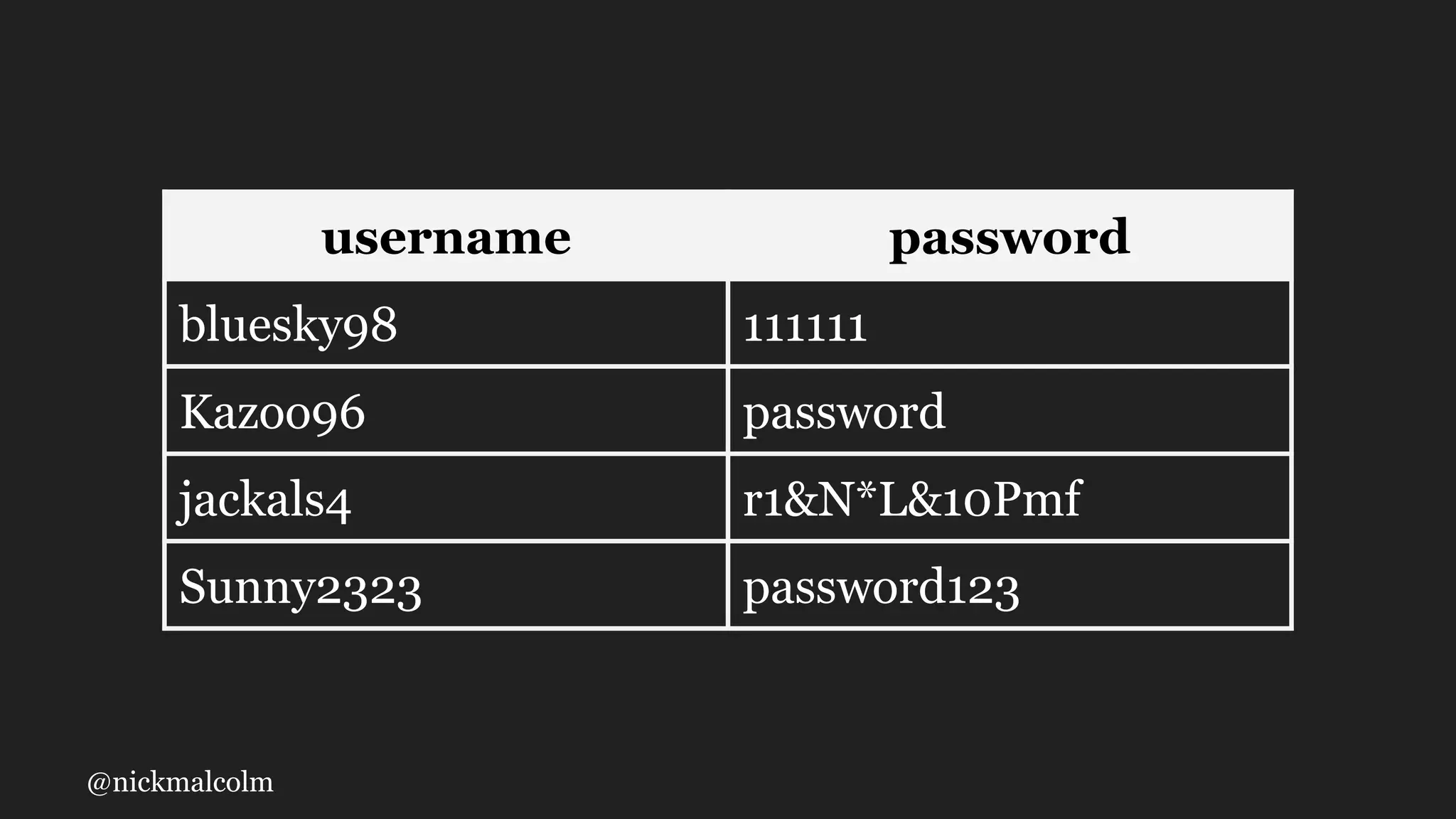
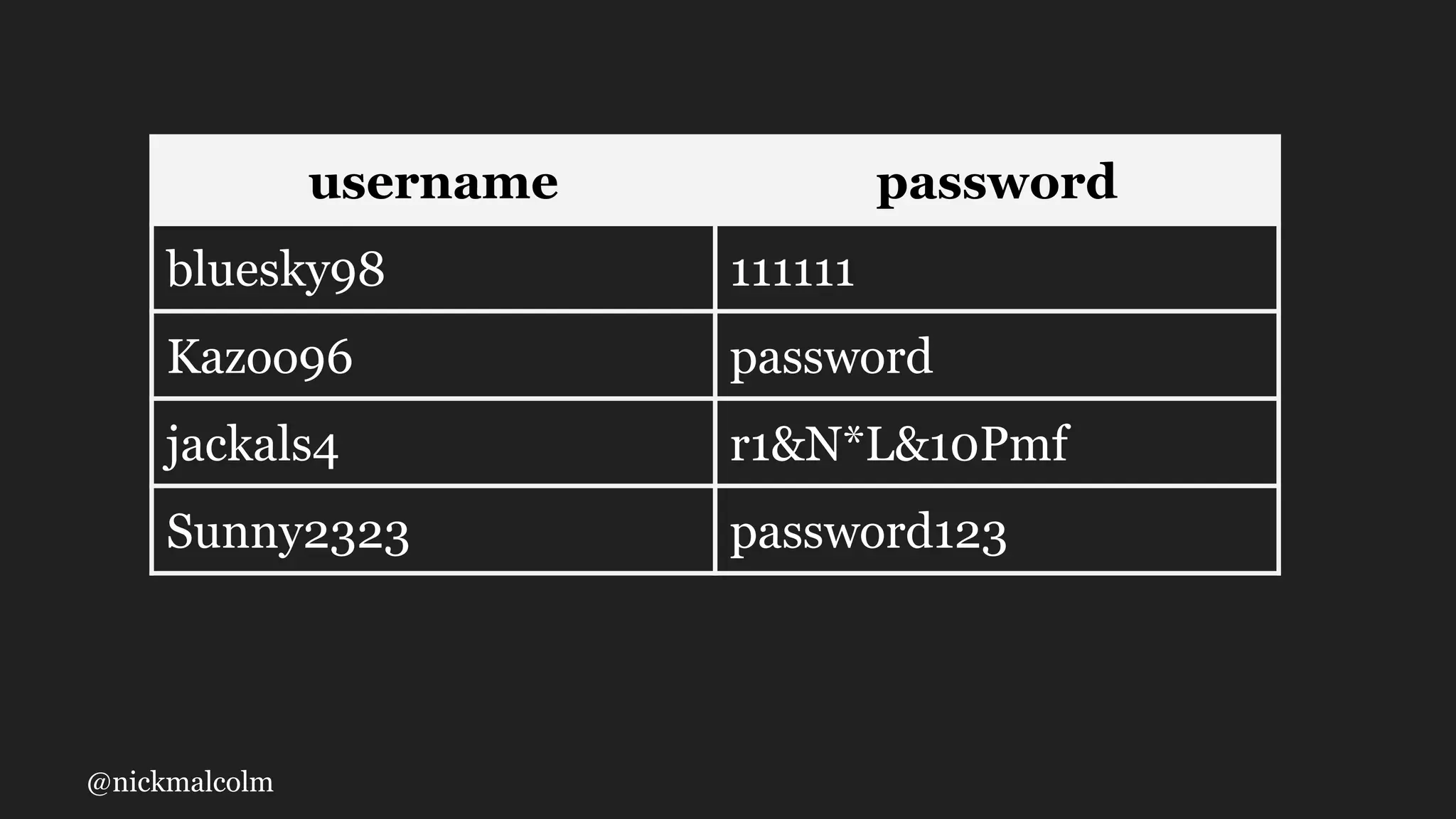
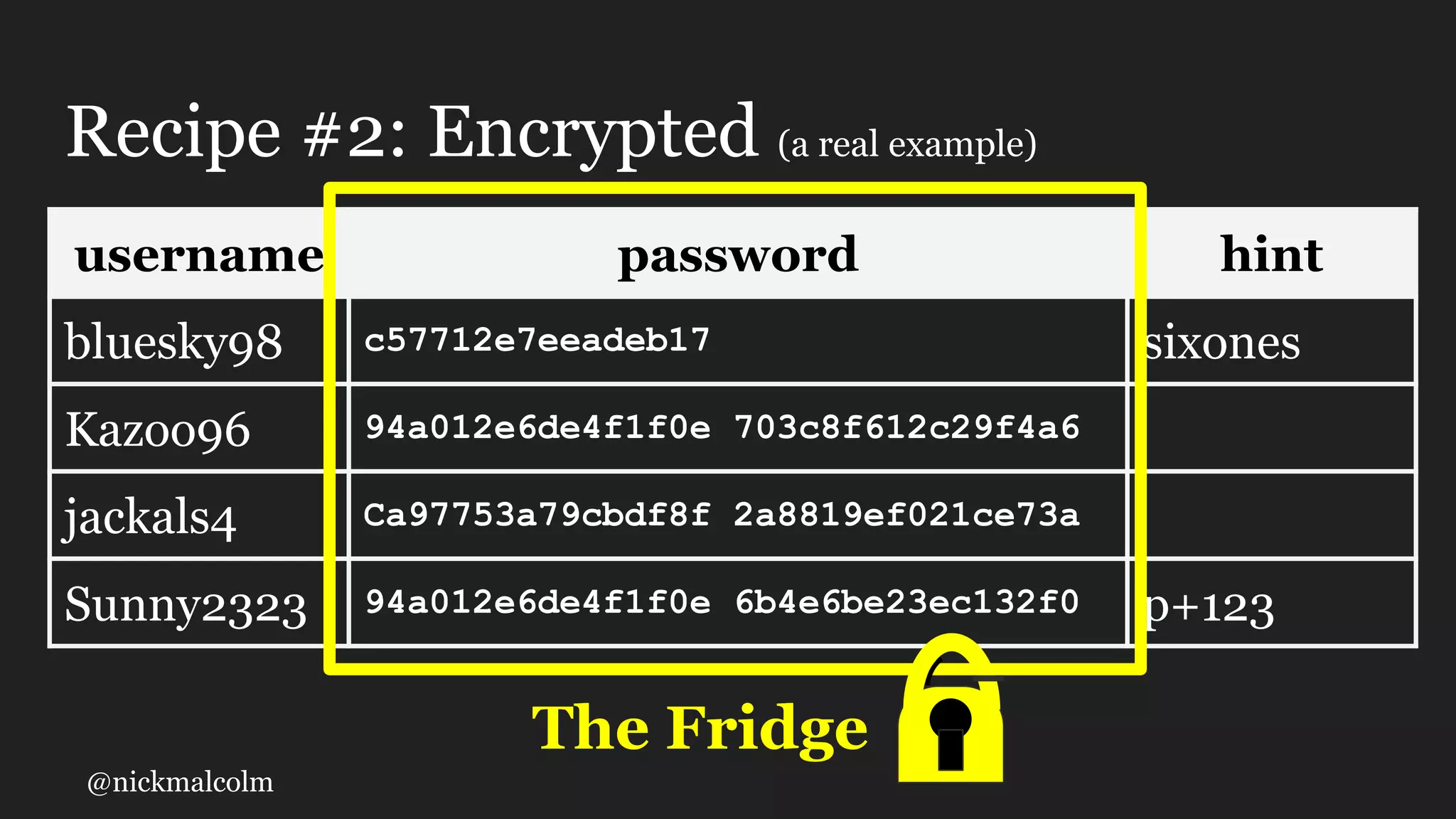
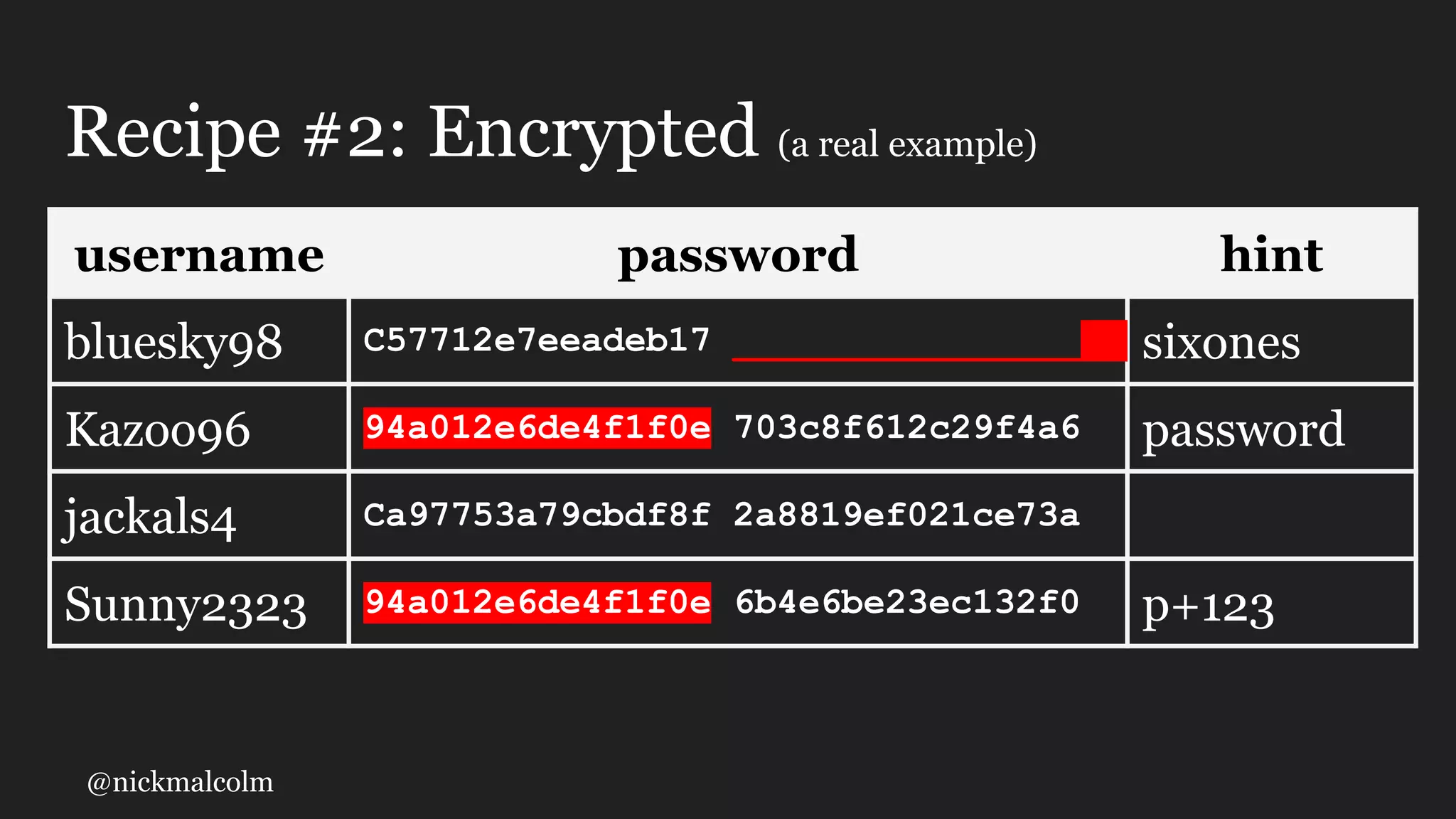
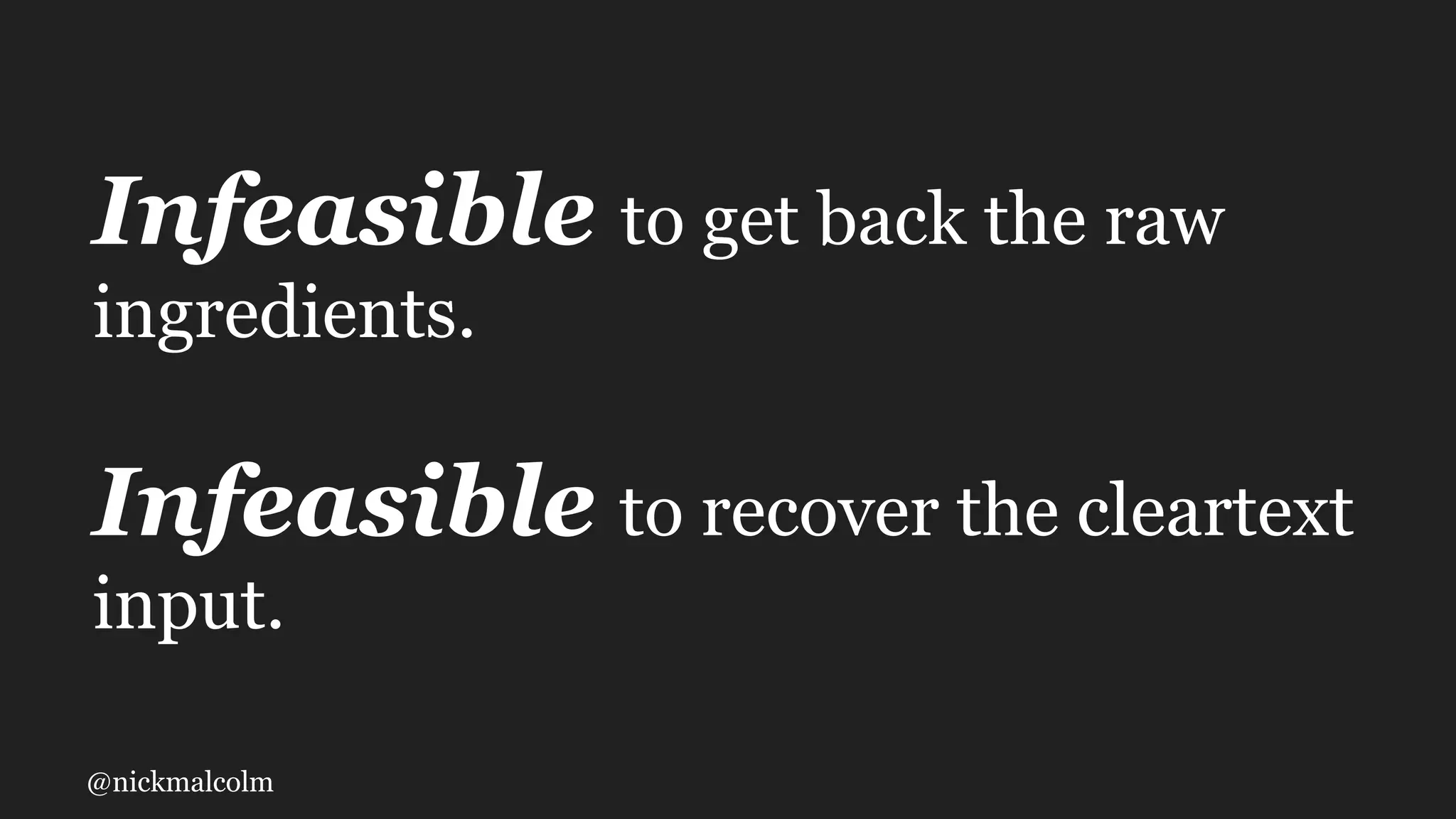
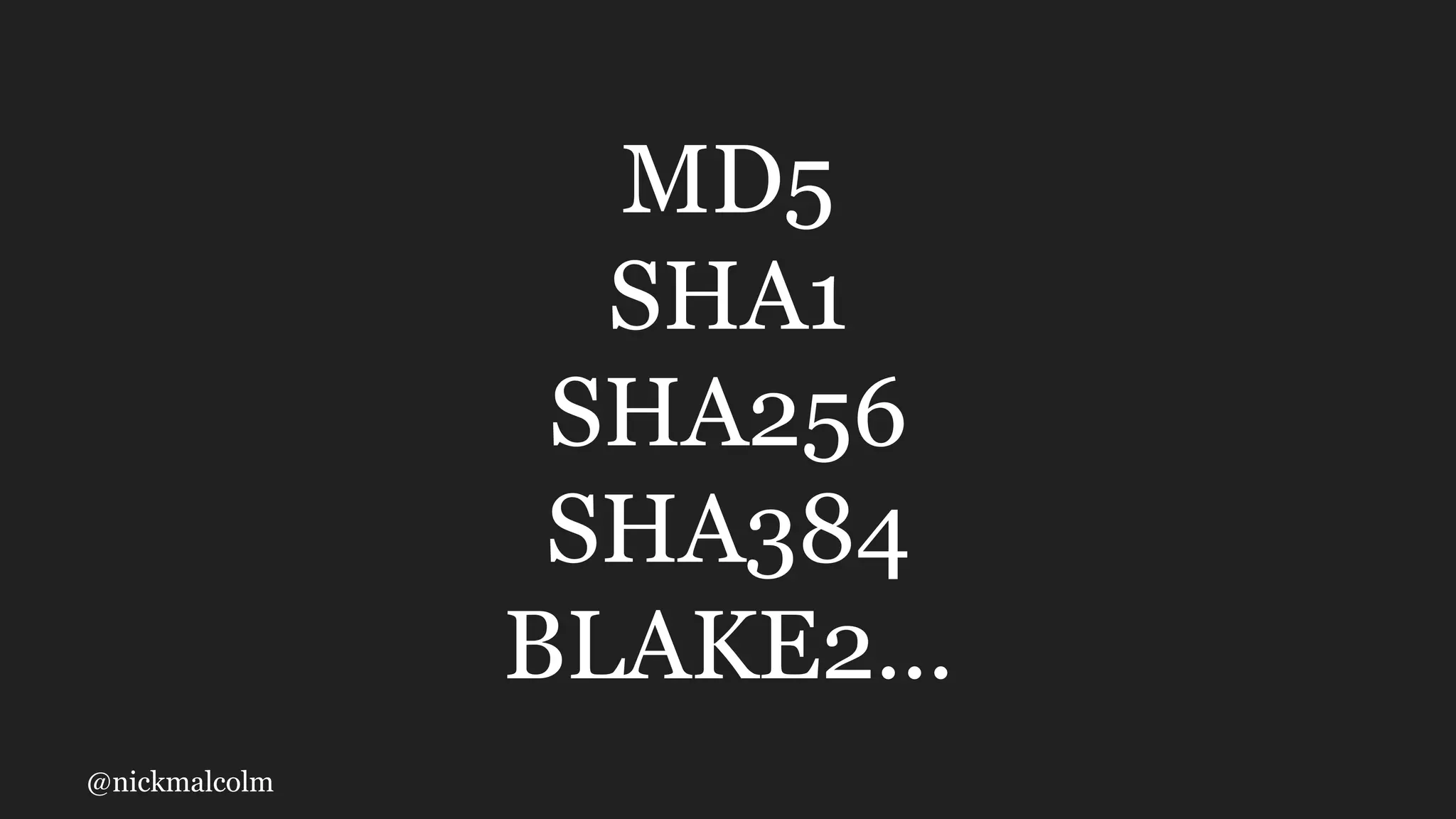
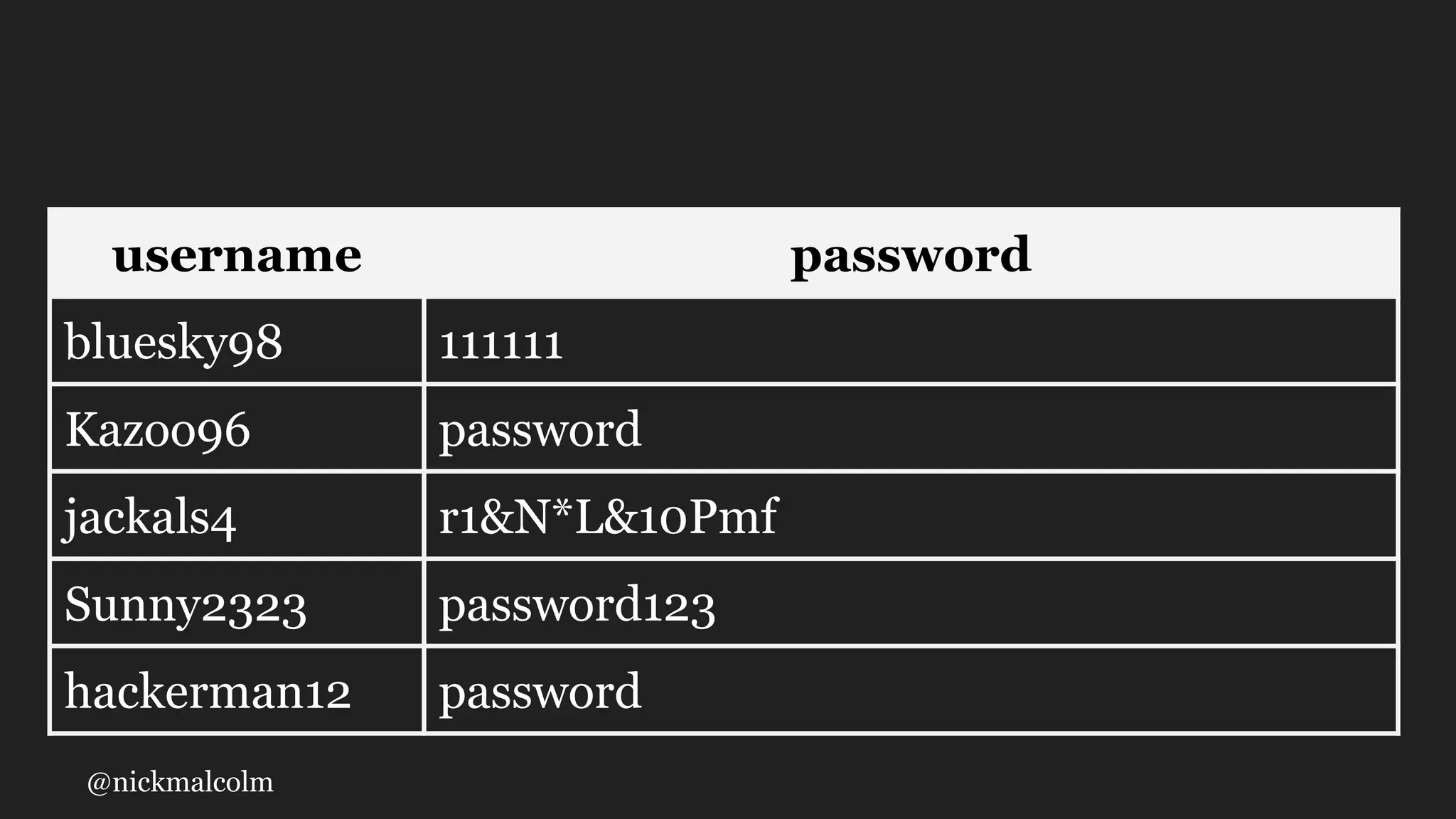
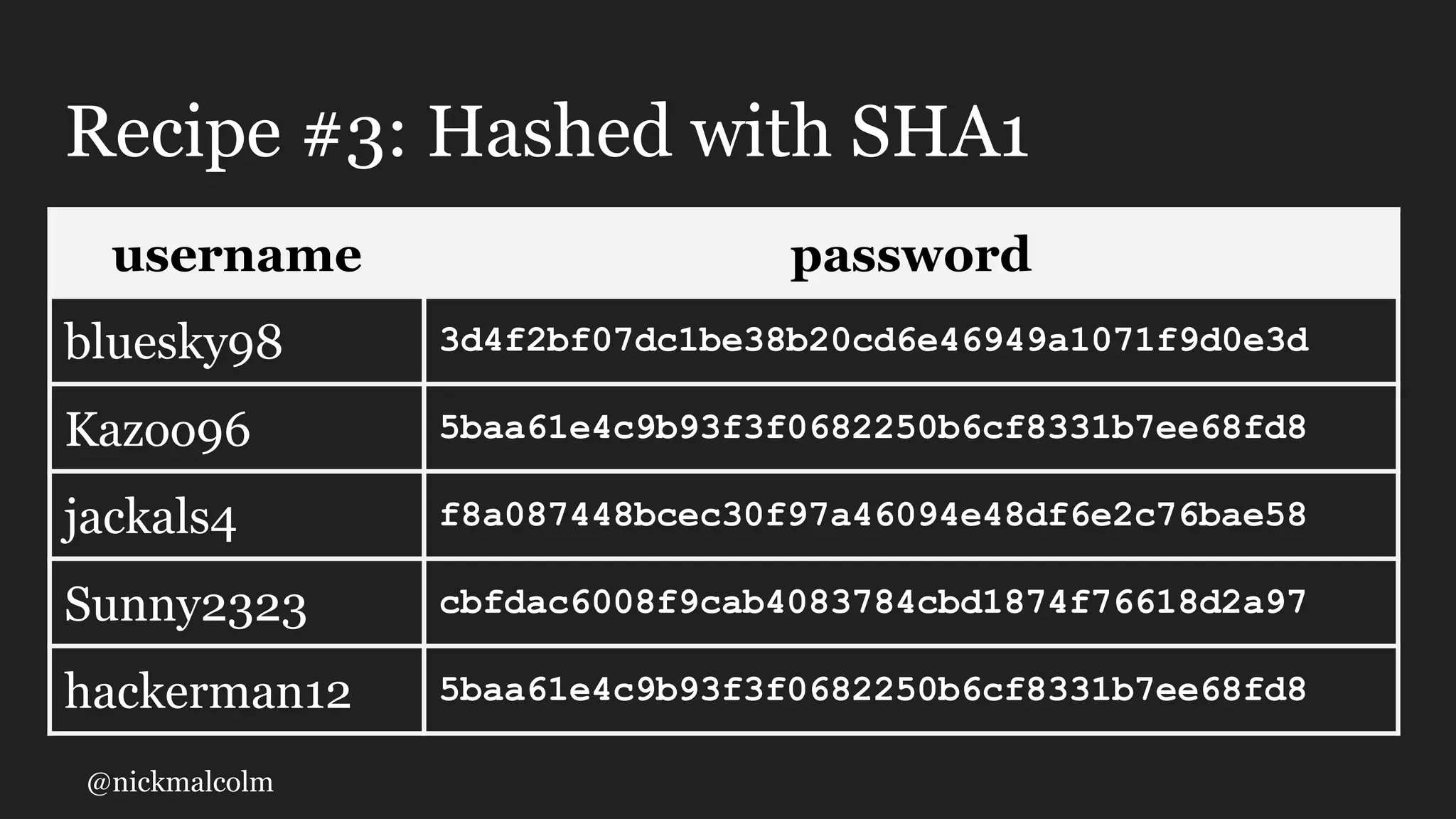
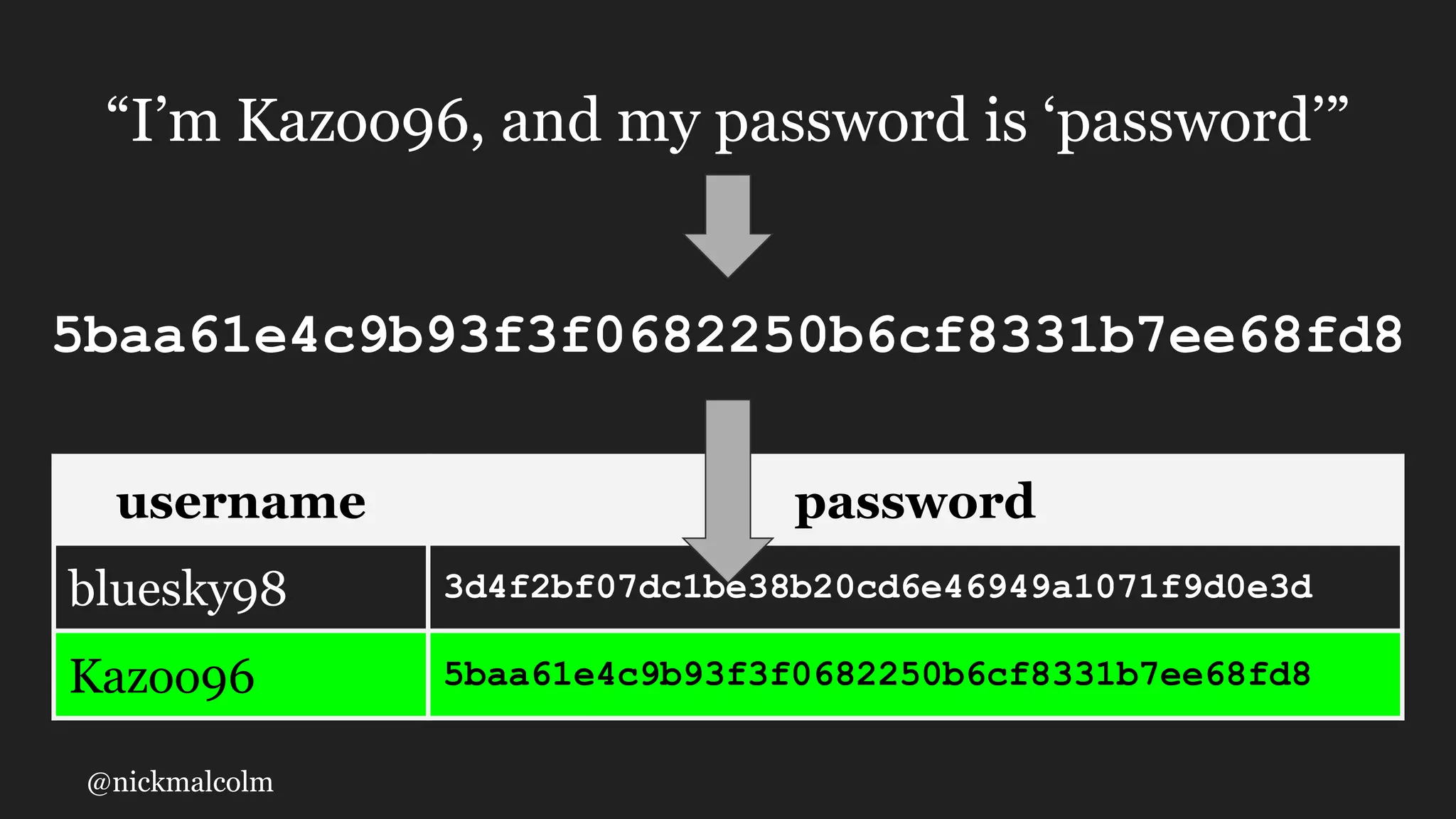
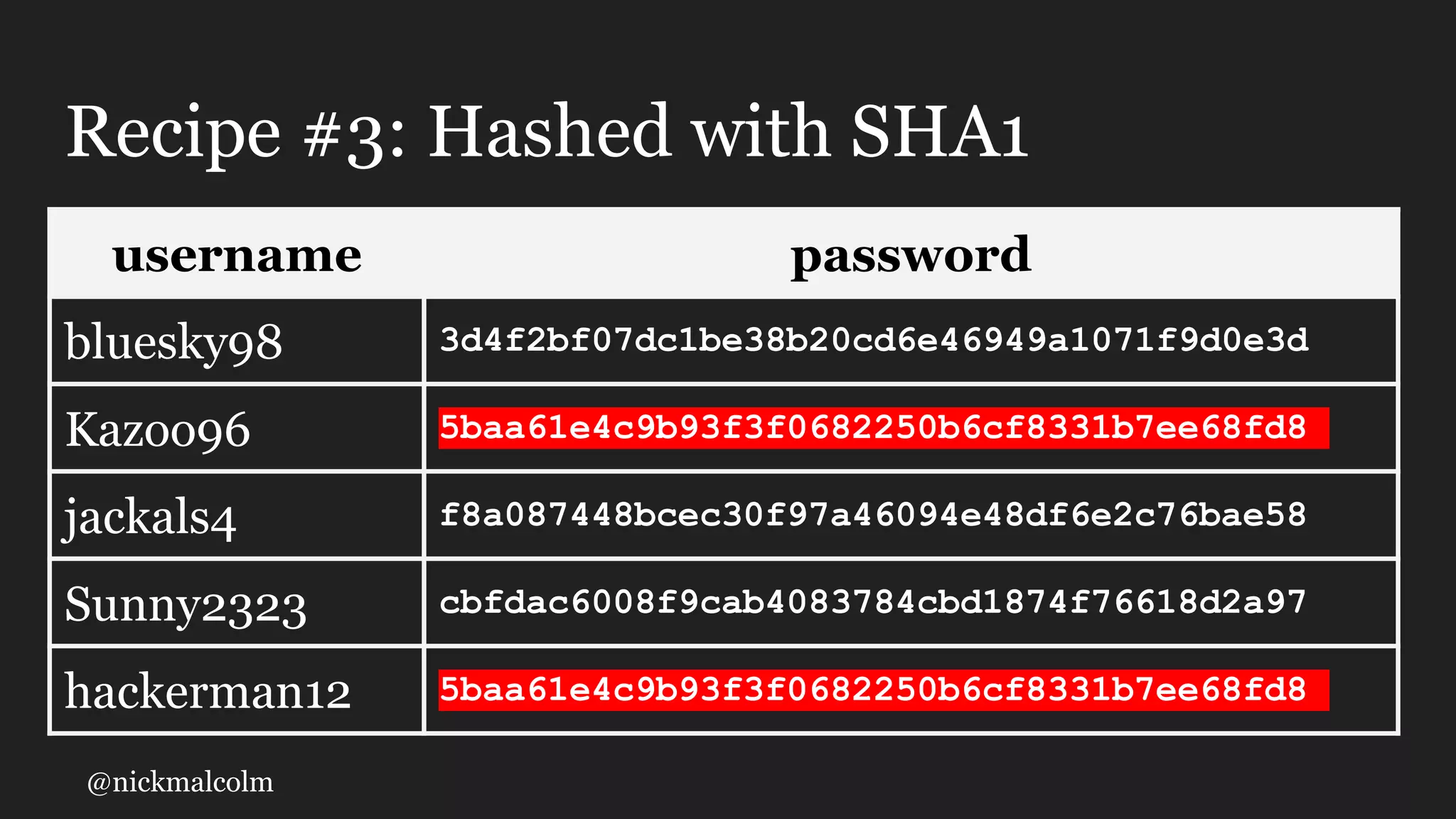
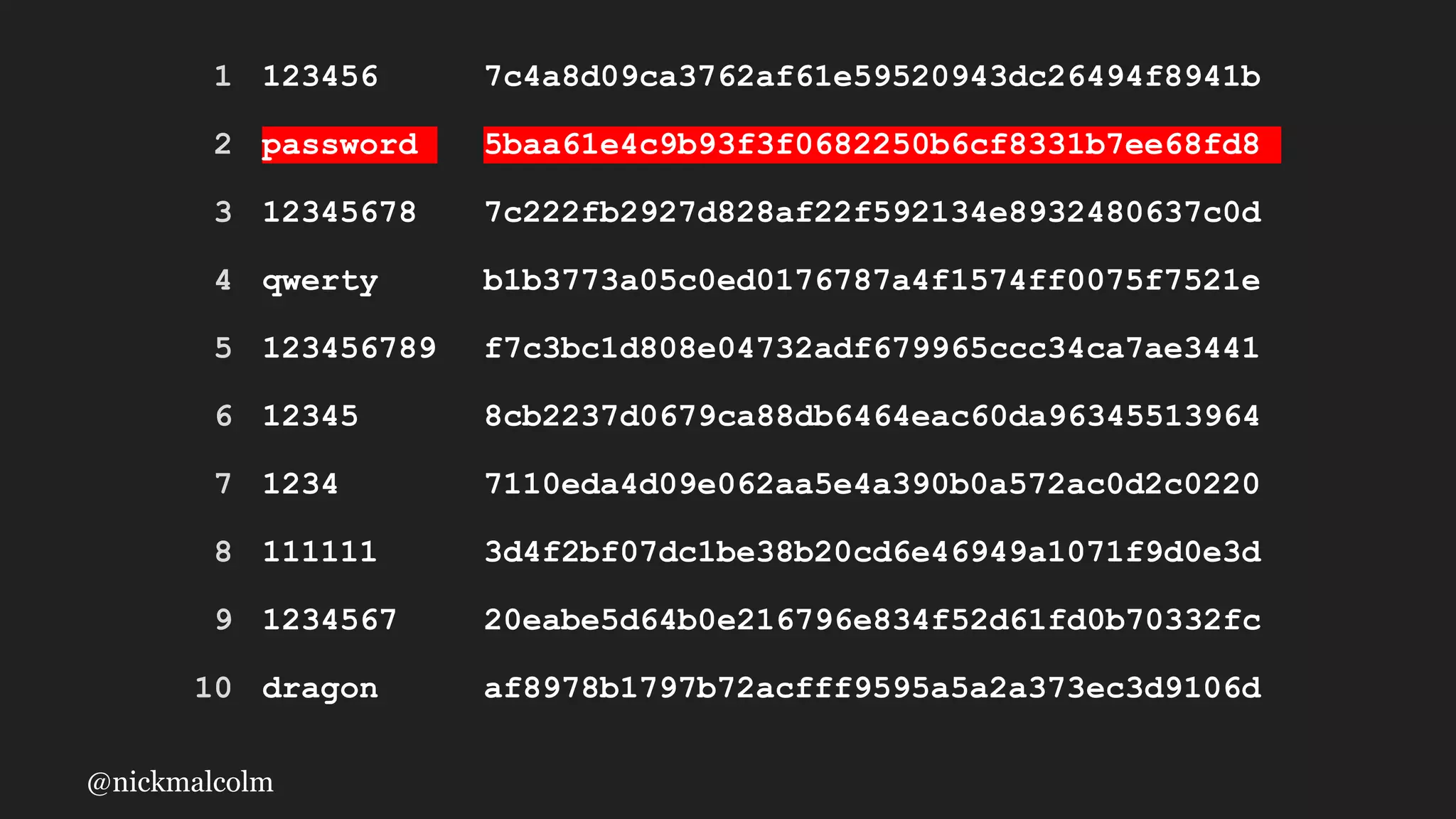
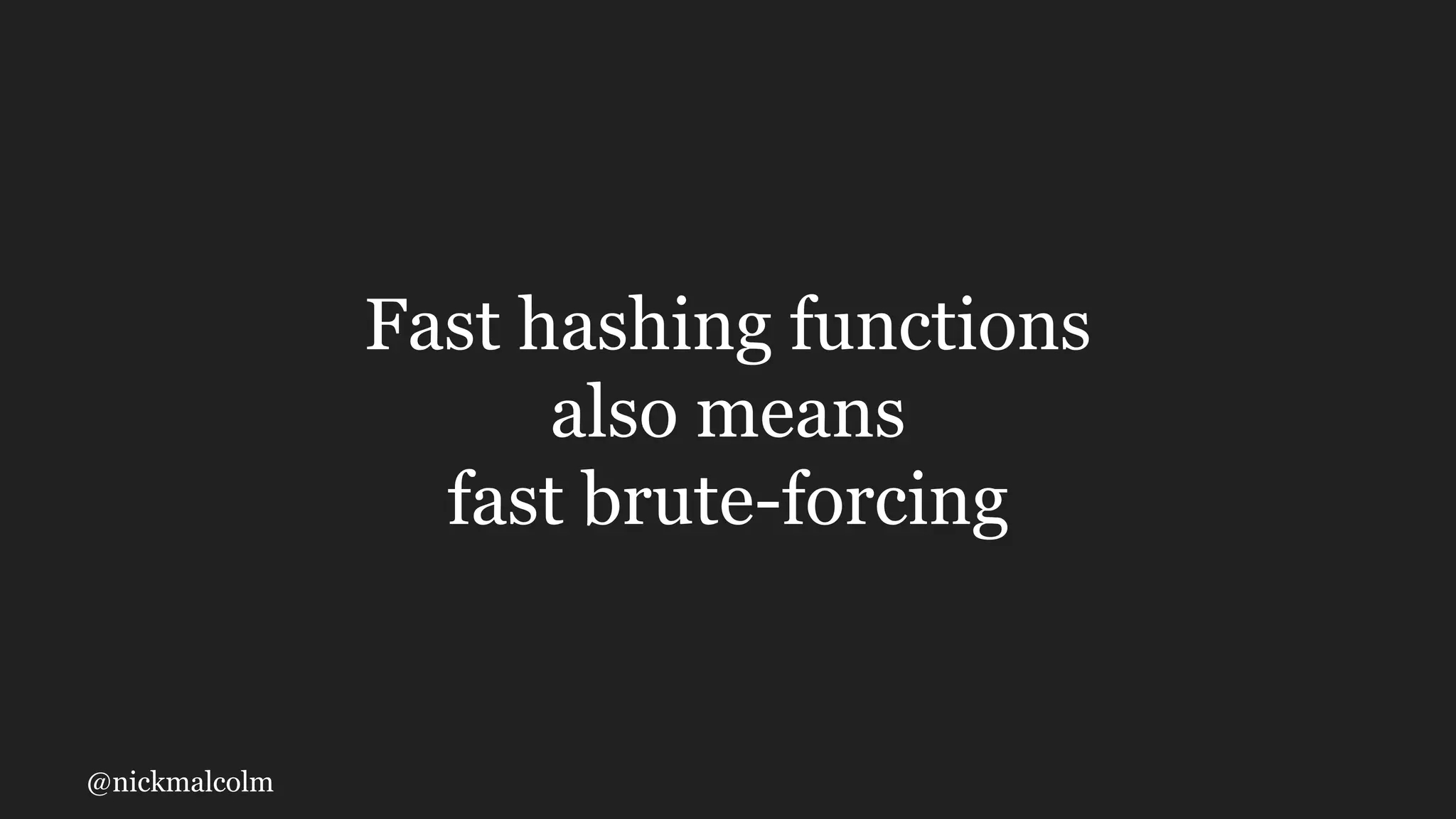
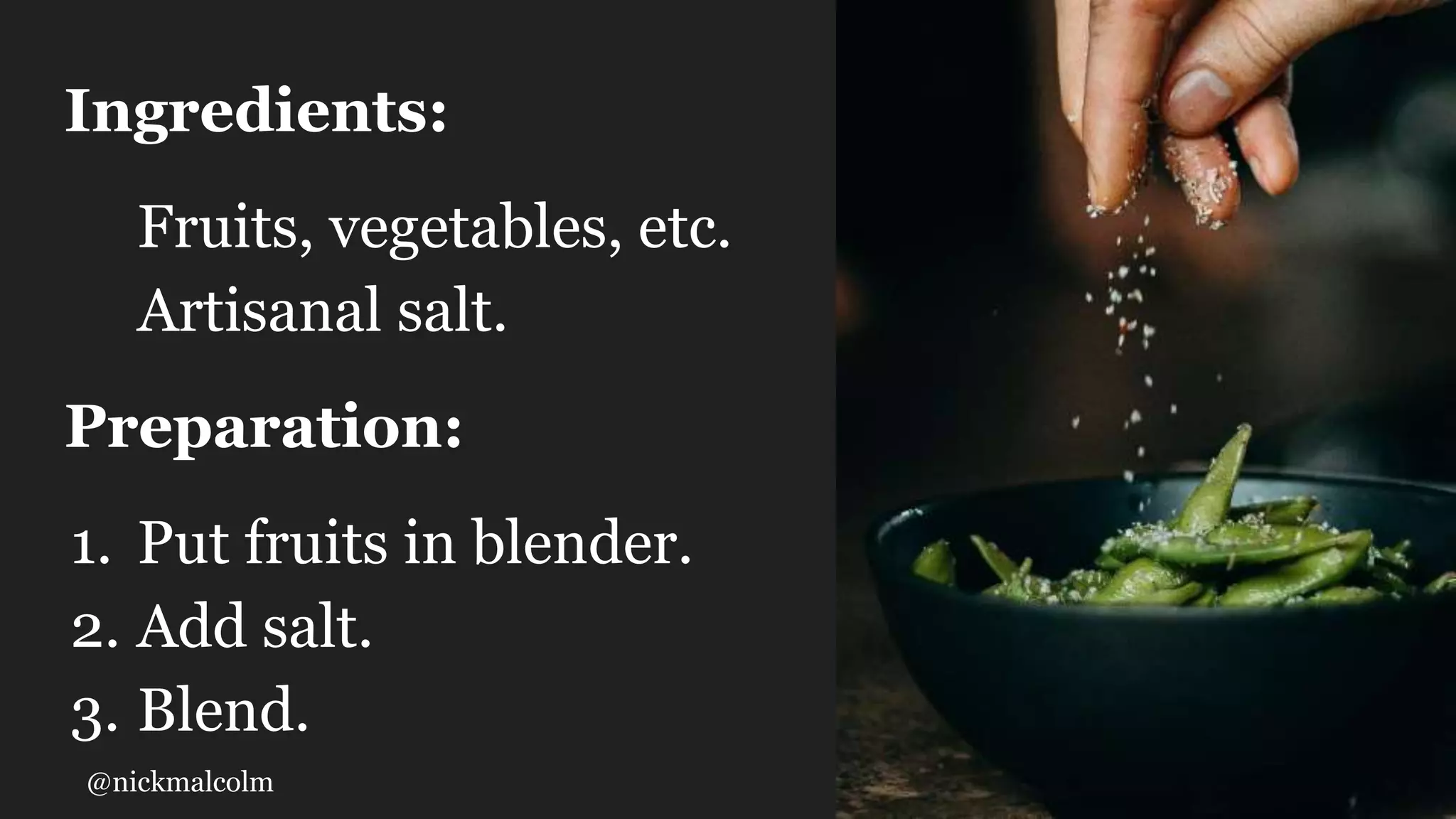
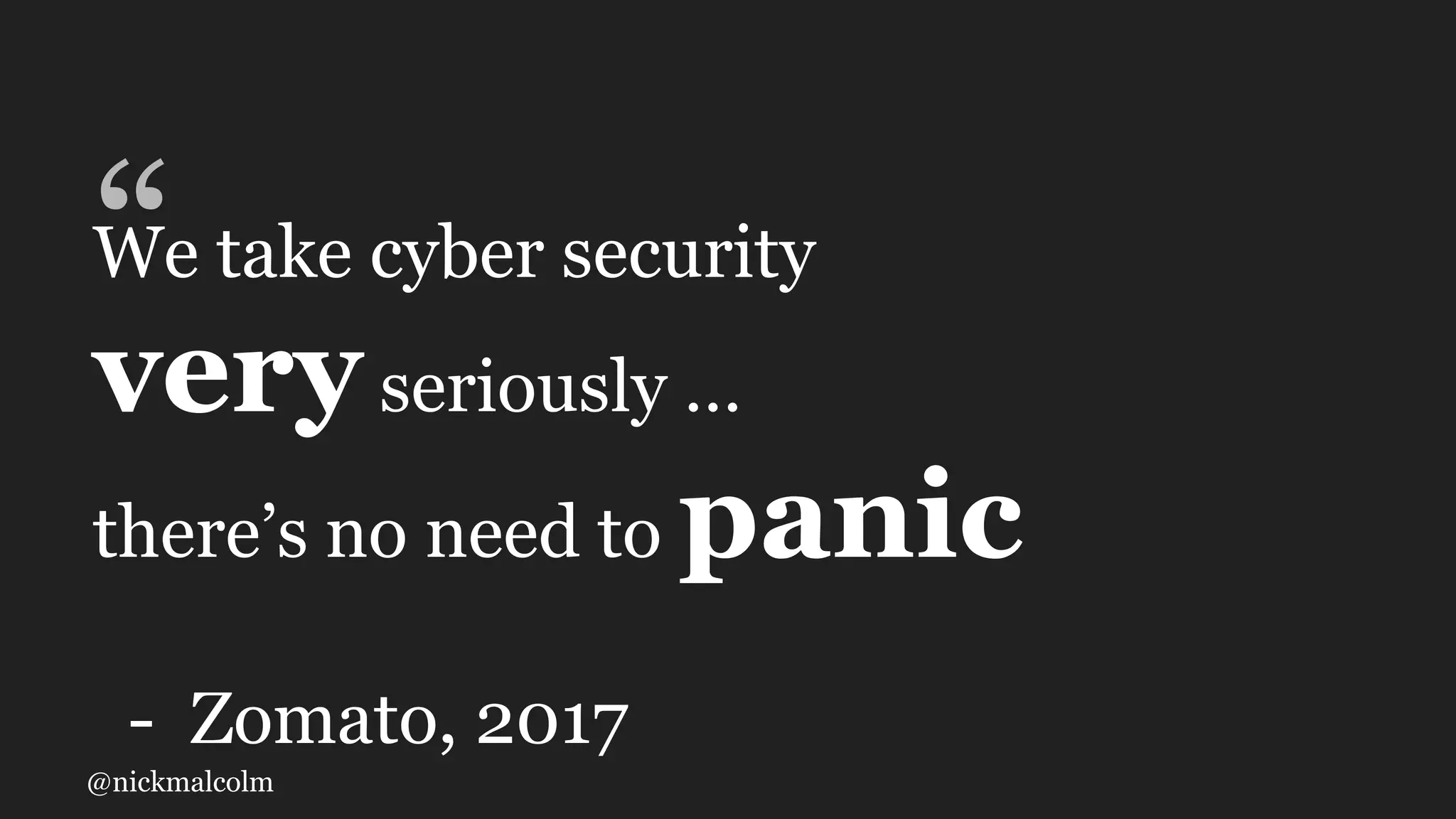
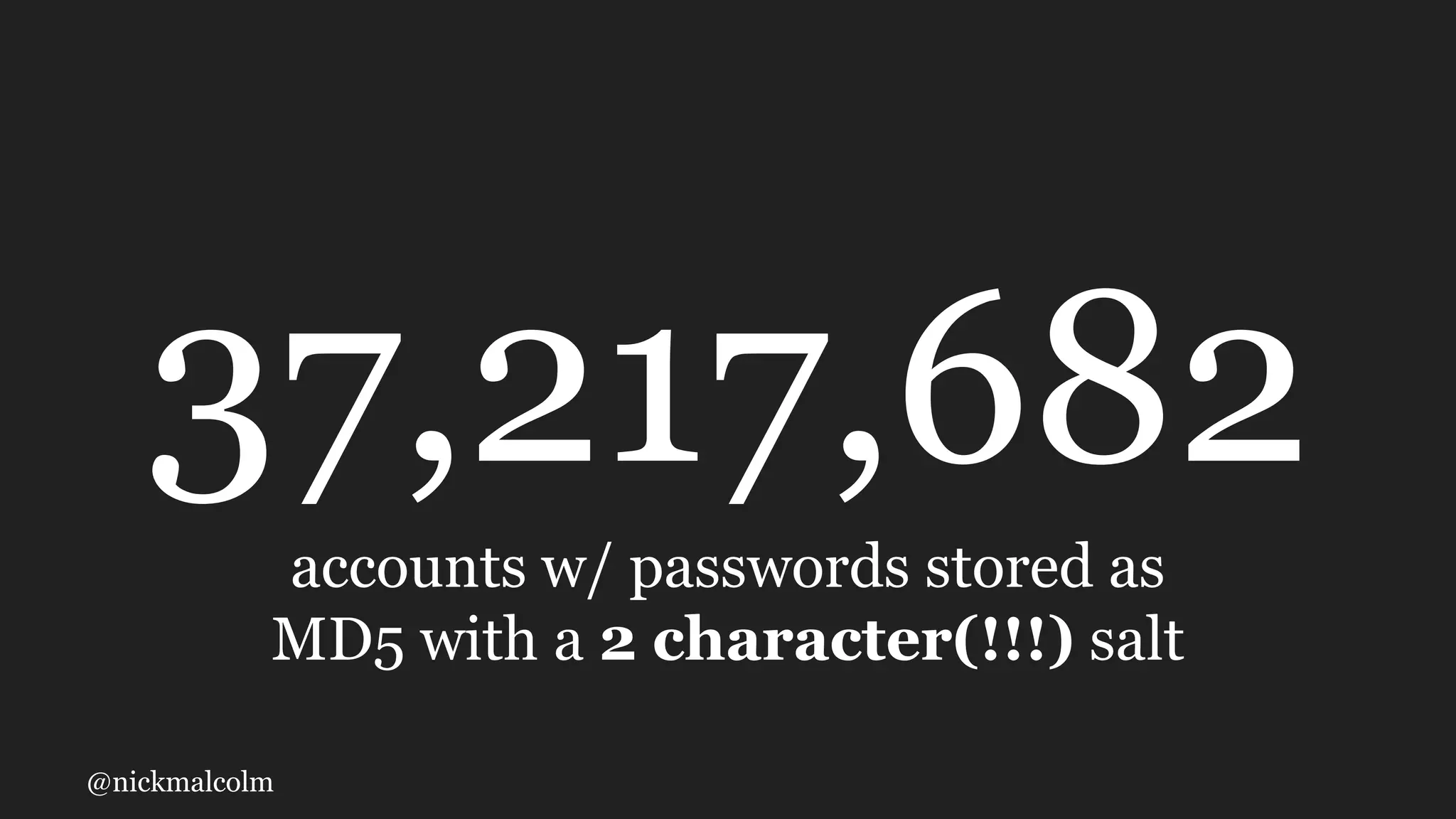
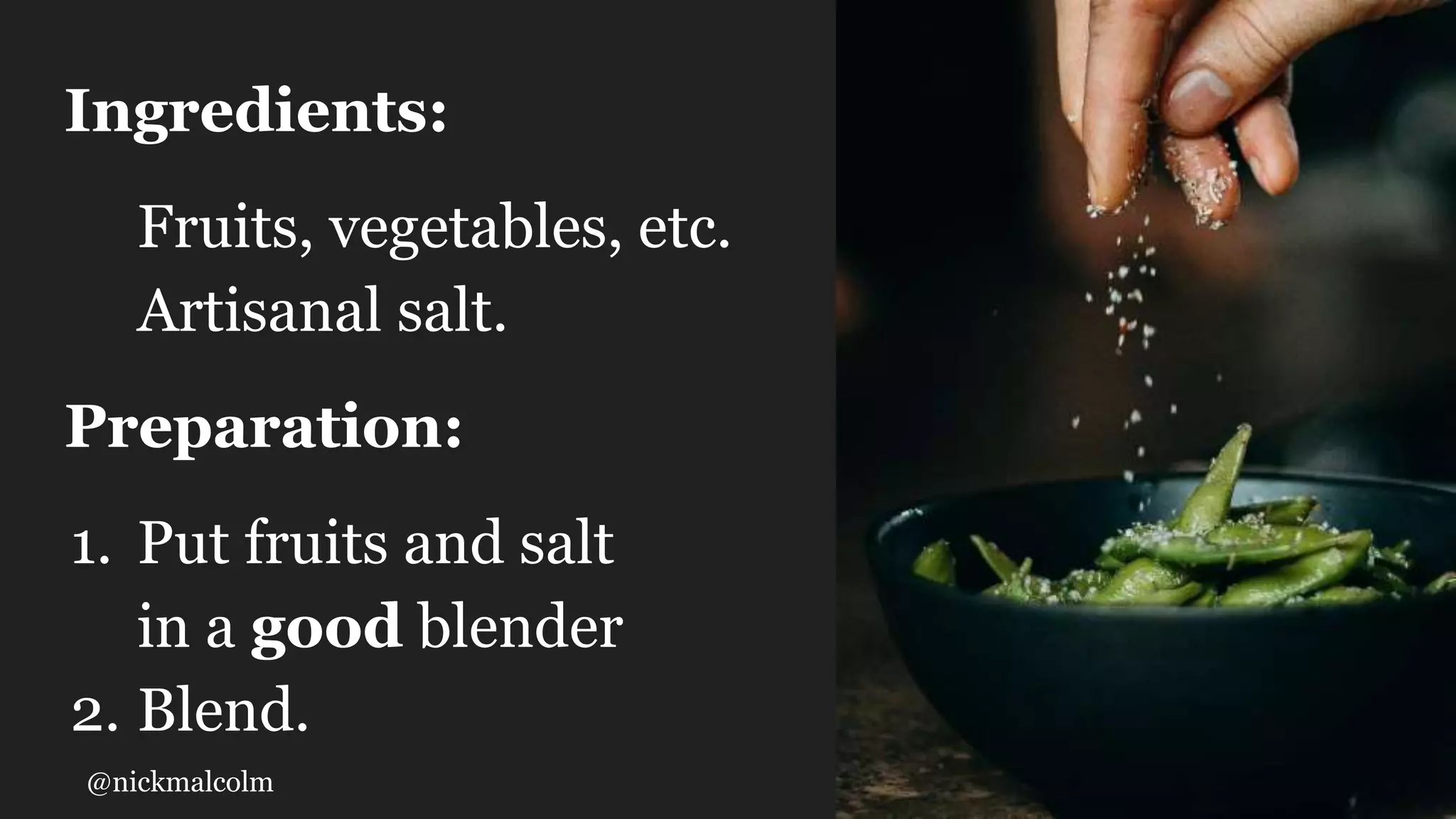
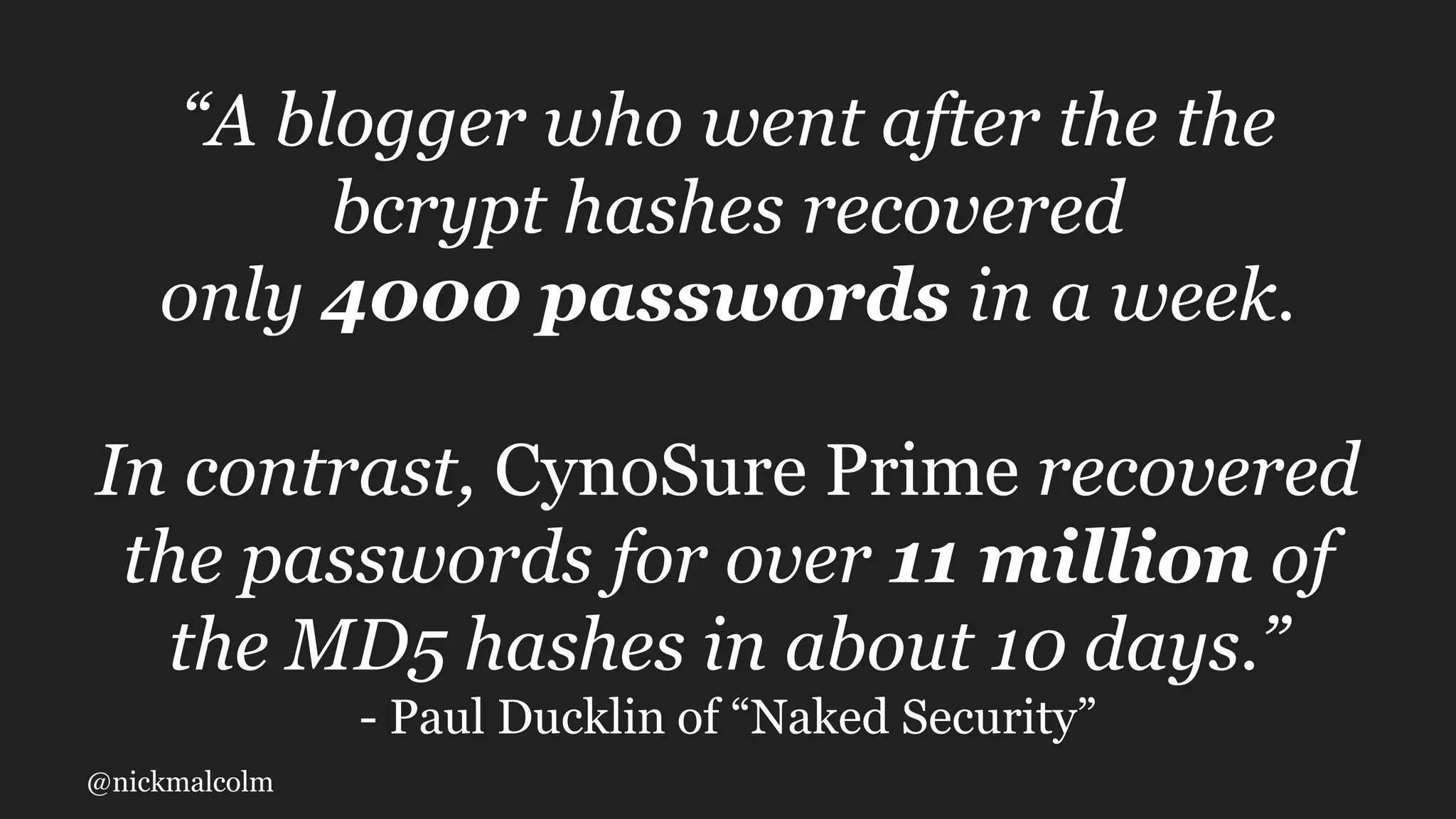
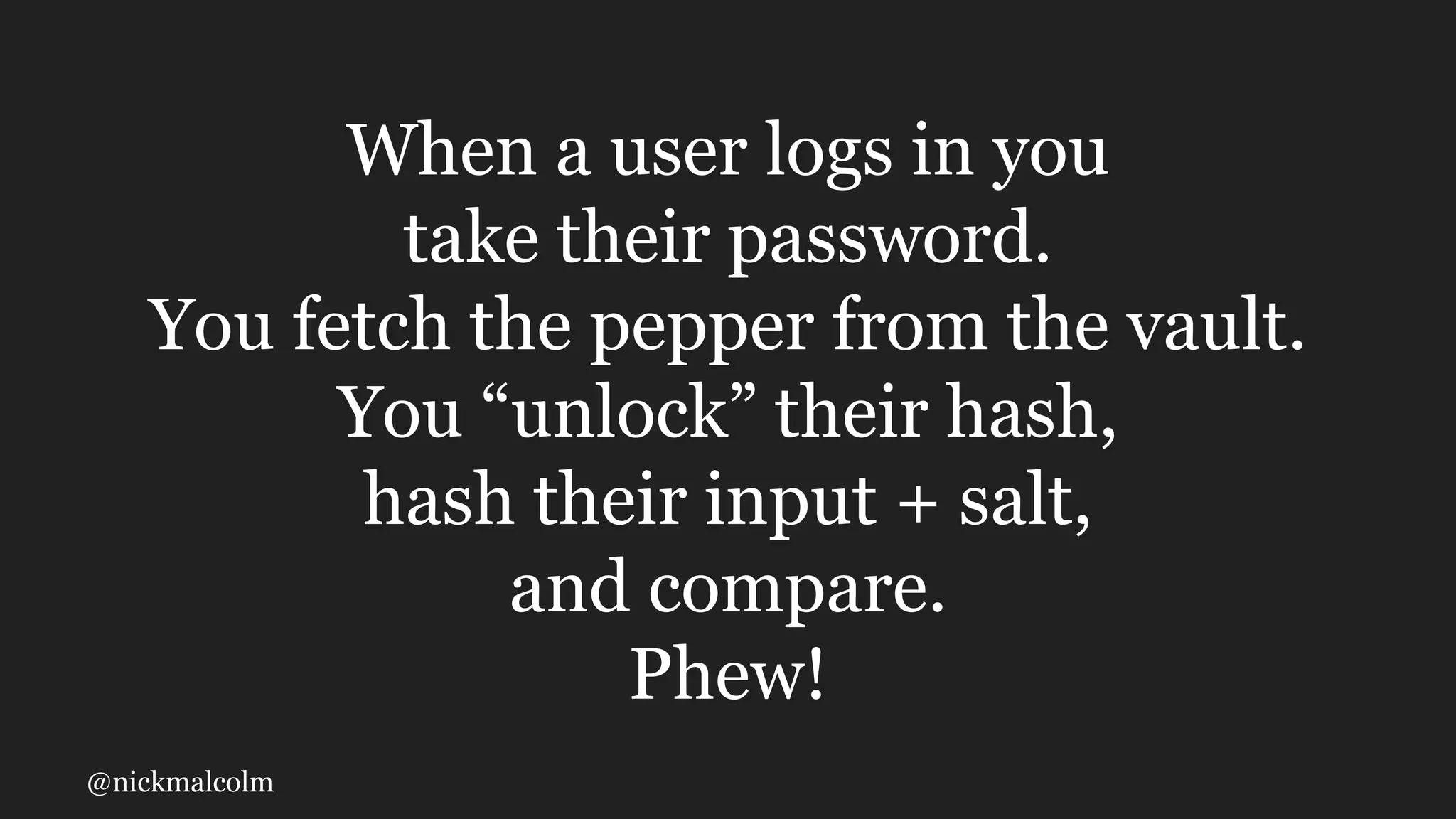
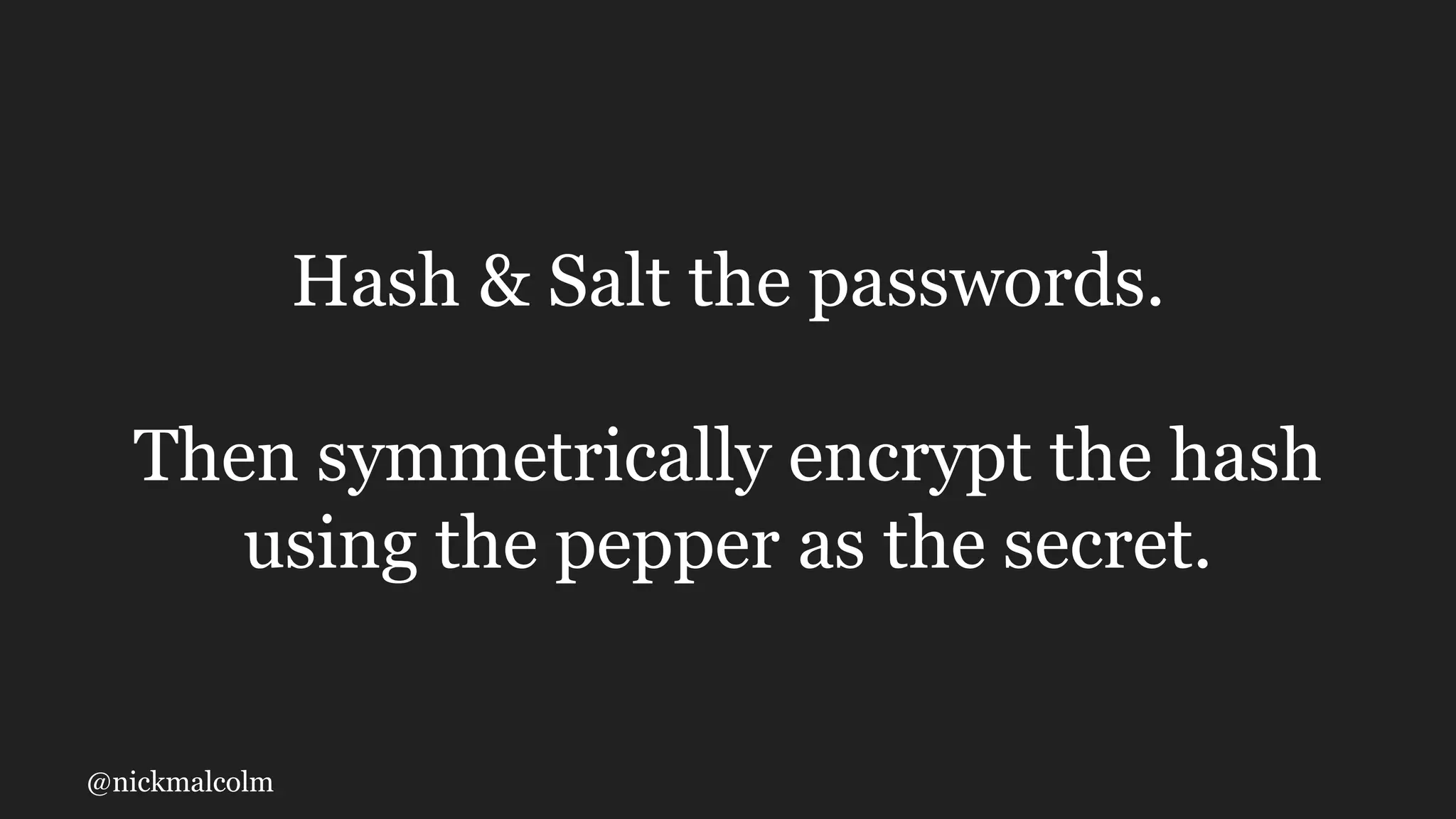
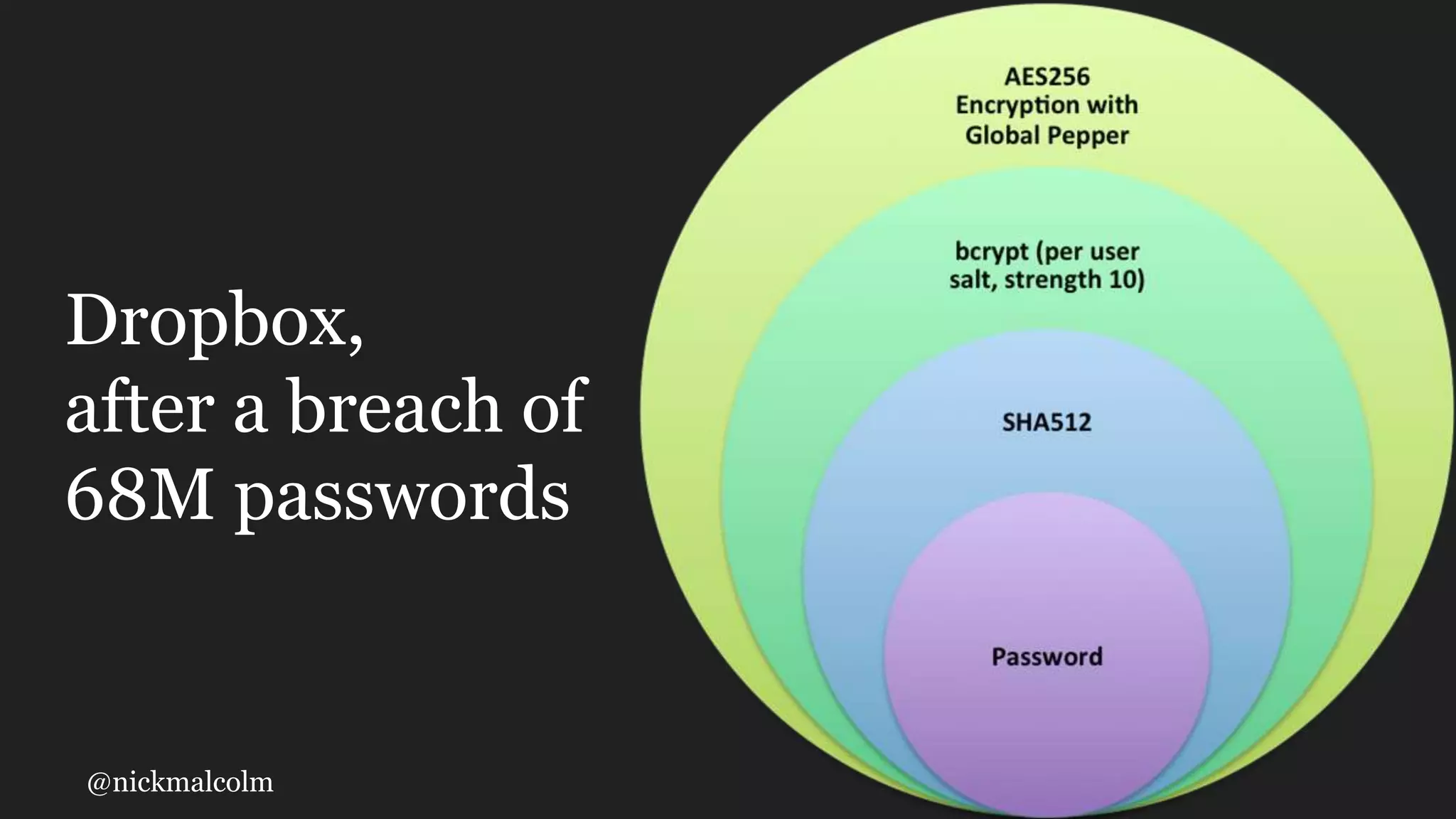
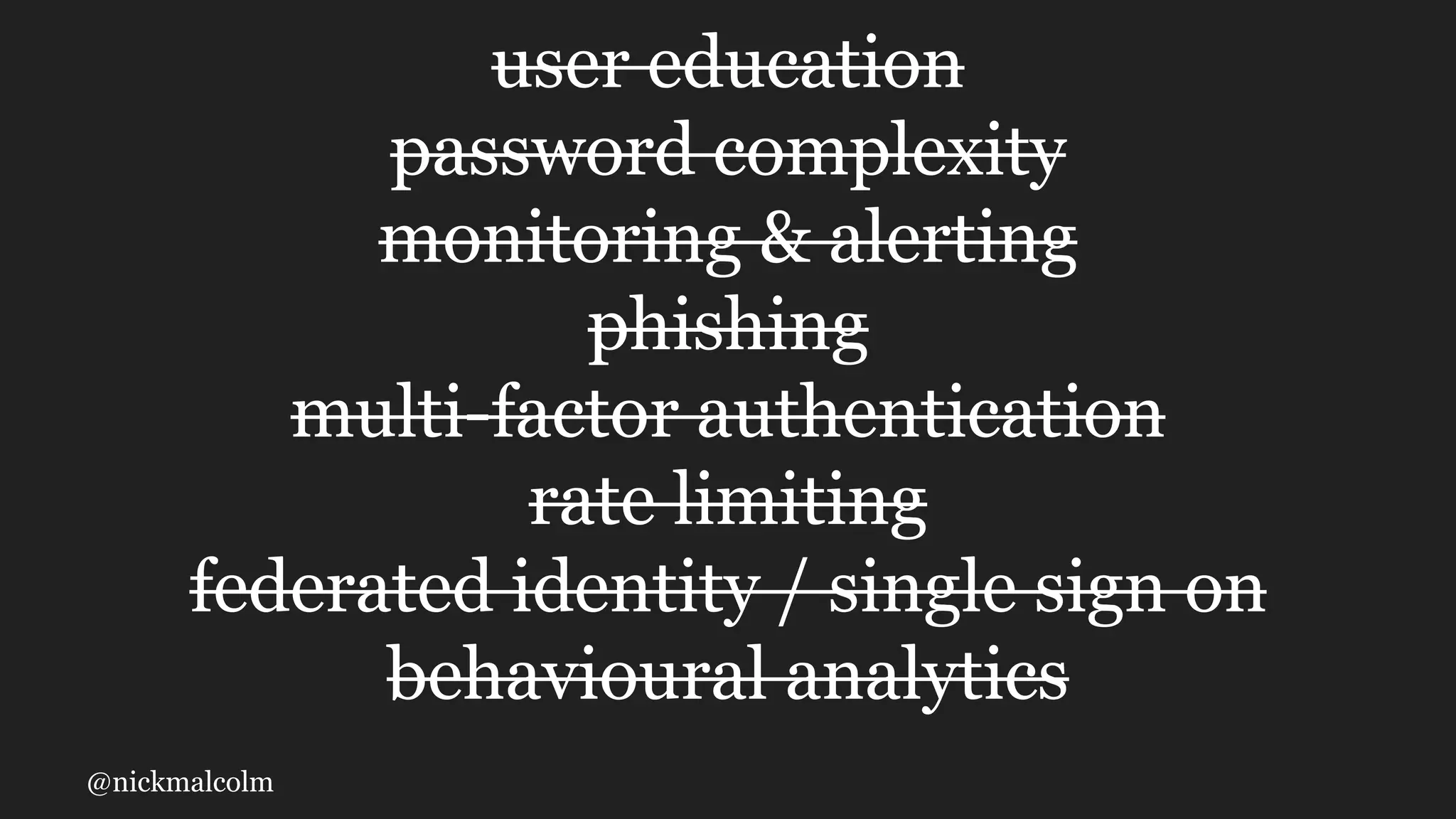
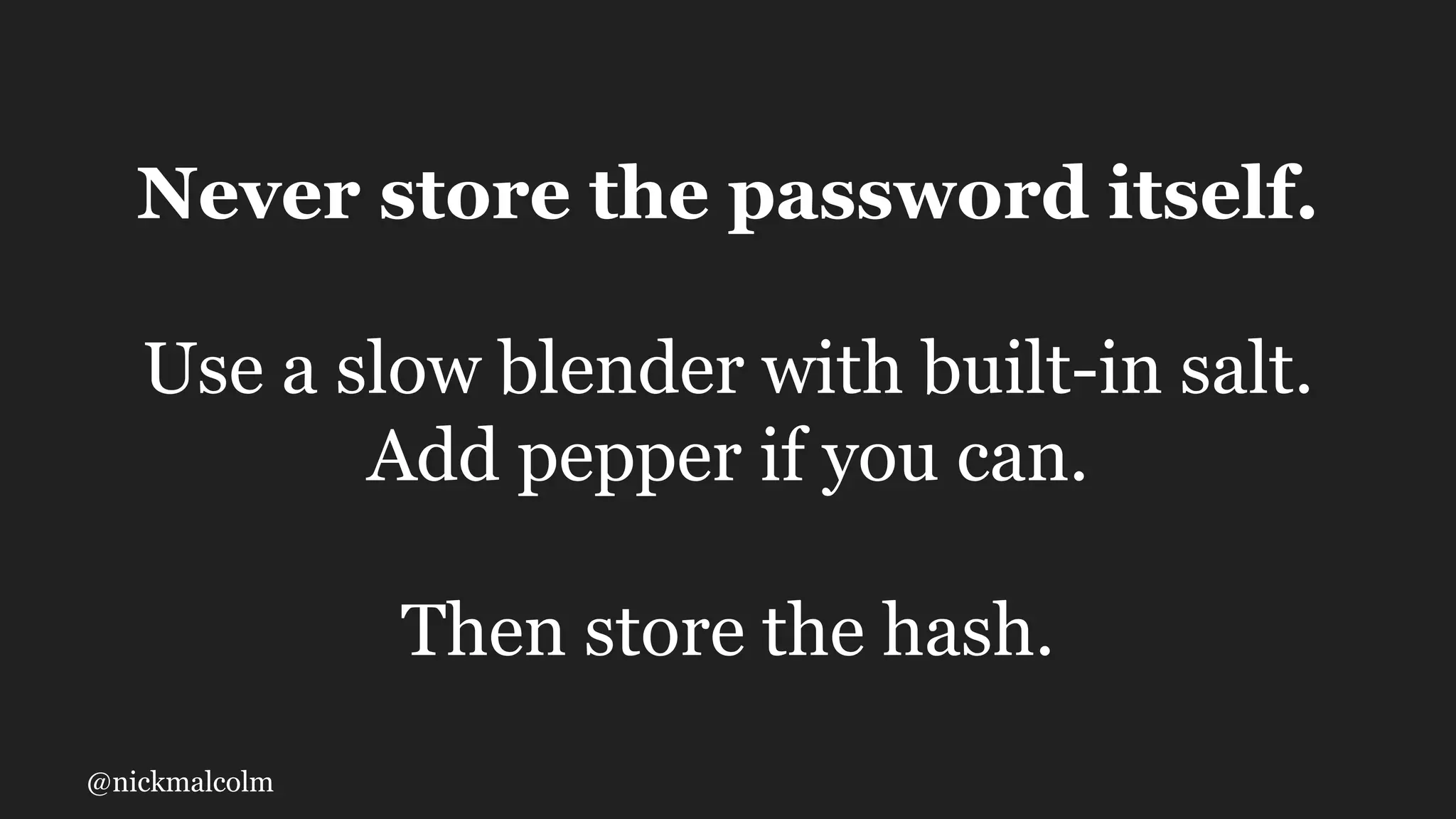
The document outlines various methods for password storage, emphasizing the significance of using hashed and salted algorithms rather than plaintext. It discusses common pitfalls in password security practices and highlights the importance of user education, complexity, and additional security measures. Ultimately, the best practice is to never store passwords directly but to utilize slow hashing functions combined with unique salts and potential peppers for added security.