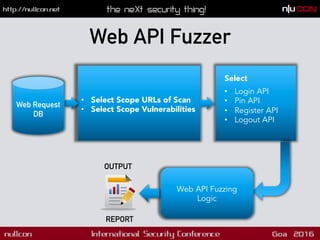
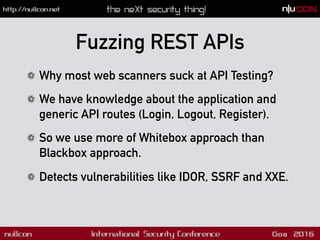
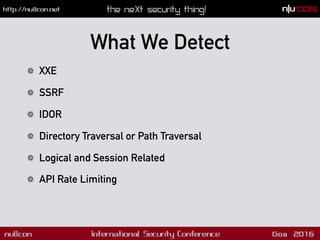
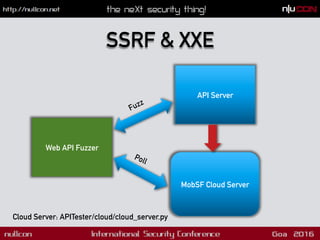
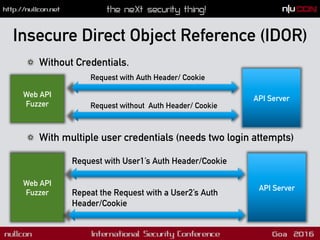
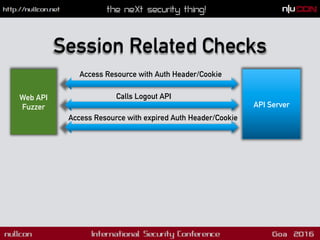
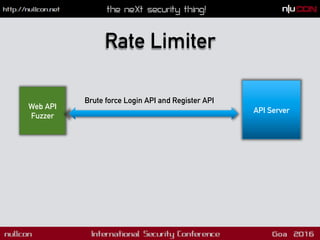
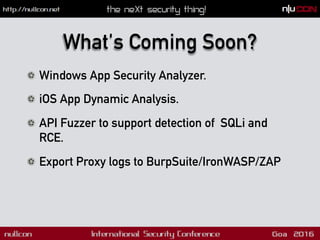
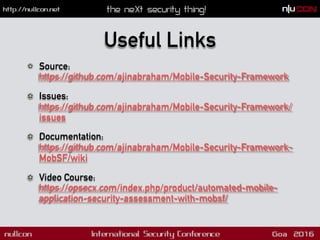
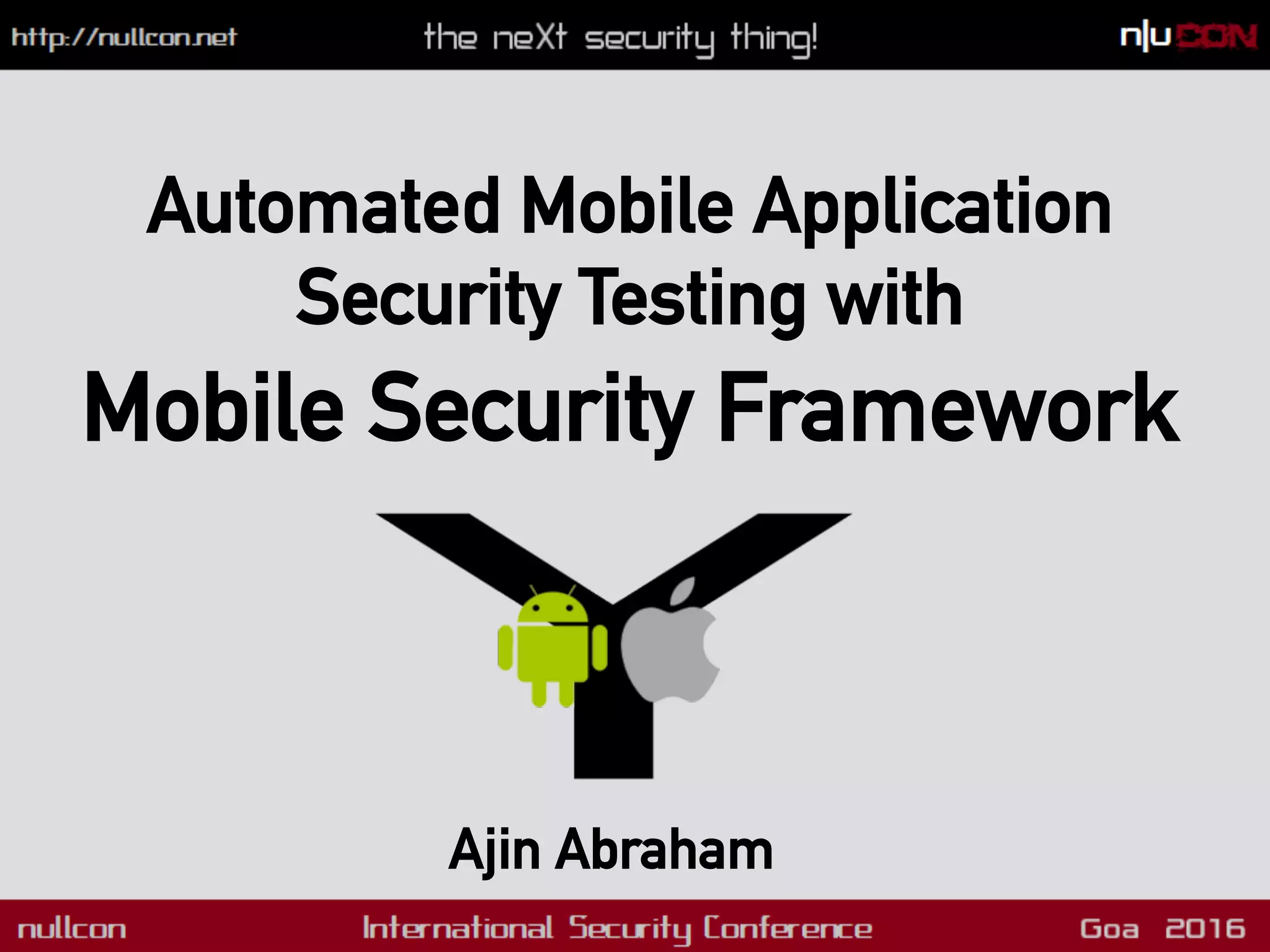
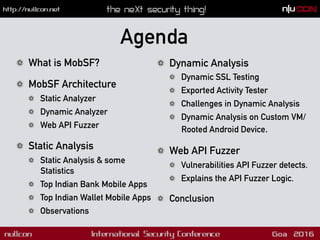
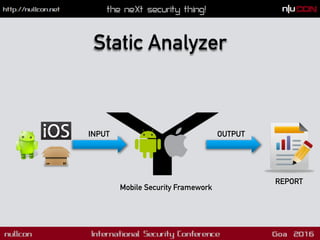
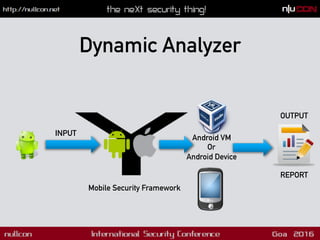
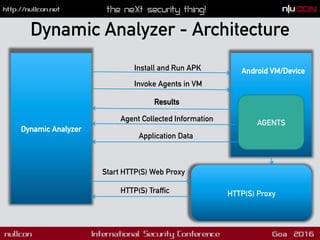
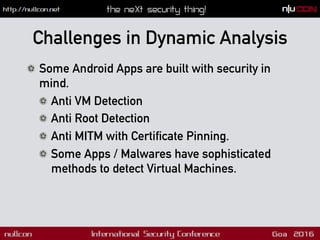
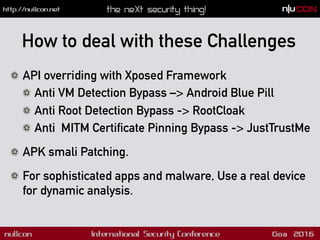
The document discusses the Mobile Security Framework (MobSF), an open-source tool for automated security testing of mobile applications. It covers features such as static and dynamic analysis, web API fuzzing, and identifies common vulnerabilities like SSL bypass and insecure direct object references. The presentation highlights challenges in mobile app security testing and introduces upcoming features like a Windows app security analyzer and enhanced API vulnerability detection.











![Dynamic Analysis on Device
! MobSFy Script – Convert your VM/ Device to support MobSF
Dynamic Analysis
! Documentation here:
https://github.com/ajinabraham/Mobile-Security-Framework-
MobSF/wiki/2.-Configure-MobSF-Dynamic-Analysis-
Environment-in-your-Android-Device-or-VM
! DEMO : Weak Crypto
! Java - String hashCode() Method
! s[0]*31^(n-1) + s[1]*31^(n-2) + ... + s[n-1]](https://image.slidesharecdn.com/nullcon-160312201930/85/Nullcon-Goa-2016-Automated-Mobile-Application-Security-Testing-with-Mobile-Security-Framework-MobSF-24-320.jpg)