This document provides an overview of implementing IPv4, including:
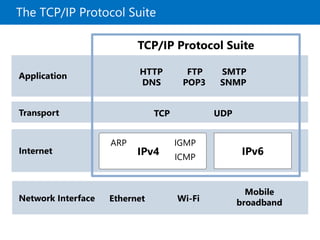
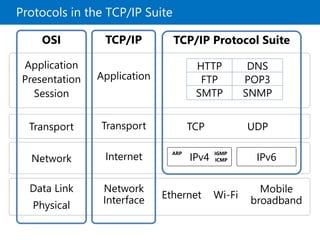
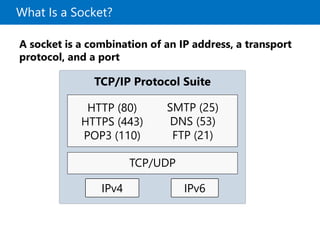
- Lessons on TCP/IP protocols, IPv4 addressing, subnetting, and configuration/troubleshooting of IPv4
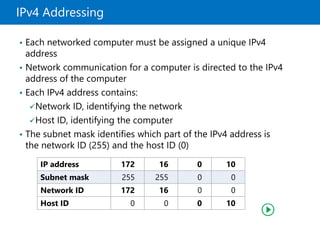
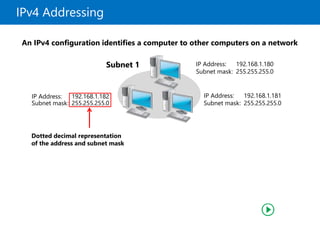
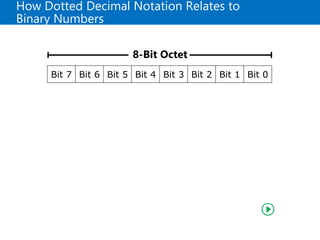
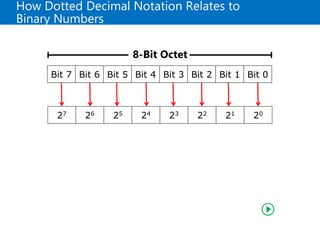
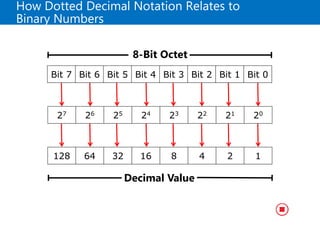
- Formatting IPv4 addresses using dotted decimal notation and relating this to binary numbers
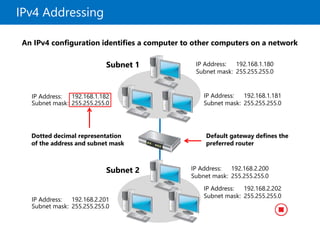
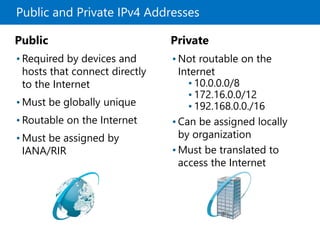
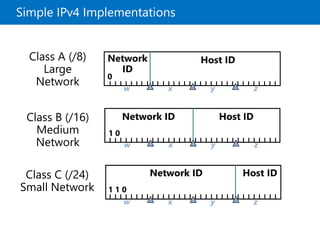
- Classifying IPv4 addresses as private or public and examples of simple/complex IPv4 implementations
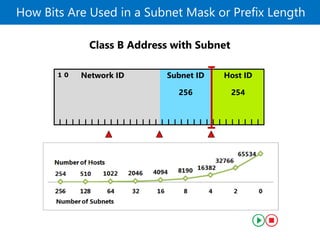
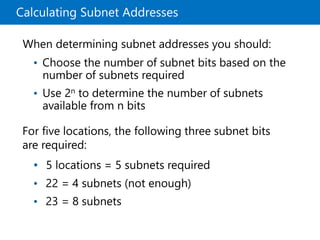
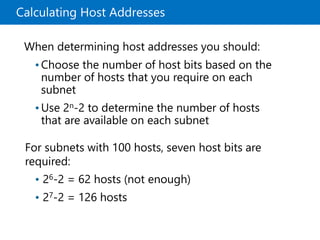
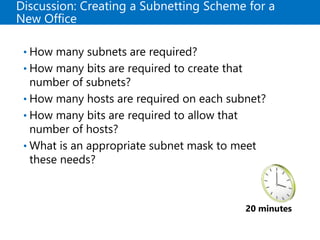
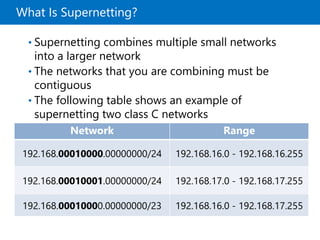
- Benefits of subnetting like segmenting traffic and techniques for calculating subnet/host addresses
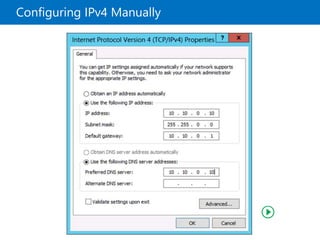
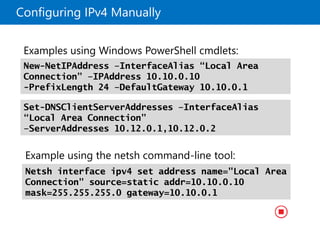
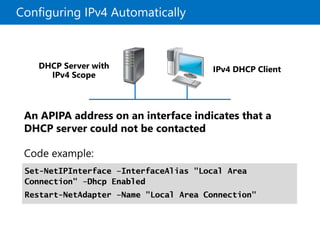
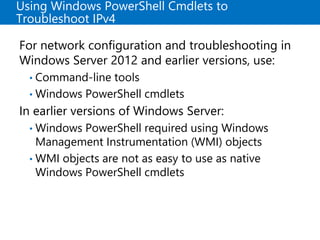
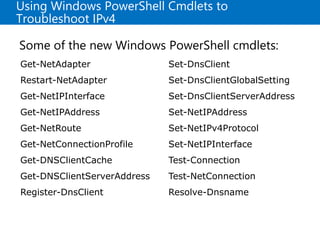
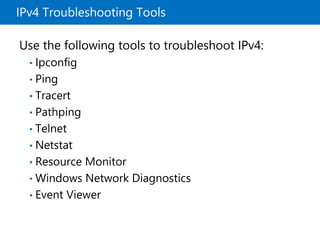
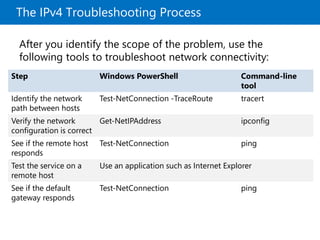
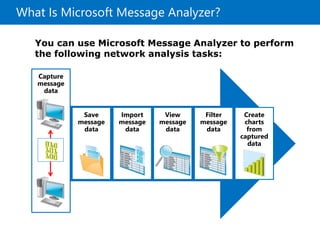
- Tools for configuring and troubleshooting IPv4 like Windows PowerShell, Ping, Tracert, and Message Analyzer