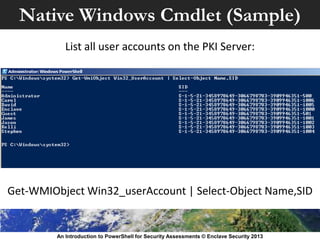
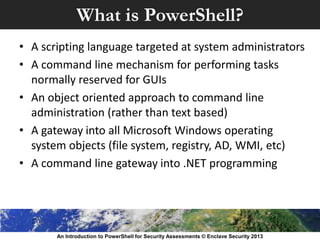
This document introduces PowerShell as a tool for security assessments. It notes that bringing outside tools to a system can cause issues, but using native operating system tools avoids these problems. PowerShell is presented as a potential solution as it is available natively on Windows systems and allows accessing operating system objects without downloading software. The document then provides an overview of PowerShell and its capabilities before presenting a case study of how to use PowerShell to assess a Microsoft Active Directory Certificate Services server.
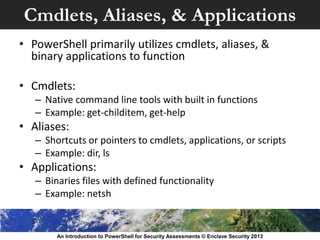
![Accessing .NET Objects
• PowerShell can also even utilize .NET libraries
• Anything .NET can do, PowerShell can also
• There is a fuzzy line between PowerShell & VB.NET
• Both of the following commands are the same:
– [datetime]::now
– Get-Date
An Introduction to PowerShell for Security Assessments © Enclave Security 2013](https://image.slidesharecdn.com/anintroductiontopowershellforsecurityassessments-130827143346-phpapp02/85/An-Introduction-to-PowerShell-for-Security-Assessments-12-320.jpg)