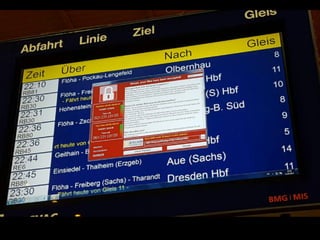
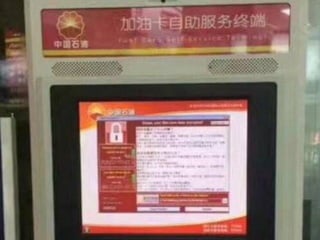
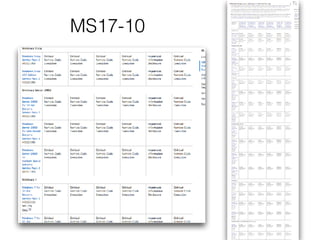
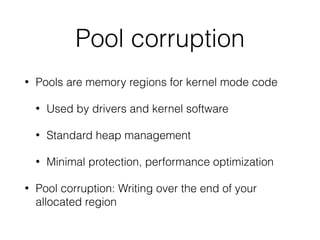
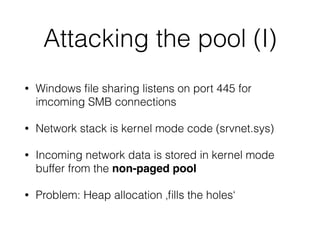
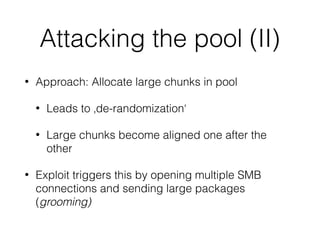
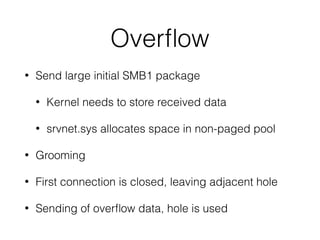
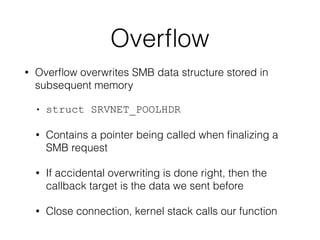
The document discusses vulnerabilities related to the WannaCry ransomware, specifically focusing on pool corruption and the EternalBlue exploit. It describes how Windows file sharing and the kernel mode network stack facilitate attacks by exploiting memory allocation in the non-paged pool. The outlined exploitation technique involves manipulating SMB connections to trigger overflows and take control of the kernel's memory handling.