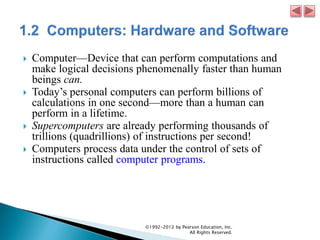
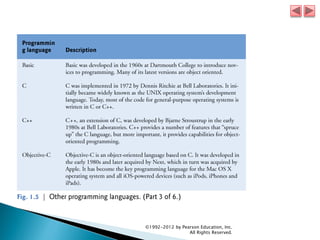
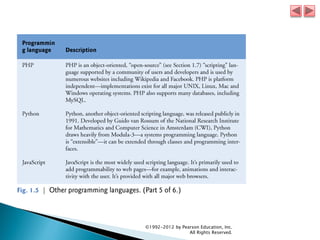
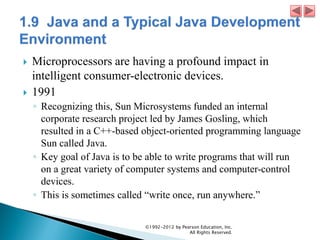
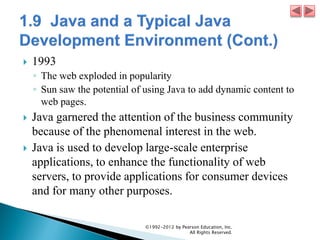
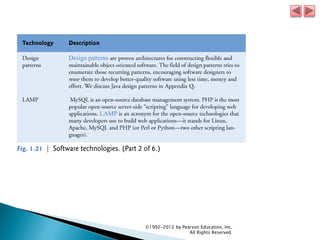
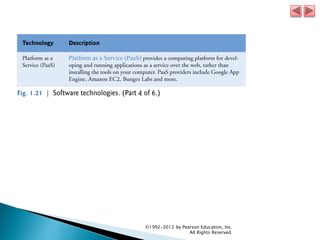
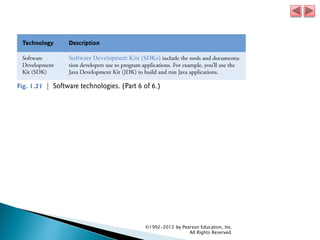
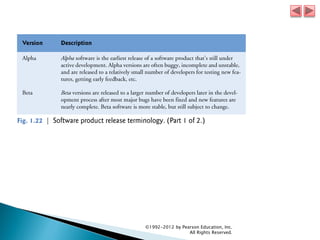
This document is an excerpt from the textbook "Java How to Program, 9/e" published by Pearson Education, Inc. in 1992. It introduces some key concepts of object-oriented programming using Java as an example, including classes, objects, methods, encapsulation, inheritance and the unified modeling language (UML). The document also discusses how Java has become a popular language for enterprise applications and mobile devices due to its portability and growth of the smartphone market.