2013 Democratization Of Technology How Cloud And Consumerization Change Everything
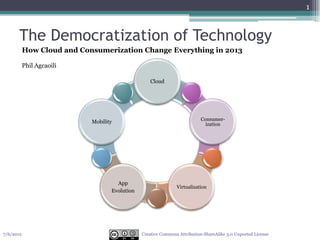
- 1. 1 The Democratization of Technology How Cloud and Consumerization Change Everything in 2013 Phil Agcaoili Cloud Consumer- Mobility ization App Virtualization Evolution 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 2. 2 Creative Commons 7/6/2012 Attribution-ShareAlike 3.0 Unported License
- 3. 3 Anytime. Anywhere. Any Device. A Collection of Devices Access Ubiquitous Services/Apps •Shifts in client computing ▫ Personal computers no longer the focus ▫ Smartphones, tablets, and other consumer devices •Emerging cloud services connect multiple devices ▫ Lots of choices for users ▫ Where, when, and how •The post-PC era ▫ Not really about being 'after' the PC ▫ Experiencing a new style of personal computing Frees individuals to use computing in fundamentally new ways Improves multiple aspects of their work and personal lives •Several driving forces are combining to create a new technology era •Trends have roots from the past decade, but aligning in new ways *Gartner 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 4. 4 Consumerization Home Technology Enters the Corporate Environment • Nothing new, consumer technology has been impacting corporate information technology for the past decade • Major wave is starting to take hold across all aspects of information technology as several key factors come together: ▫ Users are more technologically savvy and have very different expectations of technology ▫ The Internet and social media have empowered and emboldened users ▫ The rise of powerful, affordable mobile devices change the equation for users ▫ Users have become innovators ▫ Through the democratization of technology, users of all types and status within organizations can now have similar technology available to them 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 5. 5 Mobility Wherever and Whenever You Want • Mobile devices combined with the cloud can fulfill most computing tasks, • Tradeoffs are outweighed in the minds of the user by the convenience and flexibility provided by the mobile devices • Emergence of more-natural user interface experiences is making mobility practical ▫ Touch- and gesture-based user experiences ▫ Speech and contextual awareness ▫ Wearable and modular computing • Enables rich interaction with devices and a much greater level of freedom • Any given device will take on the role of the user's primary device ▫ Users have a web of devices ▫ Personal delivered at a new level, agnostic to the device itself 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 6. 6 Cloud Enabling, Flexible, and Cost-Effective Services • Cloud services individual users ▫ Business impact • Every user has a scalable and nearly infinite set of resources available for whatever they need to do • The impacts for IT infrastructures are stunning, but when this is applied to the individual, there are some specific benefits that emerge. ▫ Users' digital activities are far more self-directed than ever before ▫ Users demand to make their own choices about applications, services and content, selecting from a nearly limitless collection on the Internet • Encourages a culture of self-service that users expect in all aspects of their digital experience ▫ Lines are blurred between business and home • Opens a whole new level of opportunity 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 7. 7 Apps Evolution (of Applications) Applications Evolve to Apps • Changes occurring to the way applications are designed, delivered and consumed by users ▫ Simple but powerful ▫ Single purpose delivers • Applications can now be exposed in multiple ways and used in varying situations by the user ▫ Increases greater cross-platform portability ▫ Small user experience (UX) apps used to adjust a server- or cloud-resident application ▫ Unique characteristics of a specific device or scenario minimized HTML5 and Webkit • Profound impact on how applications are written and managed in corporate environments • Dramatic impact on all other aspects of the market ▫ Appstores ▫ Direct delivery ▫ Levels the playing field for competition 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 8. 8 Virtualization Enabling the Any Device Dream • Virtualization has improved flexibility and increased the options for how IT organizations can implement client environments • Virtualization has freed applications from the peculiarities of individual devices, operating systems or even processor architectures ▫ Eliminates browser compatibility woes ▫ Enables standardization • Virtualization provides a way to move the legacy of applications and processes developed in the PC era forward into the new emerging world • Low-power devices have access to much-greater processing power ▫ Expanding device utility ▫ Increases the reach of processor-intensive applications 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 9. 9 Conclusion • The combination of trends coupled with advances in new enabling technologies is ushering in the era of the personal cloud • The specifics of devices will become less important for the individual and organization to worry about • Users will use a collection of devices, with the PC remaining one of many options, but no one device will be the primary device • The personal cloud will take on the role of central need • Access to the cloud and the content stored or shared in the cloud will be managed and secured, rather than solely focusing on the device itself 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 10. 10 Creative Commons 7/6/2012 Attribution-ShareAlike 3.0 Unported License Democratization of Technology
- 11. 11 Problem Statement • A groundswell of new(er) technologies demanded by employees requires a new strategy to enable and empower employees ▫ Smart phones - 14% of US employees use smartphones for work today; 8% buy their own* ▫ Cloud services – more and more of our internal services are being outsourced, use of services like GoogleDocs, DropBox, etc. ▫ Social technology - 17% of employees use social technologies for work* *Forrester 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 12. 12 Why • These technologies are being used for multiple reasons ▫ Serving customers better ▫ Getting our jobs done better ▫ People are used to using these technologies at home More than half of US employees say they have better technology at home than at work* 37% of US information workers are solving their customer and business problems using technology they bring from home* • It isn‟t just about the latest technology ▫ While this may be one factor, it isn‟t the driving factor for most 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 13. 13 Reality • Employees are going to use the technology anyways ▫ “It was something I use in my personal life and wanted to use it at work” – 43% of US workers surveyed ▫ “I needed it and my company didn‟t provide an alternative” – 35% of US workers surveyed ▫ “It is better than what my company provided” – 24% of US workers surveyed • Business units and employees are moving ahead with solutions that meet their needs, with or without IT‟s or Security‟s guidance and support 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 14. So what are we going to do? 14
- 17. Throw Money at the Problem?
- 18. That would be nice… …but who can afford that?
- 19. Think different.
- 20. We have an opportunity to address the risks & leverage the benefits before the cloud becomes ubiquitous
- 21. 21 Possible responses Strategy and Free for all Not allowed measured approach using risk as a guide Questions we should be asking: – What are people really trying to do? Help customers better, use what they like to use (i.e., use at home)? – What is the value to the business? – What are the risks? – Assuming the business case holds, how can the company support the activity? 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 22. 22 What’s missing? • We aren‟t getting in front of the issues and enabling internal and external users ▫ The technology and policies are the answer, but what are the problems our employees are trying to solve? ▫ Are we asking them? ▫ Do we know what users are trying to do so we can propose the right processes and technical solutions? • People, Process, and Technology ▫ Policy ▫ Resources to handle new devices to manage ▫ Secure containers and sandboxes ▫ Change how we provide remote access 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 23. 23 Risks of doing nothing • We have multiple groups trying to solve the issue ▫ Risk of not solving the real problem ▫ Risk of ending up with multiple solutions (i.e,. No standardization or governance) • Lack of an enabled workforce resulting in less innovation ▫ How does the lack of current technologies affect our ability to innovate (and do we know where innovation will come from)? ▫ What are your competitors doing? 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 24. 24 Stakeholders • This topic or set of topics impacts many different stakeholders ▫ IT/Enterprise Architecture– non-standard solutions may proliferate ▫ Operations - someone has to support the enabling technologies ▫ Security – what are the risks? ▫ Legal – what are the liability issues? ▫ Customer Care – how can we use these technologies to better service our customers? ▫ Regional Teams – already gathering business requirements ▫ Product/Strategy – using current technology is critical to keeping up with (or getting ahead of) our customers and their expectations of our services ▫ HR – policies and procedures ▫ Customers – if we aren‟t current with technology at work, how will be innovative for our customers? 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 25. 25 Why security cares • Security is normally the first blockade used to discourage the use of new technologies • Each of these new ways of doing business involve risk ▫ A risk based approach gets the issues on the table so the business has a say in the decisions that are made around new technologies ▫ Understanding the risks puts security in an enabler role vs. a „just say no‟ role • The ability to support some or all of these technologies requires a new way of doing security at most companies 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 26. 26 Why security cares • Most rely on infrastructure protections (firewalls, locked down workstations and laptops) to provide protection • This method makes it challenging to support these new technologies ▫ Do we know who has access to our data (employees, contractors, 3rd parties)? ▫ Do we know where our data is? ▫ Is your internal network flat? • We need to provide a flexible security architecture that protects our data and resources from the inside out ▫ This will allow us to enable these new ways of doing business while managing risk • Security areas such as Identity Management, data protection, remote access and remote device management need to be focused on ▫ Virtualization/VDI/Citrix/Remote access may be the solution, but for which problem(s) 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 27. 27 Conclusion • Security must take a position on these trends • Security must be preparing to enable these services ▫ Change security model (Phil‟s perspective) Treat all end points as hostile Focus on most important data Collapse core(s) Evolve remote access paradigms Focus monitoring and application of fundamental security measures (ISO 27002, PCI DSS, etc.) • We need to manage risk • We need to embrace the changes ahead 7/6/2012 Creative Commons Attribution-ShareAlike 3.0 Unported License
- 28. Let’s review this entire presentation…
- 29. The World is Changing…
- 30. …and we can’t keep doing what we’ve been doing
- 31. We have to do something… Secure different.
- 32. 32 Creative Commons 7/6/2012 Attribution-ShareAlike 3.0 Unported License Thank You. Phil Agcaoili Twitter: @hacksec
Editor's Notes
- 1. We have a unique opportunity to define new security controls and identity risks and threats before we see full ubiquity of the cloudThis is a big opportunity for the industry because of where we are today and where the cloud is headed. And make no mistake, security is the biggest challenge we are all facing.
