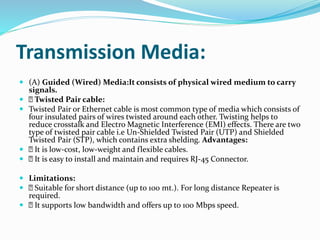
A computer network connects multiple devices together to share resources and exchange data. Common network types include personal area networks (PANs) covering small areas up to 10 meters, local area networks (LANs) spanning small offices or homes, and wide area networks (WANs) connecting larger geographic areas. Devices communicate over the network via wired or wireless transmission using various protocols like TCP/IP. Common networking devices that help establish and maintain connections include switches, routers, and wireless access points.