webinars on understanding risks, considering cyber insurance, security incidence response best practices, and creating a multi-layered security plan that actively includes your staff and executives.
Rise of Ransomware 

This presentation, Ransomware Rising, details the results of a survey of security professionals taken at RSA 2017, the world’s largest security conference, exploring their experiences with ransomware.
Conducted Feb. 13-17, at RSA 2017, the in-person survey is based on responses from 170 attendees including IT professionals, managers and executives from the U.S. (77 percent), EMEA (13 percent) and other regions (11 percent).
To learn more about preventing ransomware visit, http://bit.ly/2nwKICL
Survey: Insider Threats and Cyber Security

A survey of 310 IT security professionals taken at the Infosecurity Europe trade show by Imperva. The survey found that when it comes to insider threats, over half (58 percent) of the IT security professionals were deeply concerned about careless users who unwittingly put their organization’s data at risk.
2013 Threat Report

Cyberthreats broke new ground with mobile devices, while reaching deeper into social media. Online criminals also stepped up attacks via email, web and other traditional vectors.
Websense 2013 Threat Report

1. The number of malicious web links grew by almost 600% worldwide according to data from Websense Security Labs.
2. 85% of malicious web links were found on legitimate web hosts that had been compromised, indicating websites can no longer be trusted based on their reputation.
3. Traditional anti-virus and firewall defenses are no longer sufficient to prevent web-borne threats, as the web serves both as an attack vector and in supporting other attack vectors like social media, mobile, and email. Advanced defenses that can identify compromised legitimate sites in real-time are needed.
2015 Microsoft Vulnerabilities Report 

The document summarizes a report analyzing Microsoft's security bulletins from 2015. It found 524 total vulnerabilities reported, a 52% increase from 2014. Nearly half (251) were given the highest critical severity rating. Vulnerabilities affecting Microsoft Office products doubled year-over-year to 62. The increased threats underscore the importance of removing administrator privileges to prevent the exploitation of vulnerabilities.
Cyber attacks in 2021

Cybersecurity experts predict that cyber attacks will be twice as what happened in 2019. In 2021 it is predicted that a cyber attack will be reported every 11 seconds which is twice what it was in 2019 (every 19 seconds).
Netpluz Managed SOC - MSS Service 

The document discusses cybersecurity threats like ransomware, phishing, and data theft that can disrupt business operations and cause monetary or reputational losses. It then describes how a managed security services provider like SK infosec can monitor networks and systems 24/7, detect and respond to cyber threats through security analytics and a security operations center, and help organizations facing challenges with limited security resources. Case studies are provided showing how SK infosec's managed security services protected clients from a web-shell upload attack and C&C callback as part of an advanced persistent threat.
Overcoming Cyber Attacks

In this infographic, we look at the key cyber challenges faced by today's businesses, along with the major data breaches of 2013/14 and the effectiveness of traditional security solutions.
Next Dimension and Cisco | Solutions for PIPEDA Compliance

Duwayne Watson, a Cisco specialist from Ingram Micro, showcases various Data Security and Protection solutions such as: AMP, Umbrella, and CloudLock. These solutions can help your business remain compliant with PIPEDA legislation.
7 cyber security questions for boards

The cyber security job is everyone's business including the Board of Directors, even without a cyber security degree. Recent cyber security news proves that. According to several studies, Boards are getting it wrong and are leaving cyber awareness and risk management in the hands of the CEO, CISO, CTOs and cyber security companies. In a sense they are abdicating their responsibility to the shareholders. This slideshare proposes 7 questions every board should be asking their company executives abour IT security. They're not necessarily all encompassing and don't take the place of real cybersecurity training, but will drive the discussion to better and more complete understanding of strategic risk. Questions cover the basics of cyber security training, cyber policies, who briefs and when at board meetings. Thanks.
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Containing the outbreak: The healthcare security pandemic

James Maude, Senior Security Engineer at Avecto examines the security state of play in the healthcare industry and why it’s now a prime target for hackers.
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study, The Cyber Security Readiness of Canadian Organizations, published February 2016. The full report can be downloaded at: scalar.ca/security-study-2016/
Why network based security

Traditional point solutions for cybersecurity defenses are often ineffective against modern threats, which rely on newly discovered vulnerabilities and complex multi-pronged attacks. Network-based security solutions offer enhanced protection by collecting threat intelligence from monitoring networks and analyzing suspicious activity, in order to identify threats earlier in their lifecycle. They also offload management burdens and provide expertise that individual organizations typically lack.
Assess risks to IT security.pptx

Cyber security involves implementing layers of security and protection against digital attacks across computers, devices, systems, and networks. Organizations use frameworks to detect and identify threats, protect assets, and recover from attacks. There are various types of cyber security threats including cybercrime, cyberterrorism, and cyberattacks. Performing risk assessments is important to understand potential security risks and impacts. Assessments involve identifying risks, analyzing likelihood and impacts, developing controls, documenting processes, and ongoing monitoring. Common security risks include viruses/malware, phishing, ransomware, and denial of service attacks. Organizations should use various security testing methods like audits, penetration testing, and vulnerability scanning to regularly evaluate security weaknesses.
More Related Content
What's hot
Malware and the Cost of Inactivity

This document summarizes cybersecurity statistics from several reports published between 2013-2015. It finds that the average cost of a data breach rose to $5.9 million in 2014, with retail, financial services and healthcare being hit hardest. Mobile malware targeting Android devices increased, with web, network and email as the top infection vectors. The document also reports that 99% of cyberattacks are not detected in a timely manner, with over 2 years sometimes passing before a breach is discovered.
ISACA State of Cyber Security 2017

The document summarizes findings from ISACA's 2017 State of Cyber Security study regarding cyber security workforce trends and challenges. It reports that the cyber security skills gap persists, with many organizations receiving fewer than 5 applicants for open positions and the average time to fill positions being 3 months or more. Over half of organizations say practical hands-on experience is the most important candidate qualification, and only 70% require security certifications. The persistent skills shortage means about 1 in 5 organizations are unable to fill open cyber security roles.
Verizon Data Breach Investigations Report (DBIR) 2017

Phishing remains a significant threat according to the 2017 Verizon Data Breach Investigation Report. The report found that 28% of phishing attacks are targeted at specific individuals or groups, 66% of malware is installed via malicious email attachments, and 43% of security breaches involve social tactics like phishing. Phishing also played a role in 75% of ransomware attacks and 90% of social tactics used in breaches. The document recommends that businesses test their employees' ability to identify phishing attempts using available software tools.
4 Facts Every Business Should Know About Phishing

This presentation highlights four facts about phishing. These facts prove that phishing is a serious information security risk for businesses.
Email: still the favourite route of attack

The document discusses how email continues to be the primary attack vector for cybercriminals. It notes that 78% of people claim to be aware of phishing risks but still click unknown links in emails. Various statistics are presented about increases in spear phishing attacks, ransomware attacks, and losses to business email compromise scams. The document advocates for implementing cloud-based email security solutions to help block these evolving threats through features like advanced threat protection, malware and spam filtering, sandboxing, and encryption. It outlines options for layered protection ranging from basic email filtering to more comprehensive advanced threat protection.
5 Key Findings on Advanced Threats

This document discusses the growing threat of advanced attacks and the limitations of current security prevention and detection methods. It finds that advanced threats and data breaches are increasing significantly year-over-year. Traditional security defenses are failing to detect many of these threats in a timely manner, allowing breaches to persist for months or years without discovery. The document advocates for a unified advanced threat protection solution that can better detect threats across networks, endpoints, and email through improved visibility, intelligence, and faster incident response capabilities. Such a solution aims to ease resource burdens on IT teams and help organizations more efficiently protect their businesses from advanced threats.
Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar

Join CTO and resident security expert, Matt Eshleman, for this webinar which will cover the basics a security plan should include, giving updates and a synthesis of our recent security webinars on understanding risks, considering cyber insurance, security incidence response best practices, and creating a multi-layered security plan that actively includes your staff and executives.
Rise of Ransomware 

This presentation, Ransomware Rising, details the results of a survey of security professionals taken at RSA 2017, the world’s largest security conference, exploring their experiences with ransomware.
Conducted Feb. 13-17, at RSA 2017, the in-person survey is based on responses from 170 attendees including IT professionals, managers and executives from the U.S. (77 percent), EMEA (13 percent) and other regions (11 percent).
To learn more about preventing ransomware visit, http://bit.ly/2nwKICL
Survey: Insider Threats and Cyber Security

A survey of 310 IT security professionals taken at the Infosecurity Europe trade show by Imperva. The survey found that when it comes to insider threats, over half (58 percent) of the IT security professionals were deeply concerned about careless users who unwittingly put their organization’s data at risk.
2013 Threat Report

Cyberthreats broke new ground with mobile devices, while reaching deeper into social media. Online criminals also stepped up attacks via email, web and other traditional vectors.
Websense 2013 Threat Report

1. The number of malicious web links grew by almost 600% worldwide according to data from Websense Security Labs.
2. 85% of malicious web links were found on legitimate web hosts that had been compromised, indicating websites can no longer be trusted based on their reputation.
3. Traditional anti-virus and firewall defenses are no longer sufficient to prevent web-borne threats, as the web serves both as an attack vector and in supporting other attack vectors like social media, mobile, and email. Advanced defenses that can identify compromised legitimate sites in real-time are needed.
2015 Microsoft Vulnerabilities Report 

The document summarizes a report analyzing Microsoft's security bulletins from 2015. It found 524 total vulnerabilities reported, a 52% increase from 2014. Nearly half (251) were given the highest critical severity rating. Vulnerabilities affecting Microsoft Office products doubled year-over-year to 62. The increased threats underscore the importance of removing administrator privileges to prevent the exploitation of vulnerabilities.
Cyber attacks in 2021

Cybersecurity experts predict that cyber attacks will be twice as what happened in 2019. In 2021 it is predicted that a cyber attack will be reported every 11 seconds which is twice what it was in 2019 (every 19 seconds).
Netpluz Managed SOC - MSS Service 

The document discusses cybersecurity threats like ransomware, phishing, and data theft that can disrupt business operations and cause monetary or reputational losses. It then describes how a managed security services provider like SK infosec can monitor networks and systems 24/7, detect and respond to cyber threats through security analytics and a security operations center, and help organizations facing challenges with limited security resources. Case studies are provided showing how SK infosec's managed security services protected clients from a web-shell upload attack and C&C callback as part of an advanced persistent threat.
Overcoming Cyber Attacks

In this infographic, we look at the key cyber challenges faced by today's businesses, along with the major data breaches of 2013/14 and the effectiveness of traditional security solutions.
Next Dimension and Cisco | Solutions for PIPEDA Compliance

Duwayne Watson, a Cisco specialist from Ingram Micro, showcases various Data Security and Protection solutions such as: AMP, Umbrella, and CloudLock. These solutions can help your business remain compliant with PIPEDA legislation.
7 cyber security questions for boards

The cyber security job is everyone's business including the Board of Directors, even without a cyber security degree. Recent cyber security news proves that. According to several studies, Boards are getting it wrong and are leaving cyber awareness and risk management in the hands of the CEO, CISO, CTOs and cyber security companies. In a sense they are abdicating their responsibility to the shareholders. This slideshare proposes 7 questions every board should be asking their company executives abour IT security. They're not necessarily all encompassing and don't take the place of real cybersecurity training, but will drive the discussion to better and more complete understanding of strategic risk. Questions cover the basics of cyber security training, cyber policies, who briefs and when at board meetings. Thanks.
INFOGRAPHIC: Secure Computing as Threats Evolve

Symantec’s 2014 Internet Security Threat Report shows a marked decrease in many forms of malware and product vulnerabilities, plus faster responses to zero-day attacks. Symantec is blocking more attacks, more quickly, each year.
Containing the outbreak: The healthcare security pandemic

James Maude, Senior Security Engineer at Avecto examines the security state of play in the healthcare industry and why it’s now a prime target for hackers.
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study, The Cyber Security Readiness of Canadian Organizations, published February 2016. The full report can be downloaded at: scalar.ca/security-study-2016/
What's hot (20)
Verizon Data Breach Investigations Report (DBIR) 2017

Verizon Data Breach Investigations Report (DBIR) 2017
Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar

Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar
Next Dimension and Cisco | Solutions for PIPEDA Compliance

Next Dimension and Cisco | Solutions for PIPEDA Compliance
Containing the outbreak: The healthcare security pandemic

Containing the outbreak: The healthcare security pandemic
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
Similar to Infographic - Three steps to stopping advanced email threats
Why network based security

Traditional point solutions for cybersecurity defenses are often ineffective against modern threats, which rely on newly discovered vulnerabilities and complex multi-pronged attacks. Network-based security solutions offer enhanced protection by collecting threat intelligence from monitoring networks and analyzing suspicious activity, in order to identify threats earlier in their lifecycle. They also offload management burdens and provide expertise that individual organizations typically lack.
Assess risks to IT security.pptx

Cyber security involves implementing layers of security and protection against digital attacks across computers, devices, systems, and networks. Organizations use frameworks to detect and identify threats, protect assets, and recover from attacks. There are various types of cyber security threats including cybercrime, cyberterrorism, and cyberattacks. Performing risk assessments is important to understand potential security risks and impacts. Assessments involve identifying risks, analyzing likelihood and impacts, developing controls, documenting processes, and ongoing monitoring. Common security risks include viruses/malware, phishing, ransomware, and denial of service attacks. Organizations should use various security testing methods like audits, penetration testing, and vulnerability scanning to regularly evaluate security weaknesses.
Comprehensive Protection and Visibility into Advanced Email Attacks 

The latest version of the Symantec Cloud Email Security solution provides the strongest protection against Business Email Compromise with new, automated impersonation controls.
Securing Your Small Business Network

This document discusses security risks facing small businesses and recommends practices to secure small business networks. It outlines types of online risks like viruses, worms, hackers, spyware and phishing. It calculates the potential financial impact of security breaches and downtime. The document recommends security best practices and provides an overview of Symantec security solutions.
Email Security Overview

Websense offers several email security solutions to address modern threats. Their solutions leverage the Websense ThreatSeeker Intelligence Cloud and Advanced Classification Engine (ACE) to detect known and unknown malware, spam, and targeted attacks. Key capabilities include gateway threat analysis, point-of-click URL sandboxing, behavioral file sandboxing, and built-in data loss prevention. Websense solutions can be deployed in the cloud, on-premises with appliances, or in a hybrid model.
Balancing Cloud-Based Email Benefits With Security

This document discusses balancing the benefits of cloud-based email with security. It notes that while cloud email provides ease of use and cost savings, organizations must still maintain security. The document outlines some common security issues with cloud email like phishing, malware, and insider threats. It recommends that organizations evaluate cloud email providers based on their ability to protect against attacks, enforce encryption policies, and support a gradual migration to the cloud while integrating with other security tools. The document promotes Symantec Email Security.cloud as a solution that provides security, compliance, and flexibility for organizations adopting cloud-based email.
Email Security Market : Global Industry Trends and Forecast (2023-2032)

The global email security market is anticipated to grow at a substantial CAGR of 12.20% in the upcoming years. The global email security industry was estimated to be worth USD 3.10 billion in 2022 and was expected to be worth USD 6.93 billion by 2028.
What Ransomware Taught us in 2021?

As ransomware has become a matter of “when” rather than “if”, a ransomware recovery plan is as important as a business plan. With a documented and tested ransomware recovery plan, organizations, big and small, can make sure that their critical operations can recover quickly and critical information, such as PII, PHI, etc. is safe from ransomware.Ransomware attacks continue to grow in number, scale, and complexity. To make sure your critical data is protected, plan and prepare beforehand with backup and DR that uses air-gapping and immutability.
For more information visit : https://stonefly.com/storage/nas-storage
Overview of Ransomware Solutions from Protection to Detection and Response.pptx

Ransomware detection solutions generally focus on DLP, intrusion detection, anomaly detection with User and Entity Behavior Analysis (UEBA), and deep, real-time application of threat intelligence. These capabilities are generally the only way to proactively stop ransomware before it detonates. For example, monitoring email systems and networks for ransomware indicators may be the best way to prevent ransomware attacks from being successful. Call Us: +1 (978)-923-0040
PHISHING PROTECTION

What threatens us in cyberspace?
Phishing: typology of threats
Phishing protection
What is anti-phishing protection?
Website protection
Company and online fraud protection
Conclusion
Learn more about cyber attacks and find out how to secure yourself - https://hacken.live/2BwYyOo
Top 8 Types Of Cybersecurity Attacks.pptx

In recent years, cybersecurity attacks has appeared as a vital concern for businesses due to the growing number of threats. Safeguarding your business
https://www.bluechipgulf.ae/cybersecurity-attacks/
https://www.bluechipgulf.ae/cyber-security-solutions-dubai/
Copy of The Ongoing Threat of Ransomware on Small to Medium-Si

The document appears to be a survey assessing impediments to ransomware prevention for small businesses. It contains questions about preventative measures adopted, preparedness, barriers to prevention, security event log checking, weaknesses in detection, and measures being considered to prevent future attacks. Respondents indicate adopting training, backups, filters and secure storage. Identified challenges include limited resources, outdated documentation and keeping up with evolving threats.
Malware Attacks | How To Defend Organizations From It?

Malware or ransomware attacks How to defend organizations from them Learn in details about the tips and tricks of competing with it
Threat Intelligen.pptx

Threat intelligence provides information across a wide range of sources to assist associations with safeguarding their resources by working with a designated network safety procedure. Call Us: +1 (978)-923-0040
Cyber security.docx

The document discusses email phishing attacks and strategies to prevent them. It defines the attack surface as all possible entry points for unauthorized access, such as vulnerabilities, devices, and network nodes. Phishing works by tricking users into clicking links or entering login credentials on fake websites that look like legitimate ones. The document recommends educating users about phishing, punishing attackers legally, detecting and blocking phishing websites, and using technical methods like spam filters to stop phishing emails. It prioritizes improving remote access policies, separating personal and work data, frequently updating security systems, strong passwords, multi-factor authentication, and security training for employees.
Measures to Avoid Cyber-attacks

We are a new generation IT Software Company, helping our customers to optimize their IT investments, while preparing them for the best-in-class operating model, for delivering that “competitive edge” in their marketplace.
Measure To Avoid Cyber Attacks

The document discusses various measures that companies can take to avoid cyber attacks. It recommends that companies train employees on cybersecurity awareness, keep systems fully updated to patch vulnerabilities, implement zero trust and SSL inspection for security, examine permissions of frequently used apps, create mobile device management plans, use passwordless authentication and behavior monitoring, regularly audit networks to detect threats, develop strong data governance, automate security practices, and have an incident response plan in place. Taking a proactive approach to cybersecurity through multiple defensive strategies is crucial for businesses of all sizes to protect against increasing cyber attacks.
Splunk Discovery Day Hamburg - Security Session

This document discusses best practices for security strategies and Splunk's security offerings. It begins with an overview of the evolving threat landscape, noting that traditional defenses are no longer sufficient. It then outlines Splunk's data-driven security approach and demo. Splunk can complement or replace SIEMs by collecting, storing, searching, reporting on, and investigating machine data from various sources. It positions Splunk as a leader in security information and event management. The document concludes with next steps around discovery workshops and questions.
Securing Your Work from Home.pdf

With work from home becoming popular amid the pandemic, cyber-attacks by ransomware
operators have been on the rise and they may go on after any organization- an enterprise or a
small business, as long as they can gain access to them with ease.
No one today is a stranger to the word- Ransomware! But yes, there are certain tips and tricks
to safeguard yourself from such attacks on an organizational level. A good computer security
practice can help defend organizations against ransomware attacks.
Is Cloud the new home for Cyber Criminals? How to be Safe?

We remain on the edge of the digital age, where innovation moves rapidly, and our lives have been changed by modern computing. Digitization has brought about an amazing measure of data coursing through the internet. Handling that information has prompted a transformation by how we store and access data. The developing prevalence of cloud computing among organizations could prompt them being the following conceivable focus of cyber criminals. So, that means cloud computing is not safe? No, thats not the case! Since cloud computing is trending so cyber criminals are hitting more on it. To read more about how cyber criminals are stealing data, infecting businesses and how you can prevent it!
Similar to Infographic - Three steps to stopping advanced email threats (20)
Comprehensive Protection and Visibility into Advanced Email Attacks 

Comprehensive Protection and Visibility into Advanced Email Attacks
Balancing Cloud-Based Email Benefits With Security

Balancing Cloud-Based Email Benefits With Security
Email Security Market : Global Industry Trends and Forecast (2023-2032)

Email Security Market : Global Industry Trends and Forecast (2023-2032)
Overview of Ransomware Solutions from Protection to Detection and Response.pptx

Overview of Ransomware Solutions from Protection to Detection and Response.pptx
Copy of The Ongoing Threat of Ransomware on Small to Medium-Si

Copy of The Ongoing Threat of Ransomware on Small to Medium-Si
Malware Attacks | How To Defend Organizations From It?

Malware Attacks | How To Defend Organizations From It?
Is Cloud the new home for Cyber Criminals? How to be Safe?

Is Cloud the new home for Cyber Criminals? How to be Safe?
Recently uploaded
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

Predictive maintenance is a proactive approach that anticipates equipment failures before they happen. At the forefront of this innovative strategy is Artificial Intelligence (AI), which brings unprecedented precision and efficiency. AI in predictive maintenance is transforming industries by reducing downtime, minimizing costs, and enhancing productivity.
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
A Comprehensive Guide to DeFi Development Services in 2024

DeFi represents a paradigm shift in the financial industry. Instead of relying on traditional, centralized institutions like banks, DeFi leverages blockchain technology to create a decentralized network of financial services. This means that financial transactions can occur directly between parties, without intermediaries, using smart contracts on platforms like Ethereum.
In 2024, we are witnessing an explosion of new DeFi projects and protocols, each pushing the boundaries of what’s possible in finance.
In summary, DeFi in 2024 is not just a trend; it’s a revolution that democratizes finance, enhances security and transparency, and fosters continuous innovation. As we proceed through this presentation, we'll explore the various components and services of DeFi in detail, shedding light on how they are transforming the financial landscape.
At Intelisync, we specialize in providing comprehensive DeFi development services tailored to meet the unique needs of our clients. From smart contract development to dApp creation and security audits, we ensure that your DeFi project is built with innovation, security, and scalability in mind. Trust Intelisync to guide you through the intricate landscape of decentralized finance and unlock the full potential of blockchain technology.
Ready to take your DeFi project to the next level? Partner with Intelisync for expert DeFi development services today!
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Azure API Management to expose backend services securely

How to use Azure API Management to expose backend service securely
Trusted Execution Environment for Decentralized Process Mining

Presentation of the paper "Trusted Execution Environment for Decentralized Process Mining" given during the CAiSE 2024 Conference in Cyprus on June 7, 2024.
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on automated letter generation for Bonterra Impact Management using Google Workspace or Microsoft 365.
Interested in deploying letter generation automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Finale of the Year: Apply for Next One!

Presentation for the event called "Finale of the Year: Apply for Next One!" organized by GDSC PJATK
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Operating System Used by Users in day-to-day life.pptx

Dive into the realm of operating systems (OS) with Pravash Chandra Das, a seasoned Digital Forensic Analyst, as your guide. 🚀 This comprehensive presentation illuminates the core concepts, types, and evolution of OS, essential for understanding modern computing landscapes.
Beginning with the foundational definition, Das clarifies the pivotal role of OS as system software orchestrating hardware resources, software applications, and user interactions. Through succinct descriptions, he delineates the diverse types of OS, from single-user, single-task environments like early MS-DOS iterations, to multi-user, multi-tasking systems exemplified by modern Linux distributions.
Crucial components like the kernel and shell are dissected, highlighting their indispensable functions in resource management and user interface interaction. Das elucidates how the kernel acts as the central nervous system, orchestrating process scheduling, memory allocation, and device management. Meanwhile, the shell serves as the gateway for user commands, bridging the gap between human input and machine execution. 💻
The narrative then shifts to a captivating exploration of prominent desktop OSs, Windows, macOS, and Linux. Windows, with its globally ubiquitous presence and user-friendly interface, emerges as a cornerstone in personal computing history. macOS, lauded for its sleek design and seamless integration with Apple's ecosystem, stands as a beacon of stability and creativity. Linux, an open-source marvel, offers unparalleled flexibility and security, revolutionizing the computing landscape. 🖥️
Moving to the realm of mobile devices, Das unravels the dominance of Android and iOS. Android's open-source ethos fosters a vibrant ecosystem of customization and innovation, while iOS boasts a seamless user experience and robust security infrastructure. Meanwhile, discontinued platforms like Symbian and Palm OS evoke nostalgia for their pioneering roles in the smartphone revolution.
The journey concludes with a reflection on the ever-evolving landscape of OS, underscored by the emergence of real-time operating systems (RTOS) and the persistent quest for innovation and efficiency. As technology continues to shape our world, understanding the foundations and evolution of operating systems remains paramount. Join Pravash Chandra Das on this illuminating journey through the heart of computing. 🌟
Recently uploaded (20)
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
A Comprehensive Guide to DeFi Development Services in 2024

A Comprehensive Guide to DeFi Development Services in 2024
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
Azure API Management to expose backend services securely

Azure API Management to expose backend services securely
Trusted Execution Environment for Decentralized Process Mining

Trusted Execution Environment for Decentralized Process Mining
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Letter and Document Automation for Bonterra Impact Management (fka Social Sol...
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Operating System Used by Users in day-to-day life.pptx

Operating System Used by Users in day-to-day life.pptx
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Infographic - Three steps to stopping advanced email threats
- 1. To learn more about how to build an effective email security strategy, watch our webinar, “How to Build an Advanced Email Security Strategy” Step 2: Fight Advanced Malware-Based Threats Step 3: Respond to Threats Business email compromise (BEC) and credential phishing are effective because they rarely include malicious URLs or attachments. To fight malware-free attacks, ensure your security solution: 2/3of BEC attacks spoofed the sending domain of a targeted company (Proofpoint) Implements gateway policies to identify and block payload-free threats Implements email authentication policies to prevent all domain-spoofing attacks Leverages data loss prevention (DLP) technologies to keep sensitive information safe Malware-based threats delivered through malicious attachments and URLs continue to thrive, bypassing even “next-generation” defenses. No security solution can stop every attack. Failing to prepare for the inevitable breach can result in disrupted business, costlier cleanups, and more risk. 12%of targeted users click on malicious attachments (Verizon, 2016 DBIR) 03:45is the median time users click on malicious attachment (Verizon, 2016 DBIR) To fight latest advanced malware attacks, your team must: Get end-to-end visibility into every threat targeting your organization Invest in a cloud-based sandboxing solution that adapts to threats as they evolve Leverage predictive analytics to identify suspicious payloads chance that your company will experience a breach of at least 10,000 records within the next 24 months (Proofpoint) of companies have a budget in place for data breach mitigation (Osterman Research) of organizations would take hours, days or weeks to detect a breach (Osterman Research) 31% 75%22% A modern threat response solution should empower your team to: Automate time-consuming forensics-collection chores Contextualize data to understand and prioritize threats Remove malicious emails and quarantine infected endpoints Connect WITH CONFIDENCE 45%increase in BEC attacks in Q4 2016 (Proofpoint) 39%of organizations were hit with ransomware in 2016 (Osterman Research) $3.1bspent on BEC attacks since 2013 (FBI) Your biggest email security challenge isn't any single threat. It's the abundance of them. Ransomware, business email compromise (BEC), credential phishing, and more may be bypassing your security defenses. That puts your brand—and bottom line—at risk. Ready to fight back? Here are three steps to a complete defense: Step 1: Block Malware-Free Attacks THREE STEPS TO STOPPING ADVANCED EMAIL THREATS
