Embed presentation
Download as PDF, PPTX
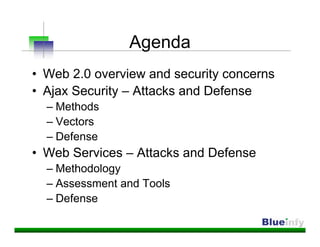
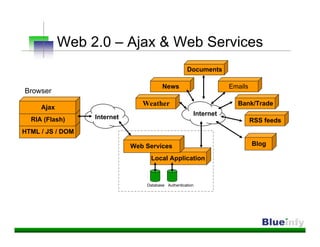
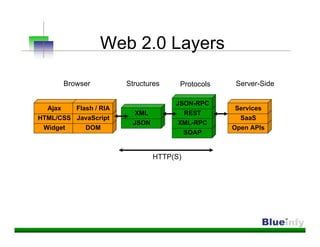
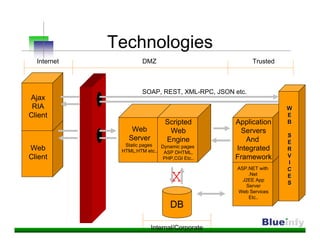
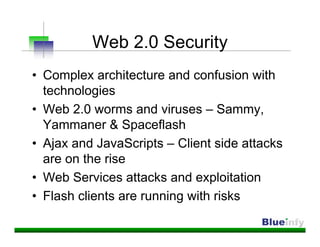

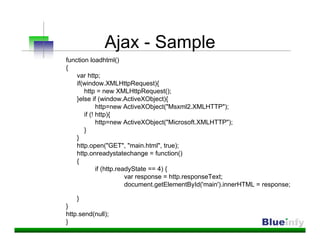
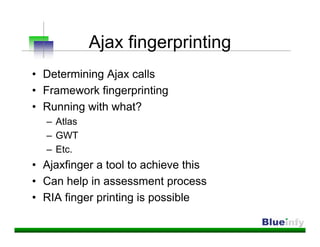
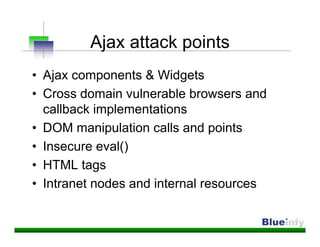
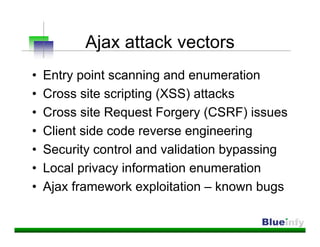
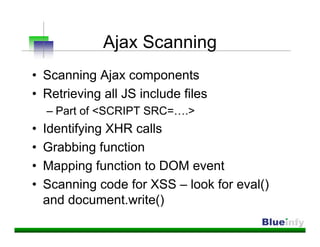
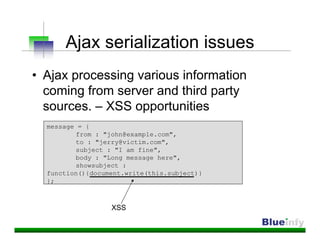
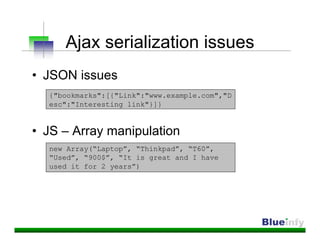
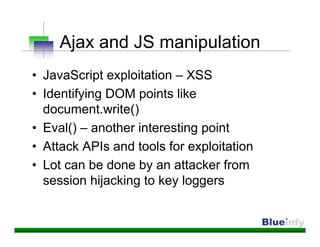
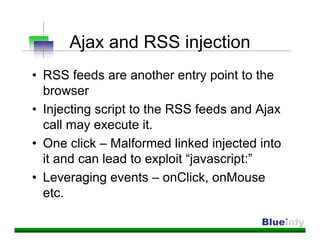
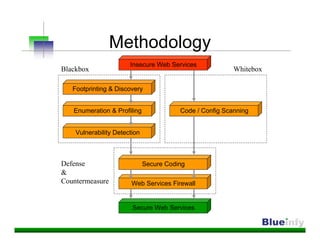
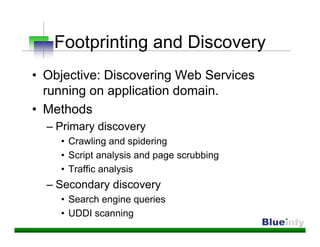
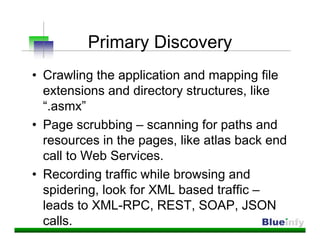
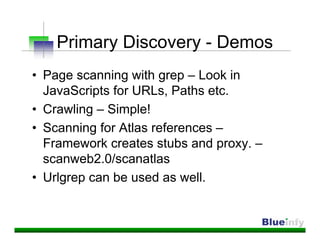
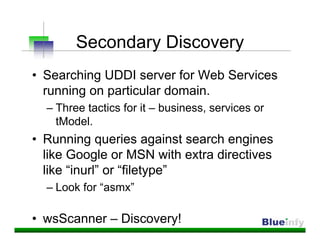
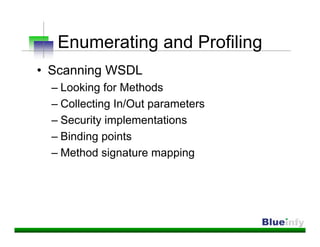
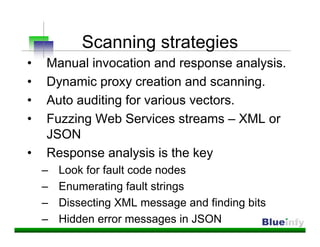
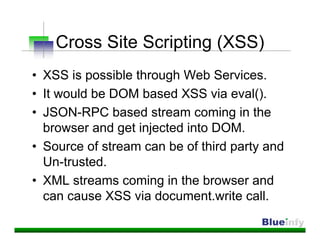
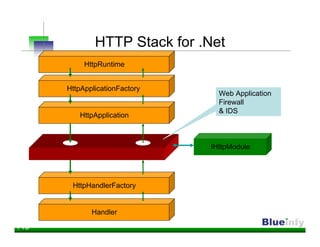

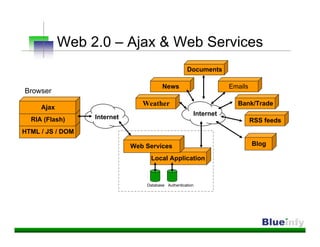
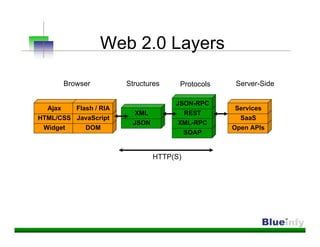
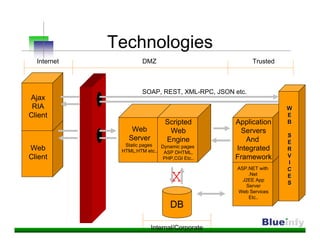
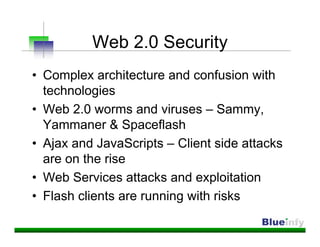
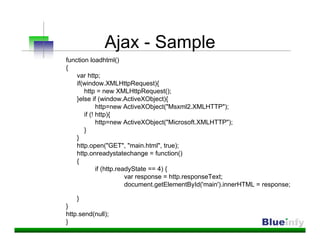
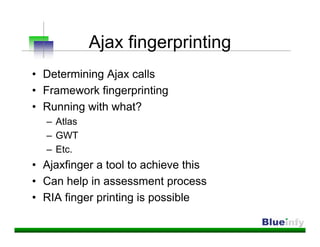
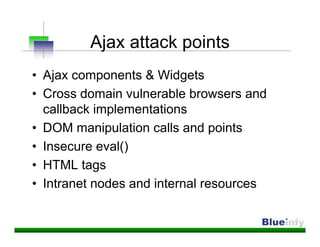
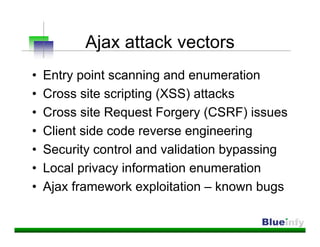
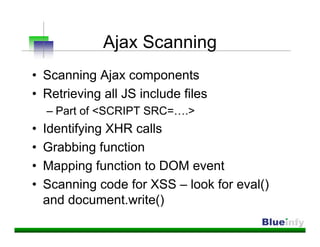
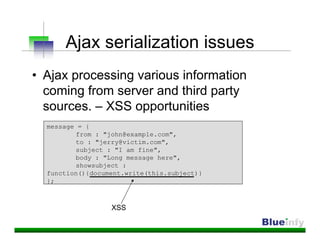
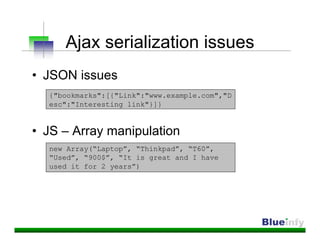
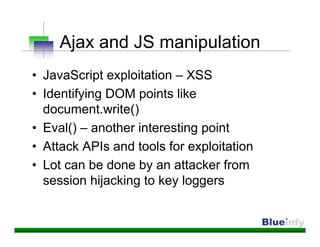
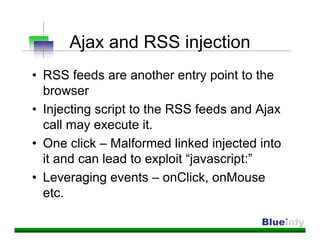
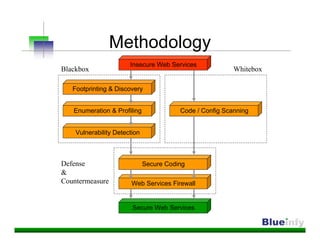
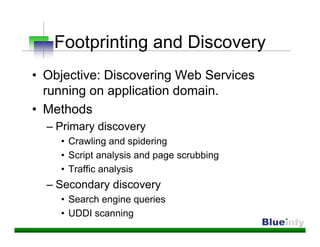
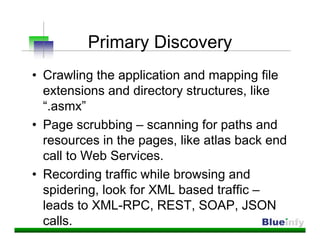
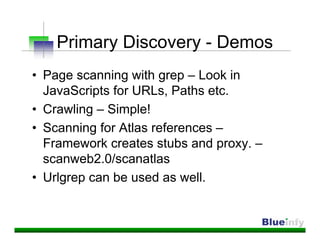
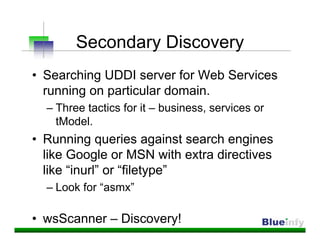
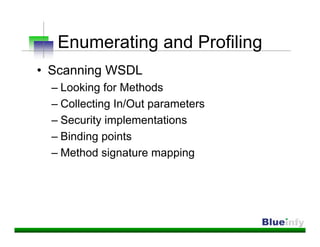
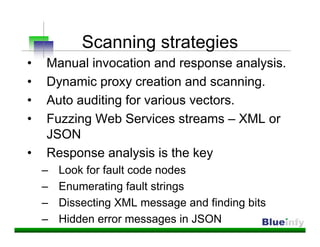
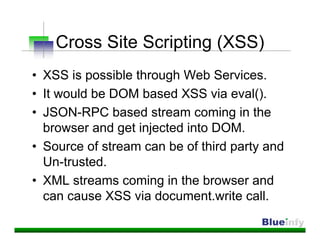
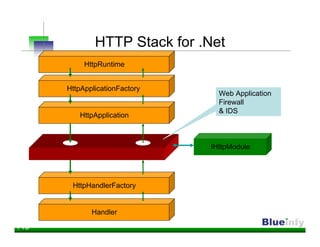
This document summarizes a presentation on hacking Web 2.0 technologies and web services. The presentation discusses security concerns with Ajax, including attacks like cross-site scripting and request forgery. It also covers fingerprinting Ajax frameworks, vulnerabilities in Ajax data structures and serialization, and defenses like validating data and avoiding client-side logic. Regarding web services, the document outlines methods for discovery, profiling, and attacks like injection flaws and insecure direct object references. It emphasizes the need for code analysis and filtering input through an IHTTPModule firewall module.