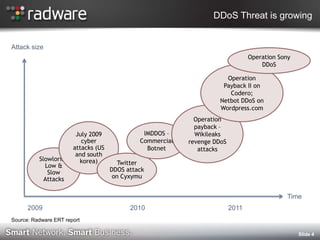
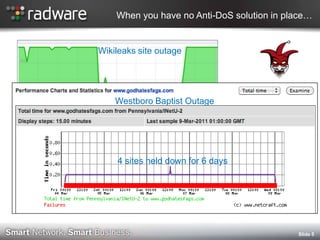
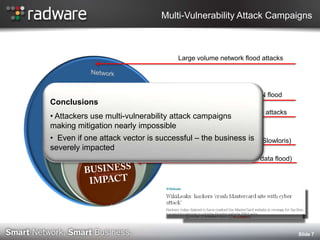
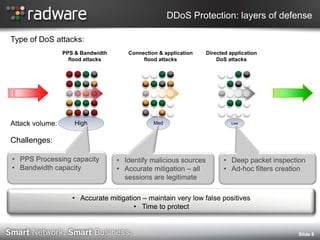
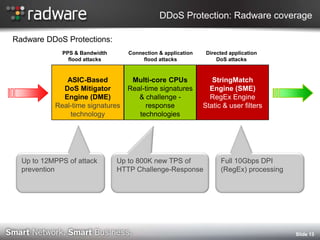
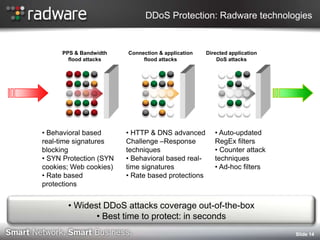
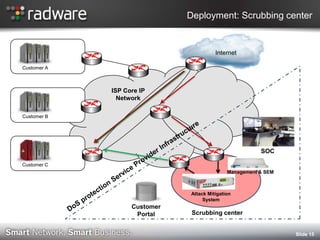
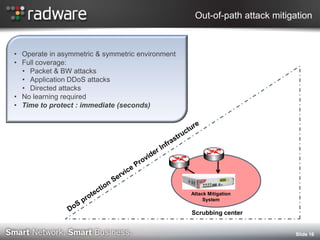
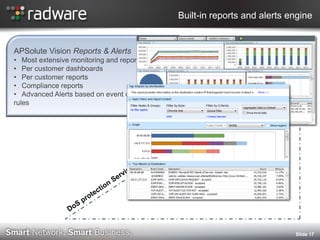
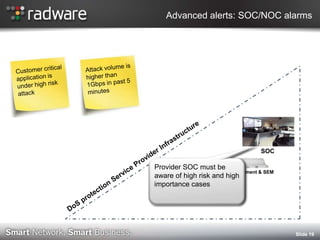
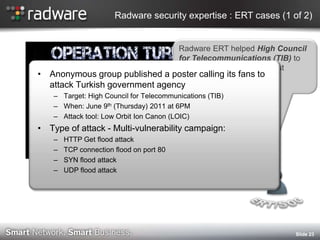
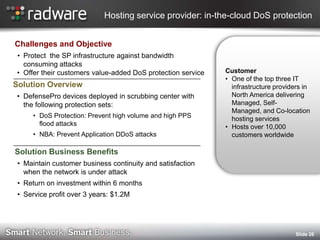
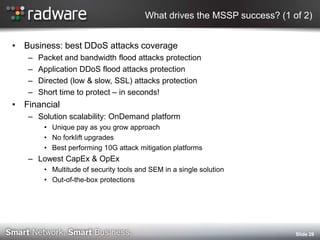
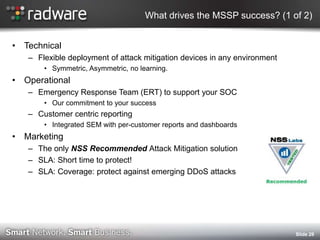
The document discusses advanced DDoS protection solutions for service providers and managed security service providers (MSSPs). It outlines key factors for MSSP success, including true DDoS protection capabilities, scalability, flexible deployment options, customer-centric reporting, and marketing differentiation. Radware's solution is presented as providing industry-leading coverage against various attack types, short time to protection, out-of-the-box protections, and support from Radware's emergency response team. A case study highlights how Radware helped a major hosting provider implement in-cloud DDoS protection and offer the service to customers.