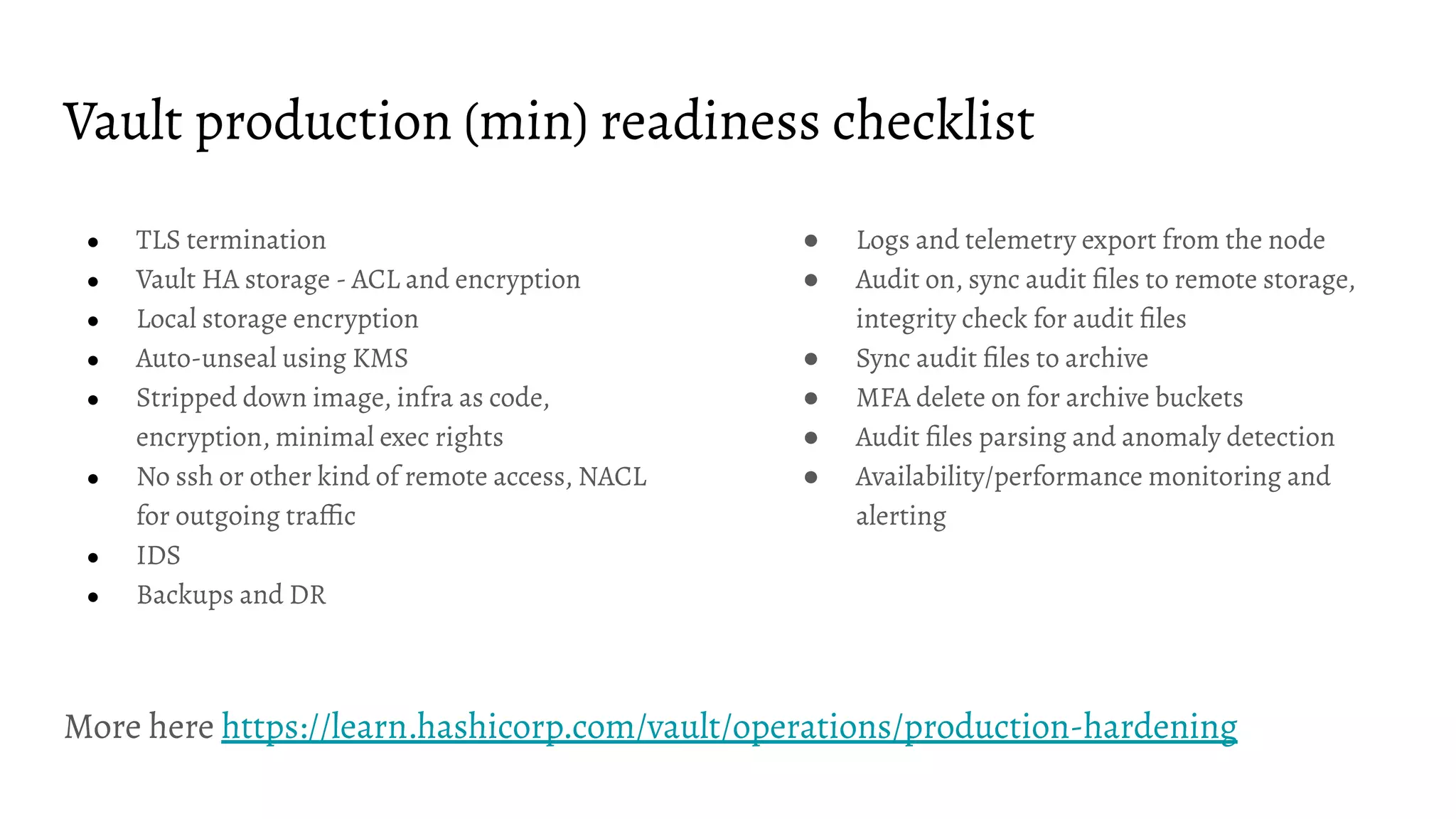
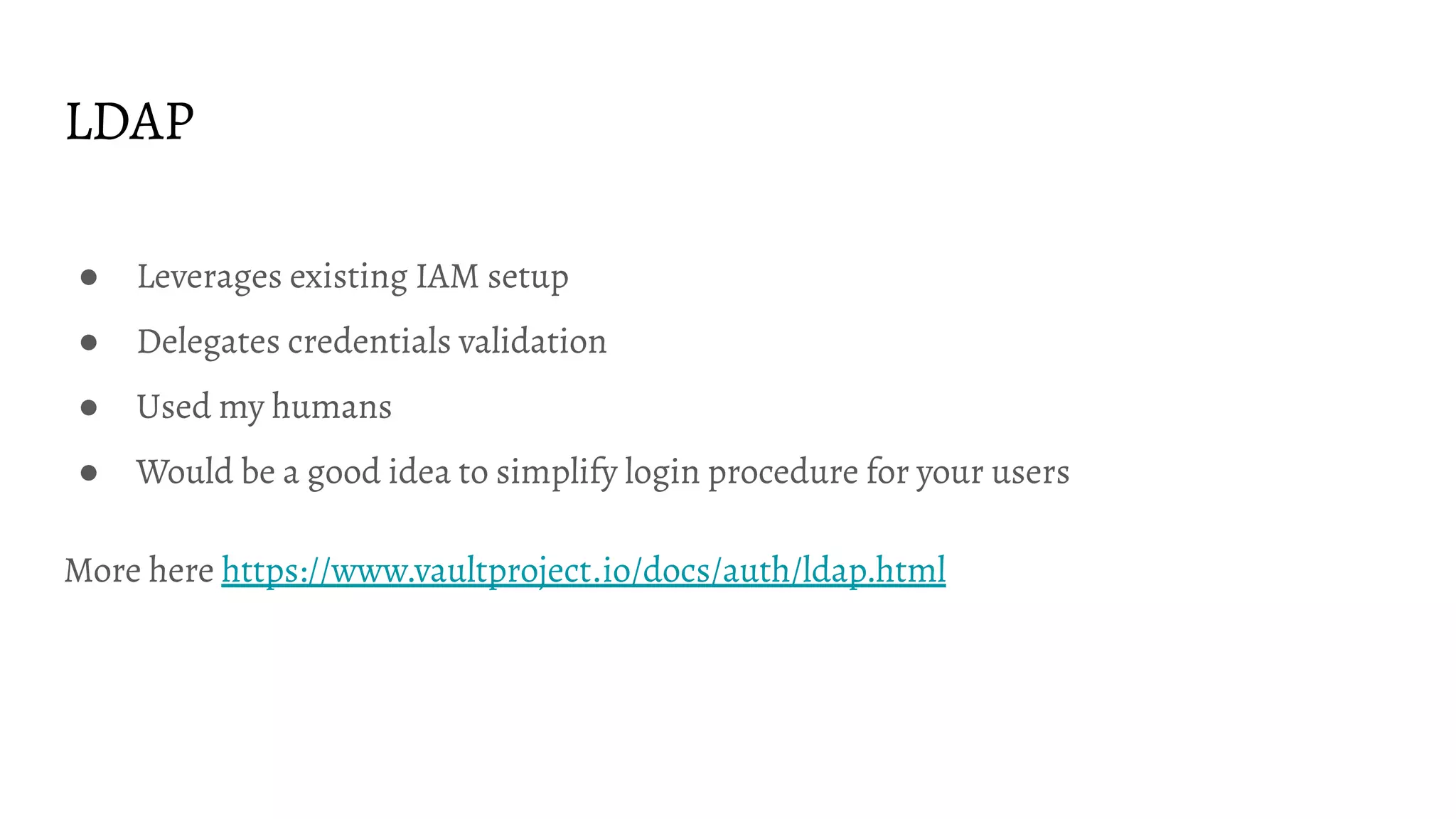
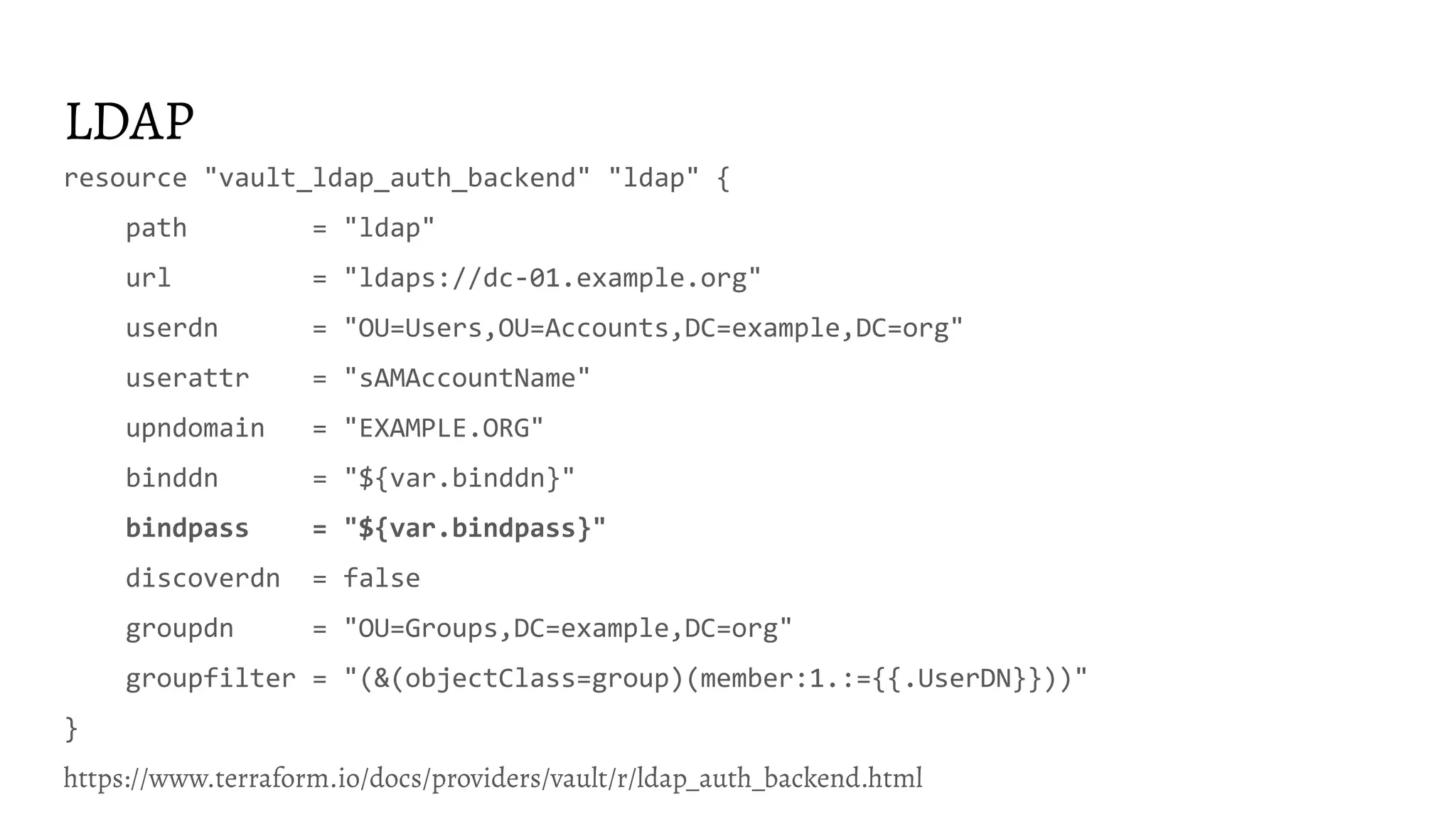
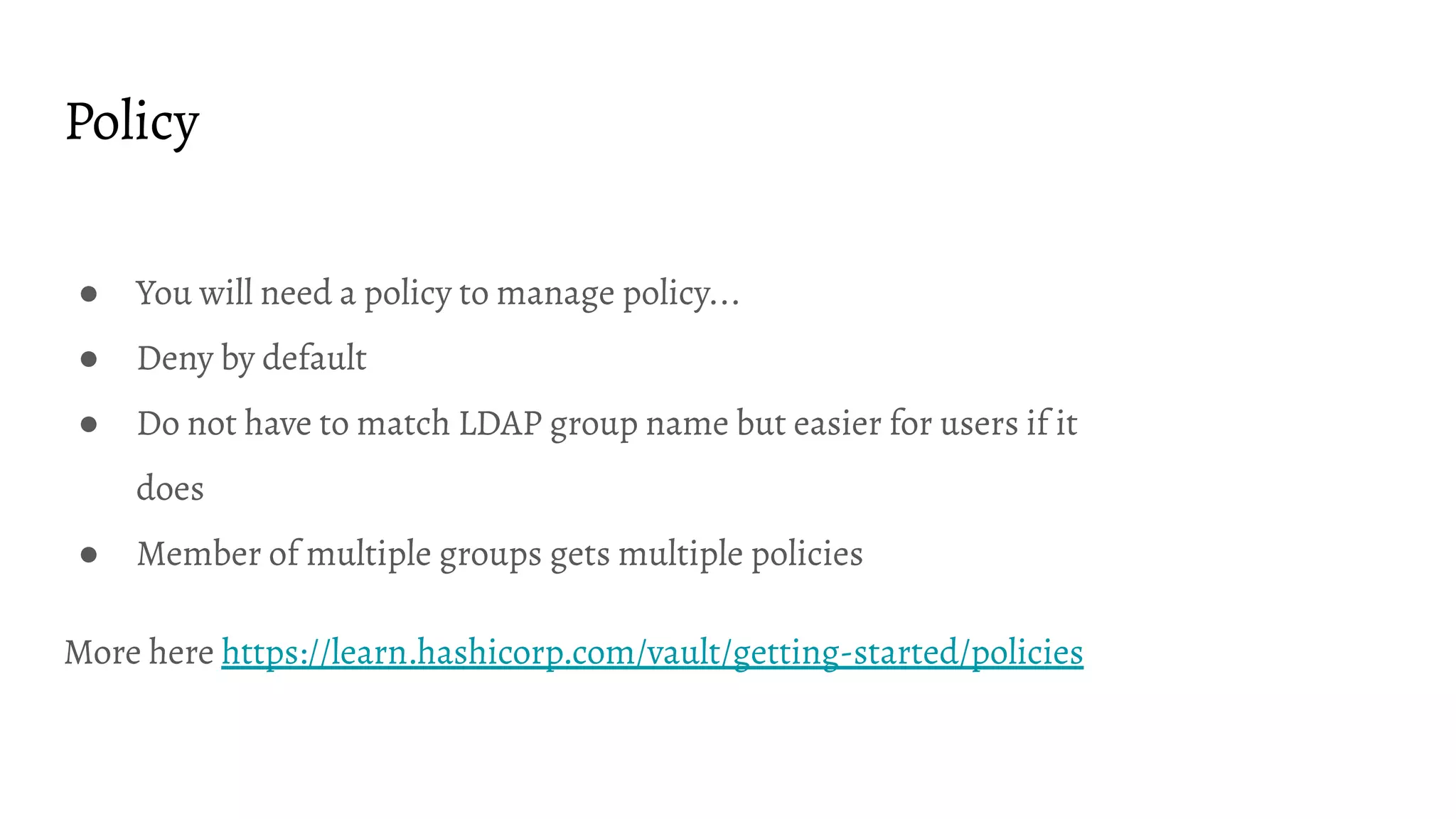
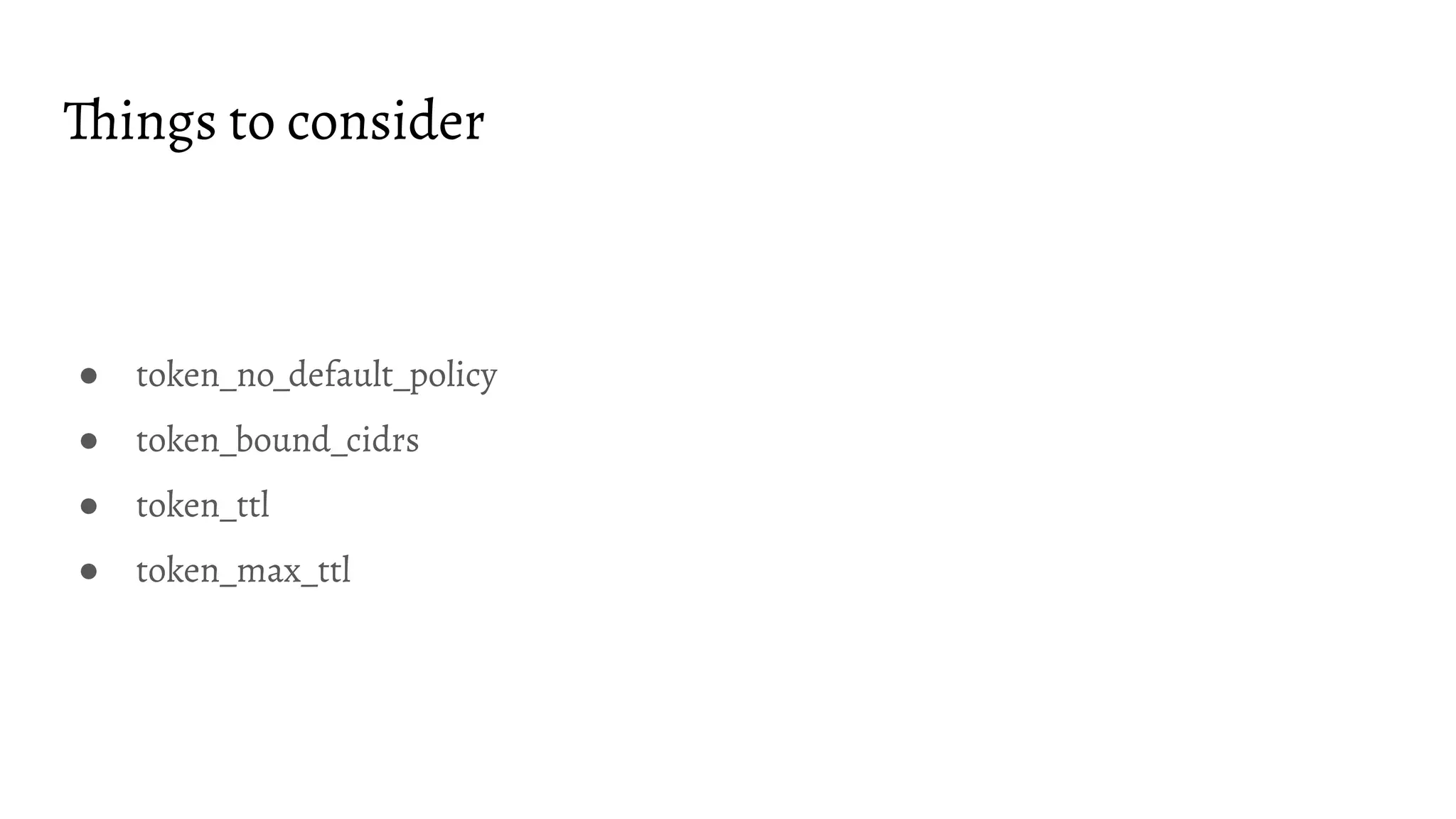
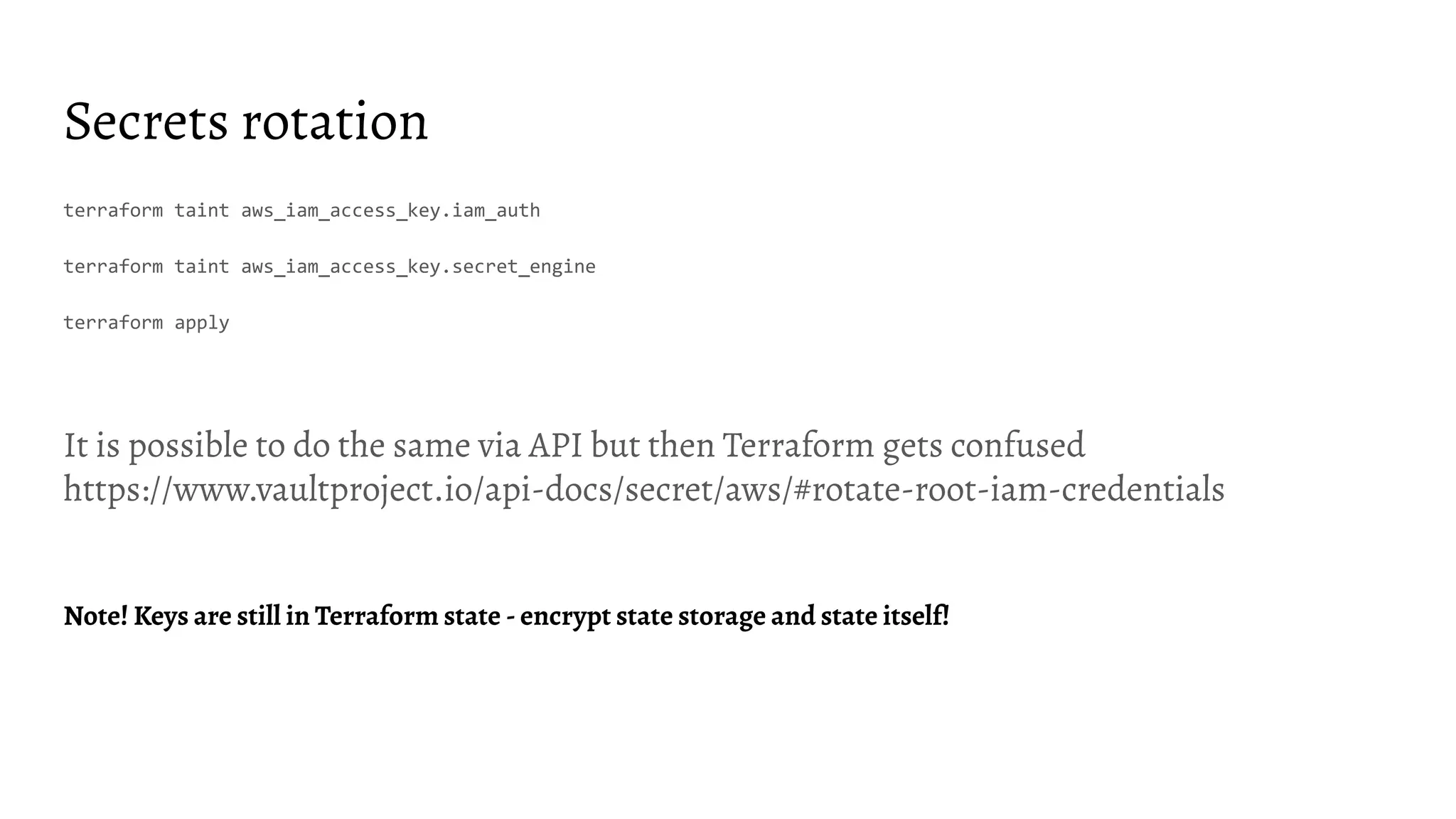
This document discusses using Terraform to configure Vault infrastructure as code. It begins with an overview of Vault and Terraform. It then covers important considerations for deploying Vault like authentication methods, policies, secret engines, and rotating secrets. The document shares examples of using Terraform resources to configure LDAP, AWS IAM, database credentials, and rotating secrets in Vault. It finds that some values added to Vault via Terraform are not always readable and recommends ways to continuously learn, share knowledge, and improve practices for infrastructure as code with Vault.
![LDAP role (backend group actually)
resource "vault_ldap_auth_backend_group" "group" {
groupname = "dba"
policies = ["dba"]
backend = "${vault_ldap_auth_backend.ldap.path}"
}
https://www.terraform.io/docs/providers/vault/r/ldap_auth_backend_group.html](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-25-2048.jpg)
![Policy
data "vault_policy_document" "example" {
rule {
path = "secret/*"
capabilities = ["create", "read", "update", "delete", "list"]
description = "allow all on secrets"
}
}
resource "vault_policy" "example" {
name = "example_policy"
policy = "${data.vault_policy_document.example.hcl}"
}
https://www.terraform.io/docs/providers/vault/d/policy_document.html](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-26-2048.jpg)
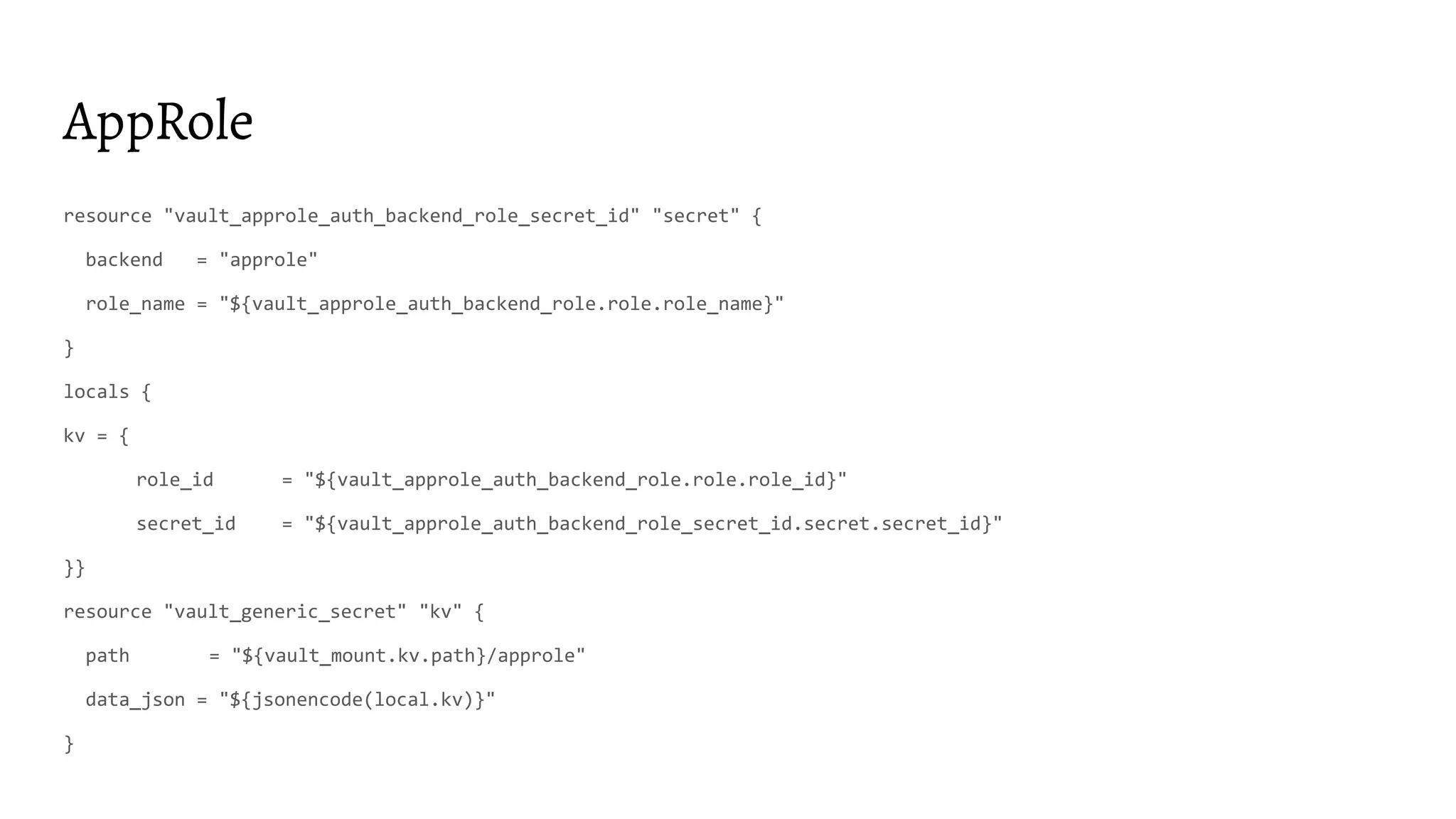
![AppRole
resource "vault_auth_backend" "approle" {
type = "approle"
}
resource "vault_approle_auth_backend_role" "example" {
backend = vault_auth_backend.approle.path
role_name = "test-role"
token_policies = ["default", "dev", "prod"]
}
https://www.terraform.io/docs/providers/vault/r/approle_auth_backend_role.html](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-30-2048.jpg)
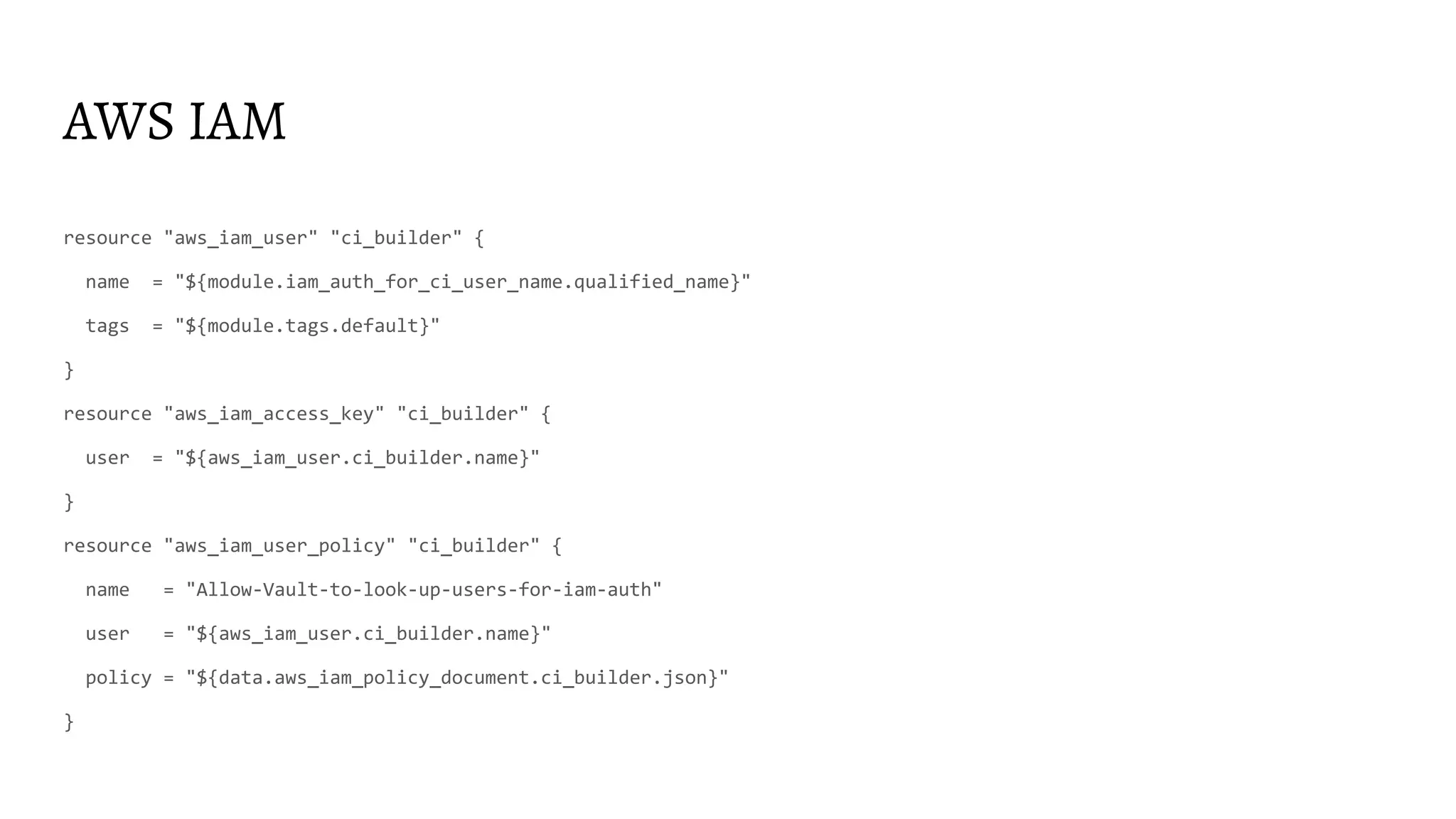
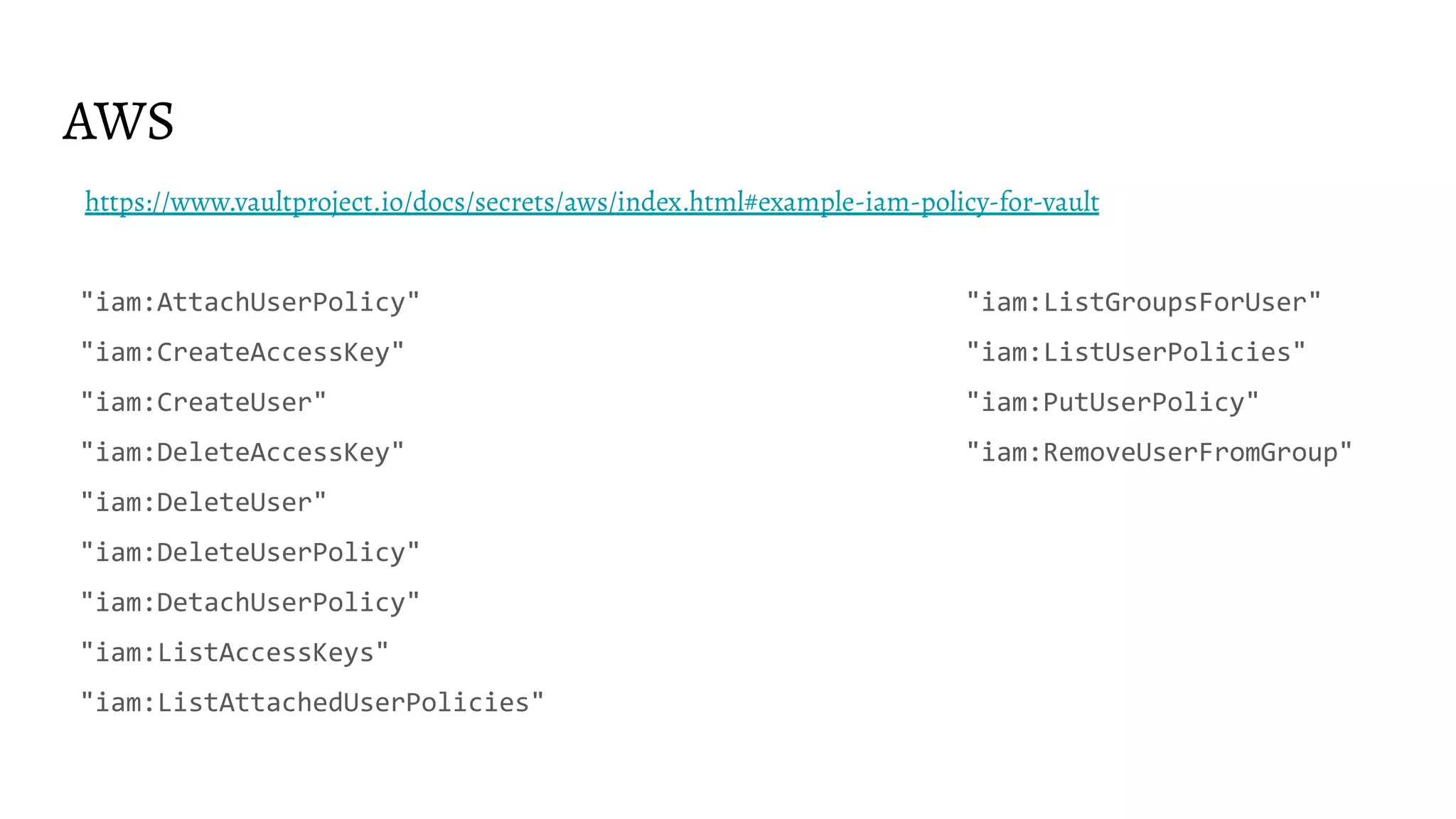
![AWS IAM
resource "vault_auth_backend" "aws" {
type = "aws"
}
resource "vault_aws_auth_backend_role" "this" {
backend = "${vault_auth_backend.aws.path}"
role = "ci-builder"
auth_type = "iam"
bound_iam_principal_arns = ["${data.aws_iam_role.ci_builder.arn}"]
token_ttl = 3600
token_max_ttl = 3600
token_policies = ["${vault_policy.ci_builder.name}"]
}
https://www.terraform.io/docs/providers/vault/r/aws_auth_backend_role.html](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-34-2048.jpg)
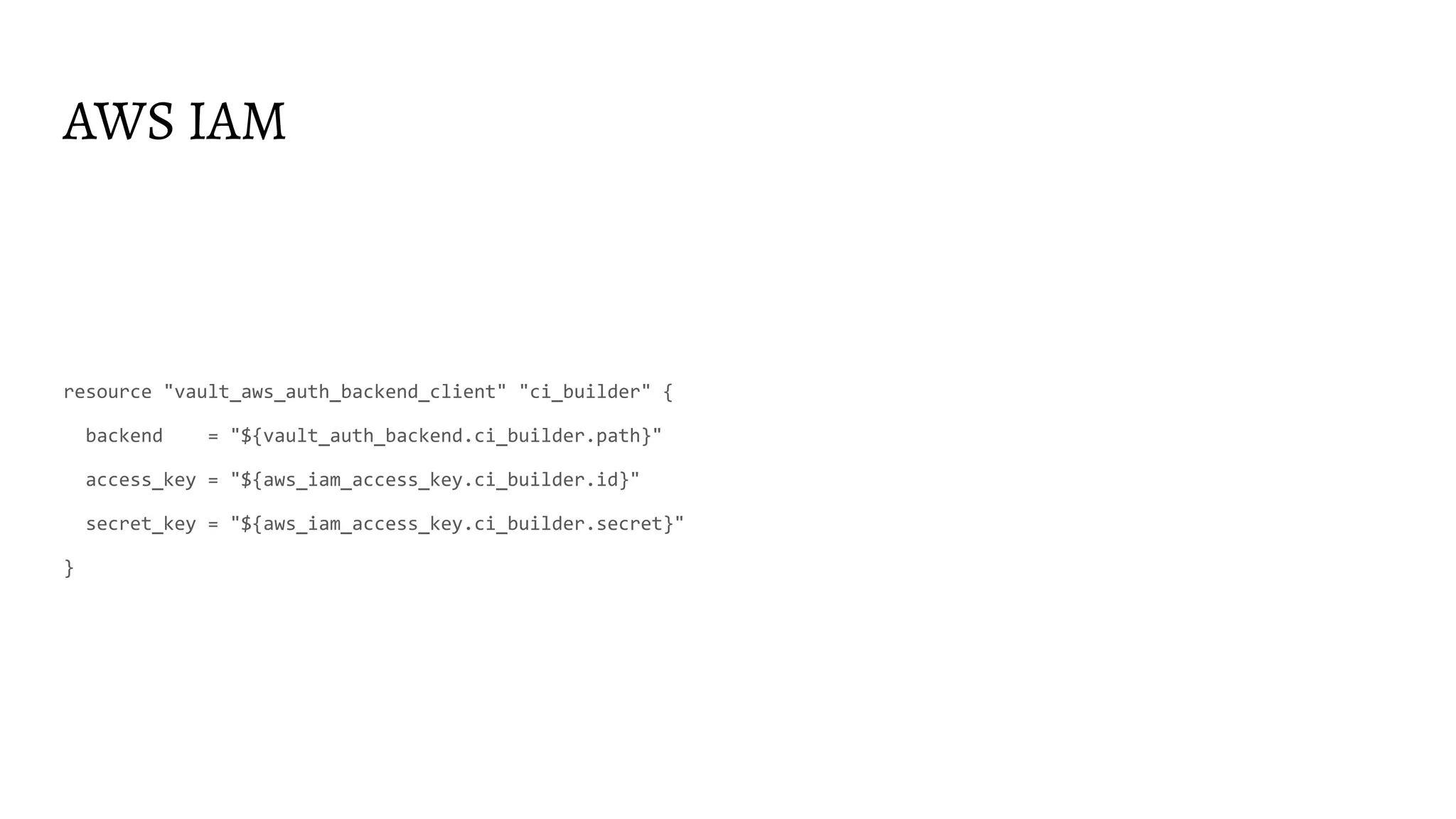
![AWS IAM
# https://www.vaultproject.io/docs/secrets/aws/index.html#example-iam-policy-for-vault
data "aws_iam_policy_document" "iam_auth_for_ci" {
statement {
effect = "Allow"
actions = ["iam:GetUser","iam:GetRole",]
resources = ["arn:aws:iam::${data.aws_caller_identity.i.account_id}:*"]
}
statement {
effect = "Allow"
actions = ["sts:AssumeRole"]
resources = ["arn:aws:iam::${data.aws_caller_identity.i.account_id}:role/vault-cluster*"]
}
}](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-36-2048.jpg)
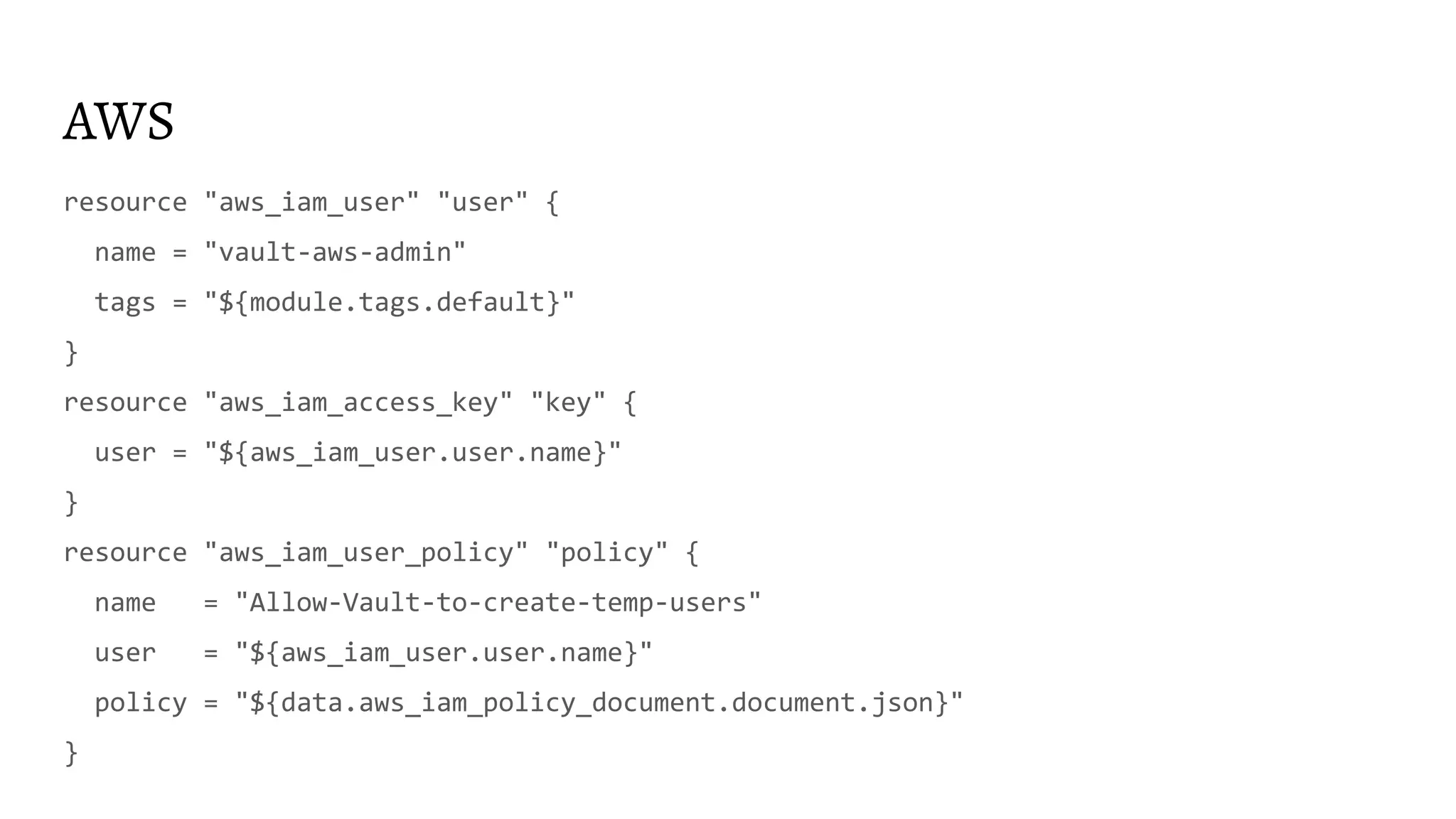
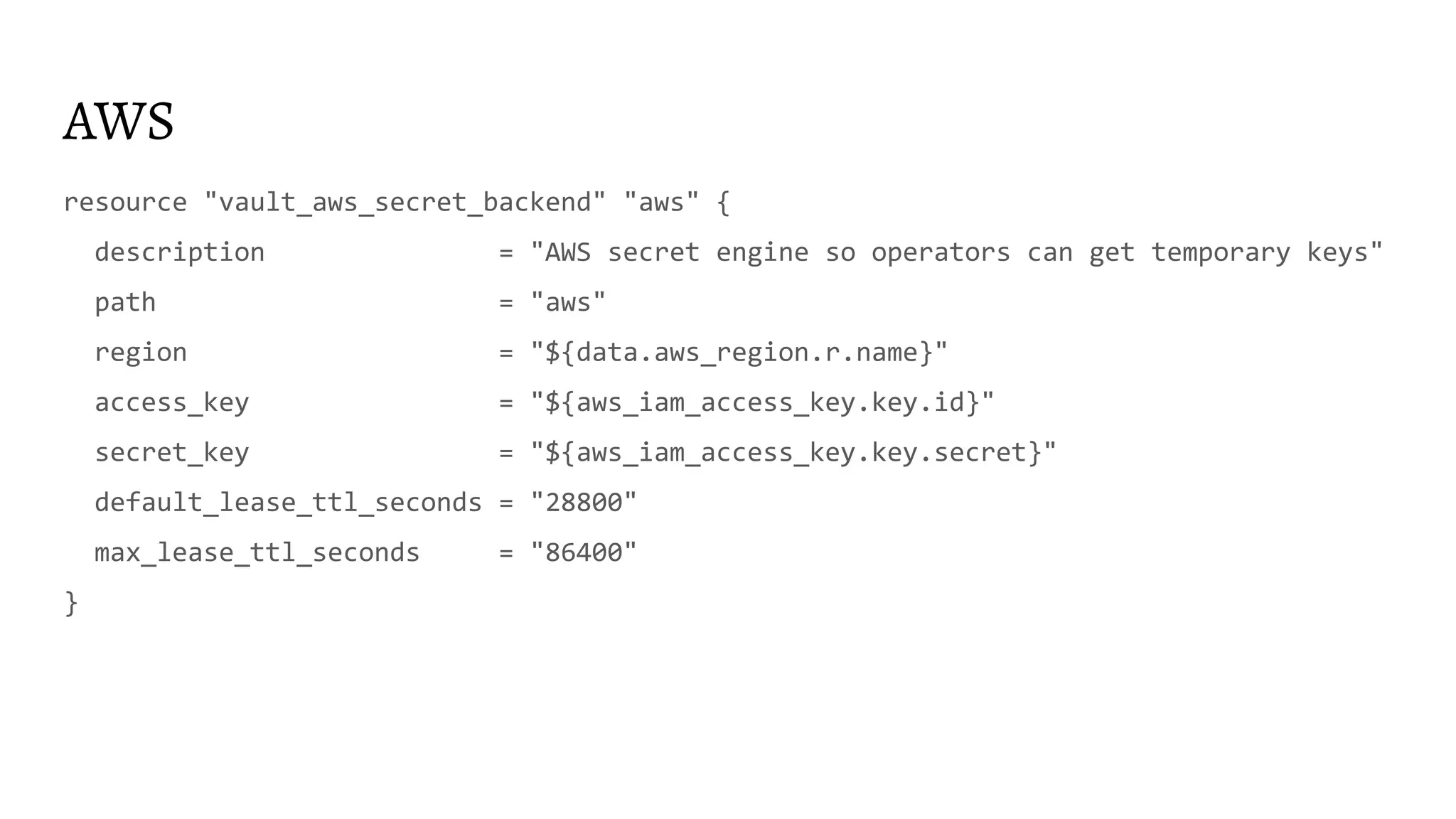
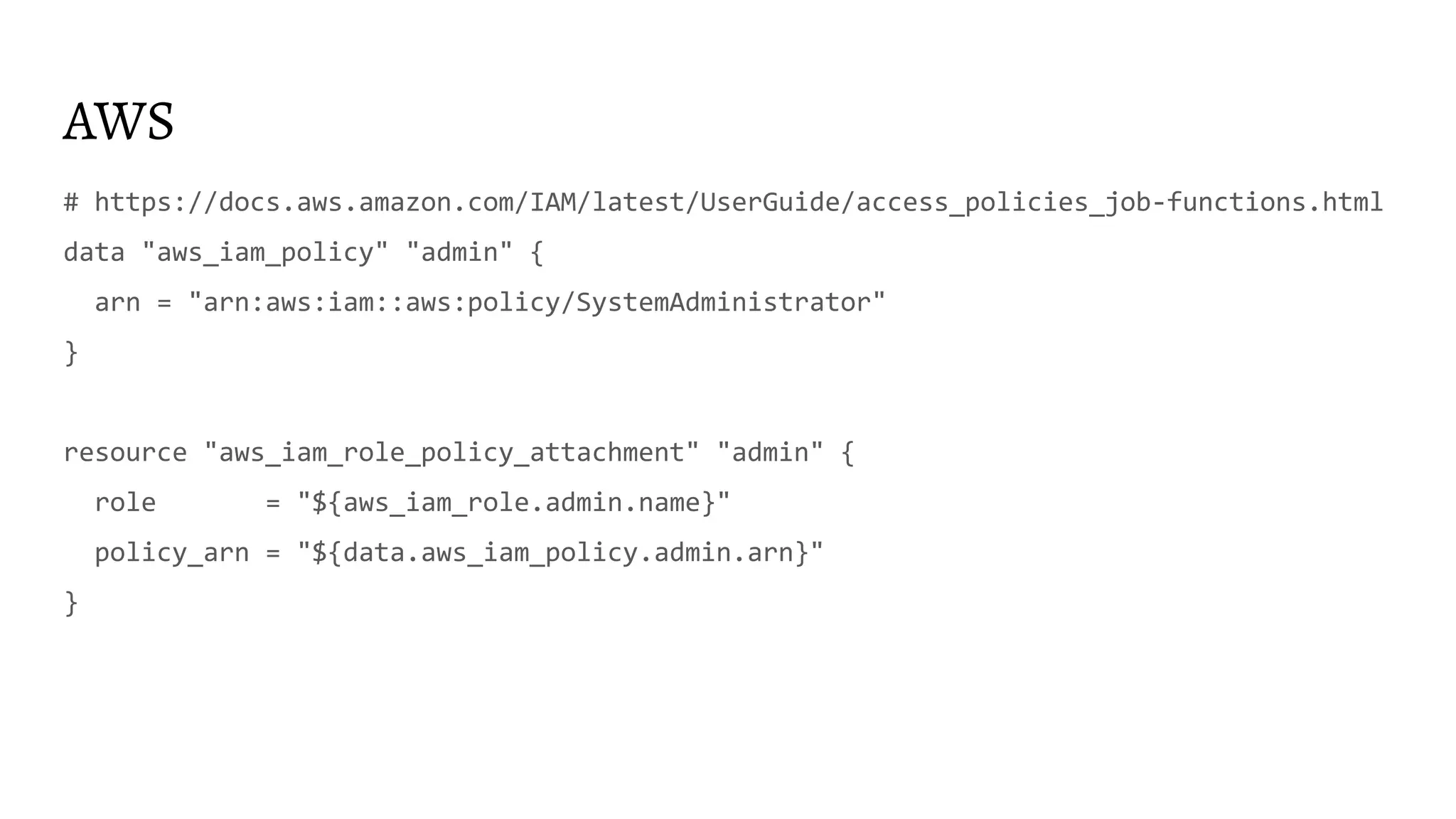
![AWS
resource "aws_iam_role" "admin" {
name = "admin"
max_session_duration = "28800"
assume_role_policy = "${data.aws_iam_policy_document.trust.json}"
tags = "${module.tags.default}"
}
resource "vault_aws_secret_backend_role" "access-aws-admin-role" {
backend = "${vault_aws_secret_backend.aws.path}"
name = "access-aws-admin-role"
role_arns = ["${aws_iam_role.admin.arn}"]
credential_type = "assumed_role"
}](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-45-2048.jpg)
![AWS
data "aws_iam_policy_document" "trust" {
statement {
effect = "Allow"
actions = ["sts:AssumeRole"]
principals {
type = "AWS"
identifiers = ["${aws_iam_user.user.arn}"]
}
}
}](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-47-2048.jpg)

![Secrets rotation
DB_SECRET_ENGINE_MOUNTS=$(vault secrets list -format=json | jq -r '. | to_entries[] | select(.value.type |
startswith("database")) | .key')
for DB_SECRET_ENGINE_MOUNT in ${DB_SECRET_ENGINE_MOUNTS}; do
DB_CONNECTION_NAMES=$(vault list -format=json ${DB_SECRET_ENGINE_MOUNT}config | jq --raw-output .[])
for DB_CONNECTION_NAME in ${DB_CONNECTION_NAMES}; do
vault write -force ${DB_SECRET_ENGINE_MOUNT}rotate-root/${DB_CONNECTION_NAME}
done
done](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-52-2048.jpg)
![KV state issue
● Terraform provider for Vault in some cases(?) does not re-read KV and newly added
values are not readable/found
● terraform state rm data-source
data "vault_generic_secret" "rundeck_auth" {
path = "secret/rundeck_auth"
}
provider "rundeck" {
url = "http://rundeck.example.com/"
auth_token = "${data.vault_generic_secret.rundeck_auth.data["auth_token"]}"
}](https://image.slidesharecdn.com/2020-02-20-hashicorpvaultconfigurationascodeviahashicorpterraformstoriesfromtrenches-200221073520/75/2020-02-20-HashiTalks-2020-HashiCorp-Vault-configuration-as-code-via-HashiCorp-Terraform-stories-from-trenches-55-2048.jpg)