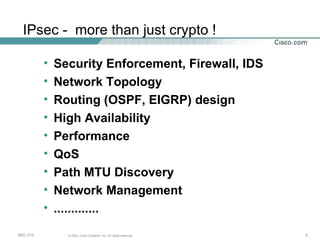
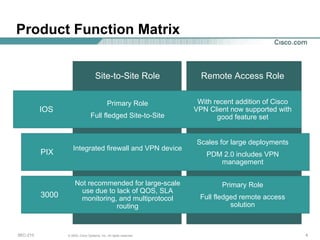
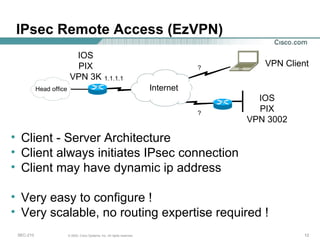
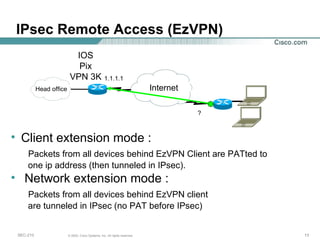
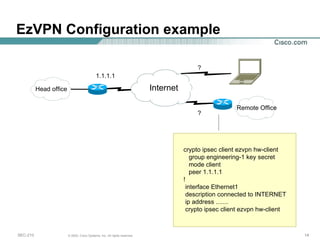
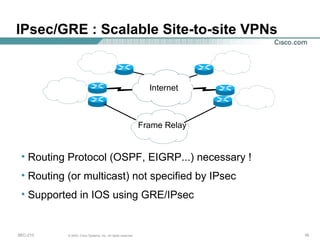
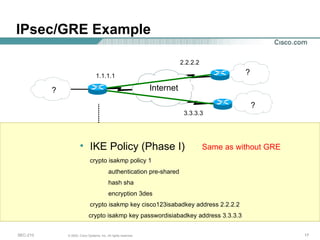
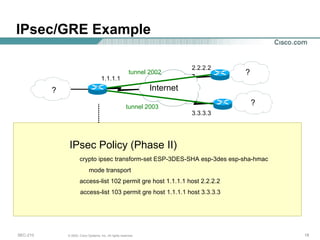
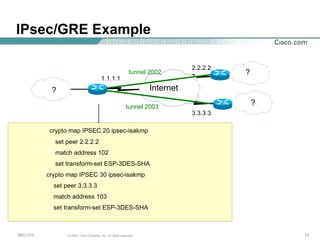
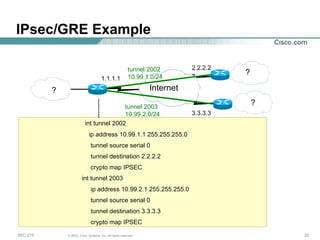
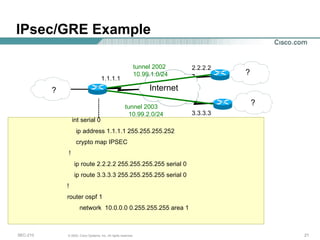
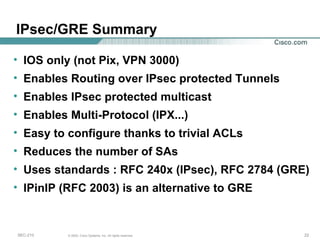
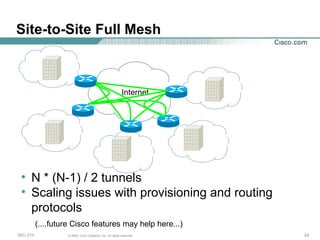
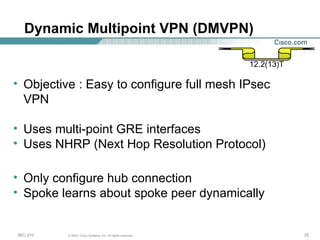
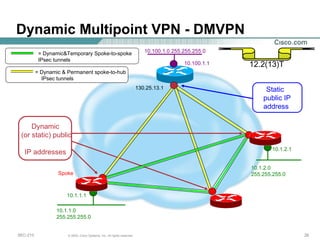
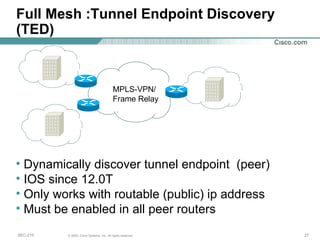
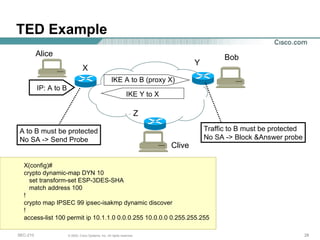
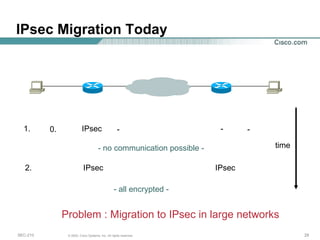
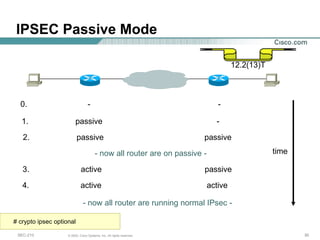
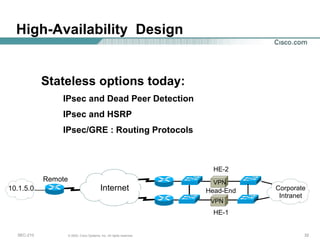
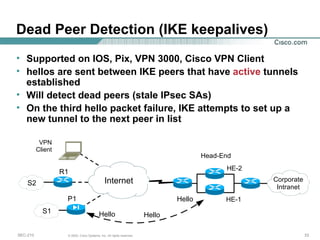
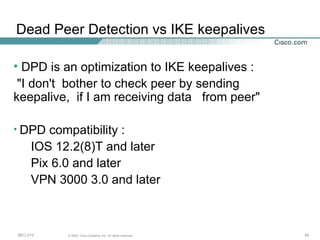
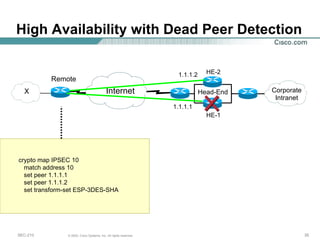
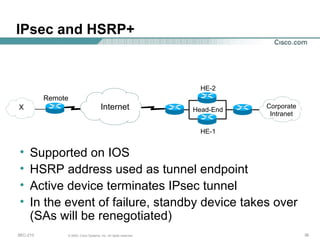
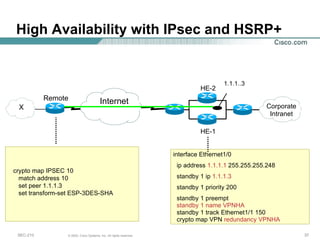
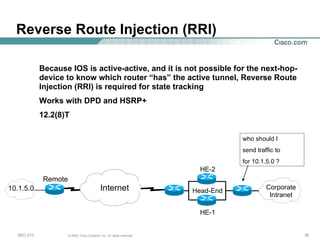
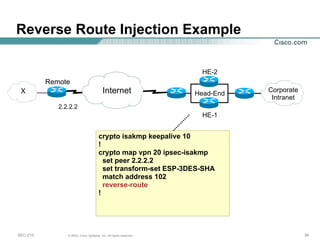
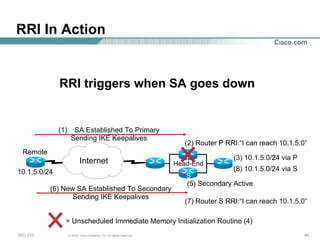
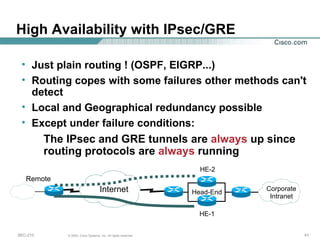
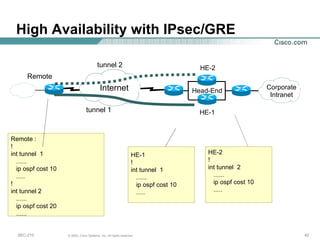
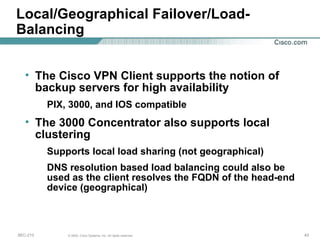
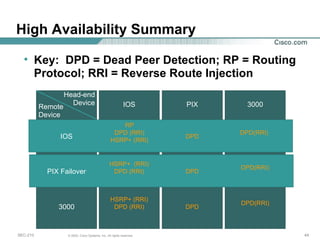
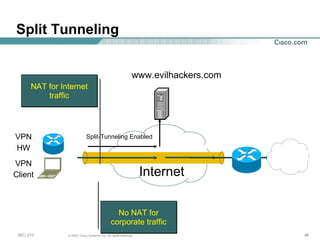
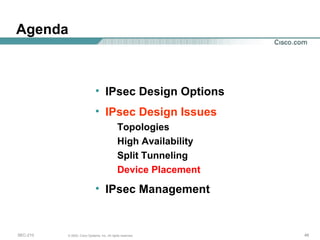
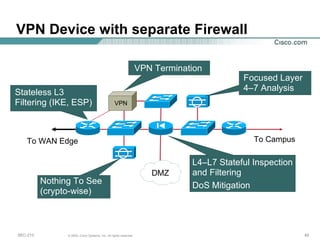
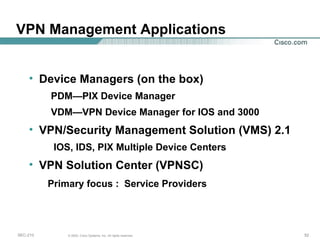
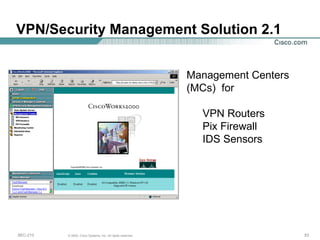
This document summarizes IPsec VPN design options and management. It discusses site-to-site and remote access VPN topologies using IPsec, including full mesh, DMVPN, and IPsec over GRE. It also covers high availability using DPD, HSRP+, and routing protocols. Other topics include split tunneling, device placement with integrated firewalls, and general IPsec management.
![Deploying and Managing Enterprise IPsec VPNs Ken Kaminski Cisco Systems Consulting Systems Engineer – Security/VPN Northeast [email_address]](https://image.slidesharecdn.com/vpn4-1231525243506308-2/75/Vpn-4-1-2048.jpg)