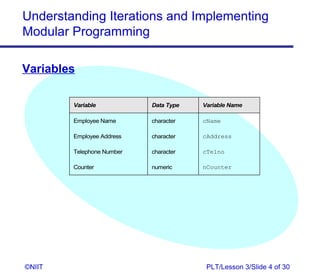
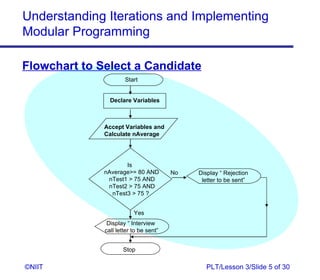
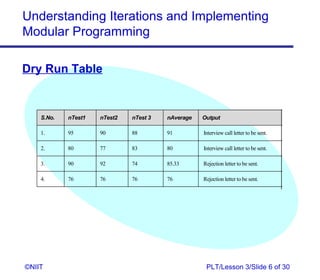
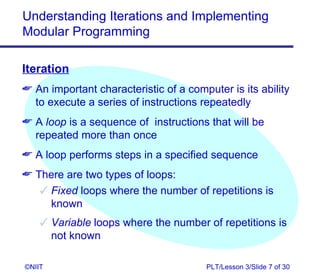
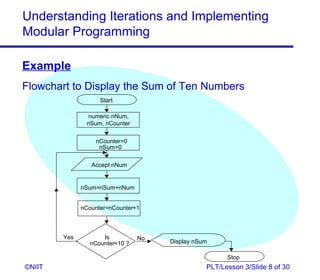
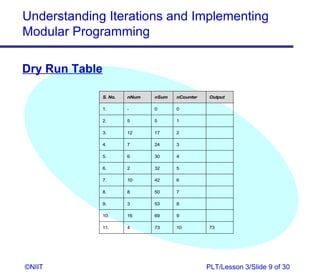
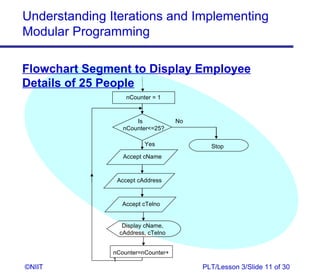
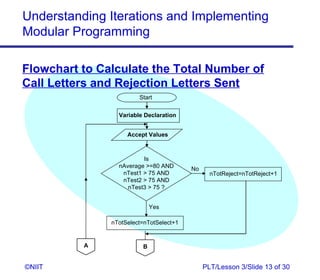
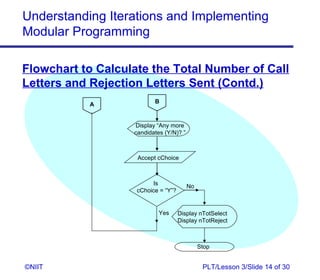
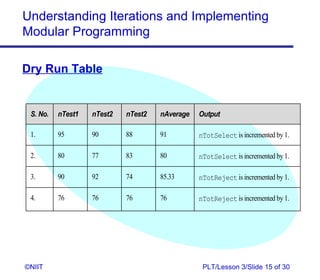
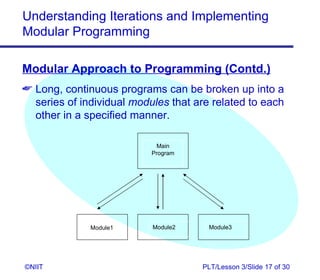
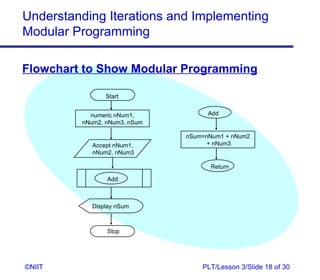
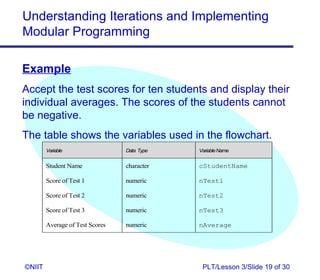
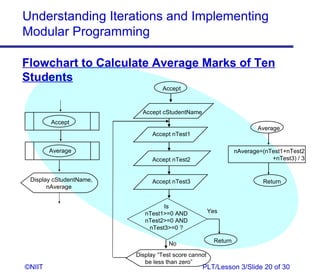
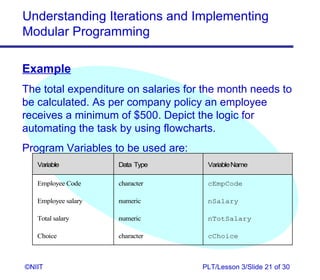
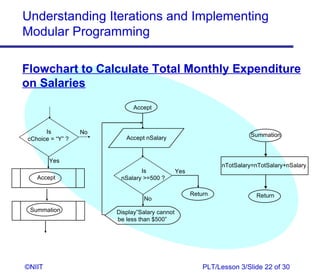
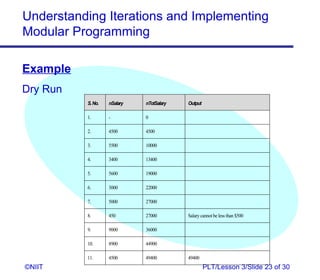
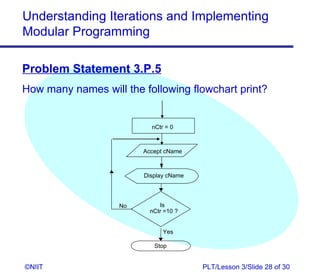
The document discusses iterations, modular programming, and flowcharts. It explains how to use dry run tables to evaluate a program's logic and output. It also describes how to represent repetitive processes and complex conditions using loops and modular structures in flowcharts. Breaking problems into smaller modules is an important part of the structured programming technique.