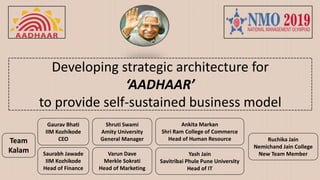
Developing strategic architecture for ‘AADHAAR’ to provide self-sustained business model
- 1. Gaurav Bhati IIM Kozhikode CEO Ankita Markan Shri Ram College of Commerce Head of Human Resource Yash Jain Savitribai Phule Pune University Head of IT Saurabh Jawade IIM Kozhikode Head of Finance Varun Dave Merkle Sokrati Head of Marketing Shruti Swami Amity University General Manager Developing strategic architecture for ‘AADHAAR’ to provide self-sustained business model Team Kalam Ruchika Jain Nemichand Jain College New Team Member
- 2. Aadhaar Considered a proof of residence and not a proof of citizenship, Aadhaar does not itself grant any rights to domicile in India. Tool for streamlining government expenditure & better targeting through JAM (Jan Dhan, Aadhaar, Mobile) initiative. Enabler for transparent and accountable system of public expenditure. SC on Sept’ 2018 issued landmark decision stating that Aadhaar’s benefits outweighs its associated risks but private entities cannot compel their customers to provide their Aadhaar number as a condition of service to verify their identity. Social inclusion project with a developmental focus & enabler for empowerment of poor A 12-digit unique identity number that can be obtained by residents of India, based on their biometric and demographic data. Concerns raised against Aadhaar: Privacy, Surveillance, Exclusion from welfare benefits.
- 3. Current Features • Only a random number – for life time, no smart card • All residents – for children, LGBTQ+ • Uniqueness: 1 person = 1 Aadhaar • Minimal data collected • Secured & Privacy of data ensured • Ubiquitous online authentication • Enrol & Update from anywhere • Vendor neutrality Data Collected through Aadhaar includes Iris, Fingers and Face Scan along with name, DOB, Gender, Address and Mobile/Email of Applicant
- 4. Problem Statement • To increase usability and easiness without compromising privacy of an individual. • Come-Up with your innovative plan to Increase reach of ADHAAR & completely cover India's Population especially in remote parts of country where technology access is nil. • Make ADHAAR’s financial model to be a self-sustaining & independent, so that it can help to fund its own development projects, technologies enhancements, R&D, etc. without being government dependent. • Restructure current ADHAAR HR Policy to avoid fraudulent activities done due to loopholes in recruitment process and presence of mischievous elements.
- 5. Our Major Recommendations (1/2) Change outsourcing model from current Project outsourcing to Professional outsourcing. Implementing complex relation algorithm using Blockchain technology to curb fraudulence while ensuring privacy. Workforce should be technically competent and there should be adequate data protection policy including non-disclosure agreements with employees as well as third –parties. Export Aadhaar technology to interested nations and consult them wherever the opportunity is present. Aadhaar enabled applications for payments like tax payments or e-governance services such as biometric attendance, healthcare, ration, etc.
- 6. Our Major Recommendations (2/2) Revenue through updates of existing and enrolment of new consumers. Timely design alterations to protect cardholders against identity breaches. Authentication and identity verification needs to be well demarcated and a careful use case analysis is required. A third party auditor under independent administrative control to protect against potential insider leaks. Several tools and technology like storing hash of biometric data, tamper proof coding and hardware system and secure multi-party computations to provide reasonable guarantees for security and privacy protection. Tech driven chatbot/AI at mobile or web module for ease in availing Aadhaar linked services like appointments, upgrades, etc.
- 7. Solution – Outsourcing model Since the organization has gained experience and achieved scale it should consider movement from project based outsourcing (where it is/was involved with multiple agencies for enrolment and registration) to professional outsourcing (where it will be working along with only one big organization) • Benefits from this Organizational Shift will be driven through • High Cost and Time Savings, • Expertise, • Quality, • No need for tracking each and every individual, therefore less transactional costs.
- 8. Solution – Complex Relation Algorithm • We propose to implement complex relation algorithm using block chain technology. • This will prove to be useful in curbing fraud while taking care of privacy concerns. • Such an analysis has proven effective in identifying organized fraud activities by modeling relationships between entities in claims and new business. • Large volumes of seemingly unrelated claims can be checked, and then patterns and problems identified. This technique might show a high-activity account with links from many accounts, or a low-activity account with strong links to a master account. Example of networking analysis showing a suspicious network
- 9. Solution – Human Resource Management Considering the nature of job we need to ensure that the workforce is not only competent but reliable and honest as well. • Ethics and Integrity should be given the maximum weightage but a non-disclosure and confidentiality agreement should be applicable for all the hired employees. • Employees should have sound knowledge of their job and they should be experts in technology. • Hire personal consultants and analysts to guide, manage and control the organizational resources. • Data Protection Policy with third-parties to avoid data leakages. • Employees should go through mandatory training and certifications to ensure adherence to quality aspects. Current Organization structure is based on functional hierarchy and is suitable to ensure control and systematic and standardized working.
- 10. Solution – Marketing • Persuade citizens to adopt Aadhaar (wherever it is voluntary) to avail services and subsidies. • Different coloured Aadhaar cards to serve different purposes and different levels of security (which can be upgraded on demand by applicants). • Consulting projects to different nations. • Export Aadhaar technology to other nations as several countries have shown interest in Aadhaar like system. • Aadhaar Payments App to provide banking services hassle free, like instant application and loan reimbursement. • Aadhaar enabled Biometric attendance to ensure increased productivity, system transparency and increased efficiency in government organizations. • Connect lending to MSME through Aadhaar. Till now the focus was only on citizens, but now the time is ripe to extend it to entities. • Online loans (e-signature linked to the accounts)
- 11. Solution – Finance • Revenue models include • Updating existing Aadhaar card details • Enrollment of left out 15 crore applicants or the newly eligible (newborns) residents. • Charging a nominal fee from CBDT (Tax authority) or other government organizations utilizing Aadhaar platform for Aadhaar enabled services like Tax payments or digital loan services. • Revenue through consulting or leveraging advertisement revenue opportunities on the Aadhaar website. • Cost includes, cost of chatbot services and departments annual budgetary expenses. FY 2019- 20 (E) FY 2020- 21 (E) FY 2021-22 (E) FY 2022- 23 (E) Revenue from Enrollment Rs. 376.50 Cr Rs 58.80 Cr Rs. 59.56 Cr Rs. 60.32 Cr Comm. from Tax Depart Rs 4 Cr Rs 4 Cr Rs 4 Cr Rs 4 Cr Cost Incurred by Hiring cyber Professional Rs 12 Cr Rs 12 Cr Rs 12 Cr Rs 12 Cr Net Additional Income Rs 368.50 Cr Rs 50.80 Cr Rs 51.56 Cr Rs 52.32 Cr Future Revenue Projections
- 12. Solution – Information Technology • Our IT solution must provide for potential identity breaches of Aadhaar card holders. A timely design alteration is needed to address the same. • Authentication and identity verification need to be well demarcated and a careful use case analysis is required to determine precisely what is required for each application. • Finally, we should also provide for potential insider leaks. A third party auditor under independent administrative control can prove to be a effective solution for the same. • Several tools and technology can provide reasonable guarantees for security and privacy protection. For e.g. Storing hash of biometric data, tamper proof coding and hardware system and secure multi-party computations.
- 13. Impact We foresee an impactful self-sustainable business organization known for its robust tools and technology which ensures • Data protection and privacy of card holders, • No surveillance of residents, • Welfare services to each and everyone at the bottom of the pyramid, • Touches individuals as well as micro business entities, and • Exporting technology and consulting services to other nations.
- 14. References • https://uidai.gov.in/ • https://main.trai.gov.in/sites/default/files/presentations_&_cv/Day- 3_25Aug2017/Session2_Digital%20world/Digital%20Identifiers_Ashok%20Kum ar.pdf • https://en.wikipedia.org/wiki/Aadhaar#2016%E2%80%93present • https://factordaily.com/aadhaar-india-stack-export/ • https://www.firstpost.com/tech/news-analysis/how-aadhaar-compares-to- other-biometric-national-identification-systems-around-the-world- 3700543.html • https://www.bloombergquint.com/law-and-policy/the-future-of-aadhaar • https://www.sas.com/content/dam/SAS/en_us/doc/whitepaper1/simplifying- fraud-analytics-105573.pdf
- 15. Thank You
