The document discusses the key components of a computer system including hardware, software, input devices, storage devices, and output devices. It defines these terms and provides examples of common devices. It also summarizes the different types of software including systems software (operating systems, utilities, programming tools, libraries) and applications software (small-scale like word processors versus large-scale like payroll systems). Finally, it outlines the stages of the systems development life cycle from problem identification to maintenance. Defining the problem accurately is important so the delivered system matches user expectations.
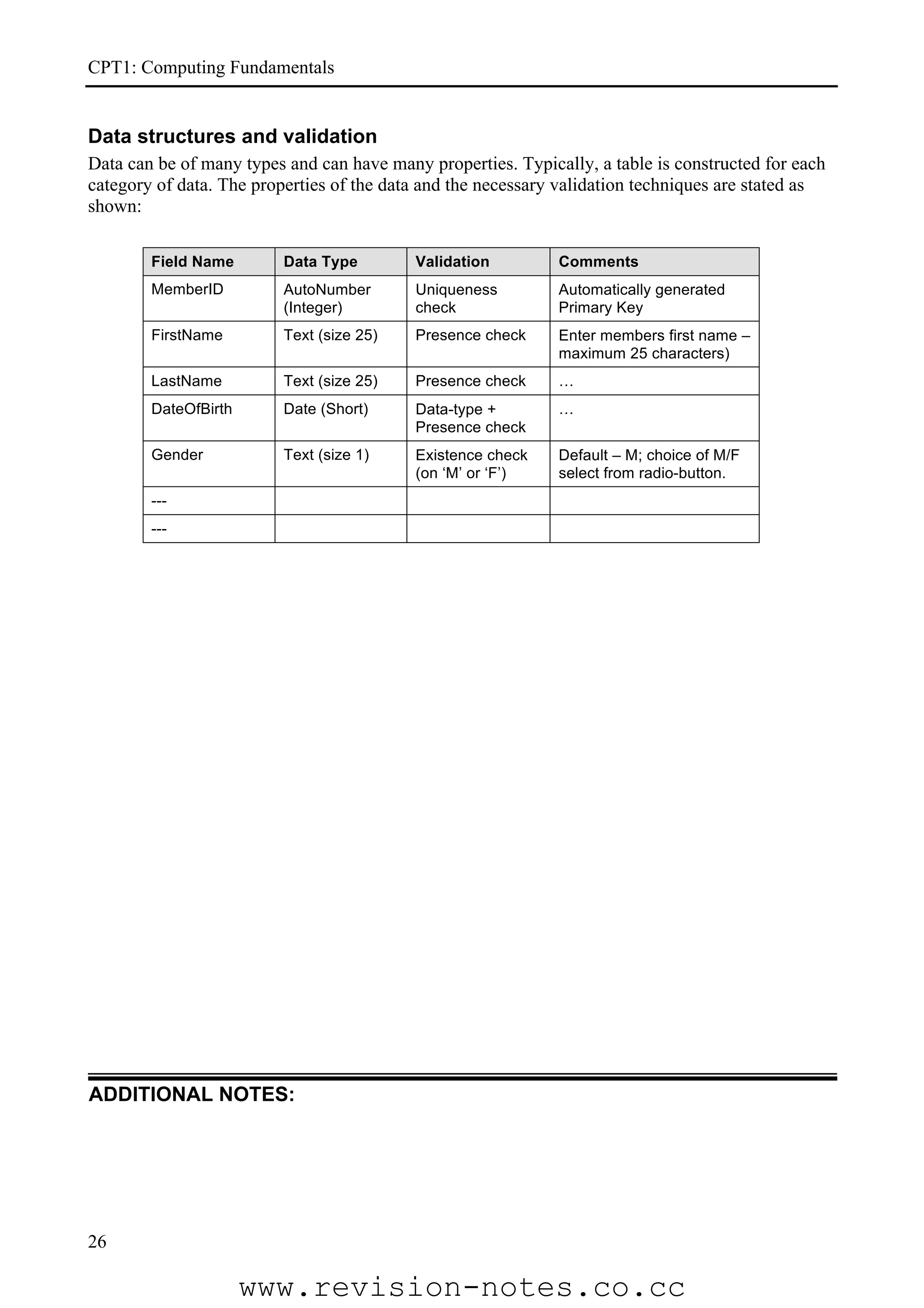
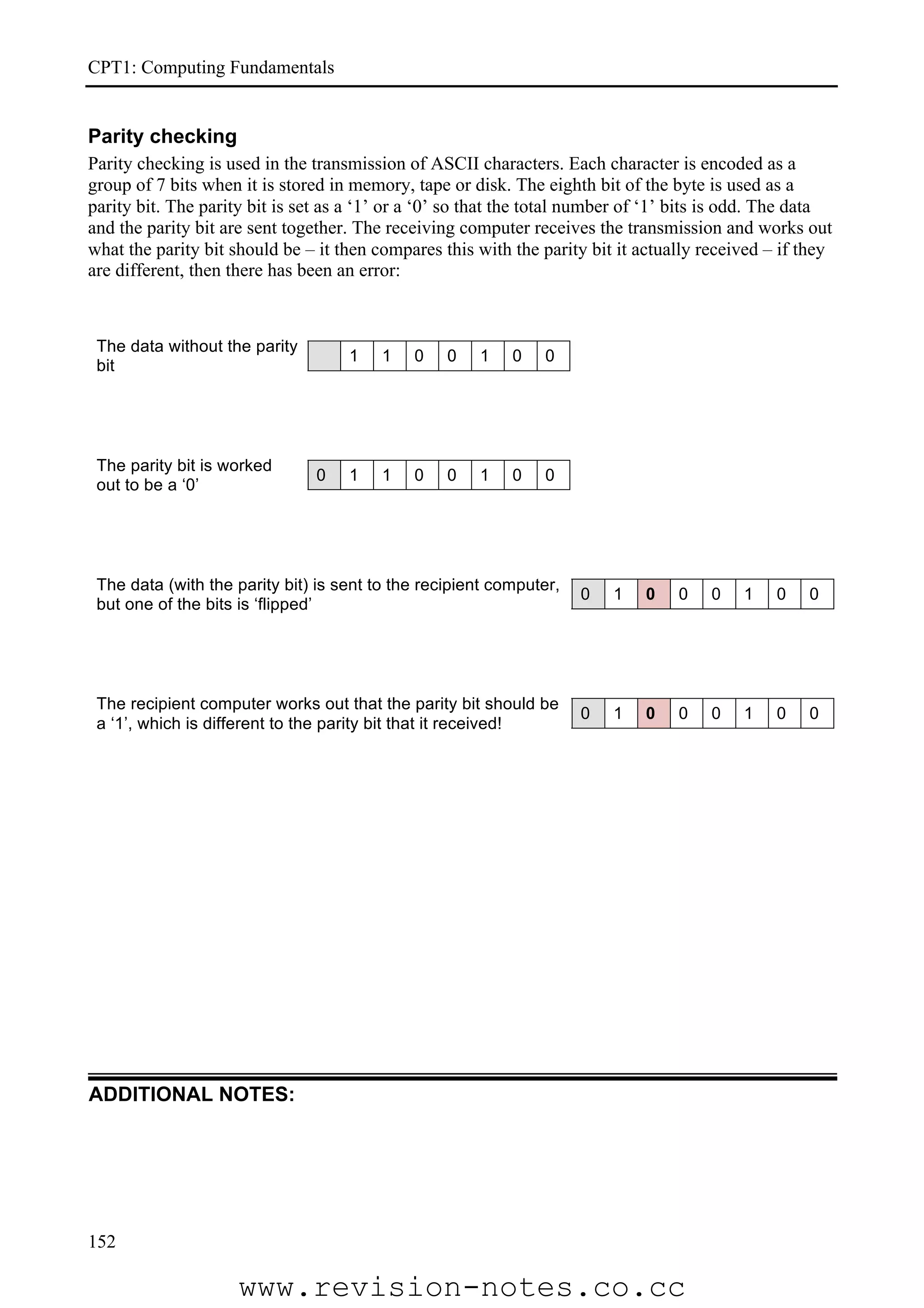
![CPT1: Computing Fundamentals
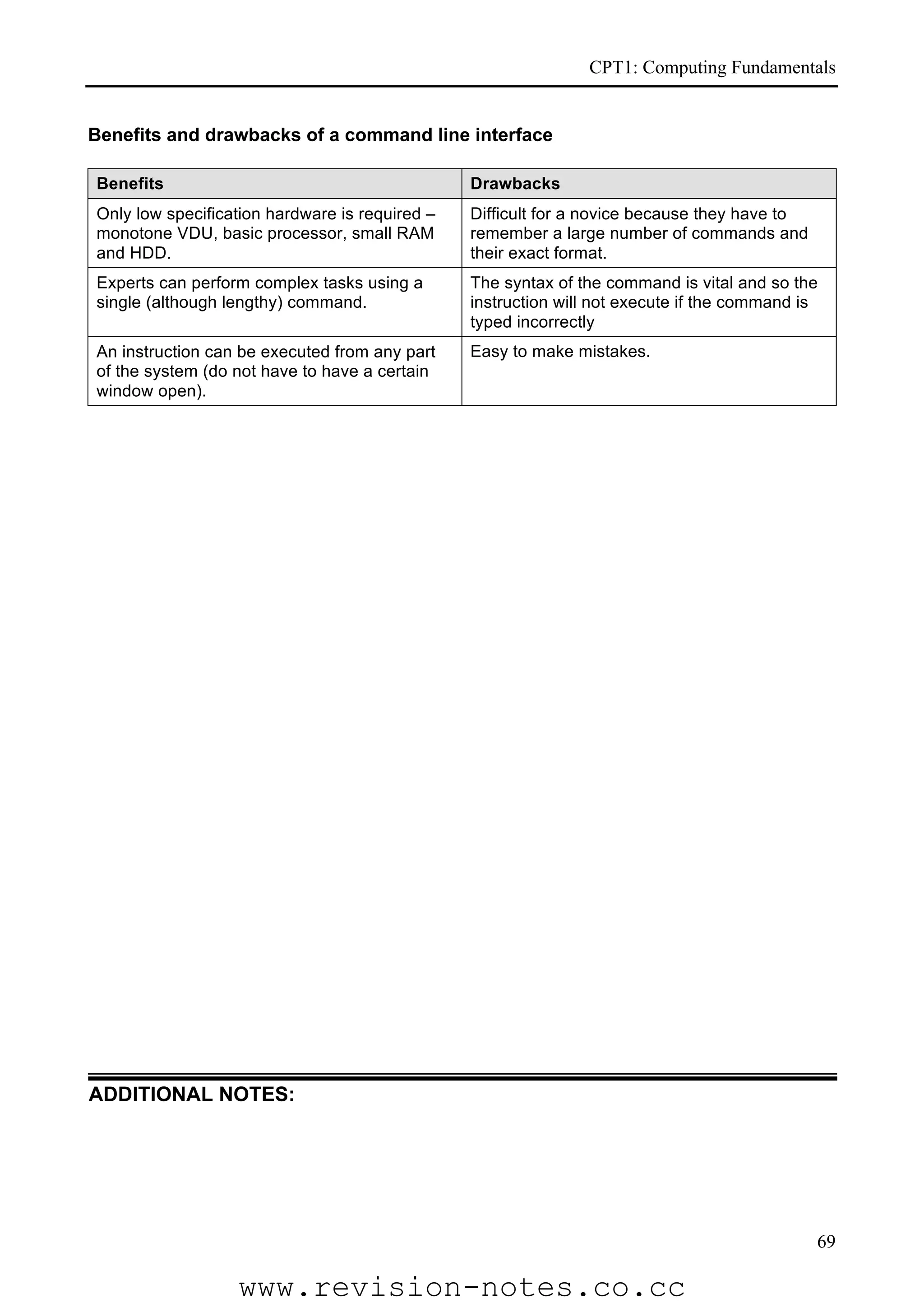
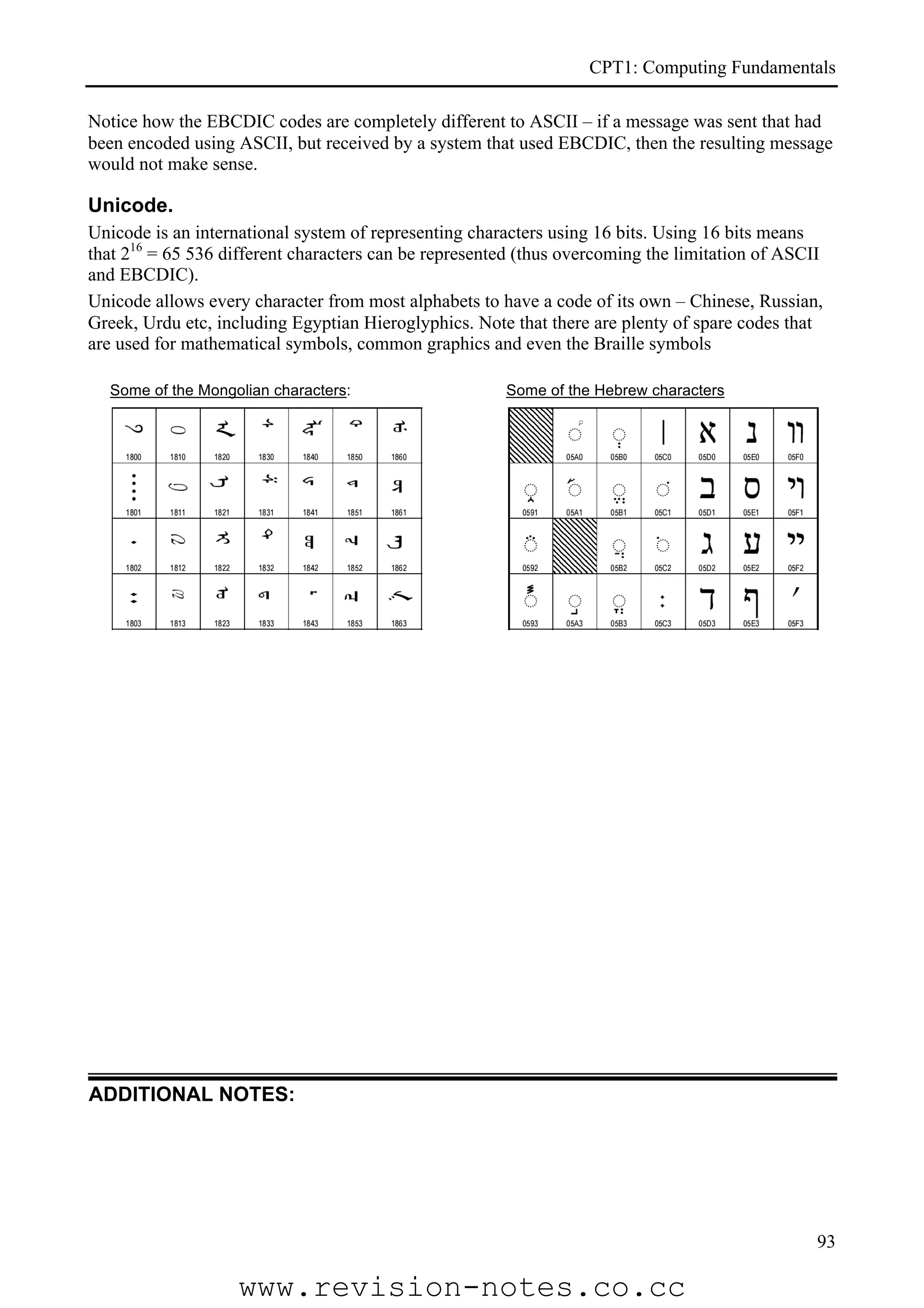
Memory management
The operating system has to allocate memory to each running application and to itself. Each
application is loaded into its own memory space – this means that if one program freezes, the others
can, in theory, keep working normally. It also means that you can terminate a ‘frozen’ program by
pressing [Ctrl]+[Alt]+[Delete]. Doing this will not effect any other programs.
To manage memory effectively, the operating system must:
• assign programs their own area of memory;
• prevent two programs from using the same area of memory;
• reallocate memory when a program is quit.
File management
The OS controls the transfer of data from disk to memory and back again. It also has to maintain a
directory of the disk so that files and free space can be quickly located. The directory is called the
File Allocation Table (FAT for short). To manage files effectively, when files are written to a disk
the OS ensures that:
• existing files are not over-written;
• when files are deleted from the disk the storage blocks are made available for new files.
Allocation of processor time
When several processes are executing on a computer at the same time (eg downloading a file,
printing and listening to an .mp3), then they will all need to receive time from the processor. Some
processes, such as printing, require very little processor time, while other processes require the
processor continuously. In such situations the Operating System would place a high priority on
printing requests to get them cleared and then allow it to concentrate on the more demanding
processes.
Input output device management
When two programs want to print to the same printer, the operating system has to ensure that the
two ‘jobs’ do not interfere with each other. It would normally do this by putting the jobs into a
queue and then pass them to the printer when the printer is ready.
ADDITIONAL NOTES:
56
www.revision-notes.co.cc](https://image.slidesharecdn.com/a-level-computing-9691-paper-1-notes-130221005611-phpapp02/75/A-level-computing-9691-paper-1-notes-29-2048.jpg)
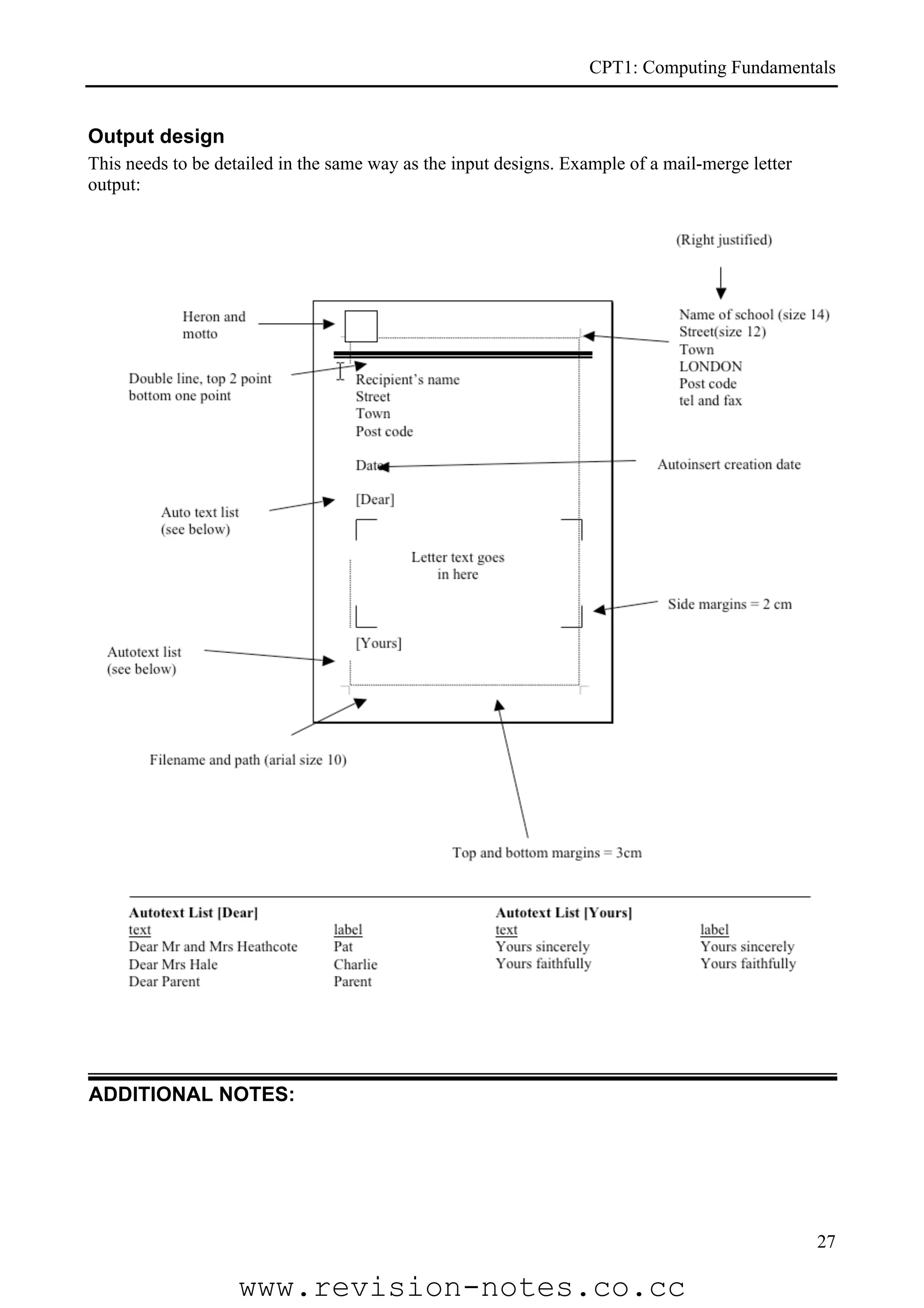
![CPT1: Computing Fundamentals
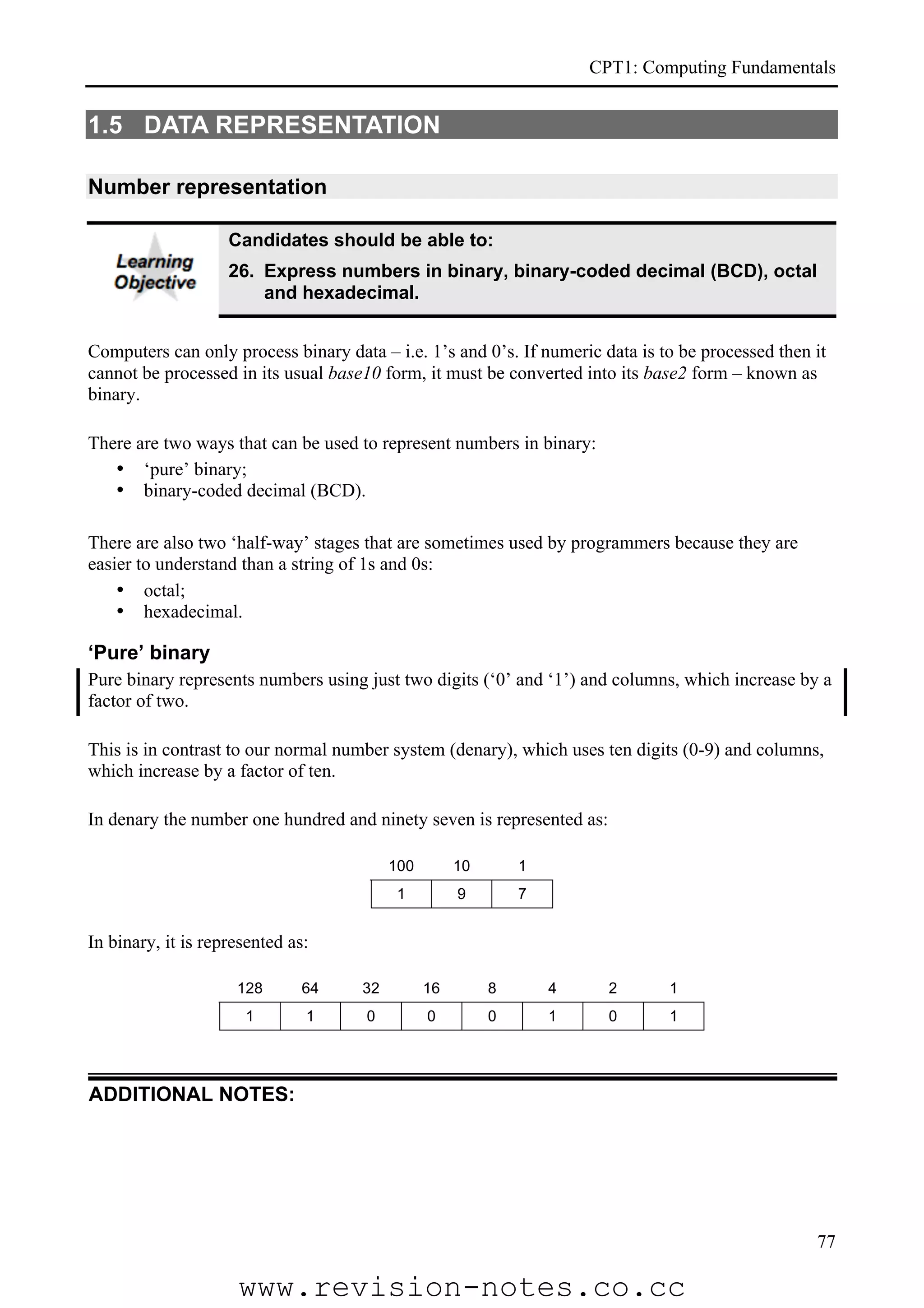
Text (character) representation
Candidates should be able to:
29. Explain the use of code to represent a character set (ASCII,
EBCDIC and UNICODE).
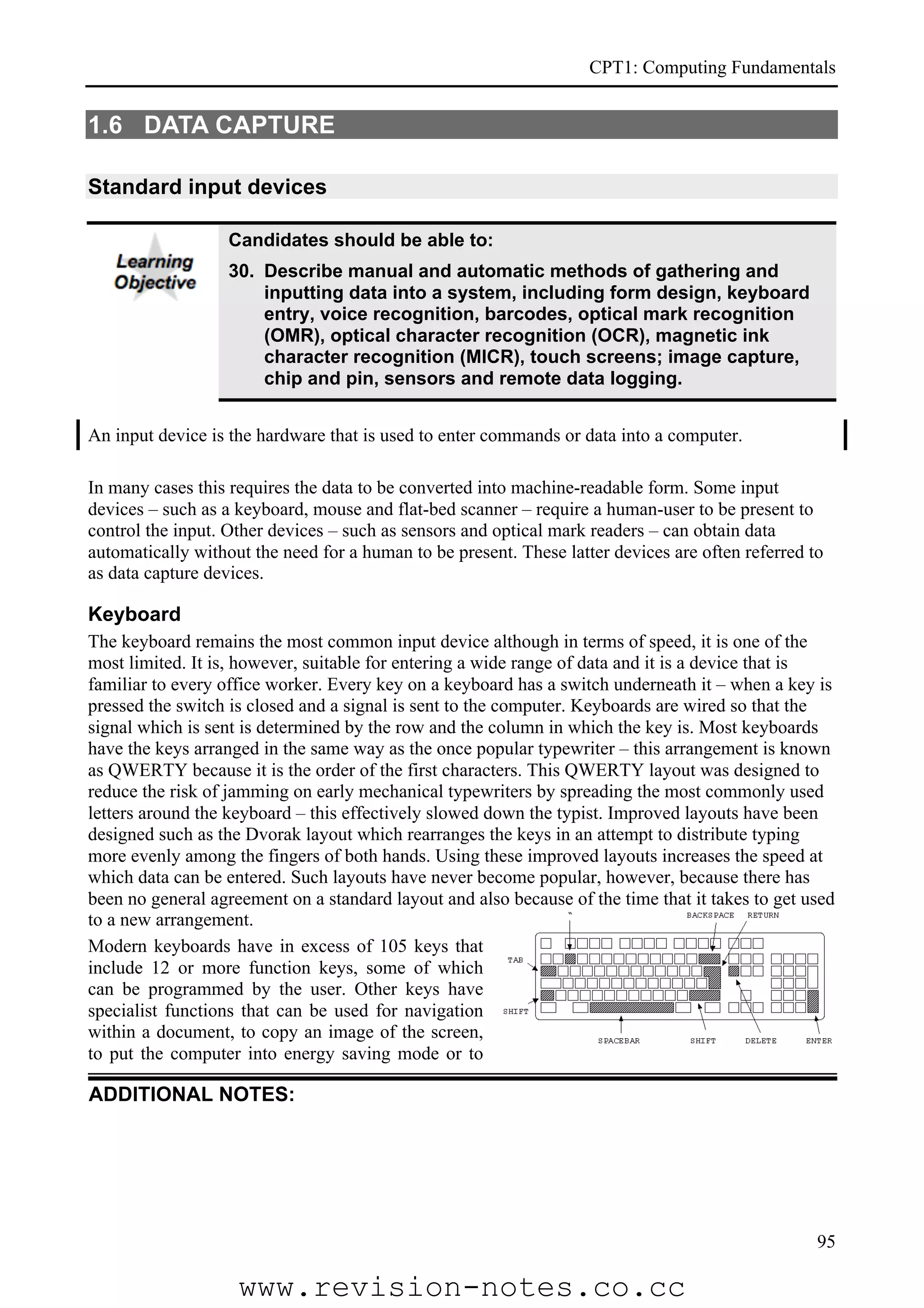
Character Set
A character set are the characters that can be recognised by a computer.
Character encoding
A computer is able to represent four types of characters:
• alphanumeric characters – letters A – Z and a – z and the digits 0 – 9.
• punctuation characters and other ‘special’ symbols such as , . ; : “ ‘ ! @ £ $ % & * ( ) + <
• graphical characters such as ♣, ♦, ♥, ♠, Ψ, , , ✘, ☛, ✻ (and many more…);
• control characters – [Return], [Esc], [Space], [Alt], etc.
Within a computer, each character is represented using a unique binary code. Although there are
many different methods of encoding the characters, three of the most common are ASCII, EBCDIC
and Unicode.
ASCII
American Standard Code for Information Interchange (ASCII) is used for character encoding by
most Windows™ PCs. ASCII can be used to translate alphanumeric characters into a 7-bit binary
code that represents all the characters available from the keyboard including punctuation and some
special symbols such as ‘@’, # and $:
A development of ASCII, known as Extended ASCII, uses an 8-bit code that also defines codes for
additional characters, including some graphical ones. Note that using an 8-bit code means the
maximum number of characters that can be represented is 256.
ADDITIONAL NOTES:
91
www.revision-notes.co.cc](https://image.slidesharecdn.com/a-level-computing-9691-paper-1-notes-130221005611-phpapp02/75/A-level-computing-9691-paper-1-notes-57-2048.jpg)
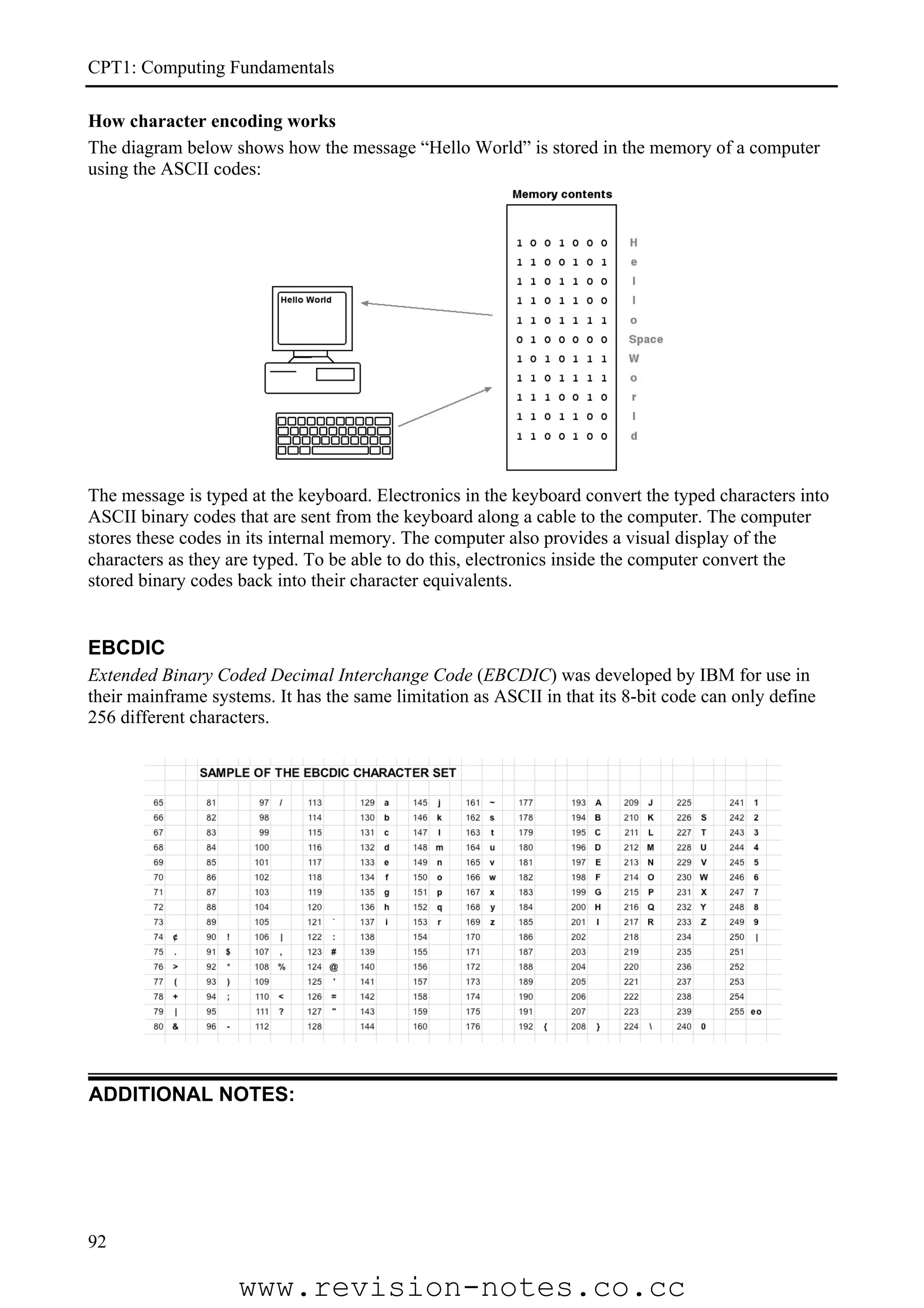


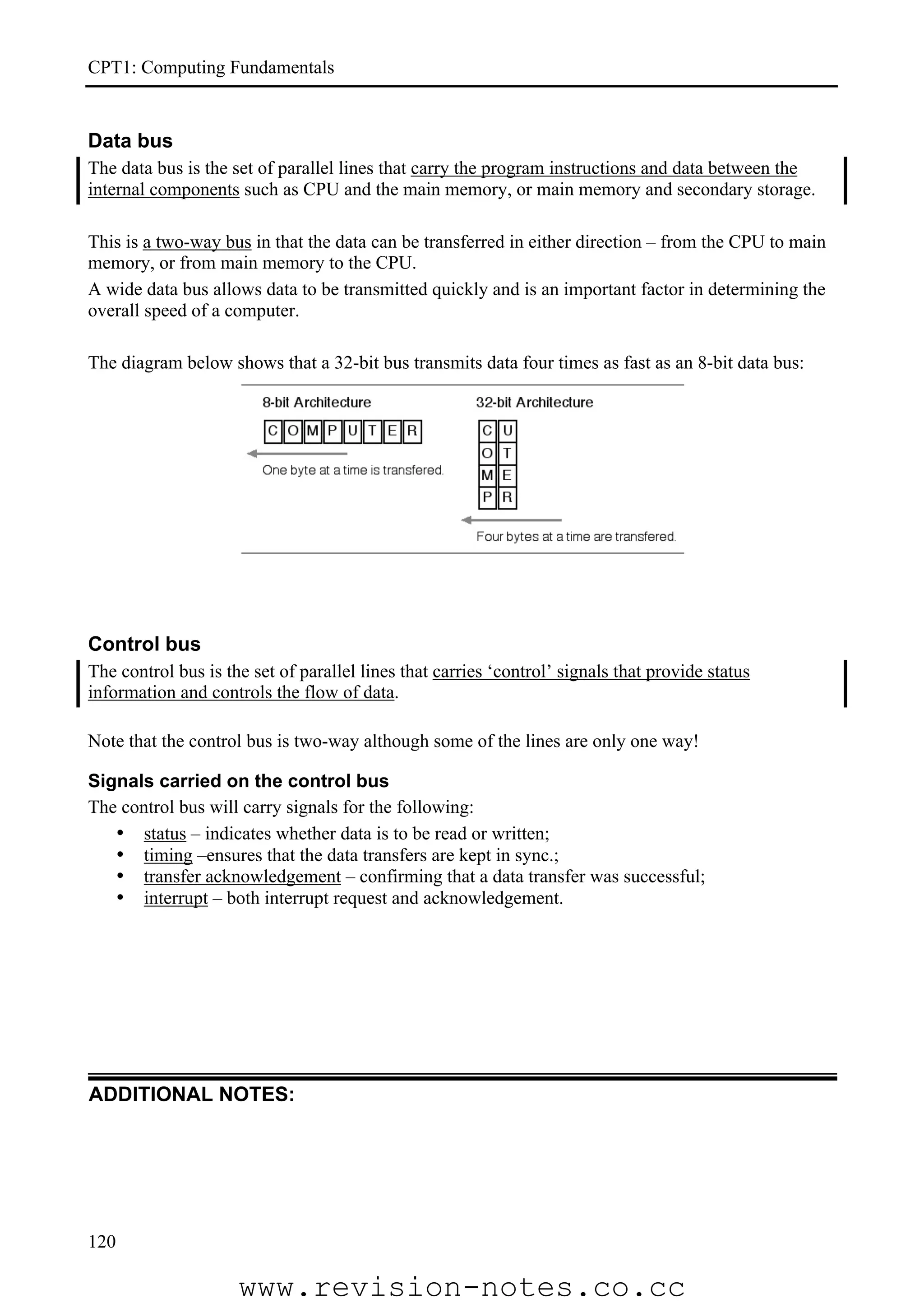
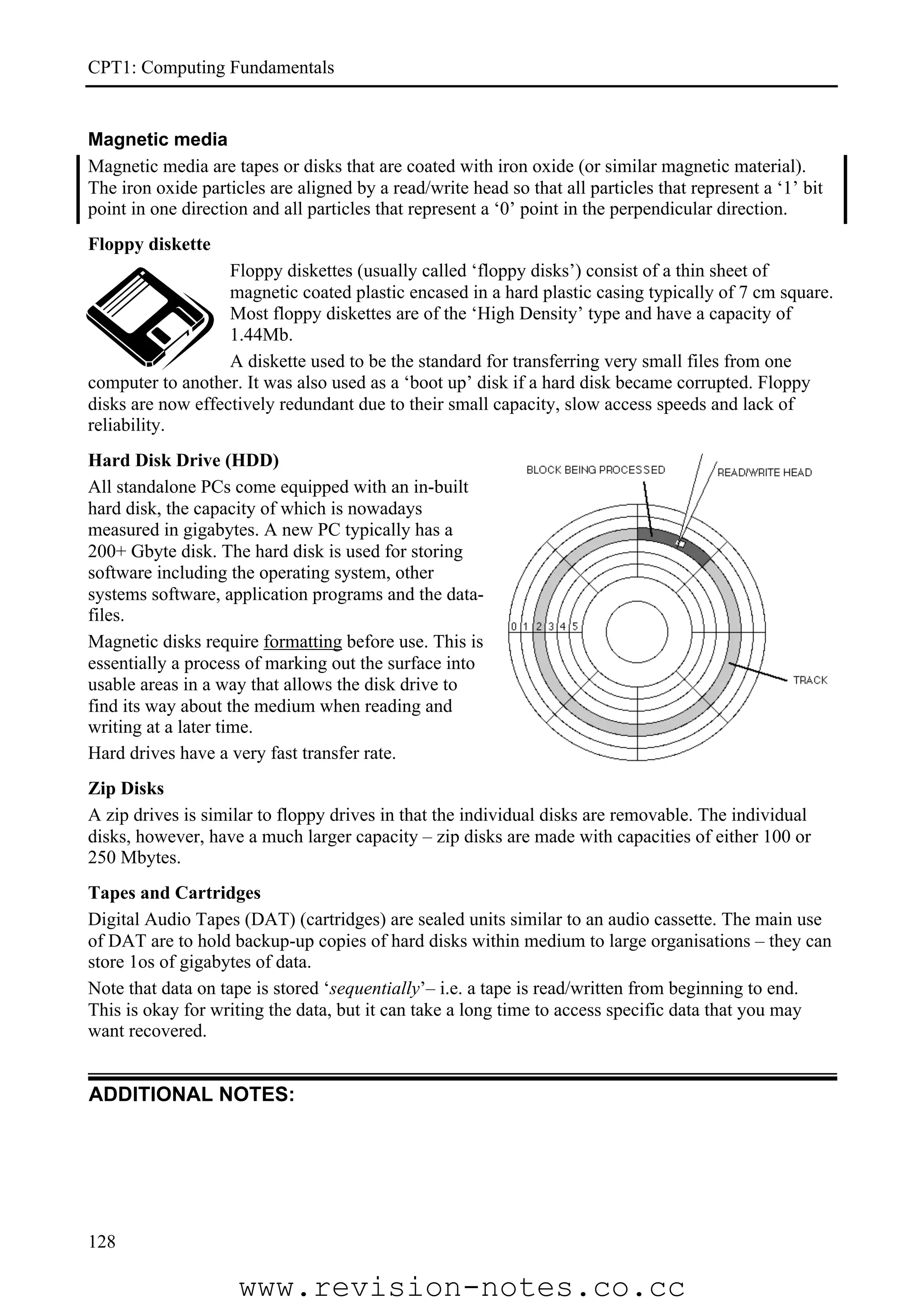
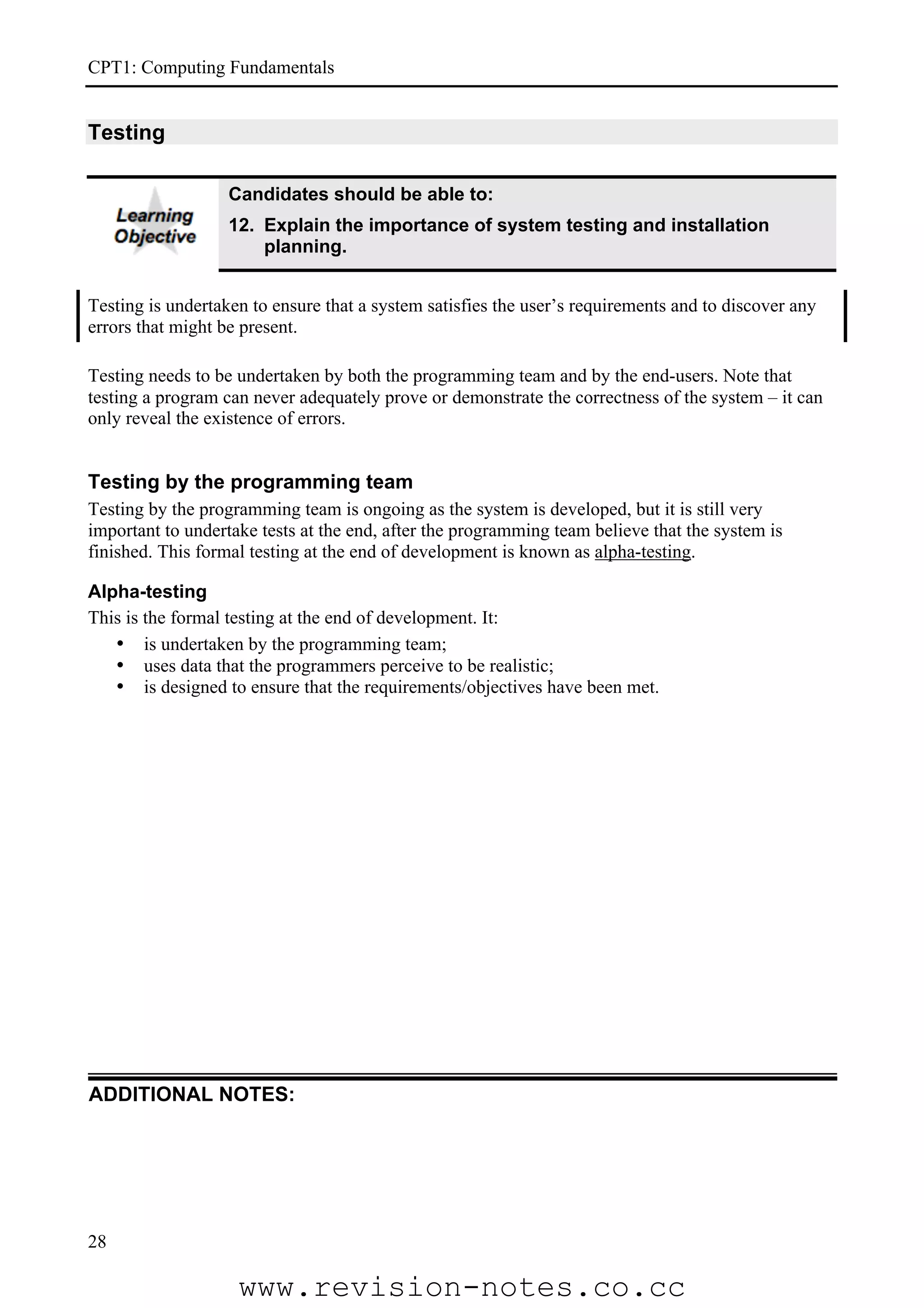
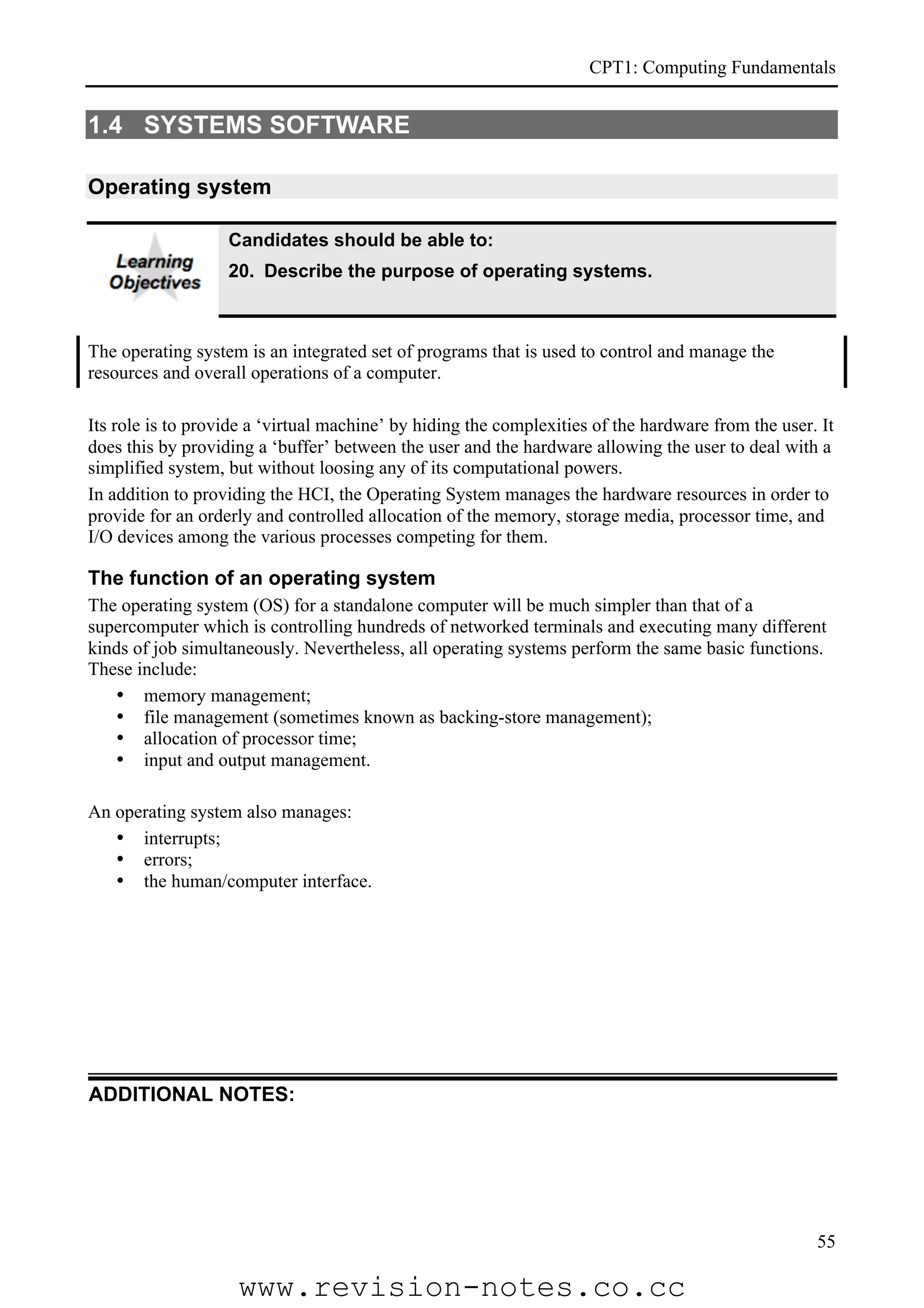
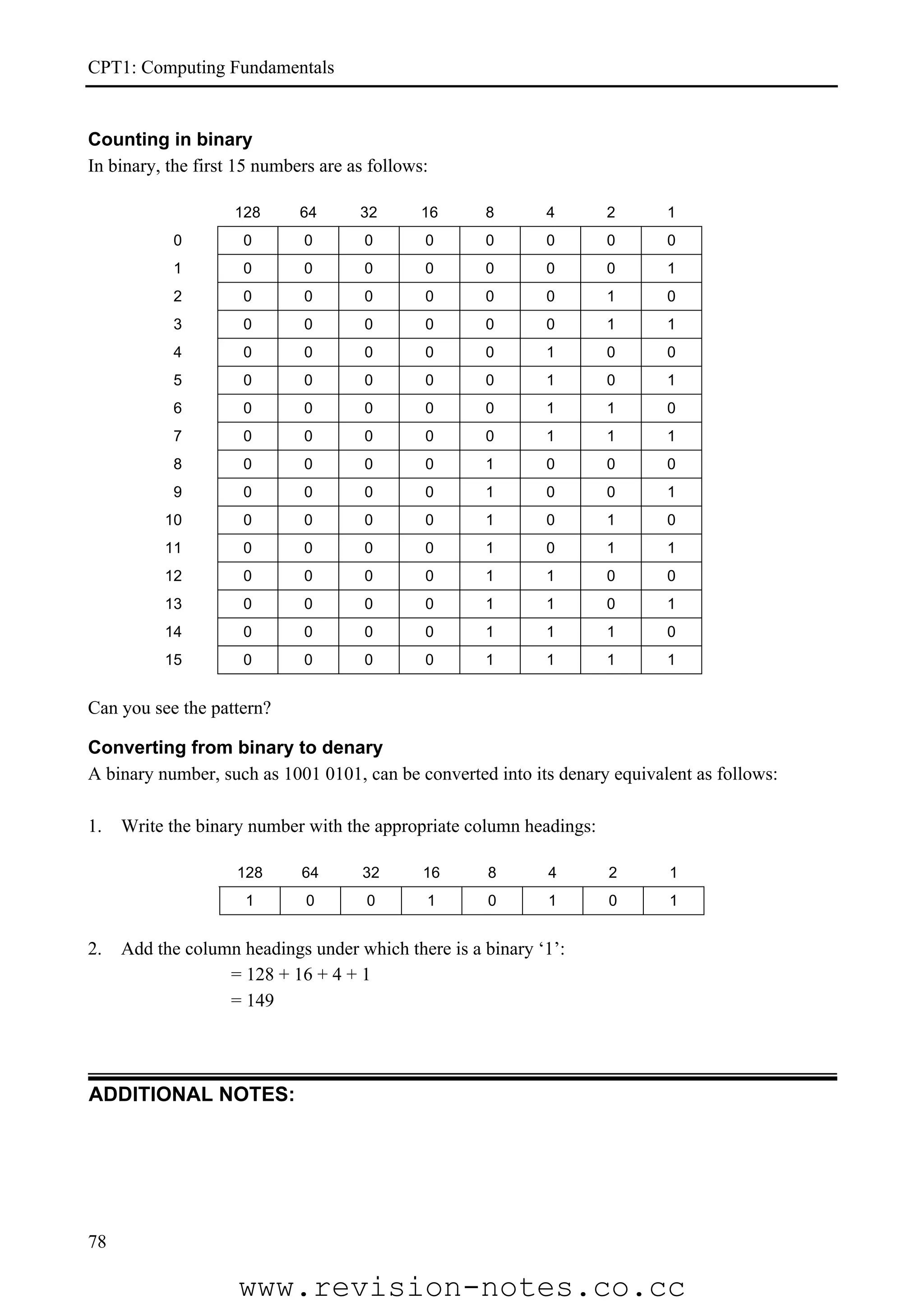
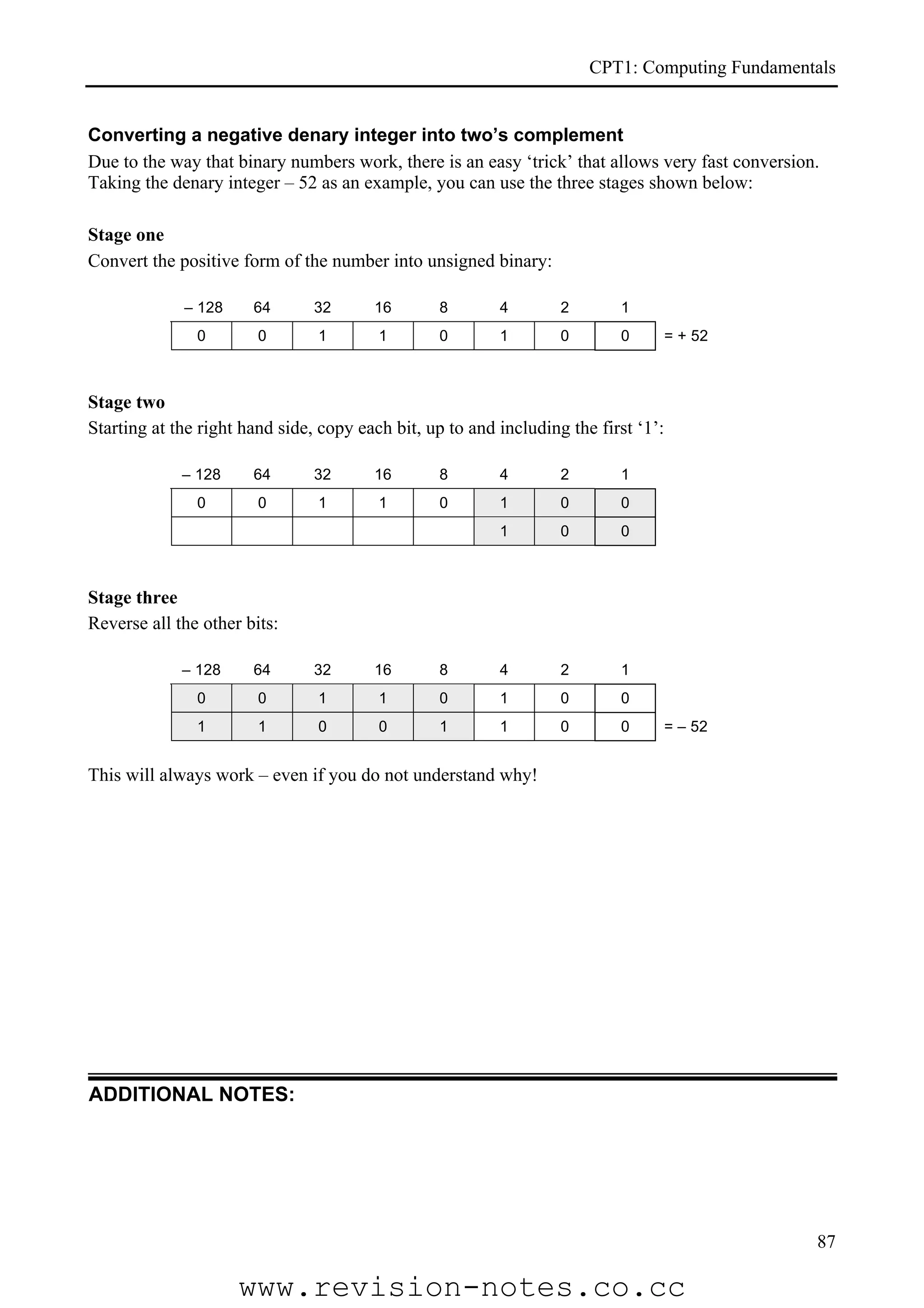
![CPT1: Computing Fundamentals
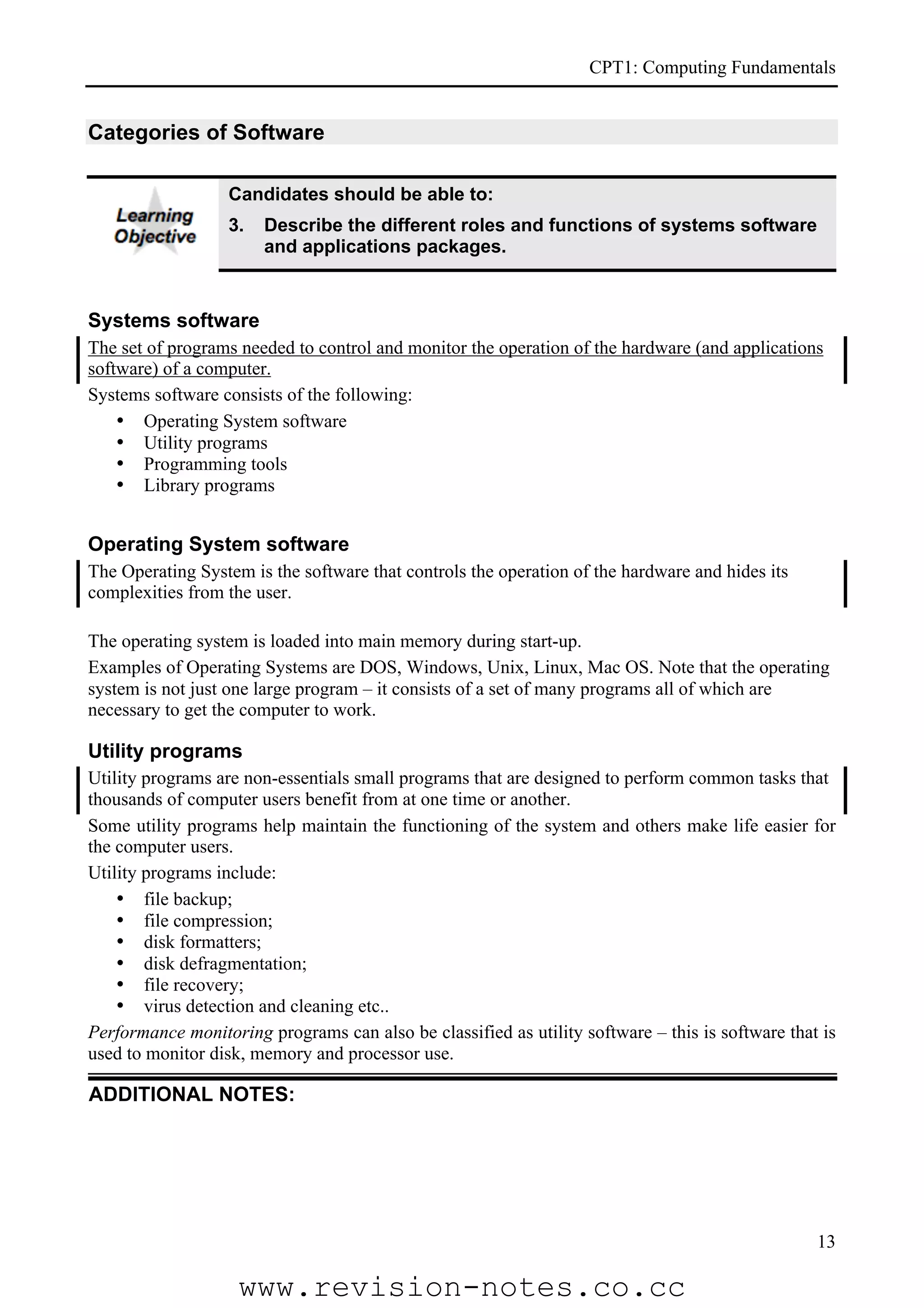
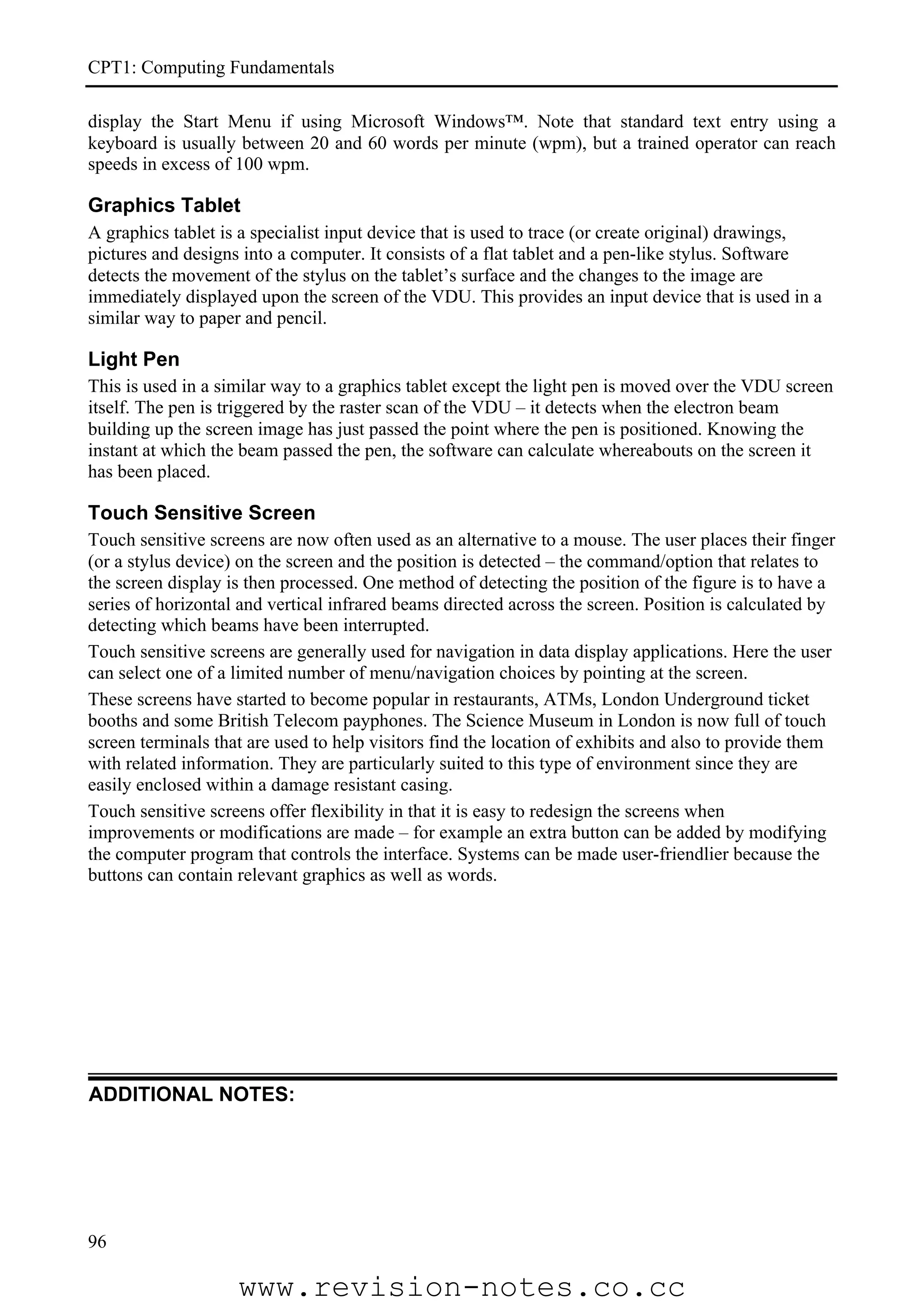
Secondary storage summary
Magnetic media
Price
Media Capacity Speed Uses
[2008]
VERY RARE NOW.
Floppy Disk 1.44 Mb V Slow Backing up small amounts of data – eg word
processing files.
VERY RARE NOW.
Zip Disk 100/250 Mb Medium
Backing up work on a home computer
Storage of operating system, application
Hard Disk > 200 Gb Fast £40
programs and user produced data-files.
Backing up large amounts of data – eg on a
Tape/DAT > 70 Gb V Slow
network file server.
Optical media
Price
Media Capacity Speed Uses
[2008]
CD-ROM 650/700 Mb Medium 30p each Distribution of commercial software
Backing/archiving up work and software on a
CD-R/RW 650/700 Mb Medium 50p each
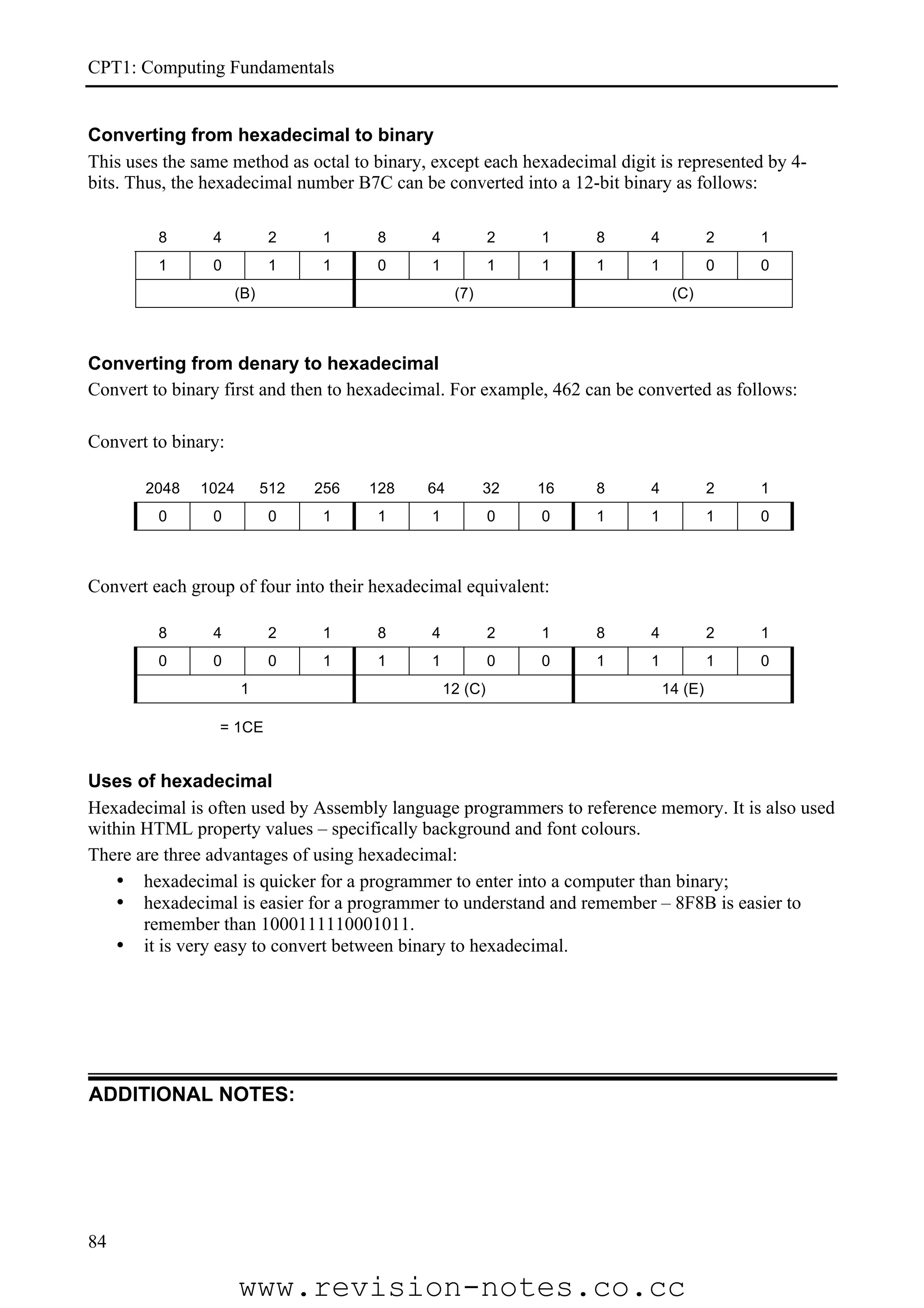
home computer.
Distribution of software – particularly ones
DVD 4.7 – 17 Gb Quite fast that contain a lot of multimedia and videos;
backing up files on the hard disk
Backing/archiving up work and software on a
DVD-R/RW 4.7 – 9.4 Gb Quite fast
home computer.
Blu-ray 25 –100+ Gb ?? Distribution of High Definition movies
Electronic media
Price
Media Capacity Speed Uses
[2008]
Storing digital images (from a digital camera);
Flash Card 8+ Gb Quite fast Storing contact details and diary information
(mobile phone).
Transferring files from one computer to
USB Pens 8+ Gb Quite fast another;
Backing up personal files.
ADDITIONAL NOTES:
131
www.revision-notes.co.cc](https://image.slidesharecdn.com/a-level-computing-9691-paper-1-notes-130221005611-phpapp02/75/A-level-computing-9691-paper-1-notes-87-2048.jpg)