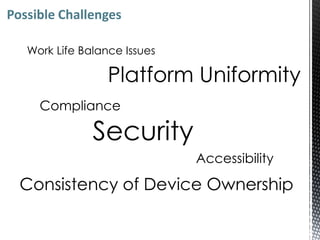
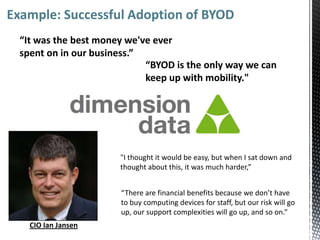
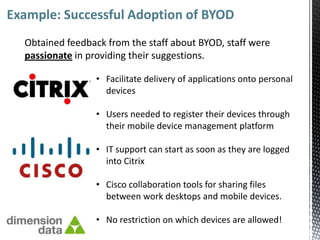
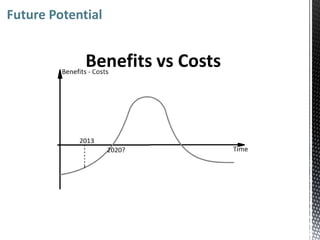
This document summarizes a presentation about mobile consumerization trends in businesses. It discusses how consumer mobile devices like smartphones and tablets are increasingly being used in the workplace. This brings both organizational benefits like reduced costs and improved productivity, but also challenges around security, management of personal devices on business networks, and maintaining a separation between work and personal life. It provides an example of a company that successfully implemented a "bring your own device" policy. Finally, it discusses future trends of more mobile devices being used for both personal and work purposes, requiring companies to adapt policies to embrace this trend while mitigating risks.