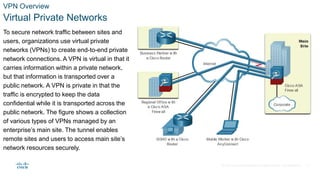
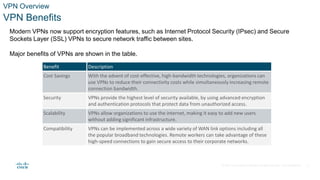
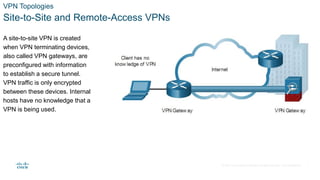
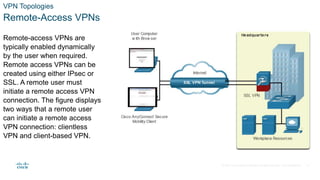
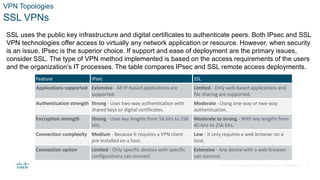
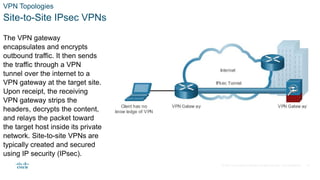
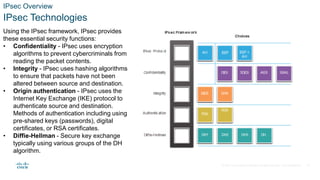
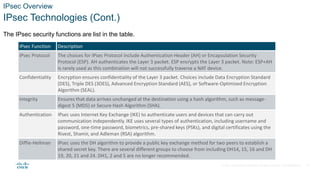
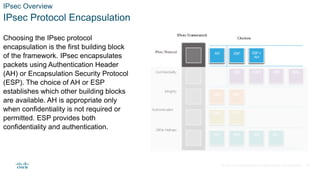
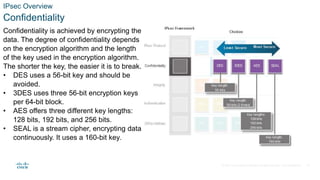
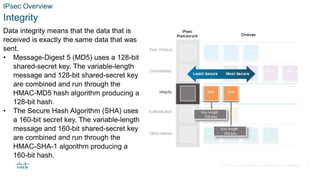
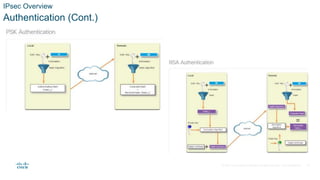
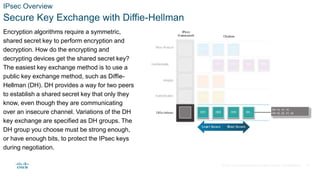
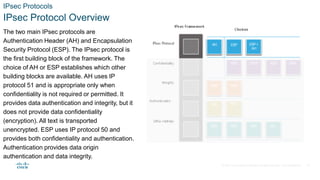
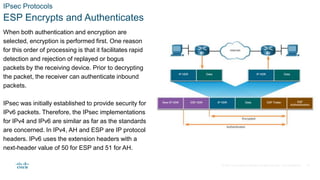
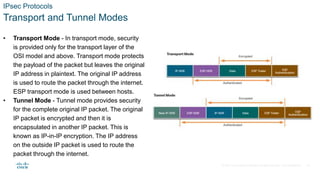
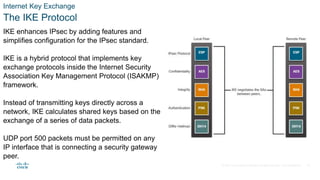
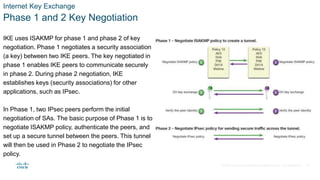
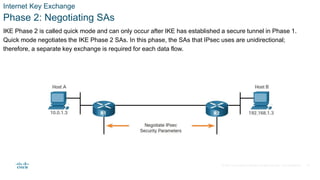
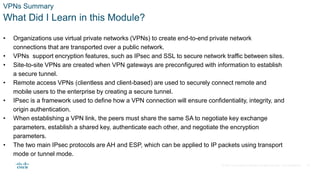
The document provides an overview of Virtual Private Networks (VPNs), emphasizing their purpose in securing network traffic between remote sites and users through encryption over public networks. It discusses the benefits of VPNs, including cost savings, enhanced security, and scalability, as well as the different types of VPN topologies like site-to-site and remote-access VPNs. Additionally, it outlines the fundamentals of the IPSec protocol, including its functions, security features, and the Internet Key Exchange (IKE) process for secure key negotiation.