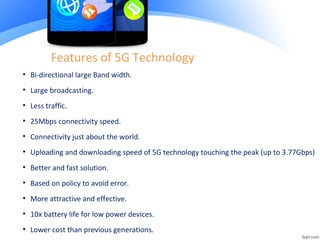
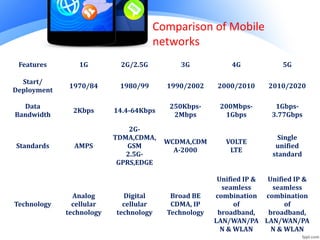
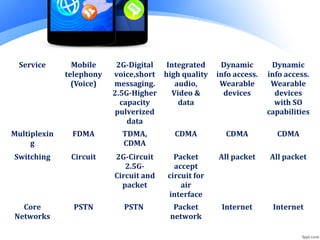
5G mobile technology aims to provide faster download speeds, lower latency, and more bandwidth than previous generations. It is expected to be fully implemented by 2020. 5G will offer super fast and efficient mobile networks through bidirectional large bandwidth and connectivity anywhere in the world. Download and upload speeds may reach 3.77 Gbps. Applications of 5G include mobile devices that can sense natural disasters, self-cleaning phones, and health monitoring through suggested medications. 5G networks will utilize unified IP and seamless combinations of technologies to dynamically access information through various connected devices.