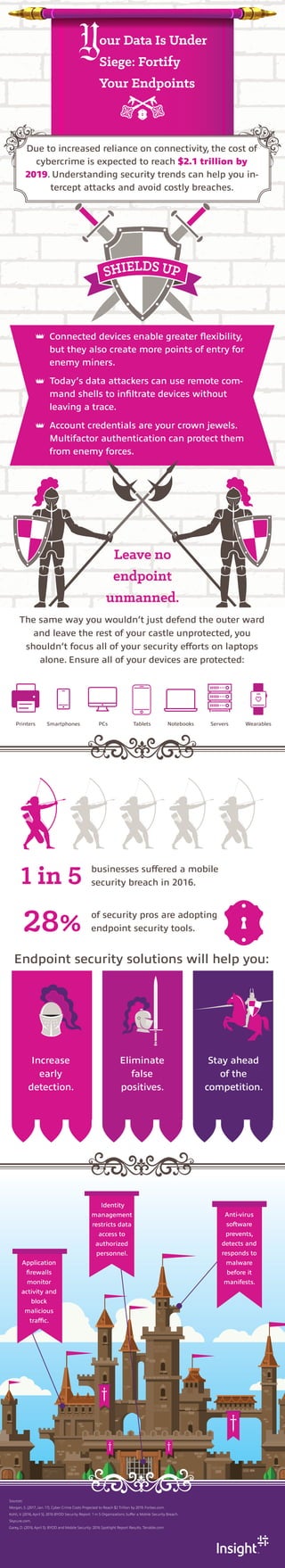
Your Data Is Under Siege: Fortify Your Endpoints
•
0 likes•46 views
1 in 5 businesses suffered a security breach in 2016. See the trends and learn how you can stop malware in its tracks.
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
Verizon Data Breach Investigations Report (DBIR) 2017

Verizon Data Breach Investigations Report (DBIR) 2017
Next-level mobile app security: A programmatic approach

Next-level mobile app security: A programmatic approach
How to Reduce Avenues of Attack: Using Intel to Plan for Cyber Threats in 2017

How to Reduce Avenues of Attack: Using Intel to Plan for Cyber Threats in 2017
Similar to Your Data Is Under Siege: Fortify Your Endpoints
Similar to Your Data Is Under Siege: Fortify Your Endpoints (20)
Top Positive and Negative Impacts of AI & ML on Cybersecurity

Top Positive and Negative Impacts of AI & ML on Cybersecurity
Security - intelligence - maturity-model-ciso-whitepaper

Security - intelligence - maturity-model-ciso-whitepaper
2021 Cybersecurity Recap: How Did We Fare Last Year? 

2021 Cybersecurity Recap: How Did We Fare Last Year?
Mobile Security Threats In Organisations: 4 Challenges To Navigate And Solve

Mobile Security Threats In Organisations: 4 Challenges To Navigate And Solve
Corporate America is Being ATTACKED and the Entry Vector May be Surprising

Corporate America is Being ATTACKED and the Entry Vector May be Surprising
More from Insight
More from Insight (20)
Infographic | The Growing Need for Fast, Secure Telehealth

Infographic | The Growing Need for Fast, Secure Telehealth
Infographic | 4 Reasons to Make the Switch to Chrome OS With Insight

Infographic | 4 Reasons to Make the Switch to Chrome OS With Insight
Take a Holistic Approach to Securing Connected Manufacturing

Take a Holistic Approach to Securing Connected Manufacturing
Infographic | Software Facilitates Smart(er) Manufacturing

Infographic | Software Facilitates Smart(er) Manufacturing
Infographic | How It Works: Community Wireless Broadband

Infographic | How It Works: Community Wireless Broadband
An Ounce of Prevention: How Healthcare Organizations Can Stop Cybercrime in I...

An Ounce of Prevention: How Healthcare Organizations Can Stop Cybercrime in I...
Welcome to the Future of Work: The Hybrid Workplace

Welcome to the Future of Work: The Hybrid Workplace
Building a Modern Workplace: The Value Add of Technology Optimization

Building a Modern Workplace: The Value Add of Technology Optimization
Recently uploaded
Recently uploaded (20)
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
Your Data Is Under Siege: Fortify Your Endpoints
- 1. our Data Is Under Siege: Fortify Your Endpoints Due to increased reliance on connectivity, the cost of cybercrime is expected to reach $2.1 trillion by 2019. Understanding security trends can help you in- tercept attacks and avoid costly breaches. Connected devices enable greater flexibility, but they also create more points of entry for enemy miners. Today’s data attackers can use remote com- mand shells to infiltrate devices without leaving a trace. Account credentials are your crown jewels. Multifactor authentication can protect them from enemy forces. Leave no endpoint unmanned. The same way you wouldn’t just defend the outer ward and leave the rest of your castle unprotected, you shouldn’t focus all of your security efforts on laptops alone. Ensure all of your devices are protected: 1 in 5 businesses suffered a mobile security breach in 2016. 28% of security pros are adopting endpoint security tools. Endpoint security solutions will help you: Increase early detection. Eliminate false positives. Stay ahead of the competition. Printers Smartphones PCs Tablets Notebooks Servers Wearables Sources: Morgan, S. (2017, Jan. 17). Cyber Crime Costs Projected to Reach $2 Trillion by 2019. Forbes.com. Kohli, V. (2016, April 5). 2016 BYOD Security Report: 1 in 5 Organizations Suffer a Mobile Security Breach. Skycure.com. Garey, D. (2016, April 5). BYOD and Mobile Security: 2016 Spotlight Report Results. Tenable.com. Application firewalls monitor activity and block malicious traffic. Identity management restricts data access to authorized personnel. Anti-virus software prevents, detects and responds to malware before it manifests.
