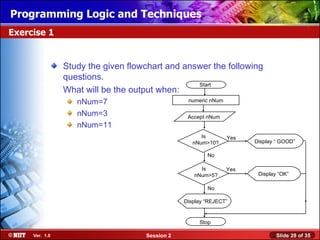
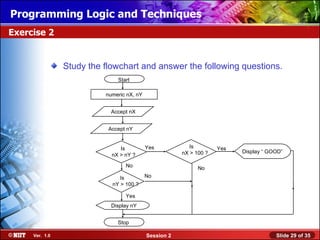
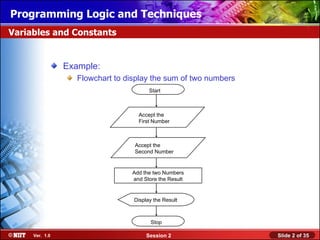
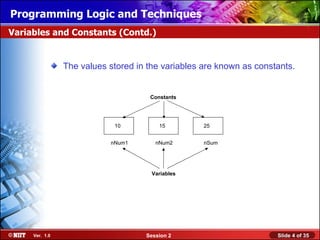
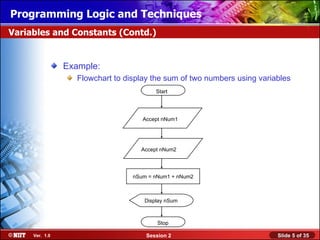
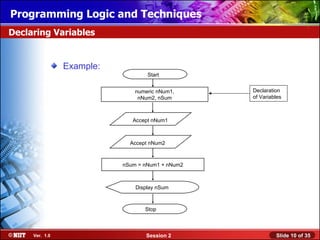
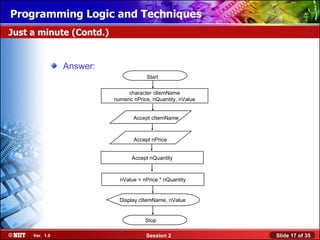
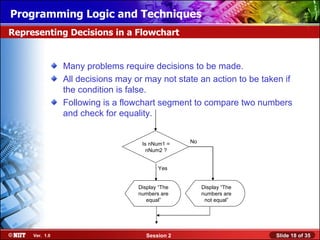
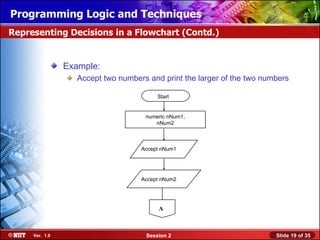
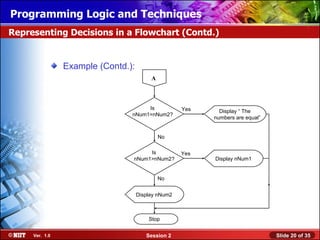
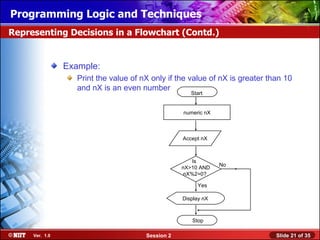
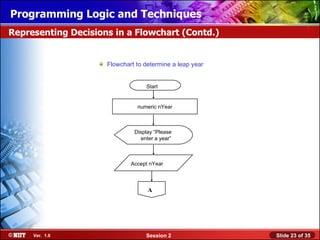
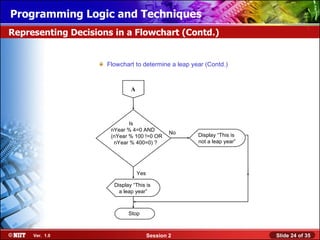
The document discusses variables, constants, data types, operators, and representing decisions in flowcharts. It provides examples of flowcharts that accept input values, perform calculations using variables and operators, and make decisions based on conditional logic. The key concepts covered include declaring variables, numeric and character data types, arithmetic, relational and logical operators, and using decision boxes in flowcharts to represent conditional statements. Exercises are included to apply these concepts in drawing flowcharts to solve problems involving decisions and calculations.
![Installing WindowsLogic and Techniques
Programming XP Professional Using Attended Installation
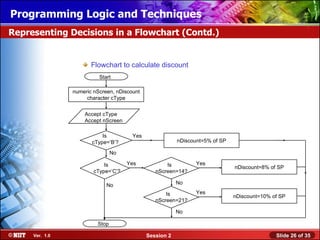
Representing Decisions in a Flowchart (Contd.)
Example:
To decide about the discount percentage on a TV, the sales
person needs to check the type of TV. If the TV is Black and
White [B], the discount will be 5 percent of the selling price. If
the type of TV is colored[C], then he has to verify the size of
TV screen. For 14 inches screen, discount is 8 percent of the
selling price and for 21 inches screen, the discount is 10
percent of the selling price.
Ver. 1.0 Session 2 Slide 25 of 35](https://image.slidesharecdn.com/02iect1s1pltsession02-120416031853-phpapp02/85/02-iec-t1_s1_plt_session_02-25-320.jpg)