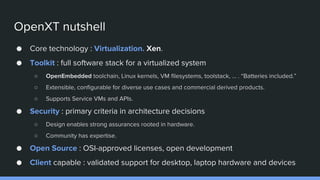
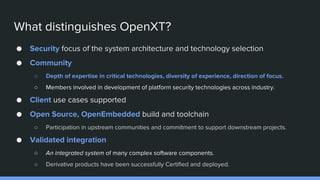
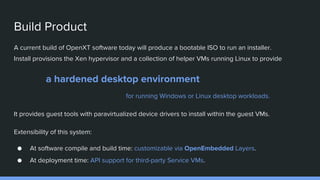
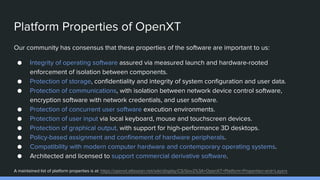
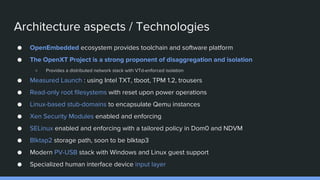
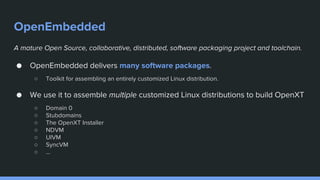
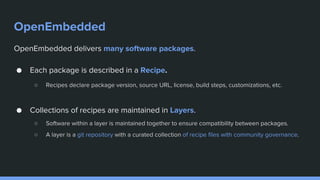
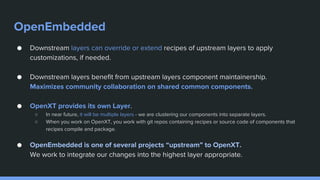
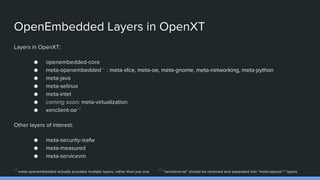
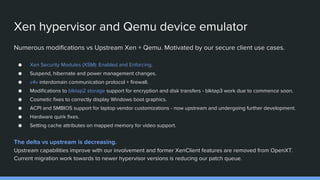
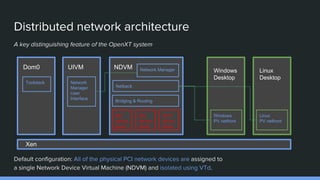
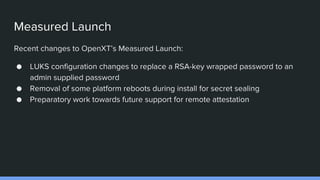
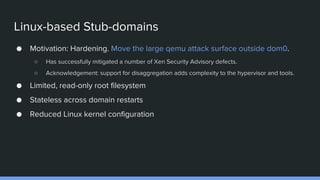
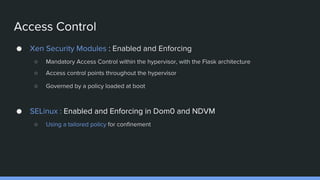
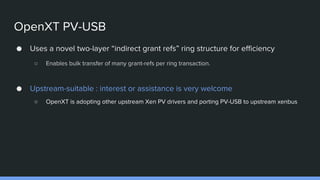
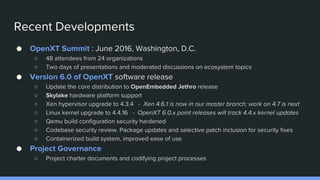
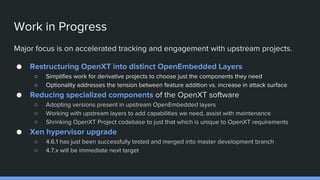
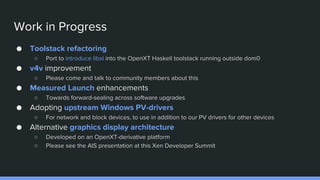
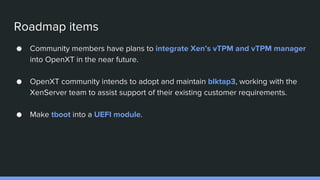
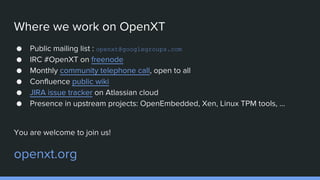
The OpenXT project, initiated by Christopher Clark at BAE Systems in 2016, focuses on advancing secure computing through an open system architecture that prioritizes extensibility and collaboration. Key features include a robust virtualization stack, an emphasis on security through hardware isolation, and support for various client use cases with integrated networking solutions. Current developments involve software updates, security reviews, and an ongoing engagement with upstream projects to streamline and enhance the OpenXT platform.