2020 network topologies and access methods
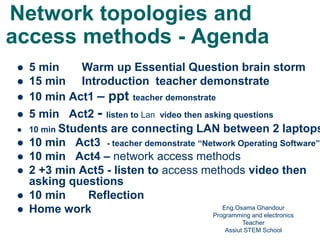
- 1. Network topologies and access methods - Agenda 5 min Warm up Essential Question brain storm 15 min Introduction teacher demonstrate 10 min Act1 – ppt teacher demonstrate 5 min Act2 - listen to Lan video then asking questions 10 min Students are connecting LAN between 2 laptops 10 min Act3 - teacher demonstrate “Network Operating Software” 10 min Act4 – network access methods 2 +3 min Act5 - listen to access methods video then asking questions 10 min Reflection Home work Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School1
- 2. Essential Questions: you were asked to create network between your school labs ,identify how will you plan to do this task? Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School2
- 3. How could to know about network topologies and access methods? Example Movie makerAsk or call a college Ask a teacher Ask or call an expert or an engineer Search through search engine such as google or Bing for ppt or pdf files using your laptop or smart phone through internet connection Use the help / F1 Search through YouTube Search through wiki Beddia Activity 2 Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School3
- 4. CS.2.07 Brain storm 5 min Essential Questions: What are the kinds of networks ? 15-4 Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School
- 5. 5 biomimicry computer network Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School
- 6. Geographically LAN WAN MAN Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School6
- 7. Introduction teacher demonstrate Topology 15 min The physical topology of a network refers to the configuration of cables, computers and other peripherals. The main types of network topologies are: – Linear Bus – Star – Ring – Tree or Hybrid Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School7
- 8. Linear Bus topology A linear bus topology consists of a main run of cable with a terminator at each end. All servers workstations and peripherals are connected to the linear cable , a bus technology called Ethernet has become the industry standard for local-area networks. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School8
- 9. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School9
- 10. Advantages & Disadvantages of Bus Topology Advantages Works well for small networks Relatively inexpensive to implement Easy to add to it Disadvantages Management costs can be high Potential for congestion with network trafficEng.Osama Ghandour Programming and electronics Teacher Assiut STEM School10
- 11. Star topology A star network is designed with each node (file server, workstation, peripheral) connected directly to a central network hub or server Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School11
- 12. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School12
- 13. Advantages & Disadvantages of Star Topology Advantages Good option for modern networks Low startup costs Easy to manage Offers opportunities for expansion Most popular topology in use; wide variety of equipment available Disadvantages Hub is a single point of failure Requires more cable than the bus Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School13
- 14. Ring topology A ring network is one where all workstations and other devices are connected in a continuous loop. There is no central server Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School14
- 15. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School15
- 16. Advantages of Ring Topology Easier to manage; easier to locate a defective node or cable problem Well-suited for transmitting signals over long distances on a LAN Handles high-volume network traffic Enables reliable communication Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School16
- 17. Disadvantages of Ring Topology Expensive Requires more cable and network equipment at the start Not used as widely as bus topology – Fewer equipment options – Fewer options for expansion to high- speed communication Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School17
- 18. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School18
- 19. Tree or hybrid topology A tree or hybrid topology combines characteristics of linear bus and star and/or ring topologies. It consists of groups of star-configured workstations connected to a linear bus backbone cable Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School19
- 20. Star-Wired Bus Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School20
- 21. Star-bus-Topology - Star- ring Topology Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School21 (CSMA/CD)
- 22. Explain the principles of networking, describe types of networks, explain basic networking concepts and technologies, describe the physical components of a network. describe network topologies, Identify Ethernet standards Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School22
- 23. 15 min Act1 – TPS -Searching about Network topologies -Students print A3 and A4 papers about Network topologies then stick it at the class room walls Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School23
- 24. Daisy chain: linked series of devices – Hubs and switches often connected in daisy chain to extend a network Hubs, gateways, routers, switches, and bridges can form part of backbone Extent to which hubs can be connected is limited Backbone Networks: Serial Backbone Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School24
- 25. 10 min Act3 - teacher demonstrate “Network Operating Software” Network operating systems co- ordinate the activities of multiple computers across a network The two major types of network OS are: – Peer-to-peer – Client/server Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School25
- 26. Peer to peer network OS – In peer to peer network OS, there is no file server or central management source; all computers are considered equal – Peer to peer networks are design primarily for small to medium LANS – AppleShare and Windows for Workgroups are examples of programs that can function as peer to peer Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School26
- 27. Client/Server network OS – Client/server network OS centralise functions and applications in one or more dedicated file servers. – The file server provides access to resources and provides security – Novel Netware and Windows NT Server are examples of client/server network operating systems Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School27
- 28. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School28 Now students Concentrate to PPT demonstration about network models stopping it then asking questions 10 m press here
- 29. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School29 Activity using laptops Concentrate to PPT about LAN between 2 laptops using UTP cable then asking questions 10 m press here
- 30. Network Flow of data / Computer network access methods The Function of Access Methods The set of rules that defines how a computer puts data onto the network cable and takes data from the cable is called an access method. Once data is moving on the network, access methods help to regulate the flow of 10 min Act4 – network access methods Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School30
- 31. Traffic Control on the Cable A network is in some ways like a railroad track, along which several trains run. The track is interspersed with occasional railway stations. When a train is on the track, all other trains must abide by a procedure that governs how and when they enter the flow of traffic. Without such a procedure, entering trains would collide with the one already on the track. Train pictures Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School31
- 32. What are important differences between a railroad system and a computer network?. Train pictures Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School32
- 33. Network Flow of data / computer network access methods – Carrier-sense multiple-access with collision detection (CSMA/CD) – Carrier-sense multiple-access with collision avoidance (CSMA/CA) – Token passing Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School33
- 34. 2 min Act5 - listen to access methods video then asking questions press here Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School34
- 35. Carrier-sense multiple-access with collision detection (CSMA/CD) Collision occurs if two computers put data on the cable at the same time35 Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School
- 36. Access methods prevent computers from gaining simultaneous access to the cable. By making sure that only one computer at a time can put data on the network cable, access methods ensure that the sending and receiving of network data is an orderly process. Computers can transmit data only if the cable is freeEng.Osama Ghandour Programming and electronics Teacher Assiut STEM School36
- 37. لى انت دا بى حس حاجة كل Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School37
- 38. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School38
- 39. With these points in mind, the name of the access method—carrier-sense multiple access with collision detection (CSMA/CD)—makes sense. Computers listen to or "sense" the cable (carrier- sense). Commonly, many computers on the network attempt to transmit data (multiple access); each one first listens to detect any possible collisions. If a computer detects a possible collision, it waits for a random period of time before retransmitting (collision detection).39
- 40. CSMA/CD is known as a contention method because computers on the network contend, or compete, for an opportunity to send data CSMA/CD Considerations The more computers there are on the network, the more network traffic there will be. With more traffic, collision avoidance and collisions tend to increase, which slows the network down, so CSMA/CD can be a slow-access method. Ex. journal exams Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School40
- 41. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School41
- 42. After each collision, both computers will have to try to retransmit their data. If the network is very busy, there is a chance that the attempts by both computers will result in collisions with packets from other computers on the network. If this happens, four computers (the two original computers and the two computers whose transmitted packets collided with the original computer's retransmitted packets) will have to attempt to retransmit. These proliferating retransmissions can slow the network to a near standstill. The occurrence of this problem depends on the number of users attempting to use the network and which applications they are using. Database applications tend to put more traffic on the network than word-processing applications do. Ex journal exams42
- 43. Depending on the hardware components, the cabling, and the networking software, using a CSMA/CD network with many users running several database applications can be very frustrating because of heavy network traffic. Ex journal exams Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School43
- 44. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School44
- 45. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School45
- 46. 2 min Act5 - listen to Token ring access method video then asking questions press hereEng.Osama Ghandour Programming and electronics Teacher Assiut STEM School46
- 47. Token-Passing Access Method In the access method known as token passing, a special type of packet, called a token, circulates around a cable ring from computer to computer. When any computer on the ring needs to send data across the network, it must wait for a free token. When a free token is detected, the computer will take control of it if the computer has data to send. The computer can now transmit data. Data is transmitted in frames, and additional information, such as addressing, is attached to the frame in the form of headers and trailers Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School47
- 48. While the token is in use by one computer, other computers cannot transmit data. Because only one computer at a time can use the token, no contention and no collision take place, and no time is spent waiting for computers to resend tokens due to network traffic on the cable. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School48
- 49. Demand Priority Access Method Demand priority is a relatively new access method designed for the 100-Mbps Ethernet standard known as 100VG-AnyLAN. It has been sanctioned and standardized by the Institute of Electrical and Electronic Engineers (IEEE) in its 802.12 specification, which is discussed later in this chapter. This access method is based on the fact that repeaters and end nodes are the two components that make up all 100VG-AnyLAN networks. Figure 3.4 shows a demand-priority network. The repeaters manage network access by doing round-robin searches for requests to send from all nodes on the network. The repeater, or hub, is responsible for noting all addresses, links, and end nodes and verifying that they are all functioning. According to the 100VG-AnyLAN definition, an end node can be a computer, bridge, router, or switch.49
- 50. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School50
- 51. Demand-Priority Contention As in CSMA/CD, two computers using the demand- priority access method can cause contention by transmitting at exactly the same time. However, with demand priority, it is possible to implement a scheme in which certain types of data will be given priority if there is contention. If the hub or repeater receives two requests at the same time, the highest priority request is serviced first. If the two requests are of the same priority, both requests are serviced by alternating between the two. In a demand-priority network, computers can receive and transmit at the same time because of the cabling scheme defined for this access method. In this method, four pairs of wires are used, which enables quartet signaling, transmitting 25 MHz signals on each of the pairs of wire in the cable. 51
- 52. Demand priority offers several advantages over CSMA/CD including: The use of four pairs of wires. By using four pairs of wires, computers can transmit and receive at the same time. Transmissions through the hub. Transmissions are not broadcast to all the other computers on the network. The computers do not contend on their own for access to the cable, but operate under the centralized control of the hub. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School52
- 53. Feature or function CSMA/CD CSMA/CA Token passing Demand priority Type of Communicatio n Broadcast- based Broadcast- based Token-based Hub-based Type of access method Contention Contention Noncontention Contention Type of network Ethernet LocalTalk Token Ring ArcNet 100VG- AnyLan Table 3.1 Features of Different Access Methods 53
- 54. Managing data on a network is a form of traffic control. The set of rules that governs how network traffic is controlled is called the access method. When using the CSMA/CD access method, a computer waits until the network is quiet and then transmits its data. If two computers transmit at the same time, the data will collide and have to be re-sent. If two data packets collide, both will be destroyed. When using the CSMA/CA access method, a computer transmits its intent to transmit before actually sending the data. When using the token-ring access method, each computer must wait to receive the token before it can transmit data. Only one computer at a time can use the token. When using the demand-priority access method, each computer communicates only with a hub. The hub then controls the flow of data. Access methods summary 54
- 55. Ethernet is a Network Operating Software Bus topology Network access method Backbone Networks ’element Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School55
- 56. INCORRECT!!! Try Again Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School56
- 57. CORRECT Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School57
- 58. CCNA Certified Computer Network Administrator this Certificate from Cisco company www.netacade.com Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School Exam costs 3000 L.E. in CISCO centers But through online exam is free of charge 58
- 59. Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School59 Closing and summery Network topologies HybridBus StarRing Network OS AppleShare and Windows Novel Netware and Windows NT Client/server Peer-to-peer Network access methods (CSMA/CD) - (CSMA/CA) Token passing - Demand priority
- 60. 5 min Reflection • Mansion one type of each of : • network topologies • network OS • network access methods ? Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School60
- 61. Home work provides a summary comparison between network types , its OS and its access data methods in a tabel . Computer-Networks- -Introduction_Computer_Networking pdf file Eng.Osama Ghandour Programming and electronics Teacher Assiut STEM School61
- 62. Journal Question In computer Science (CS.2.08), you learned about different network Topologies. What kind of these network Topologies would you suggest for a new factory working in the field of the industry you are working on for this semester Capstone? Explain why you suggested this kind? 62
