The document summarizes McAfee's Threats Report for the third quarter of 2013. Some key points:
- Mobile malware increased 33% while overall new malware exceeded 20 million. New ransomware and rootkits also rose.
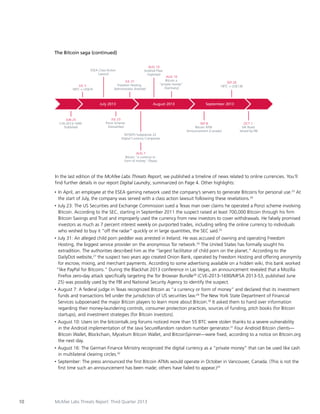
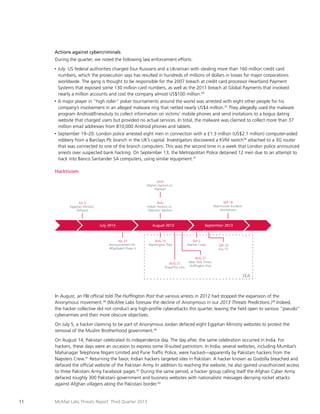
- Digital currencies like Bitcoin are increasingly used by cybercriminals for money laundering and anonymous transactions on dark web markets. The shutdown of Silk Road prompted new illegal sites.
- The "Deep Web" contains unregulated online markets selling illegal drugs, weapons, credit cards, and even murder-for-hire services accessible through Tor and paid with Bitcoin.
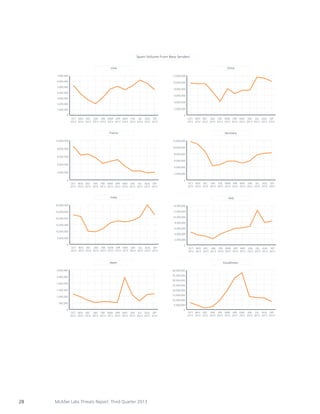
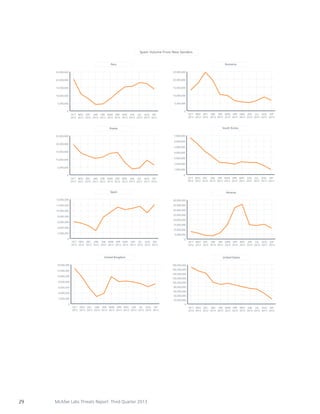
- Hacktivism and political hacking increased, while spam volume reached its highest level since 2010. Browser