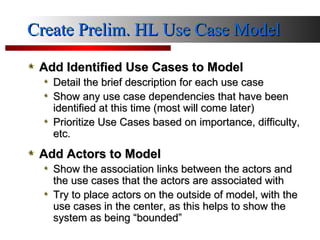
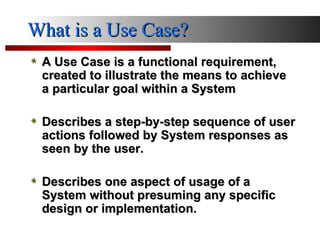
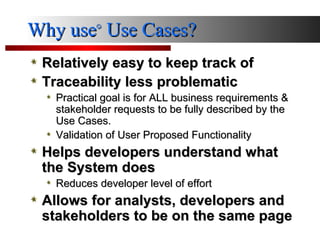
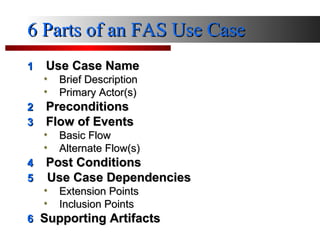
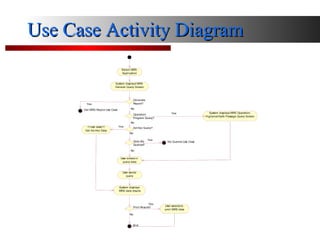
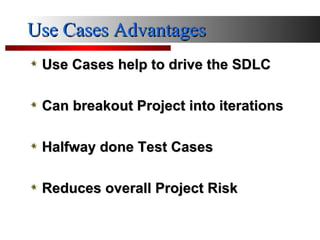
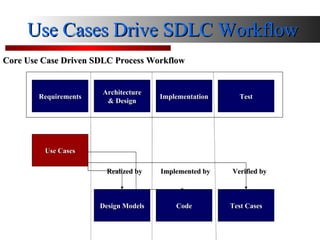
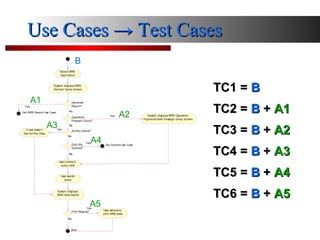
The document outlines a workshop led by Brent H. Snyder on identifying use cases and actors in system development. It discusses creating preliminary high-level use case models, detailing use case dependencies, and prioritizing based on importance and difficulty. The importance of use cases in driving the software development life cycle (SDLC) and reducing risks through structured validation and testing is emphasized.