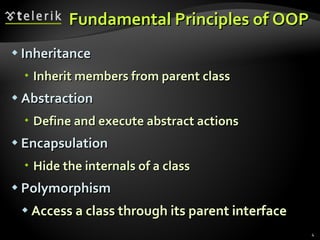
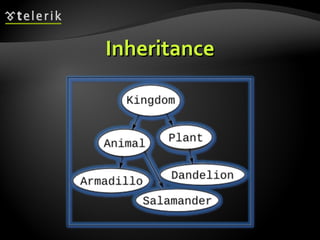
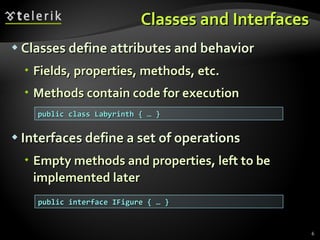
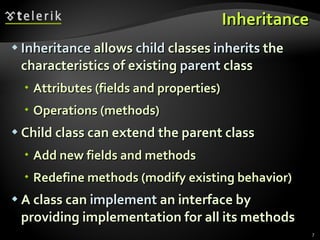
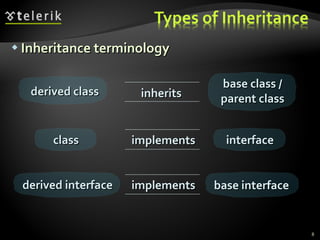
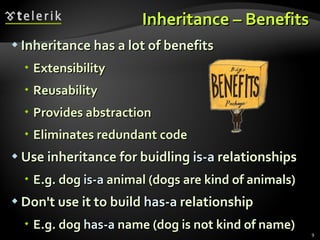
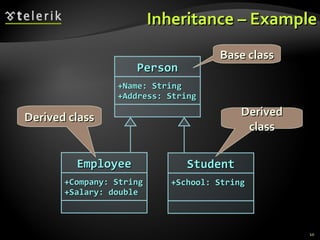
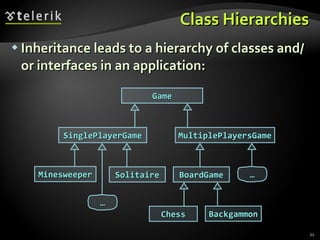
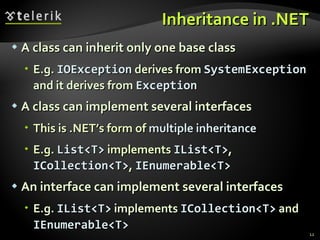
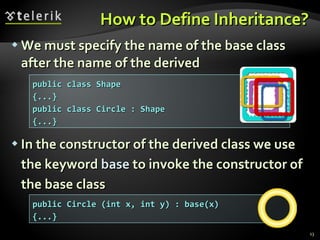
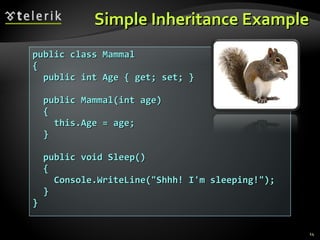
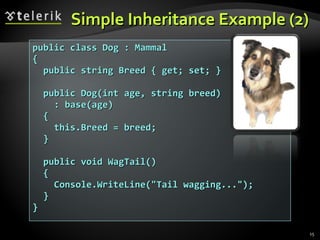
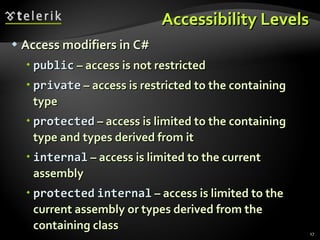
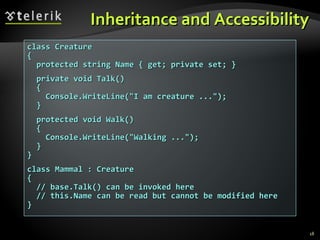
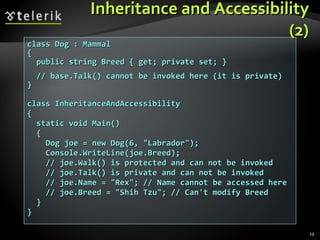
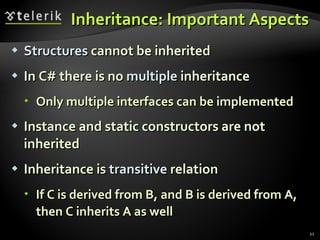
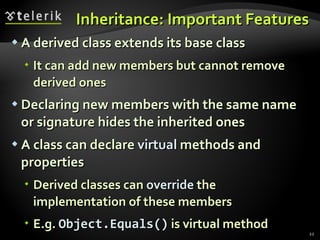
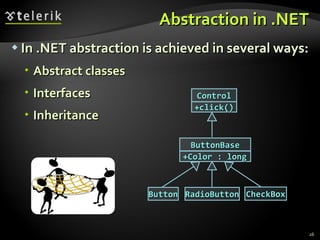
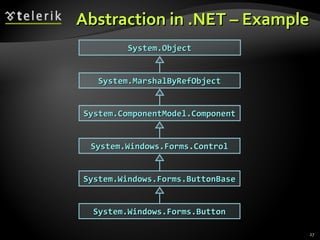
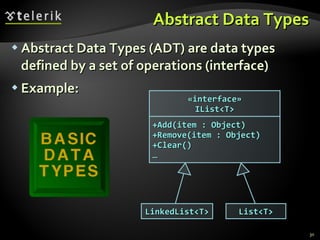
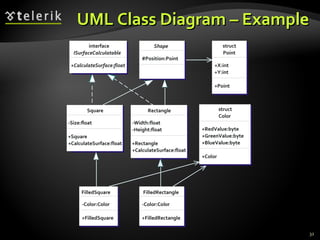
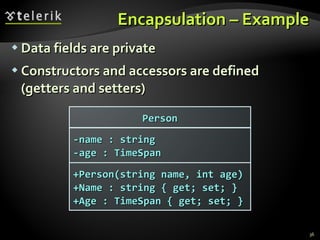
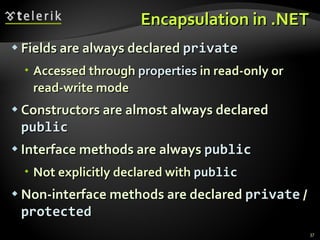
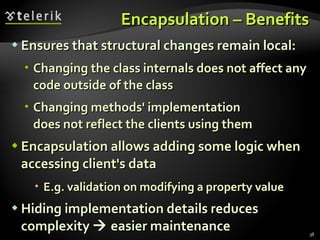
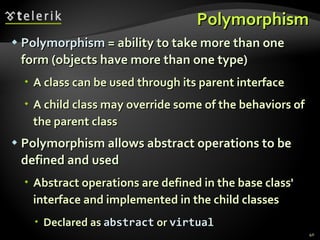
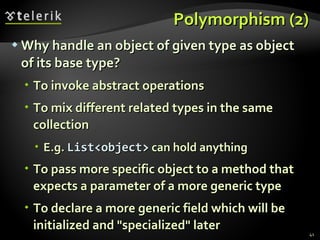
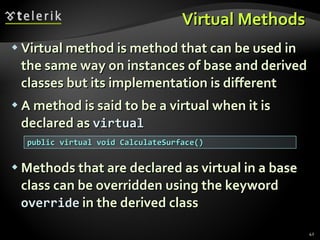
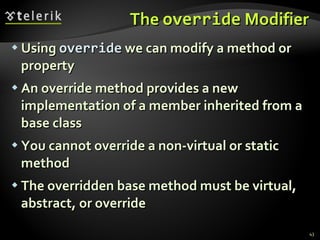
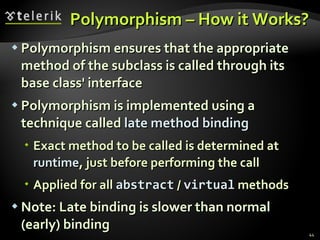
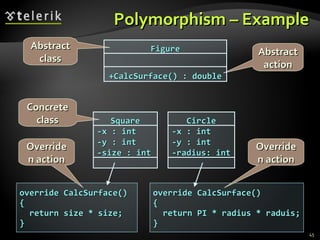
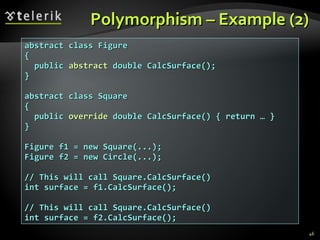
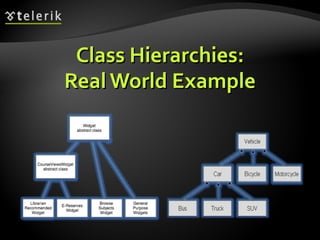
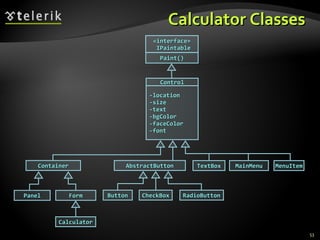
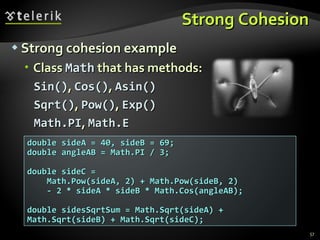
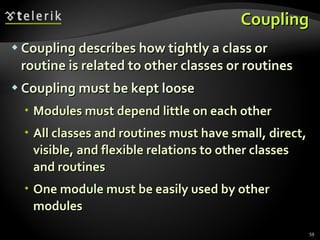
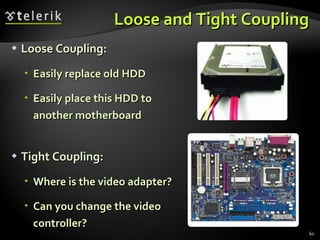
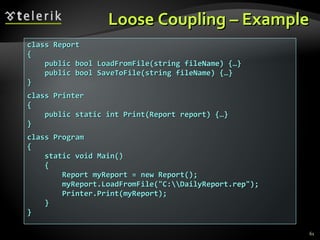
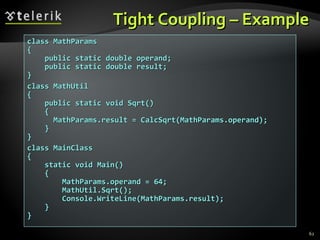
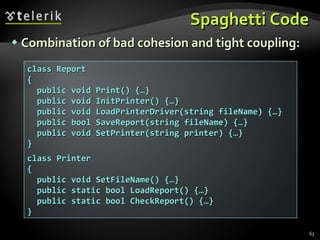
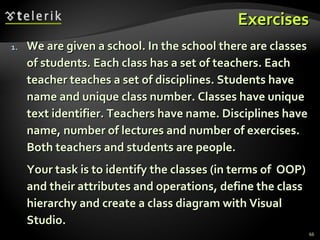
The document outlines the fundamental concepts of object-oriented programming (OOP), including inheritance, encapsulation, abstraction, and polymorphism. It discusses how inheritance allows classes to derive characteristics from parent classes, while encapsulation keeps data hidden and accessible through interfaces. The document emphasizes the importance of strong cohesion and loose coupling to avoid complexities and promote maintainable code.