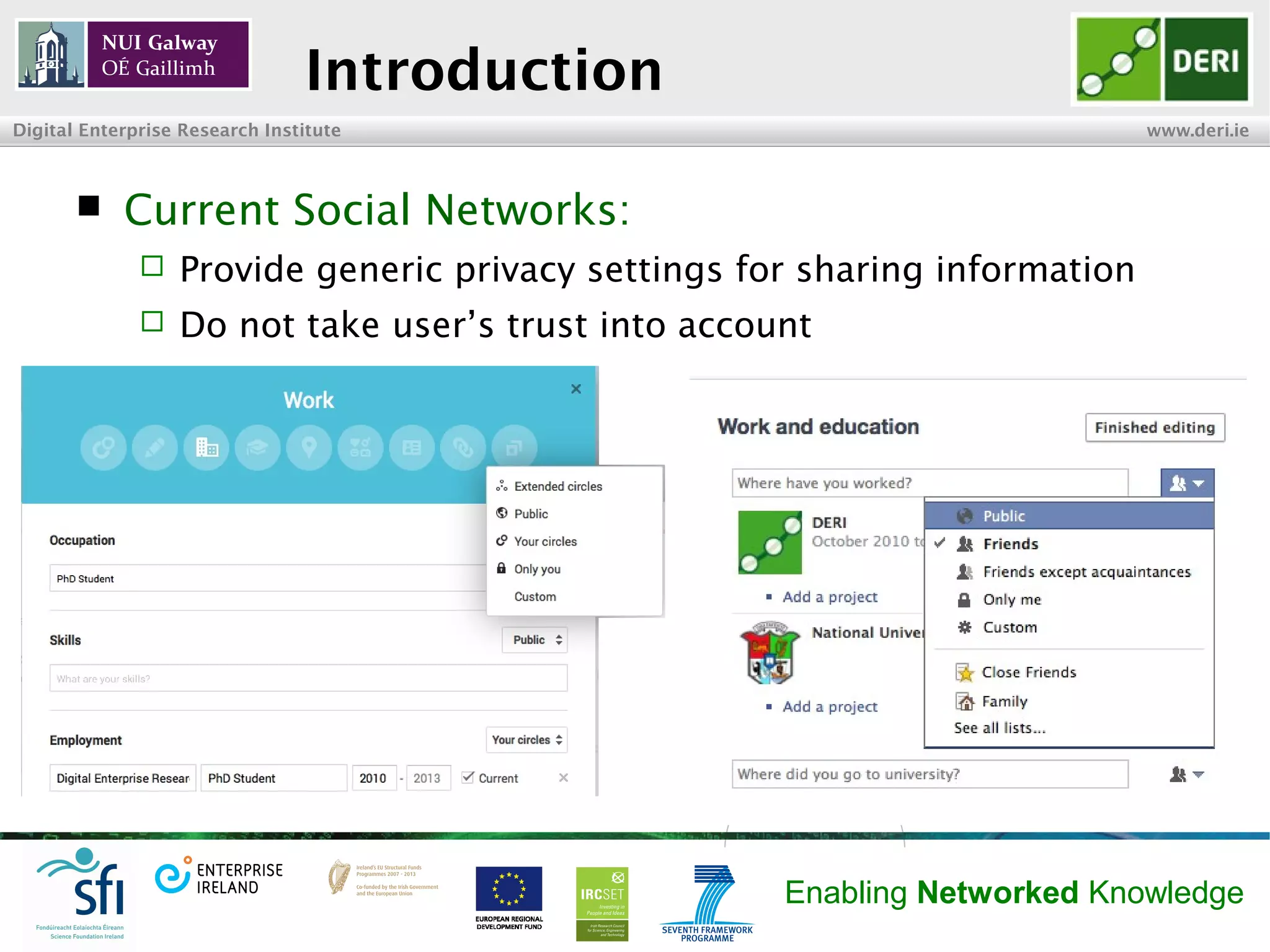
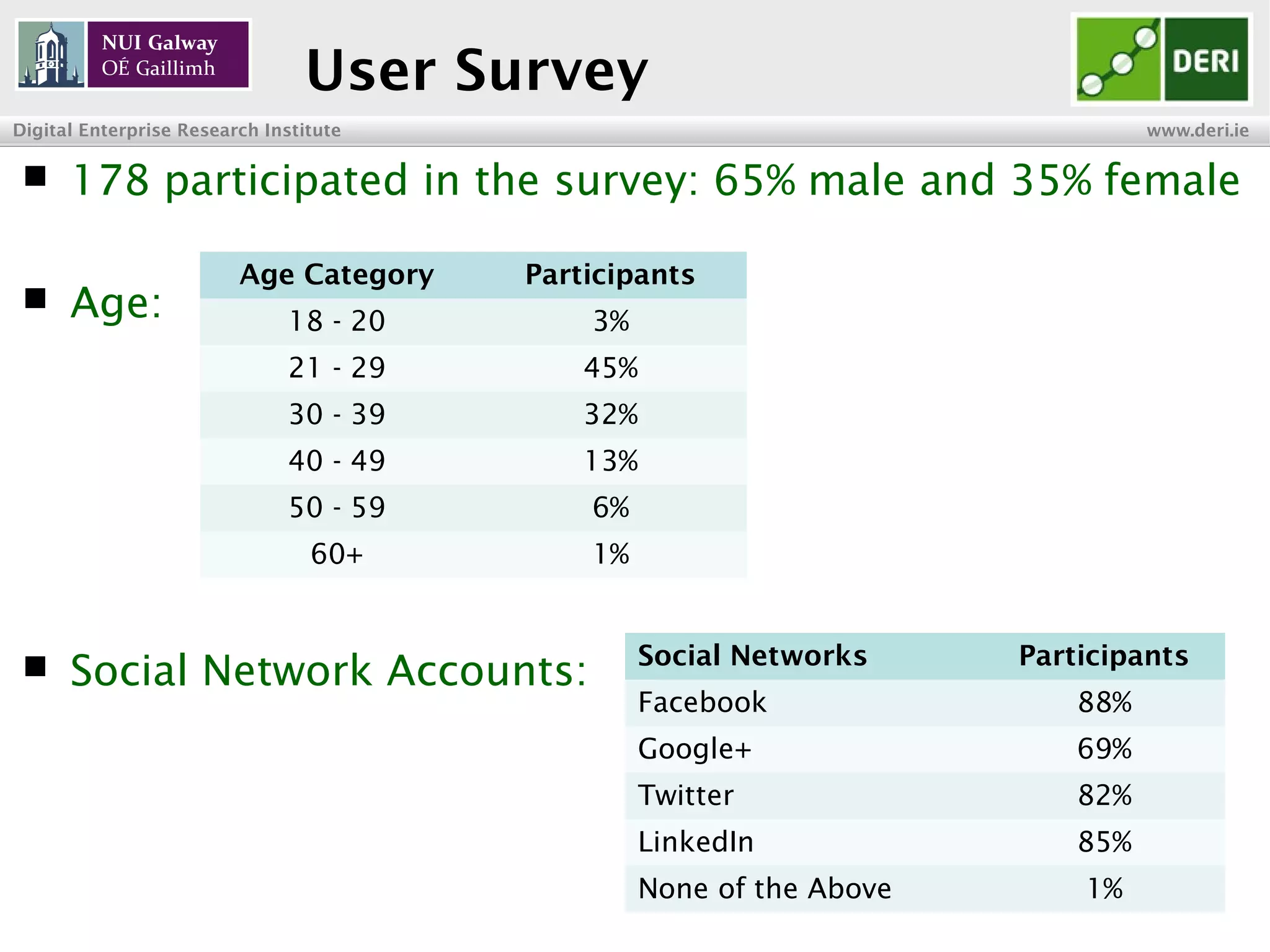
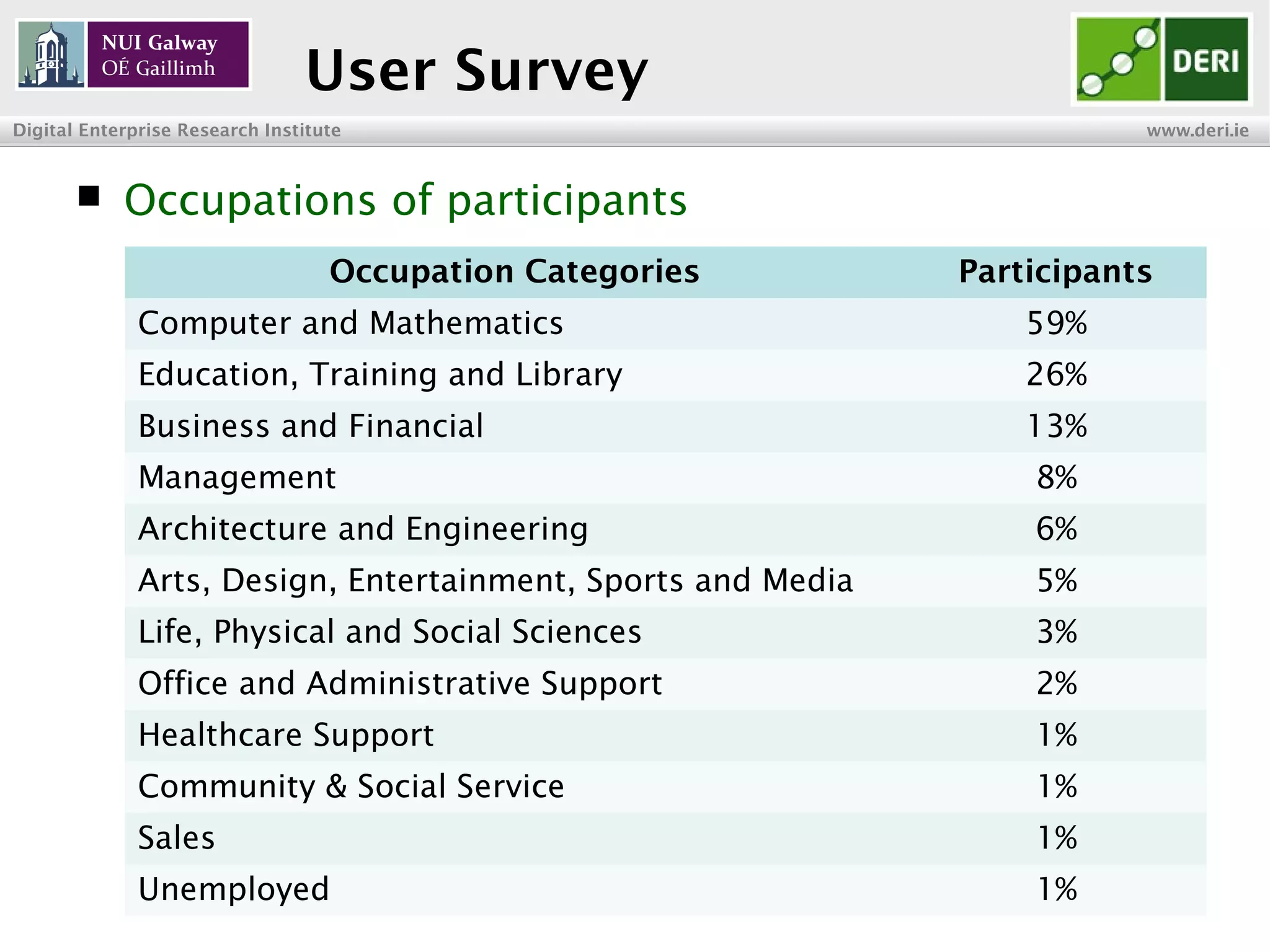
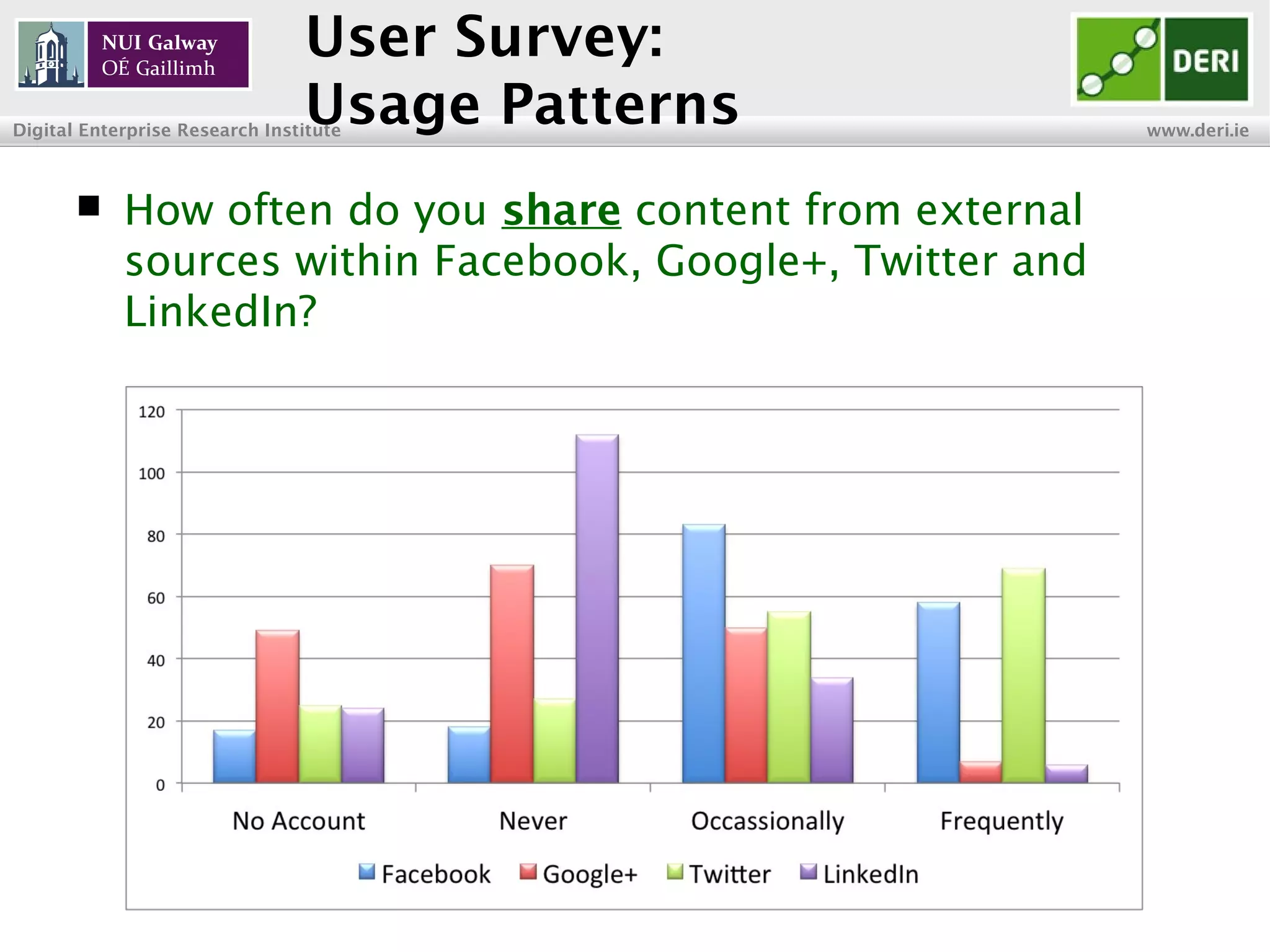
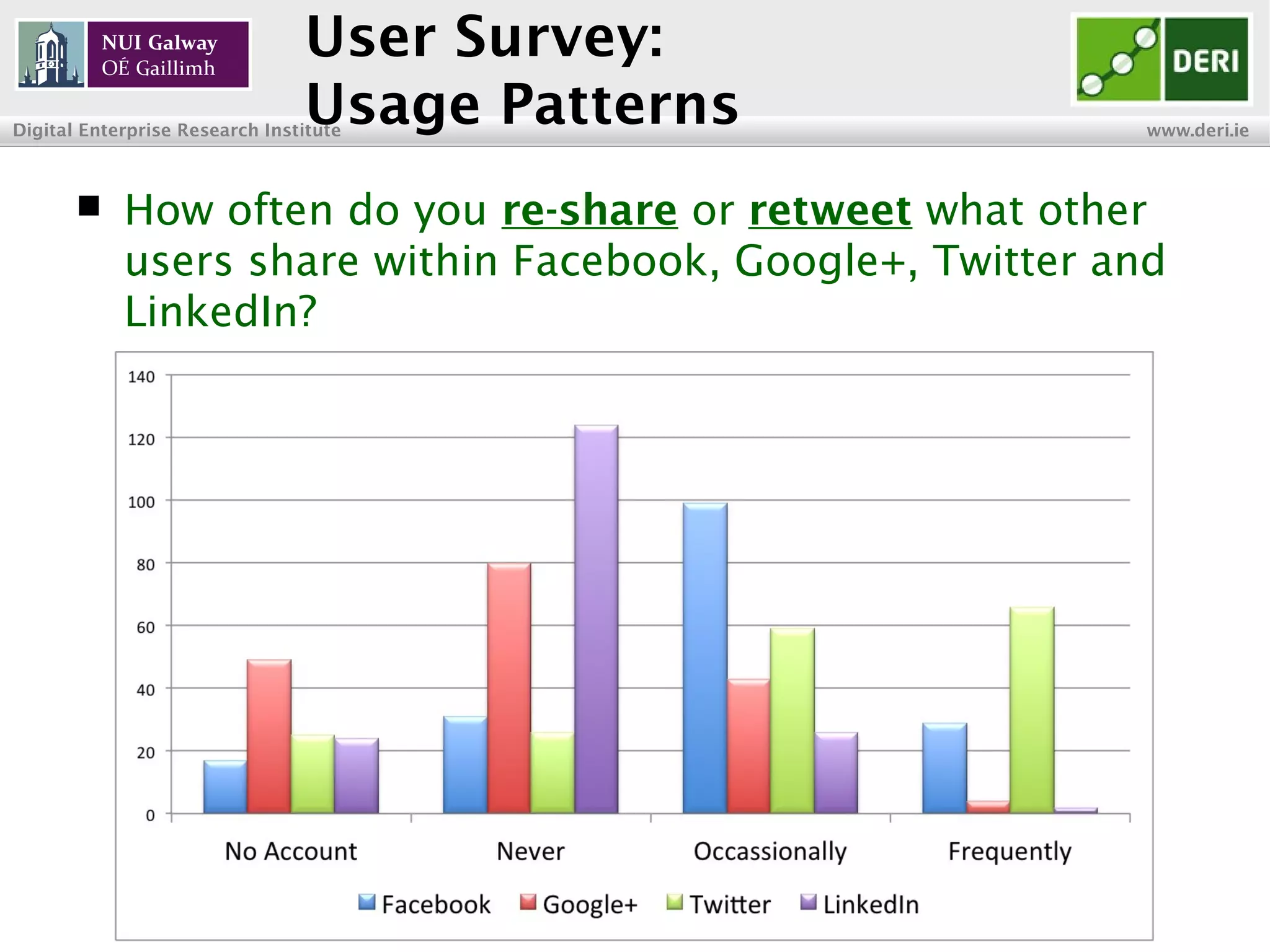
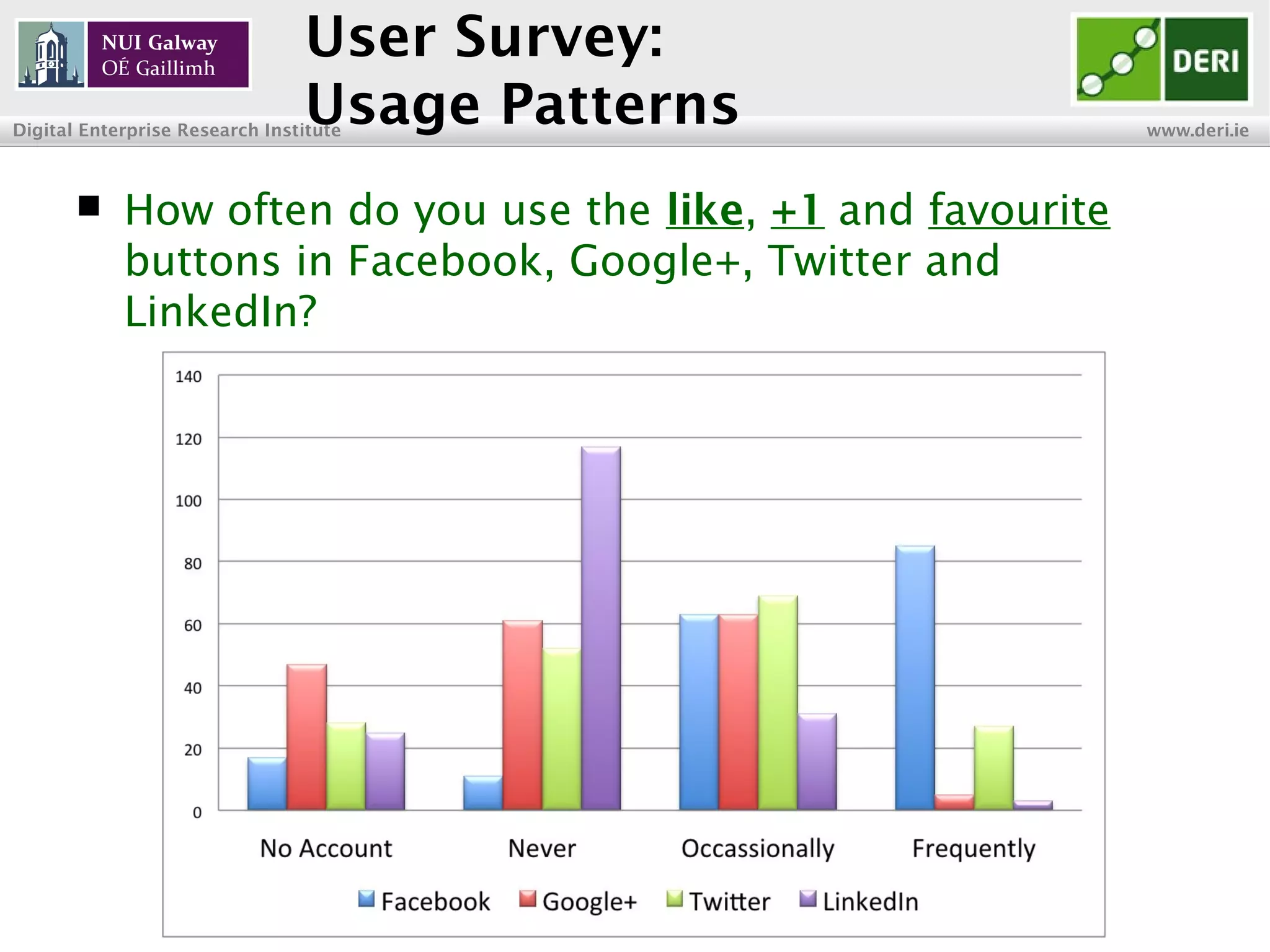
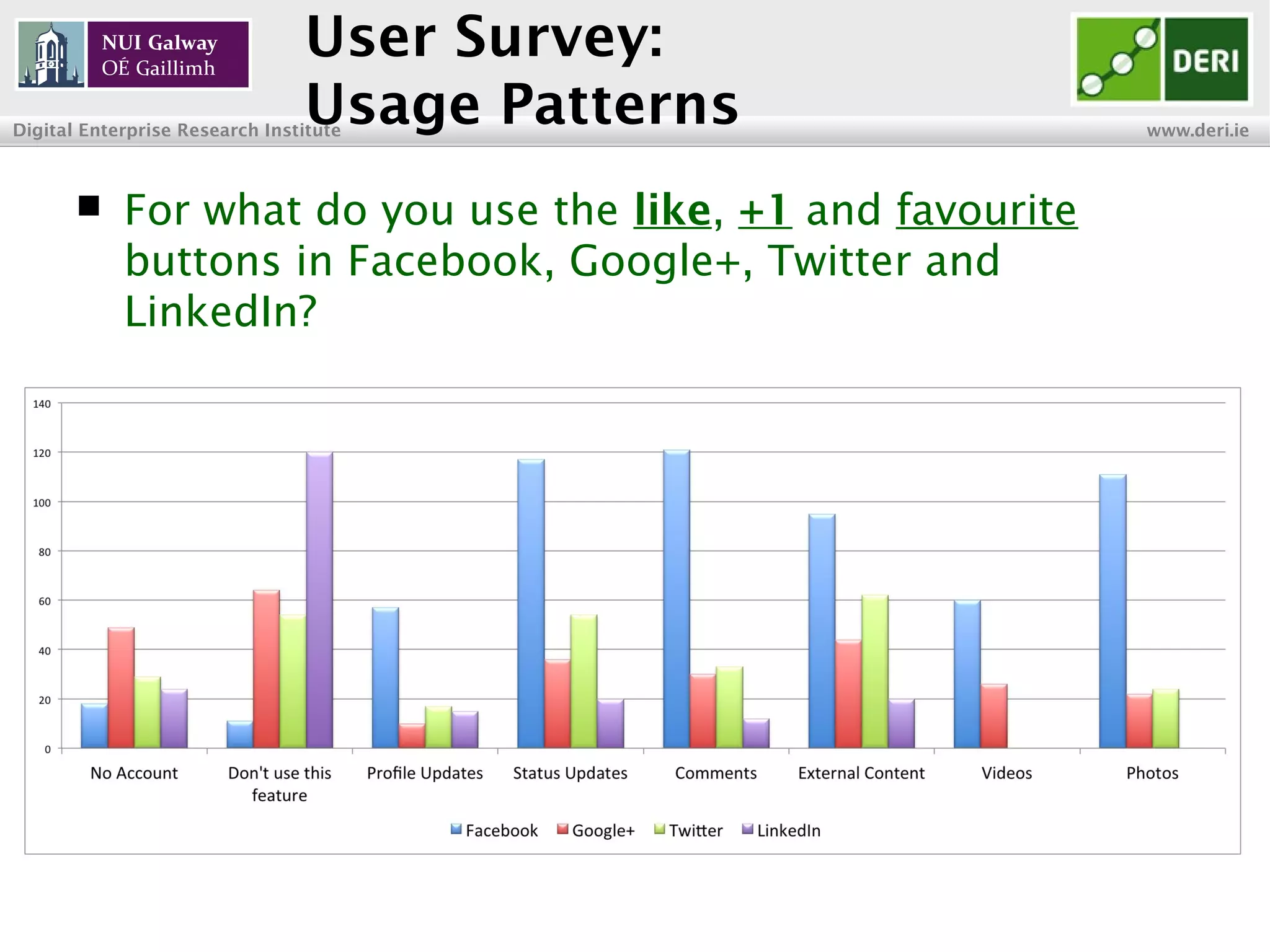
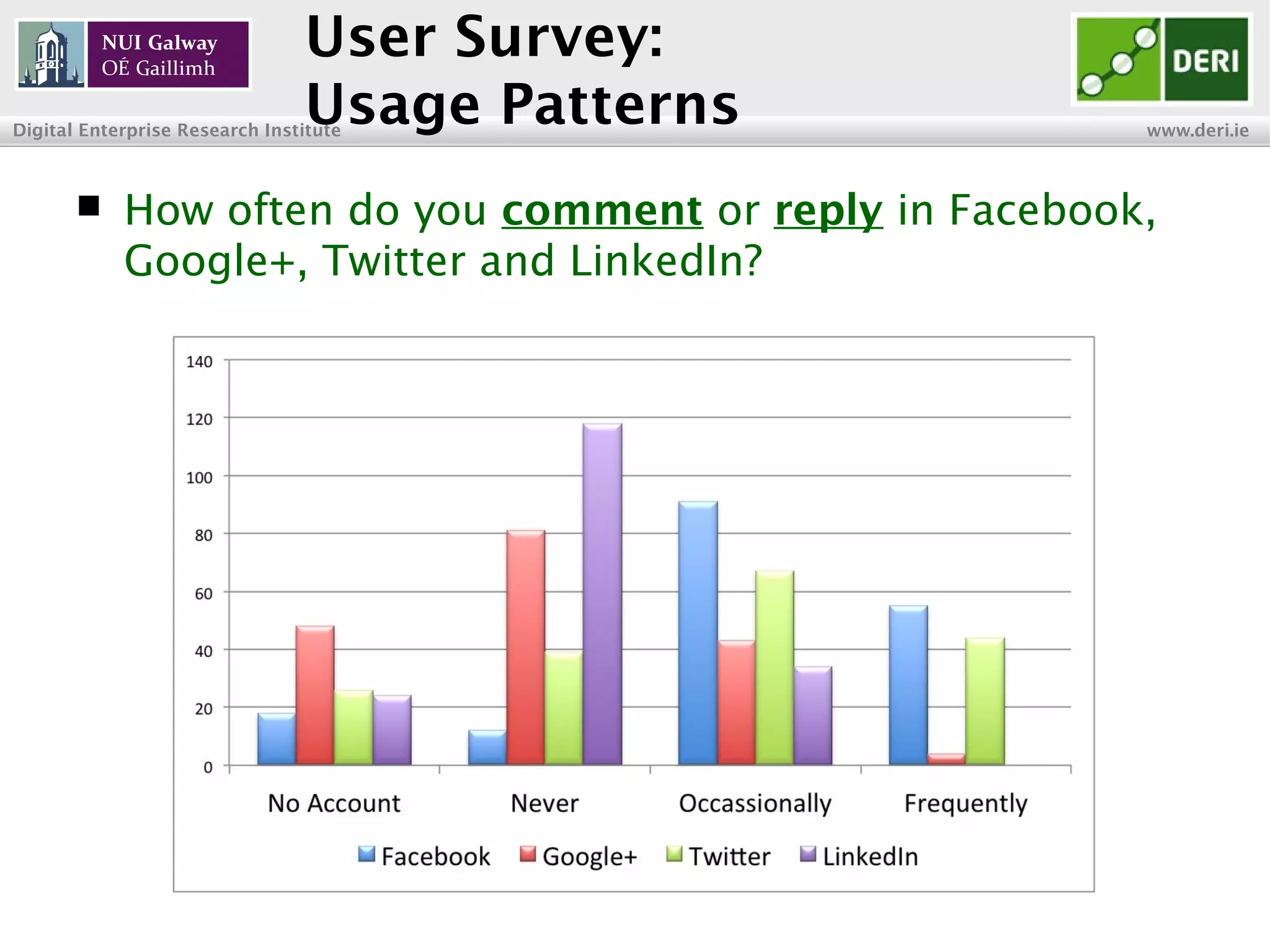
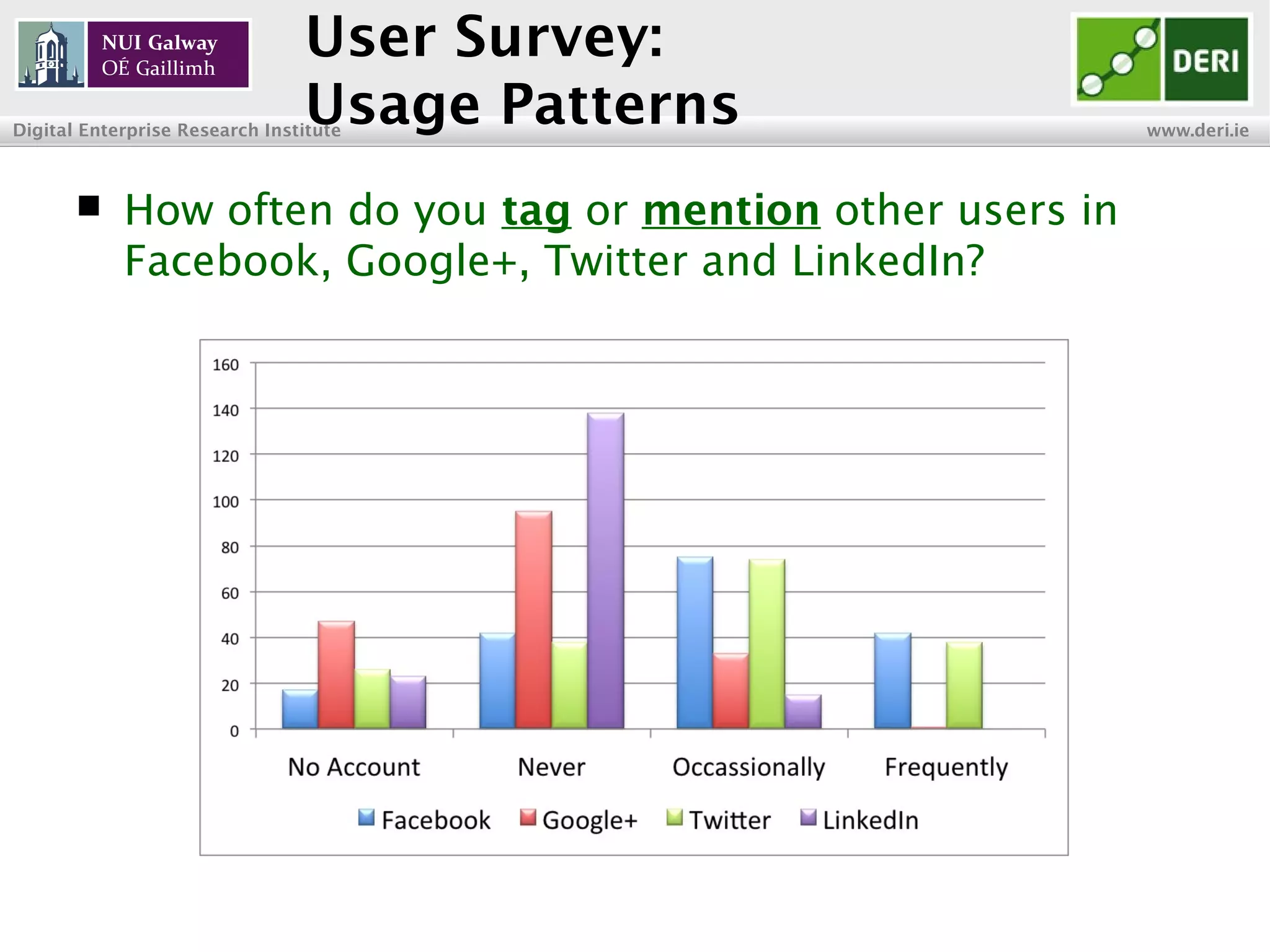
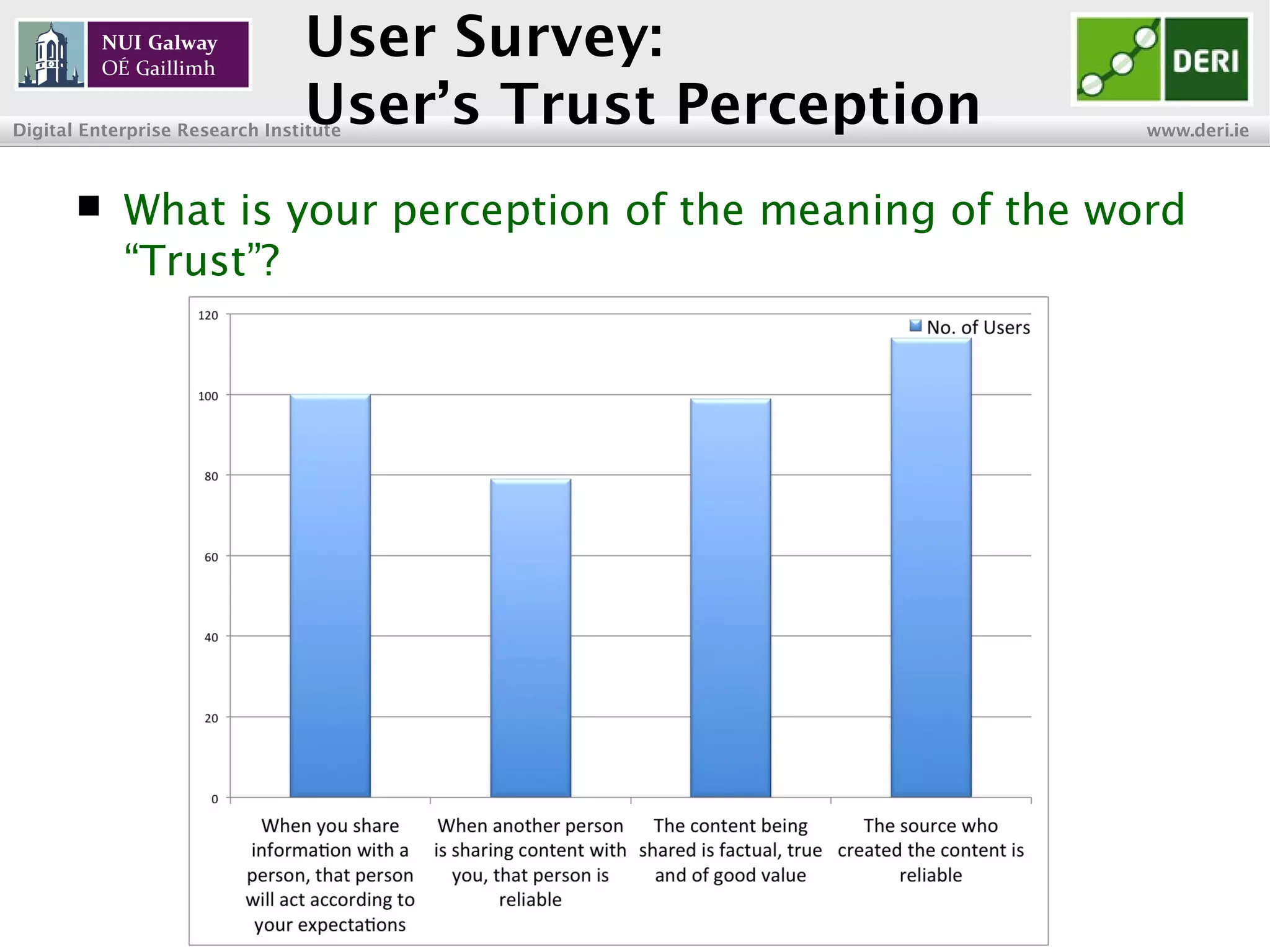
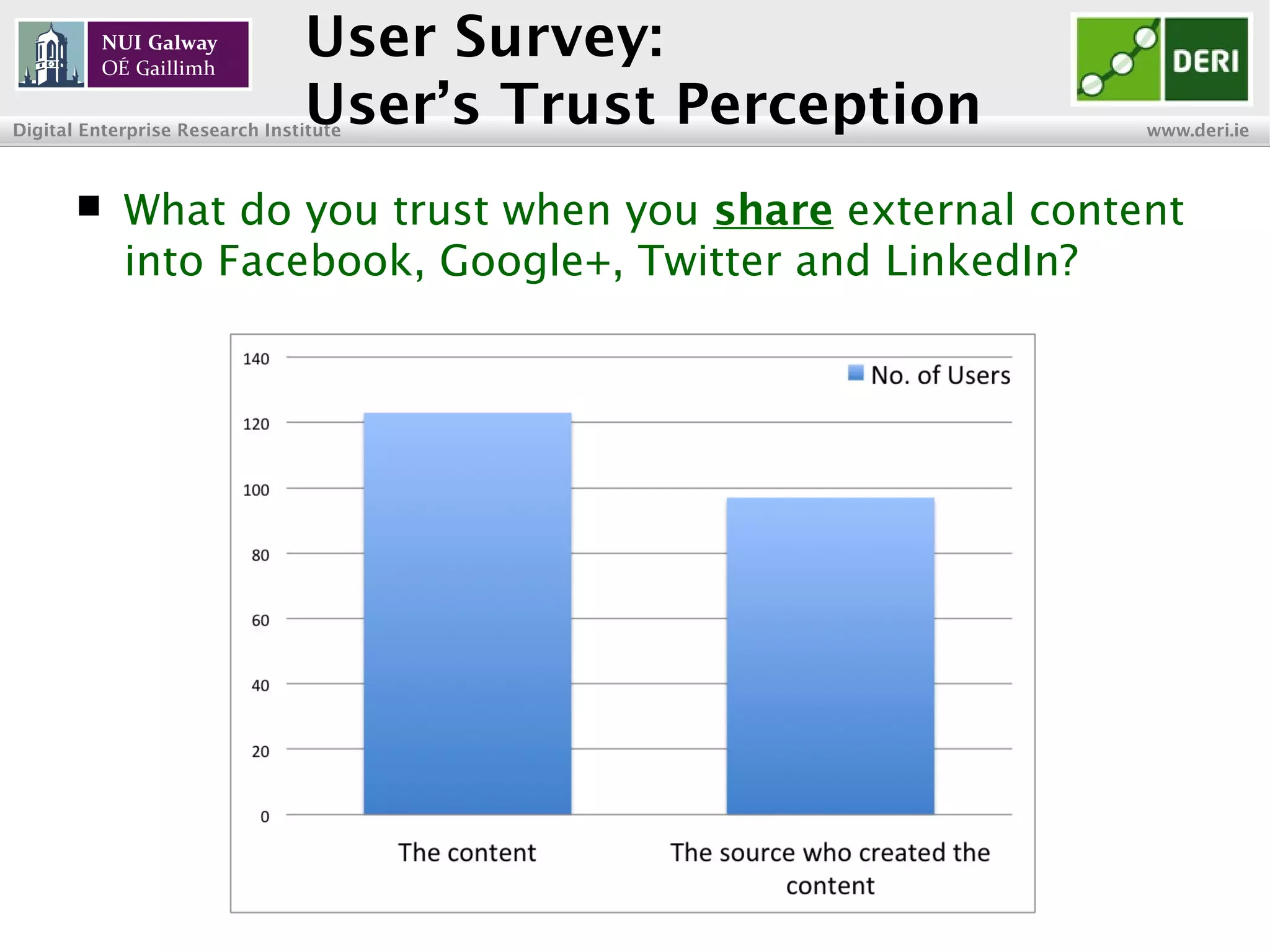
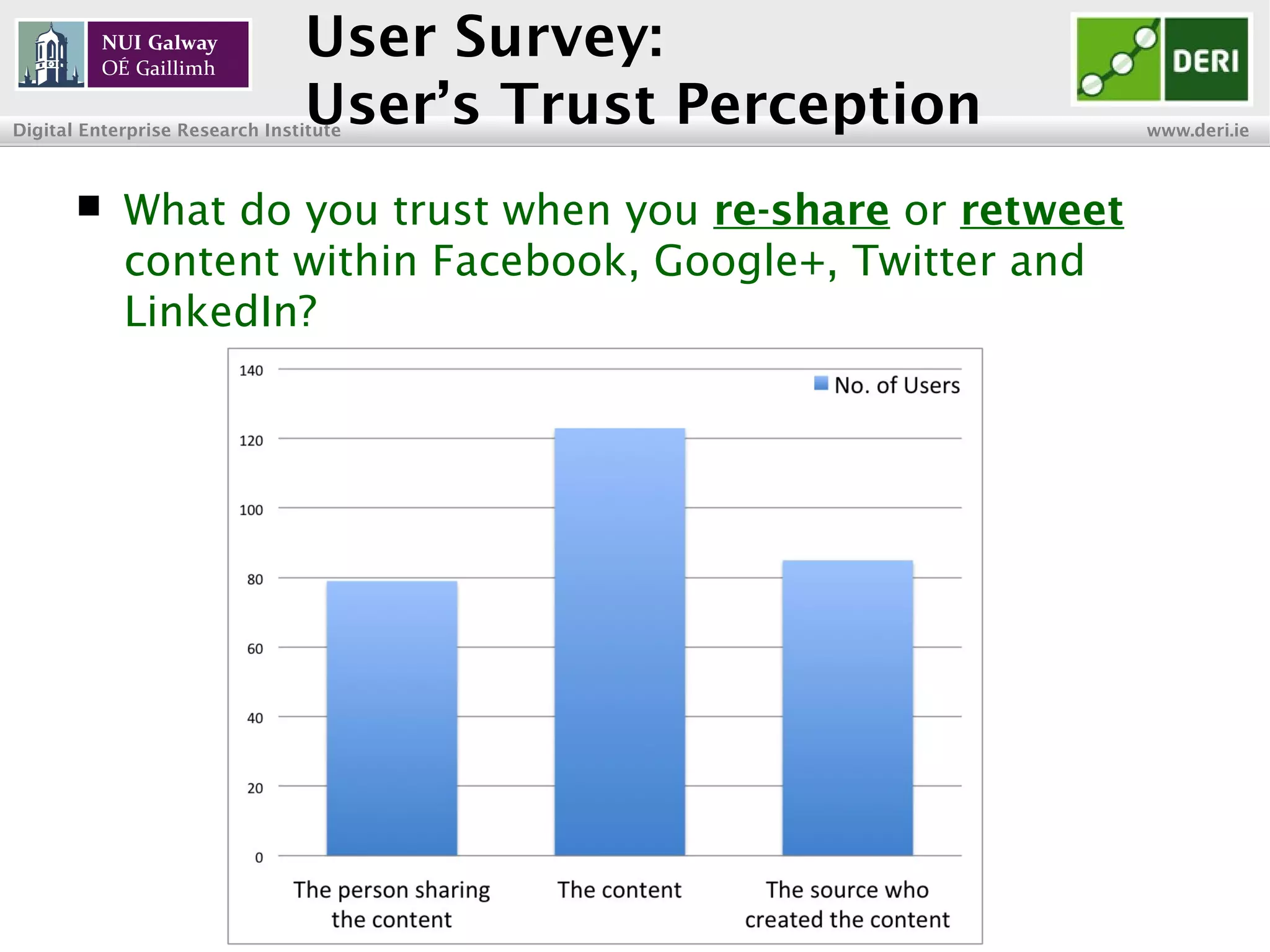
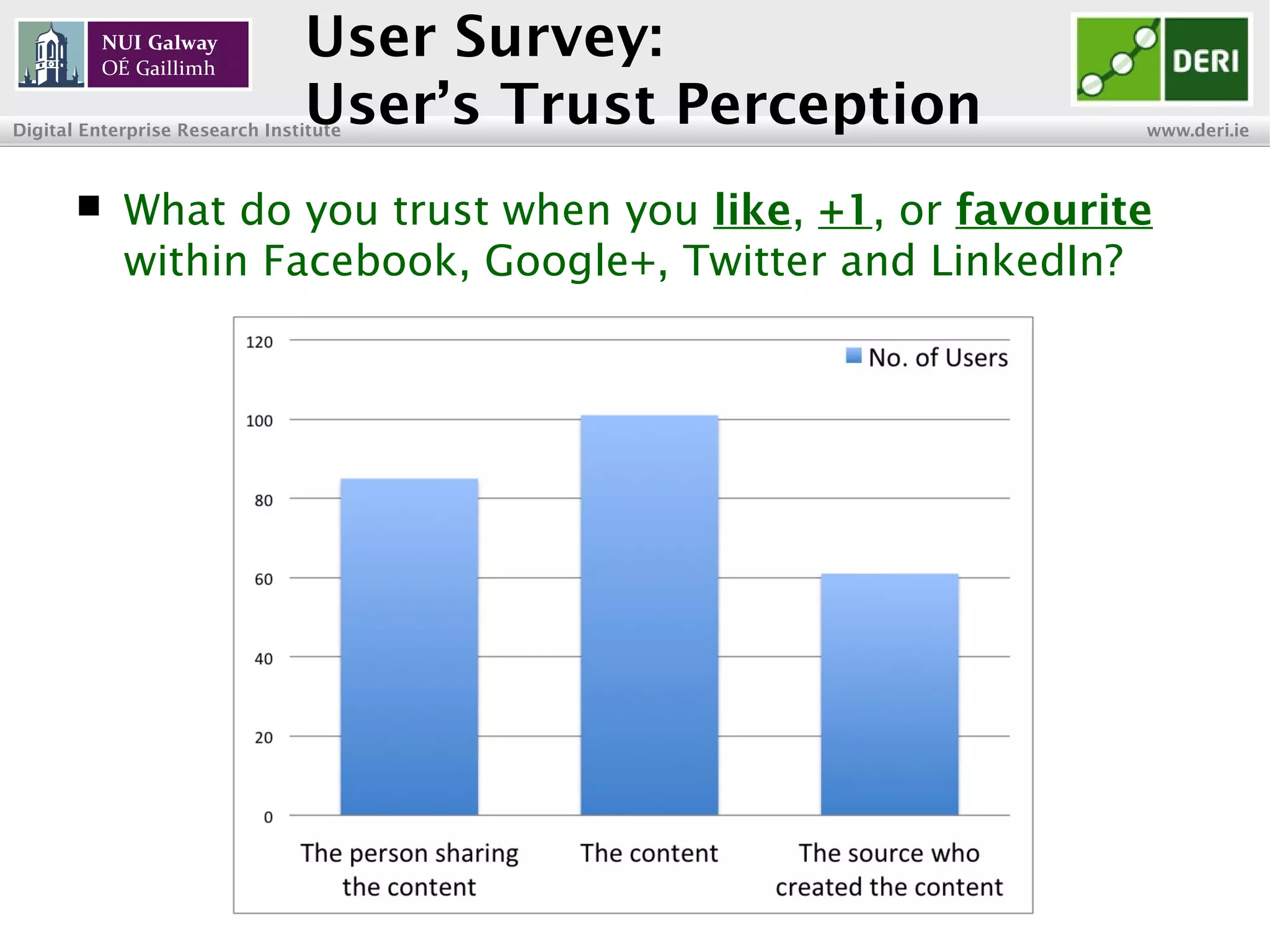
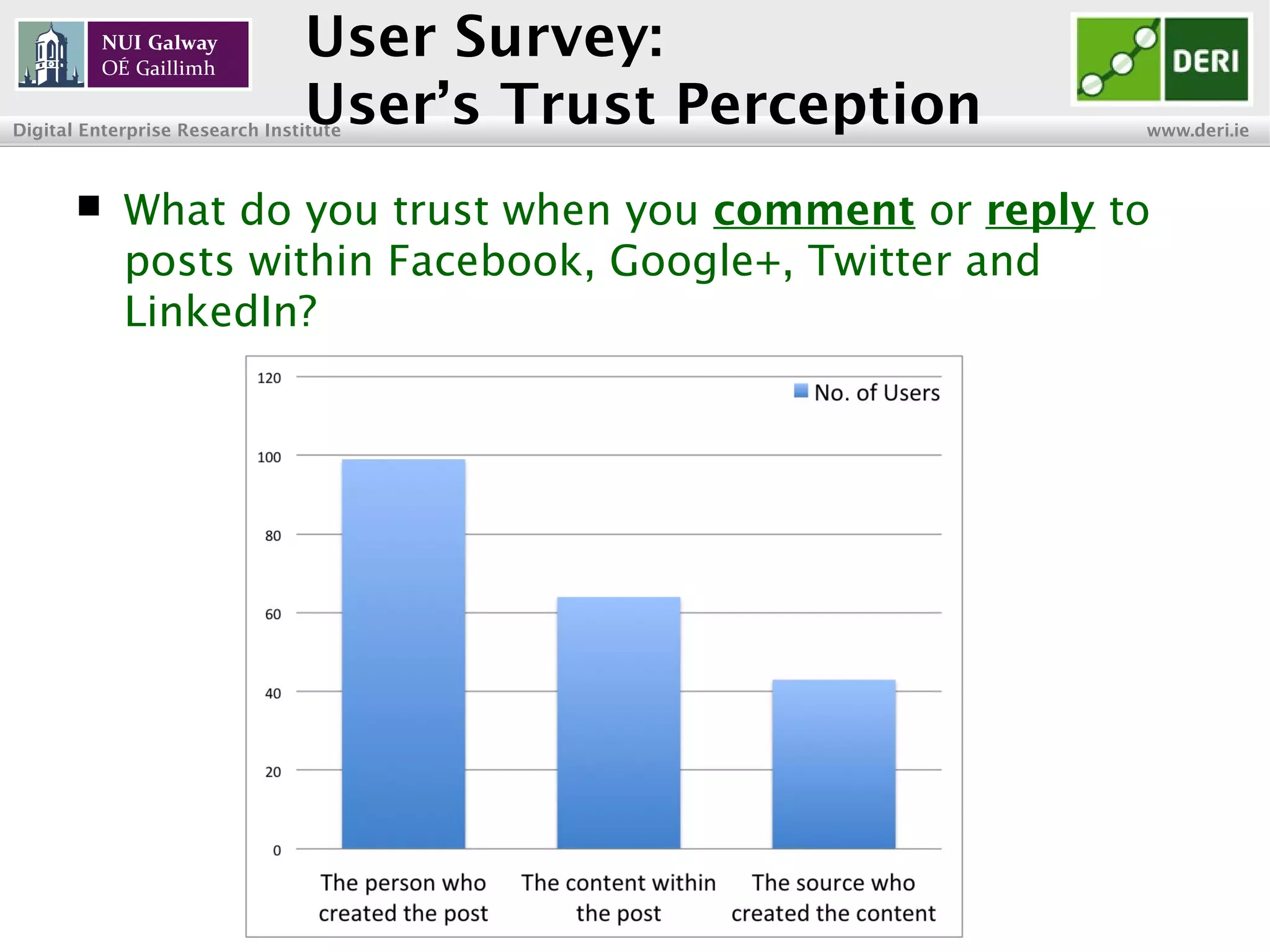
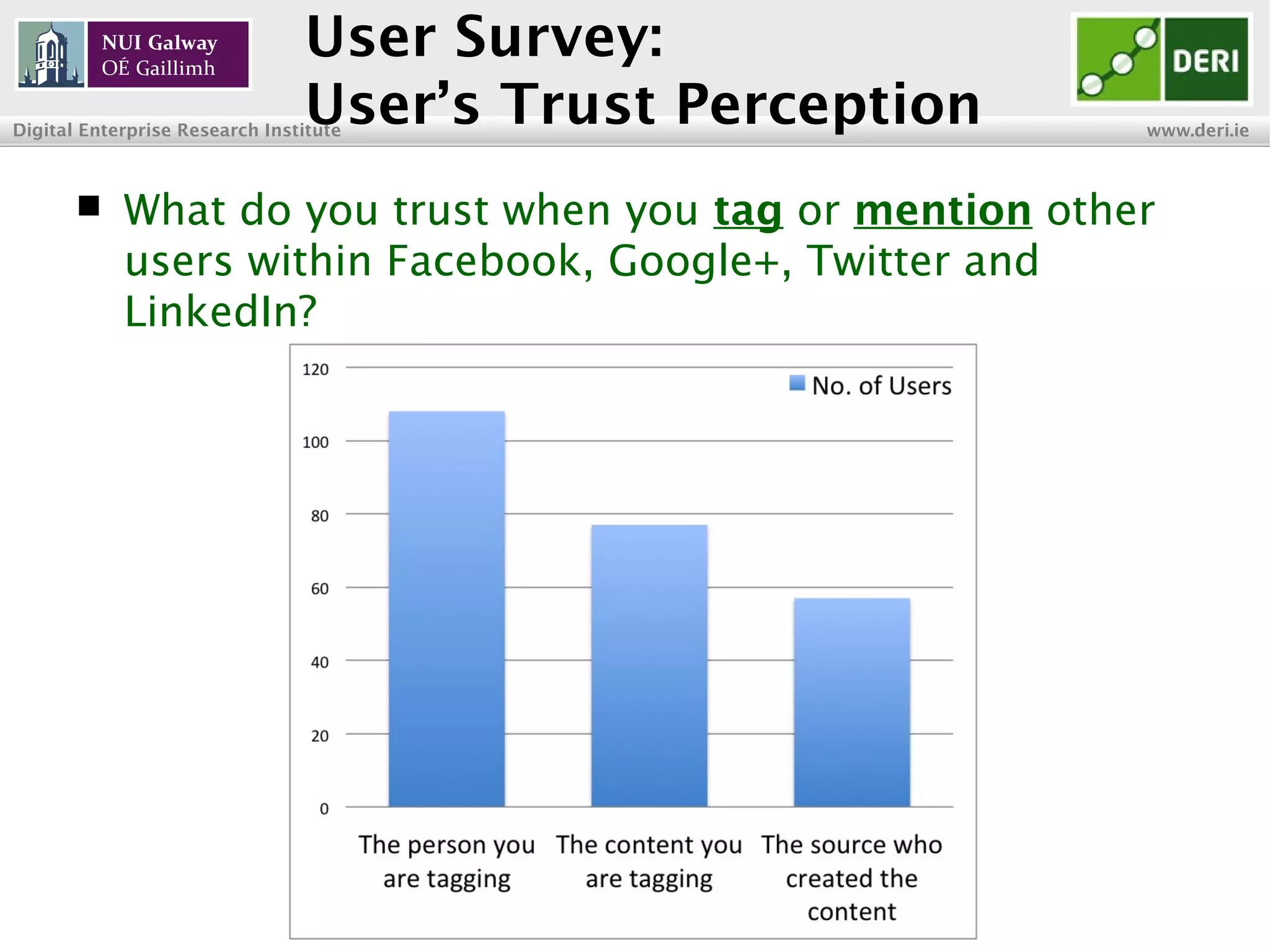
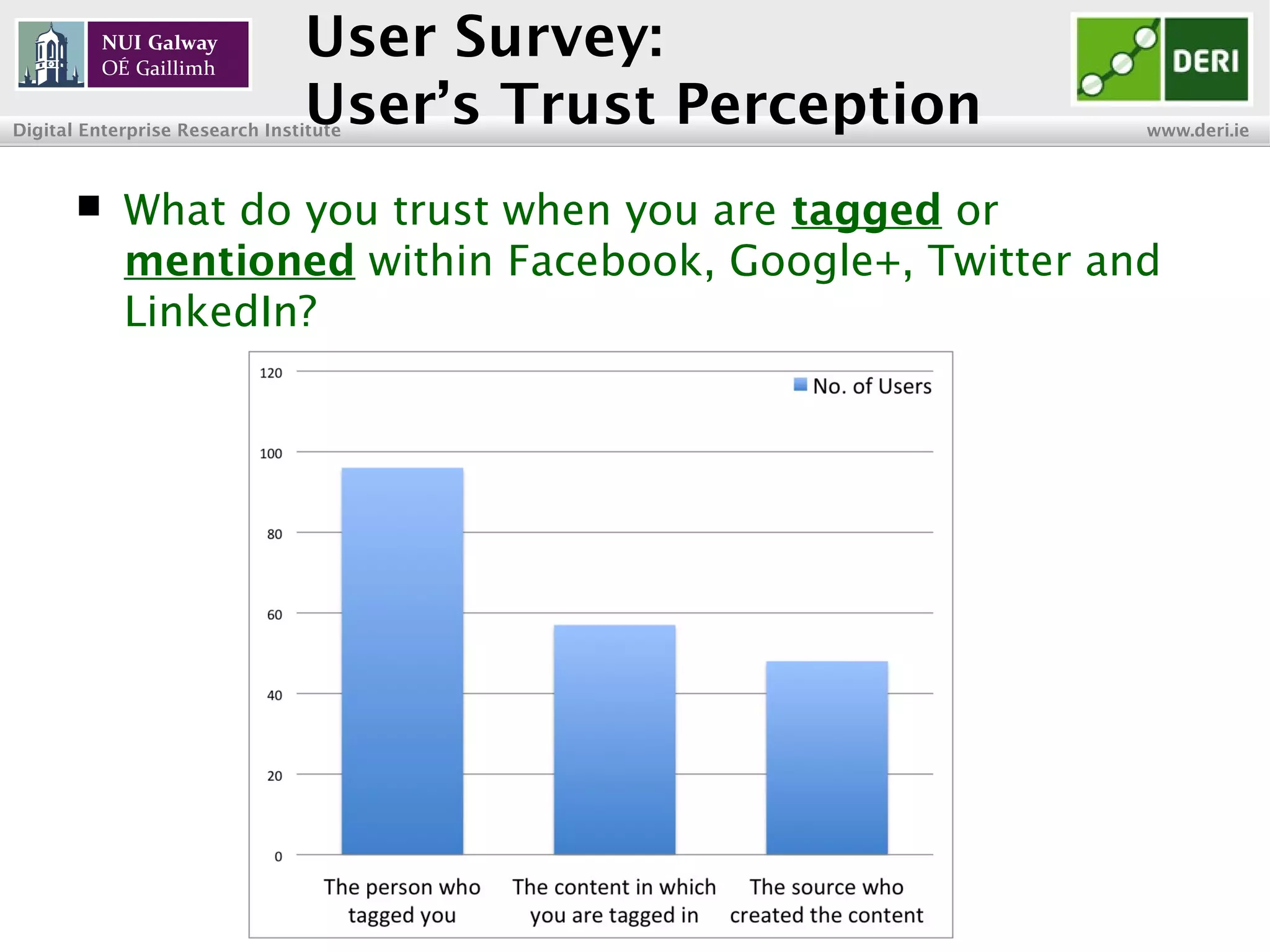
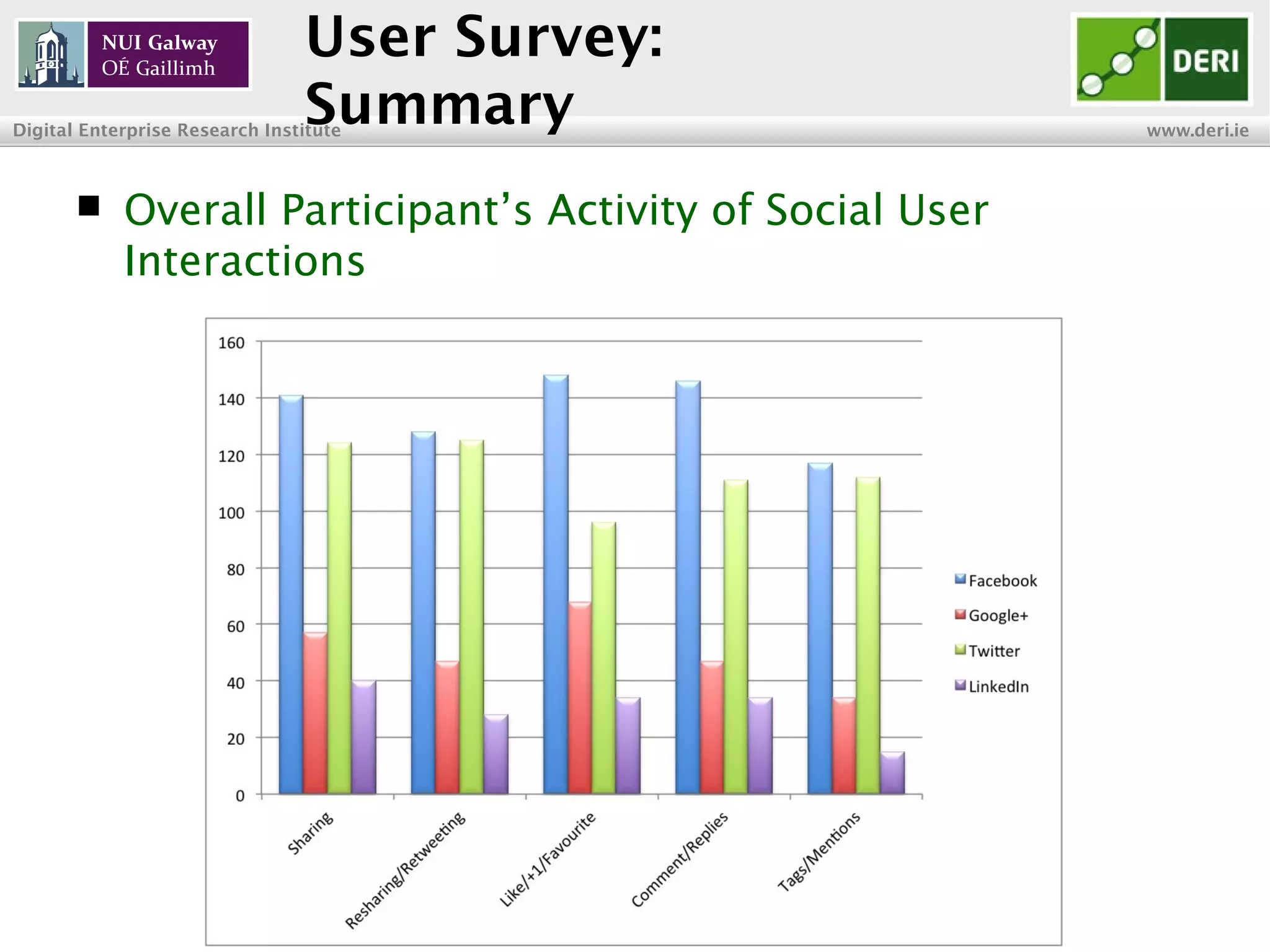
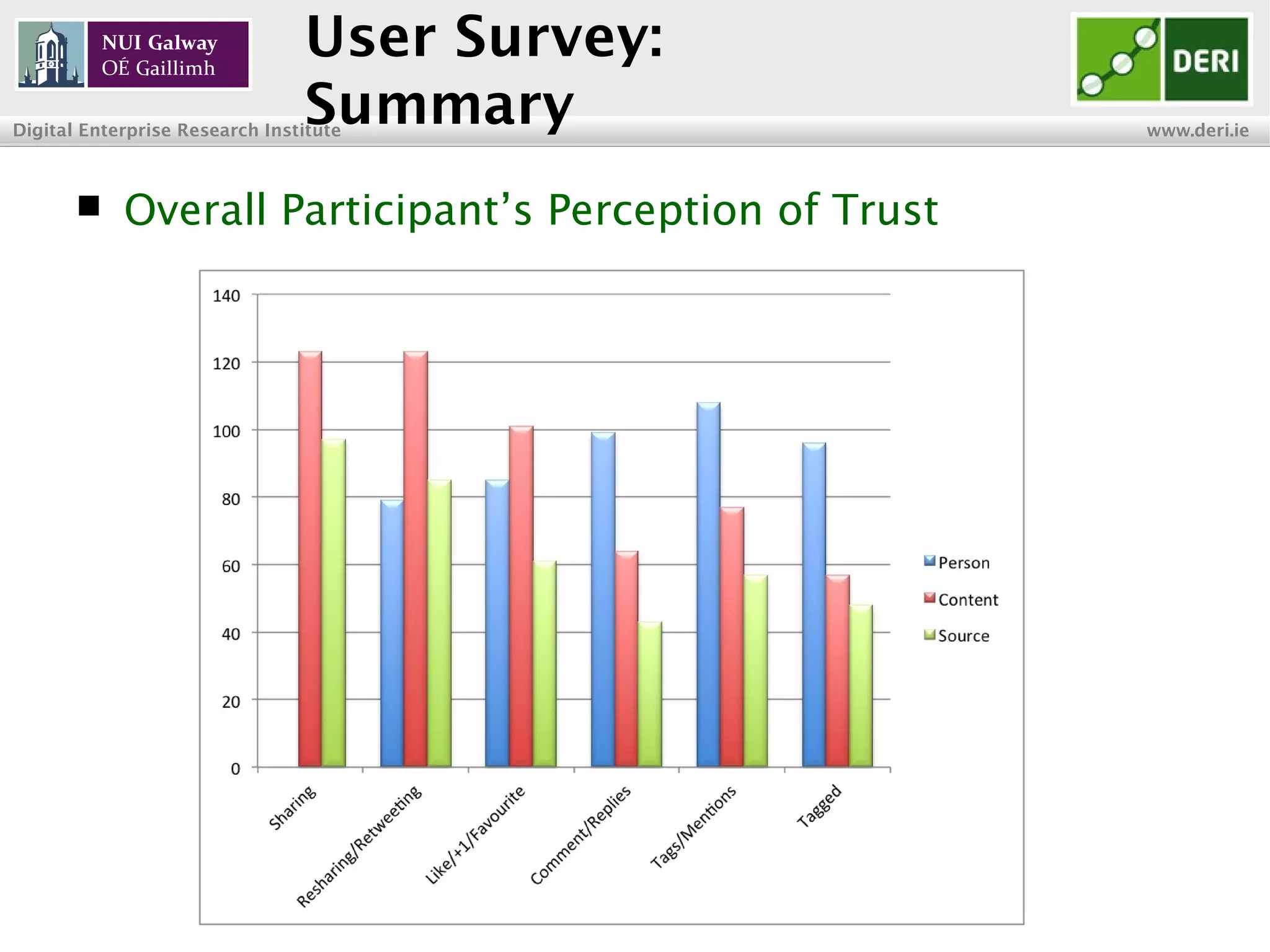
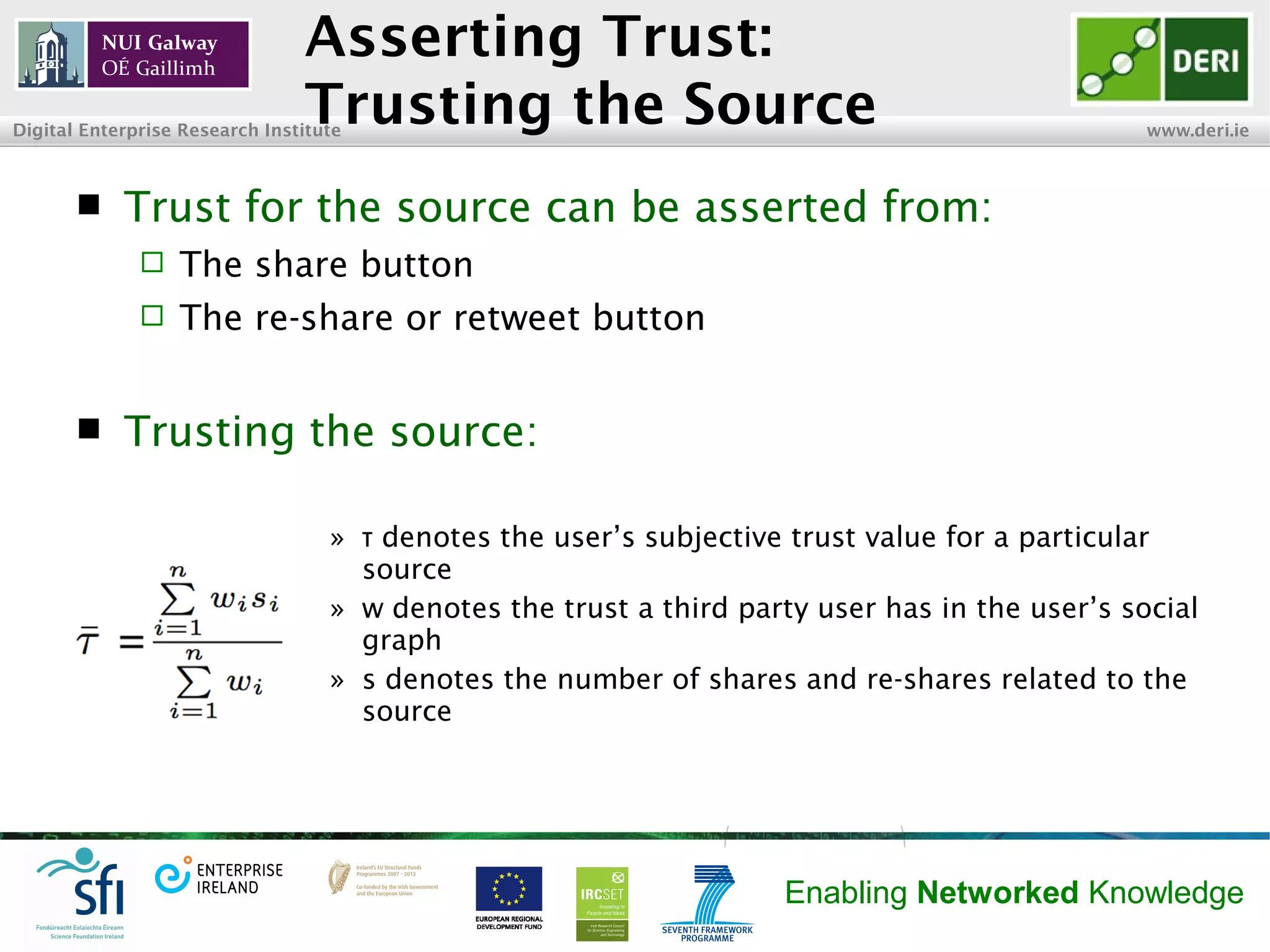
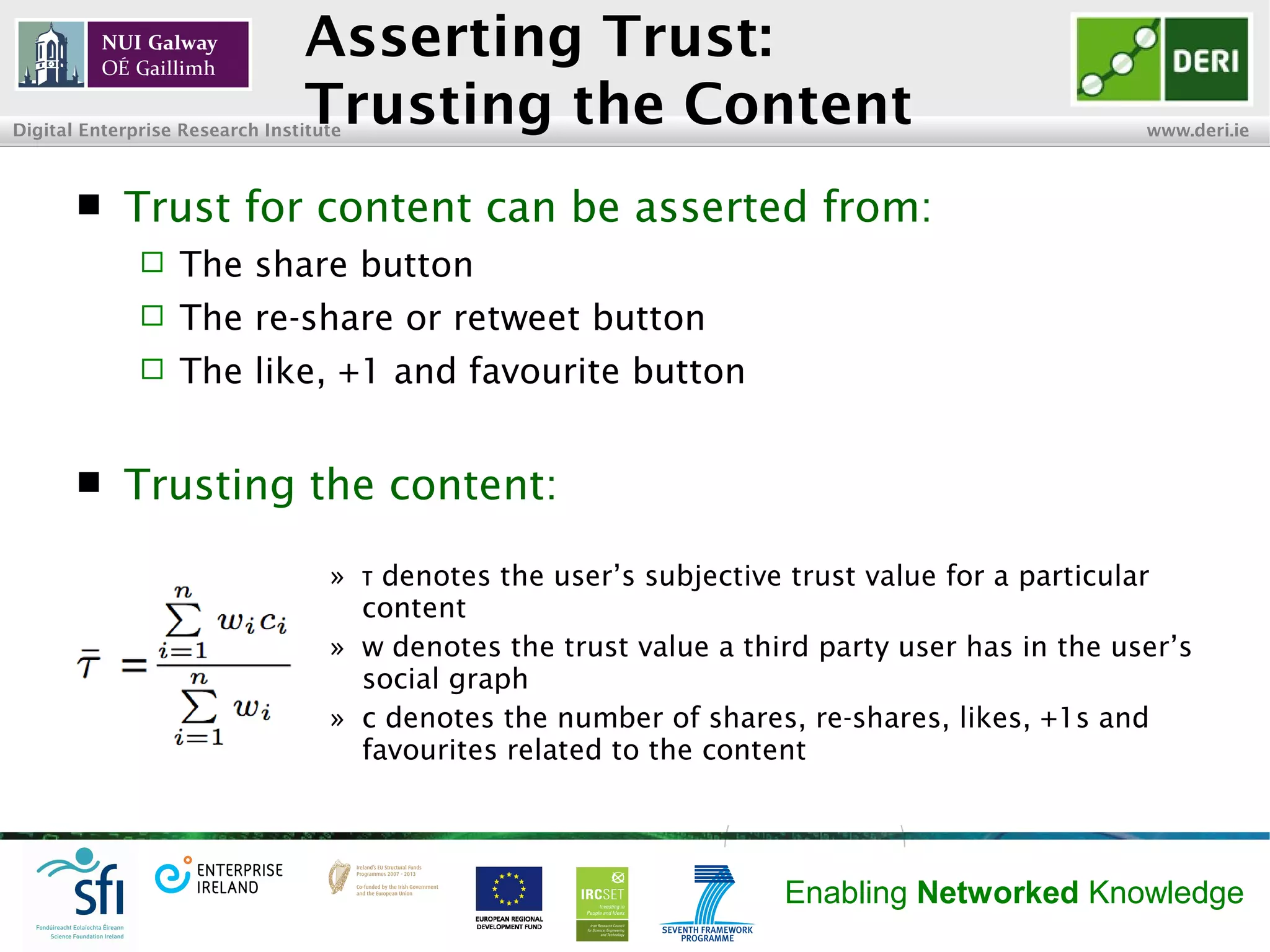
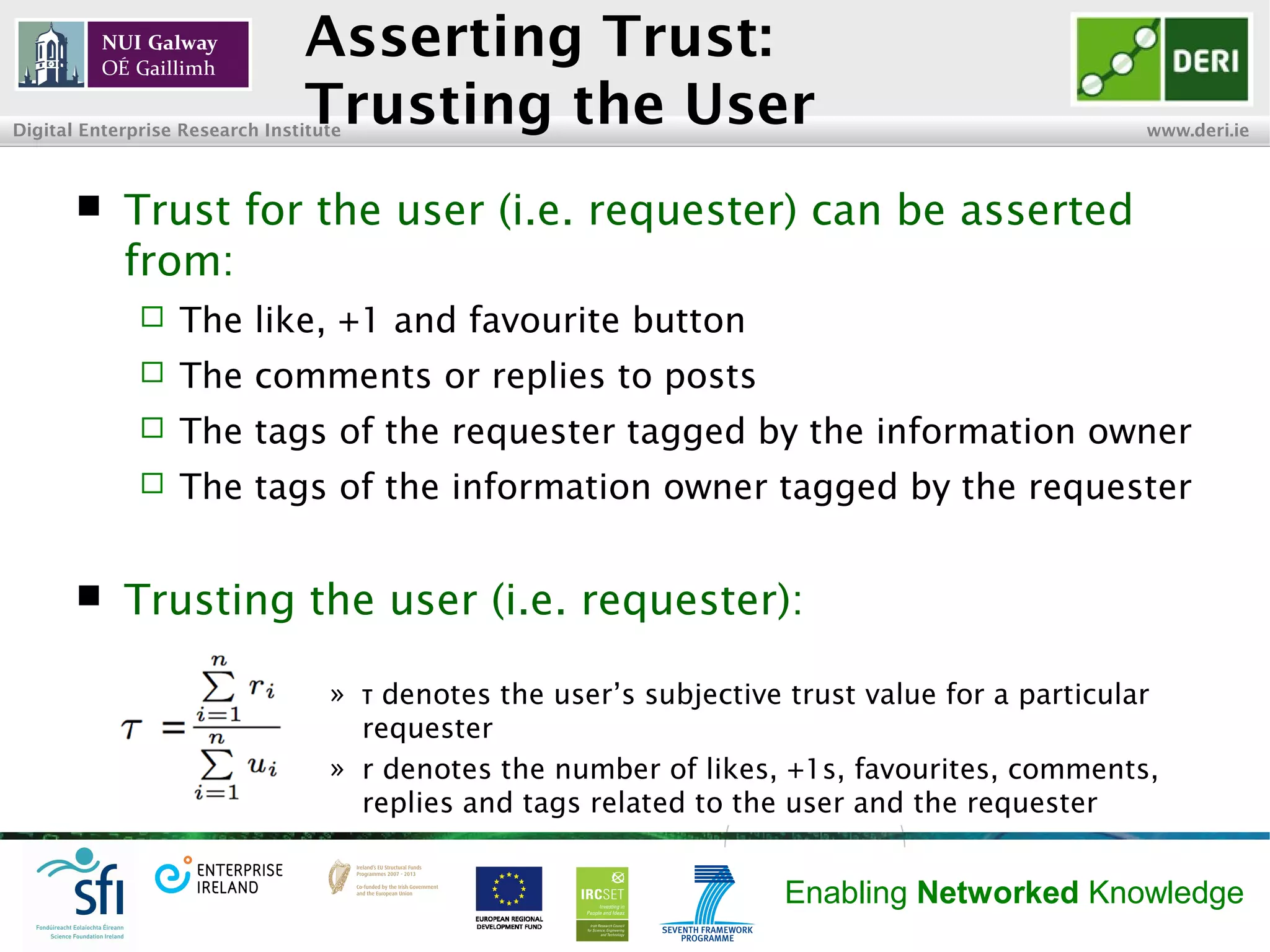
The document discusses research on how trust can be inferred from user interactions within social networks, highlighting the need for privacy settings that account for user trust. A survey of 178 participants explored their social media usage patterns and perceptions of trust regarding various interactions like sharing, liking, and commenting. The findings emphasize the importance of trusting the source, content, and individuals involved in social interactions, with future work aimed at implementing these insights into privacy frameworks.