Raabit and bacteria
•Download as PPTX, PDF•
0 likes•1,076 views
and defense mechanism
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
Key Distribution Problem in advanced operating system

Key Distribution Problem in advanced operating system
Inter-Process Communication in distributed systems

Inter-Process Communication in distributed systems
Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...

Circuit Switching, Packet Switching, Virtual Circuit Networks and Datagram Ne...
Client Server Architecture in Software engineering

Client Server Architecture in Software engineering
Basic communication operations - One to all Broadcast

Basic communication operations - One to all Broadcast
Viewers also liked
Viewers also liked (17)
Similar to Raabit and bacteria
Similar to Raabit and bacteria (20)
MongoDB.local Sydney: The Changing Face of Data Privacy & Ethics, and How Mon...

MongoDB.local Sydney: The Changing Face of Data Privacy & Ethics, and How Mon...
Hacker Halted 2014 - Reverse Engineering the Android OS

Hacker Halted 2014 - Reverse Engineering the Android OS
SC-900 Concepts of Security, Compliance, and Identity

SC-900 Concepts of Security, Compliance, and Identity
Entrepreneurship & Commerce in IT - 11 - Security & Encryption

Entrepreneurship & Commerce in IT - 11 - Security & Encryption
More from sabin kafle
More from sabin kafle (19)
Recently uploaded
Recently uploaded (20)
A Critique of the Proposed National Education Policy Reform

A Critique of the Proposed National Education Policy Reform
Separation of Lanthanides/ Lanthanides and Actinides

Separation of Lanthanides/ Lanthanides and Actinides
Introduction to ArtificiaI Intelligence in Higher Education

Introduction to ArtificiaI Intelligence in Higher Education
Micromeritics - Fundamental and Derived Properties of Powders

Micromeritics - Fundamental and Derived Properties of Powders
Call Girls in Dwarka Mor Delhi Contact Us 9654467111

Call Girls in Dwarka Mor Delhi Contact Us 9654467111
Kisan Call Centre - To harness potential of ICT in Agriculture by answer farm...

Kisan Call Centre - To harness potential of ICT in Agriculture by answer farm...
TataKelola dan KamSiber Kecerdasan Buatan v022.pdf

TataKelola dan KamSiber Kecerdasan Buatan v022.pdf
Raabit and bacteria
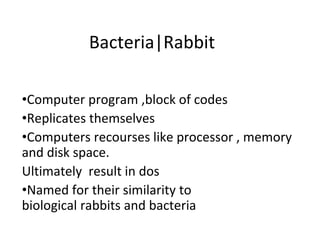
- 1. Bacteria|Rabbit •Computer program ,block of codes •Replicates themselves •Computers recourses like processor , memory and disk space. Ultimately result in dos •Named for their similarity to biological rabbits and bacteria
- 2. Defense method • Sandboxing • Proof carrying code • Information flow matrices • Reducing right • Malicious logic alternating files • Notion of trust
- 3. Sandboxing • Creation of virtual environment • Sandboxes, virtual machines also restrict rights – Modify program by inserting instructions to cause traps when violation of policy – feel safe & secure about what the executing software can do.
- 4. Proof-Carrying Code • originally described in 1996 by George Necula and Peter Lee • software mechanism for validating that allows a host system to verify properties about an application • Security policy to determine whether the application i safe to execute • Code consumer (user) specifies safety requirement • Code producer (author) generates proof code meets this requirement – Proof integrated with executable code – Changing the code invalidates proof • code + proof delivered to consumer • Consumer validates proof
- 5. Information flow metrics • Propounded byHenry and Kafura • Idea: limit distance a virus can spread • transfer of information from a variable x to a variable y in a given process • Ensure confidentiality • Metric associated with information, not objects – You can tag files with metric, but how do you tag the information in them? – This prevent sharing • To stop spread, make V = 0 – Disallows sharing
- 6. Reducing Protection Domain • Application of principle of least privilege • Basic idea: remove rights from process so it can only perform its function – Warning: if that function requires it to write, it can write anything – But you can make sure it writes only to those objects you expect
- 7. Detect Alteration of Files • developed by Silicon Graphics • allows applications to watch certain files and be notified when they are modified • Compute manipulation detection code (MDC) to generate signature block for each file, and save it • Later, recompute MDC and compare to stored MDC – If different, file has changed
- 8. Notion of trust • Trust the user to take explicit actions to limit their process’ protection domain sufficiently • based on the authenticated identity of external parties • Rigid authentication mechanisms, such as public key cryptographic and Kerberos to protect users information. • Types : Direct trust & Third Party Trust
- 9. Thank you!
