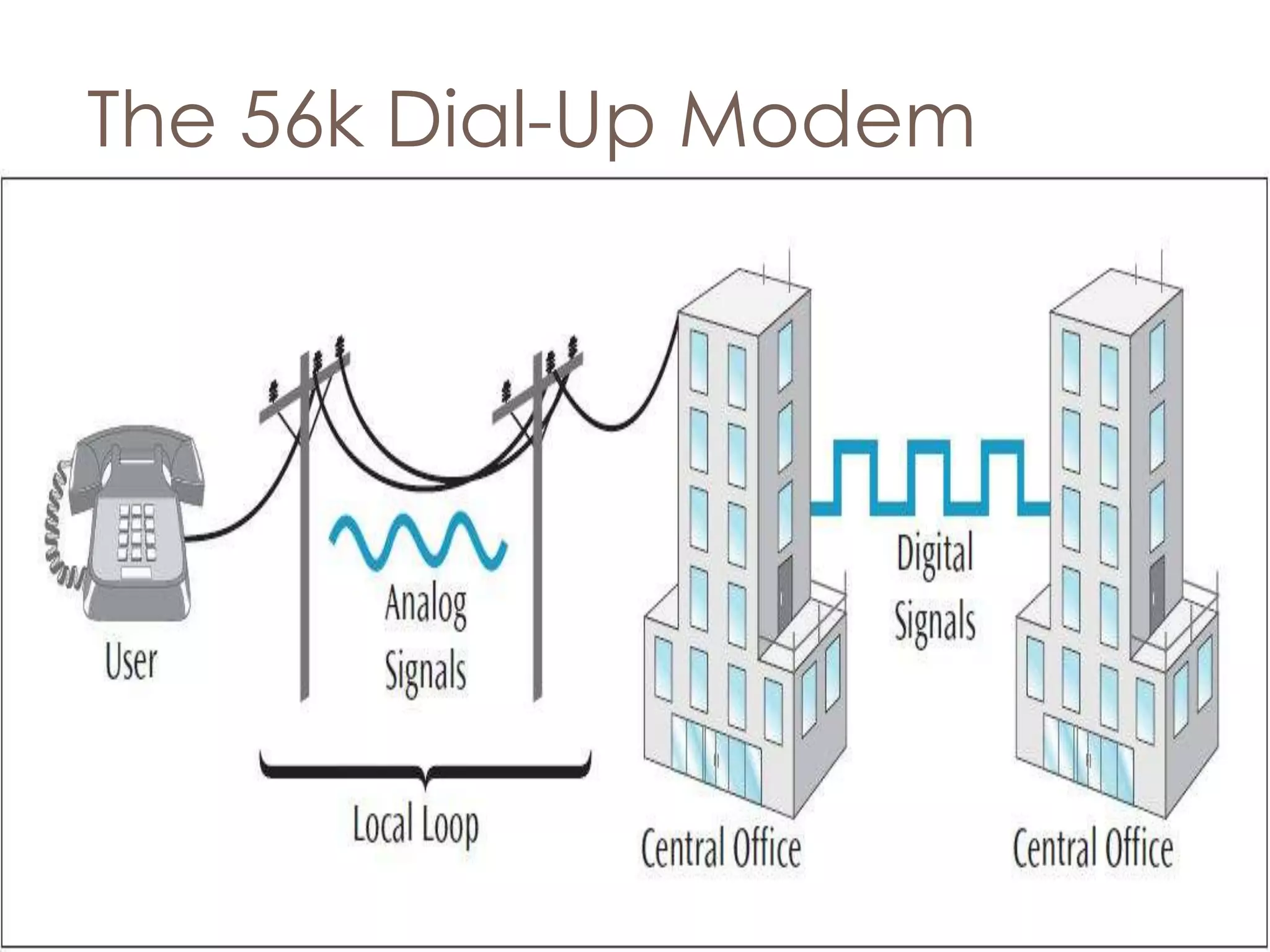
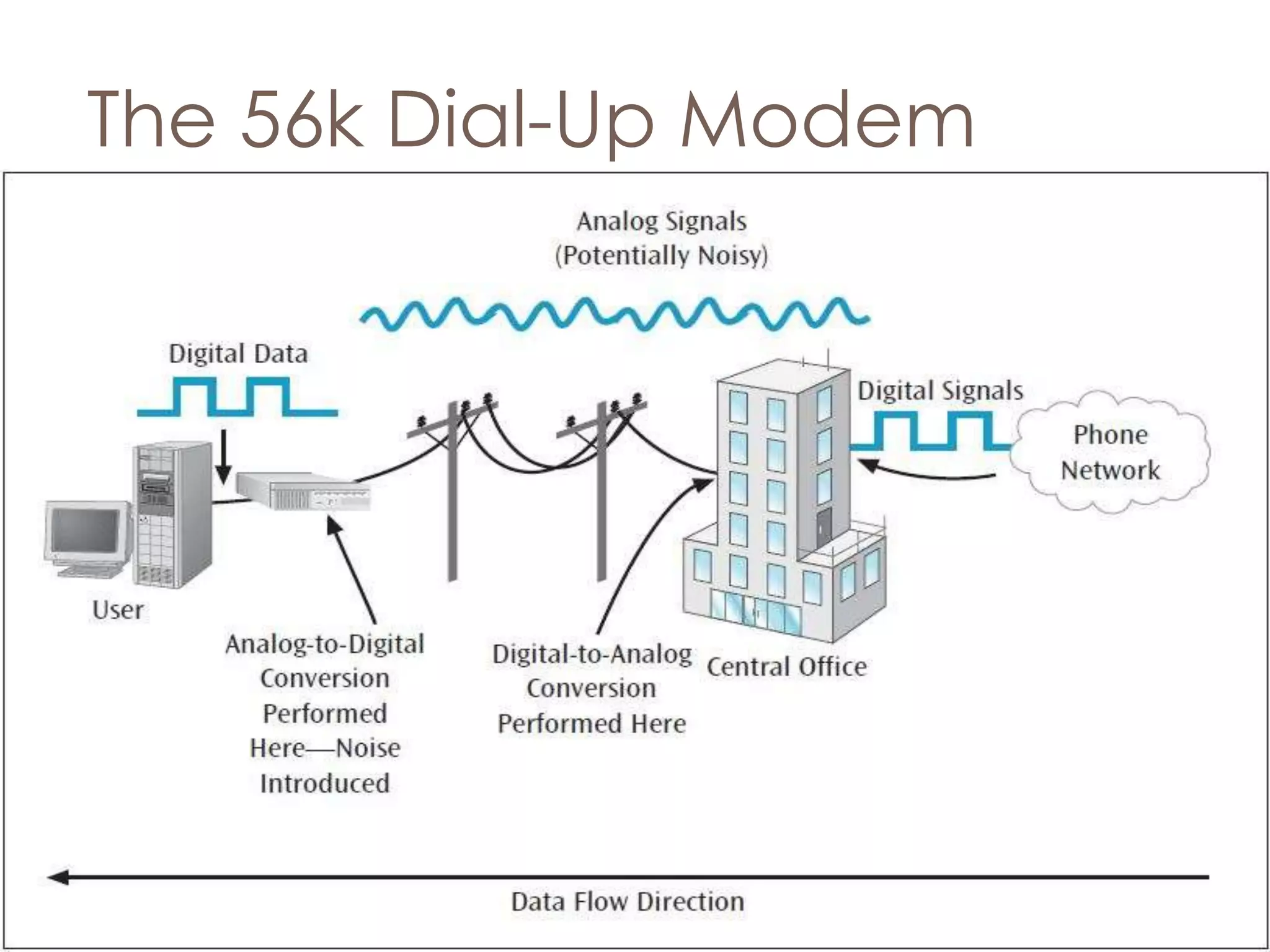
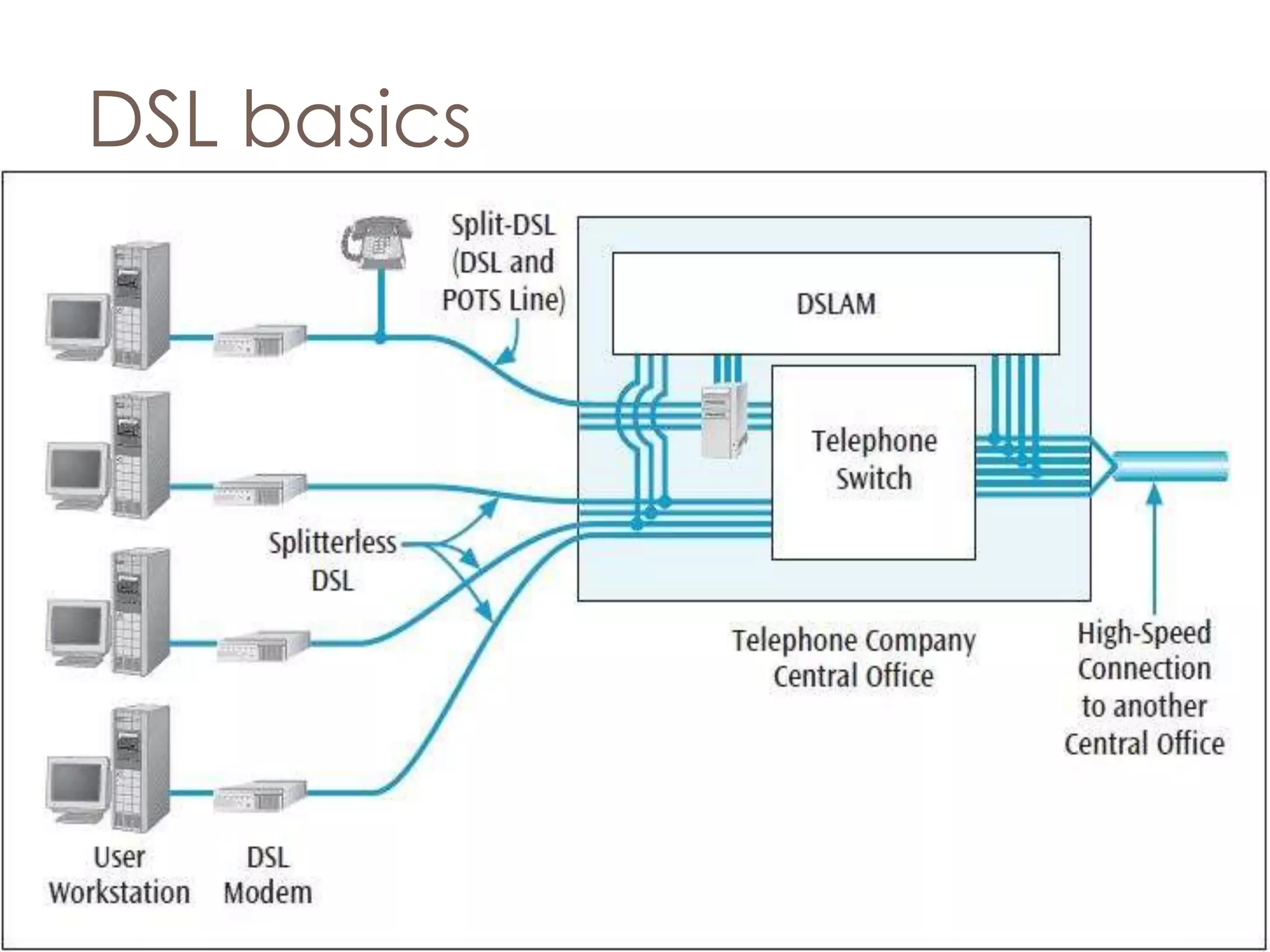
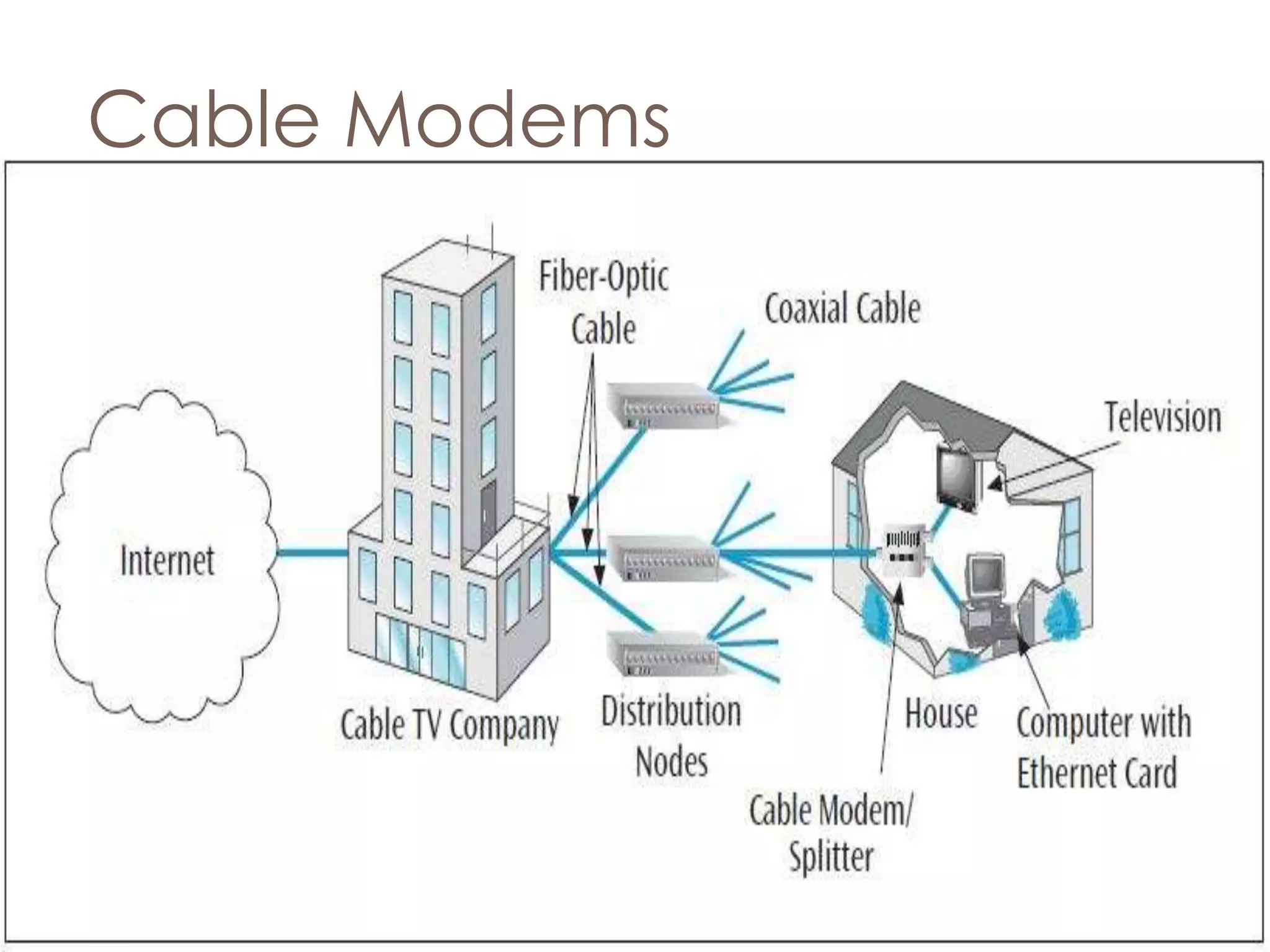
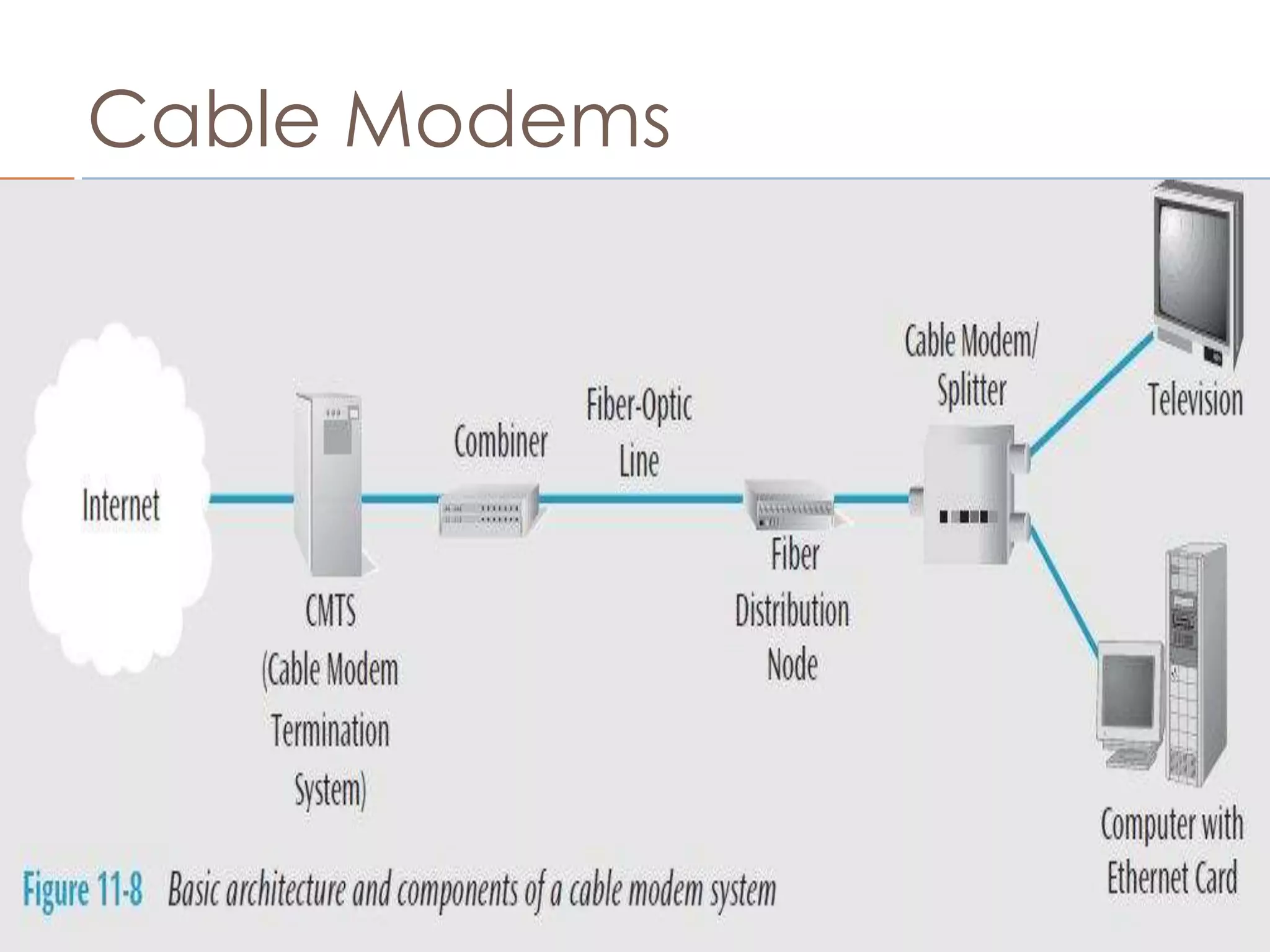
The document discusses different types of home internet connections, including dial-up modems, DSL, and cable modems. It describes how 56k dial-up modems worked using both analog and digital signaling to achieve higher speeds. Digital Subscriber Line (DSL) connections transmit data over existing telephone lines at speeds from hundreds of kbps to several mbps using technology like ADSL, VDSL2, and RADSL. Cable modems provide high-speed internet access through a cable television connection and separate computer data from video signals.