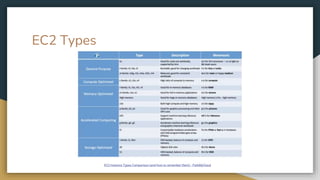
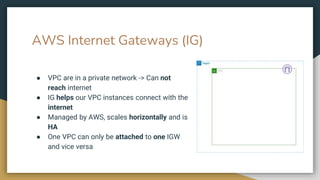
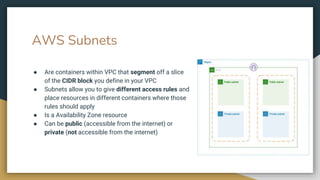
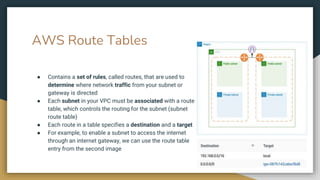
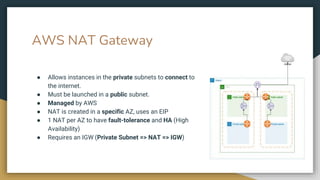
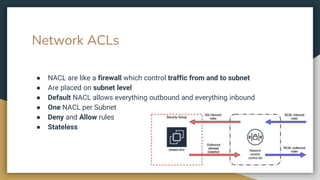
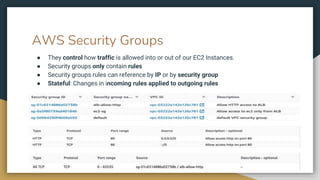
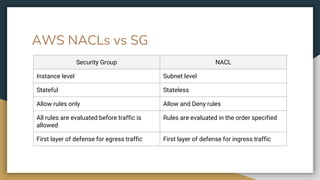
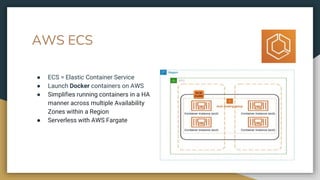
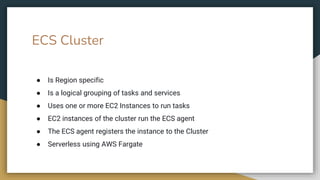
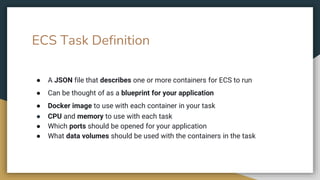
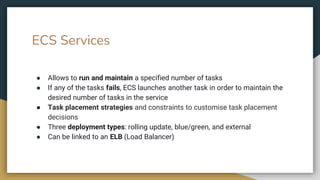
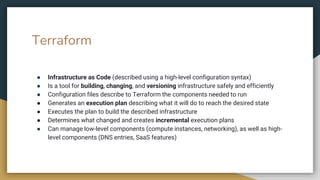
The document provides an introduction to AWS, detailing its main components such as regions, availability zones, and services like EC2, ELB, and VPC. It also explains network configurations including NAT gateways, subnets, security groups, and the use of Terraform for infrastructure as code. Overall, it outlines how to manage and deploy cloud resources effectively while ensuring fault tolerance and high availability.