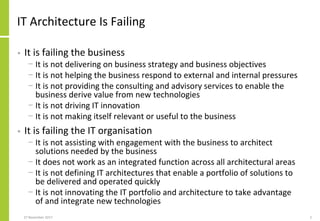
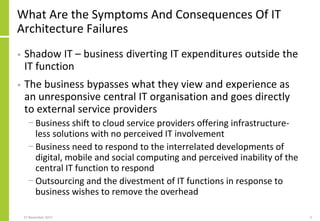
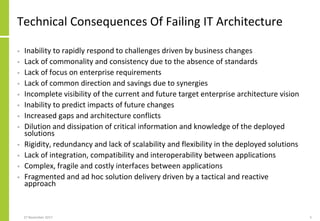
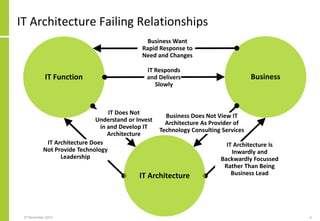
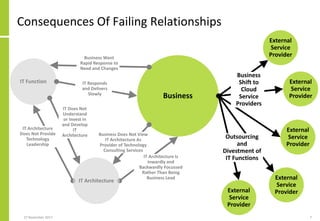
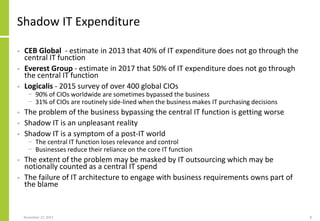
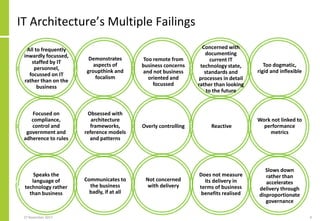
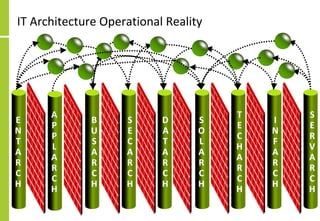
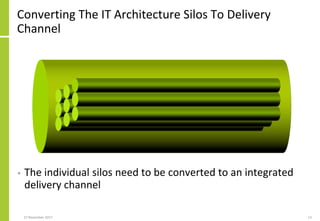
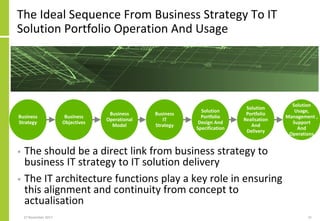
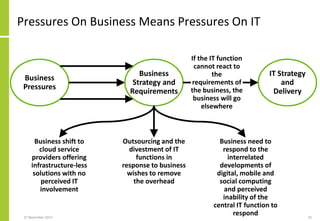
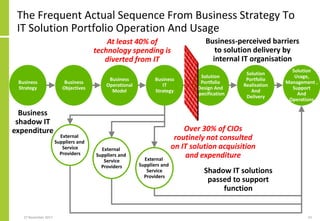
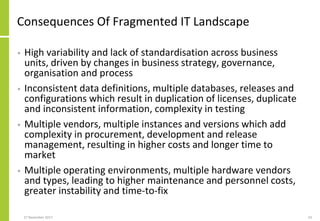
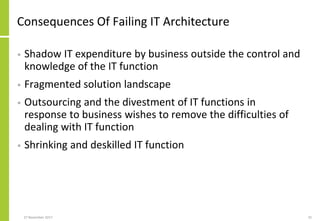
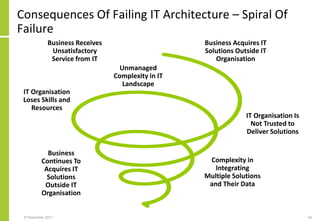
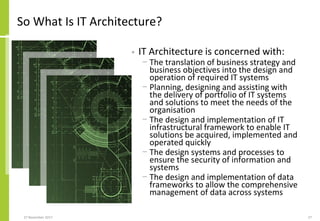
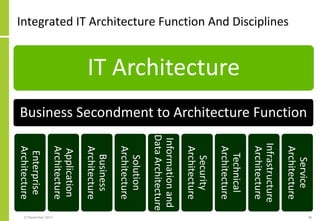
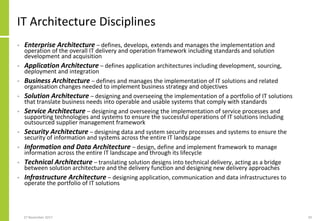
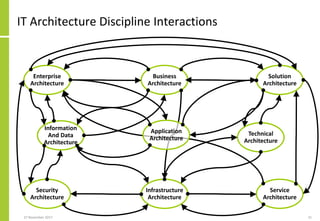
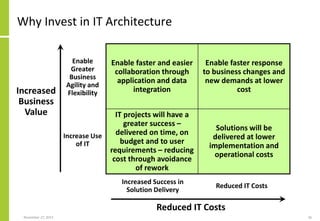
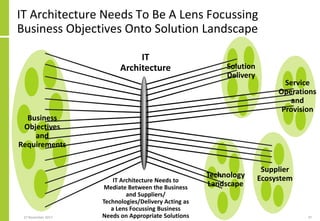
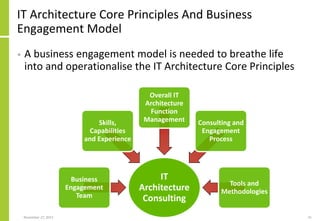
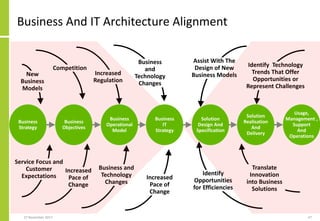
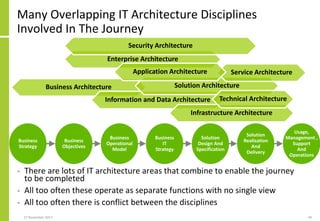
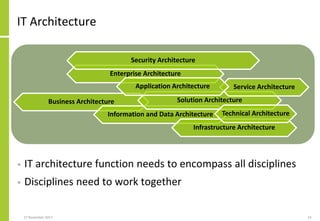
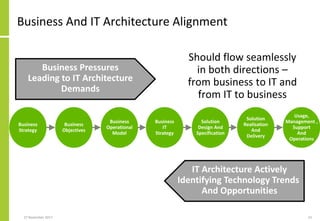
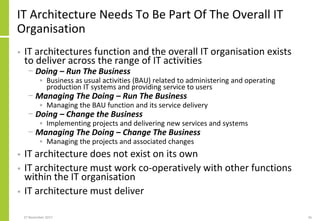
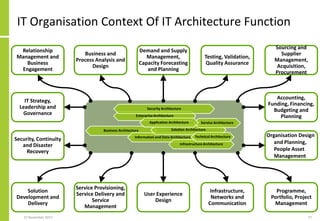
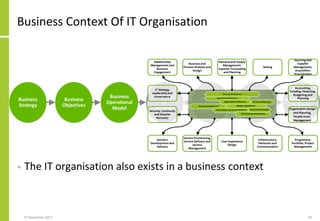
The document critiques the failures of IT architecture in effectively supporting business strategies and objectives, leading to shadow IT and a reliance on external service providers. It highlights issues such as slow response times, lack of integration, and poor communication, which weaken the relationship between IT and business functions. Furthermore, it calls for an alignment of IT architecture with business needs and emphasizes the necessity of a collaborative approach to enhance both governance and delivery of IT solutions.