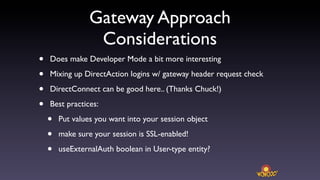
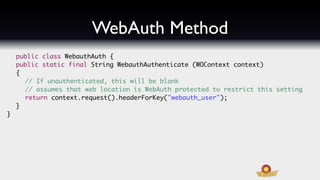
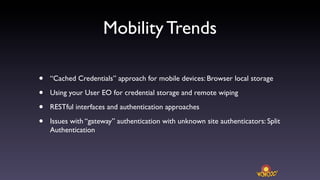
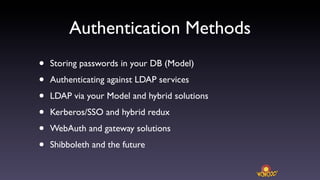
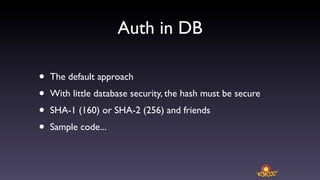
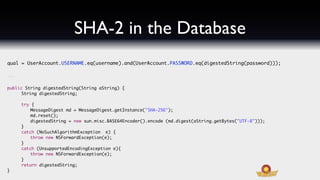
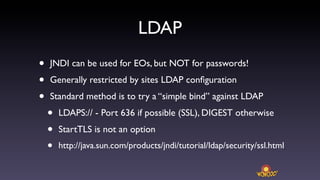
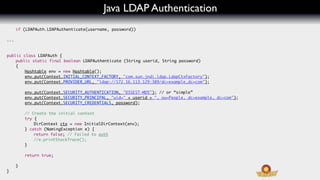
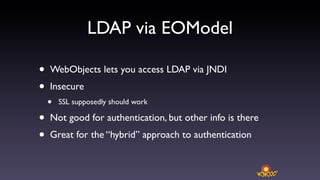
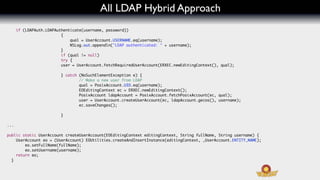
This document discusses various third party authentication methods that can be used with WebObjects applications, including storing hashed passwords in a database, authenticating against LDAP services, Kerberos/SSO, and gateway/web authentication solutions. It provides code examples for hashing passwords with SHA-256 before storing in a database, authenticating against an LDAP server using JNDI, and authenticating with Kerberos. It also discusses hybrid approaches that integrate database and LDAP user attributes, as well as considerations for using gateway/web authentication.

![Kerberos Methods
public class KerberosAuth {
static final String krbPath = "/Library/Preferences/edu.mit.Kerberos";
public static final boolean KerberosAuthenticate (String userid, char[] password)
{
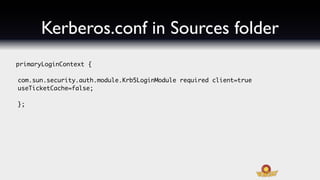
System.setProperty("java.security.krb5.conf", krbPath);
System.setProperty("java.security.auth.login.config", KerberosAuth.class.getResource("/kerberos.conf").toExternalForm());
try {
LoginContext lc = new LoginContext("primaryLoginContext", new UserNamePasswordCallbackHandler(userid, password));
lc.login();
}
catch (LoginException e) {
// e.printStackTrace();
return false; // Consider all failures as equal
}
return true;
}](https://image.slidesharecdn.com/wowodc-3rdpartyauth-110908070644-phpapp02/85/Third-Party-Auth-in-WebObjects-13-320.jpg)
![Kerberos Method Part 2
public static class UserNamePasswordCallbackHandler implements CallbackHandler {
private String _userName;
private char[] _password;
public UserNamePasswordCallbackHandler(String userName, char[] password) {
_userName = userName;
_password = password;
}
public void handle(Callback[] callbacks) throws IOException, UnsupportedCallbackException {
for (Callback callback : callbacks) {
if (callback instanceof NameCallback && _userName != null) {
((NameCallback) callback).setName(_userName);
}
else if (callback instanceof PasswordCallback && _password != null) {
((PasswordCallback) callback).setPassword(_password);
}
}
}
}](https://image.slidesharecdn.com/wowodc-3rdpartyauth-110908070644-phpapp02/85/Third-Party-Auth-in-WebObjects-14-320.jpg)