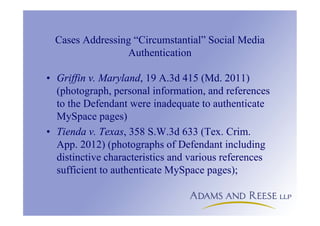
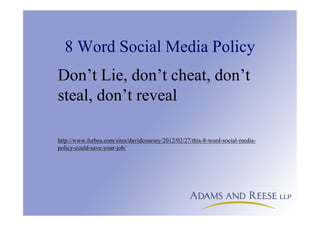
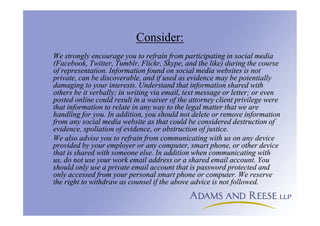
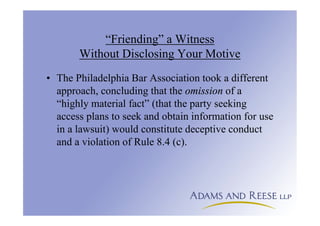
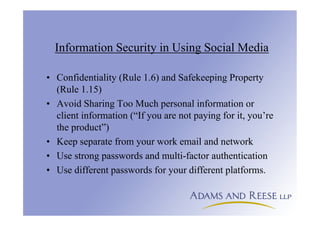
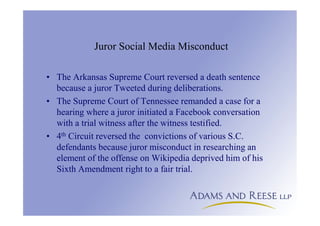
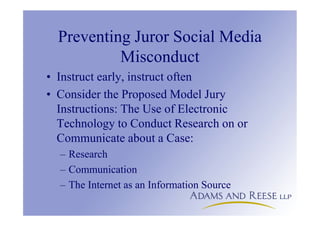
The document discusses the ethical responsibilities of attorneys in using social media, emphasizing the need for professional competence and adherence to ethics rules related to client confidentiality and communication. It highlights the implications of social media on attorney-client privilege and the risks associated with oversharing, while providing guidelines for secure communication and the management of online presence. Additionally, it addresses potential juror misconduct related to social media and the importance of establishing evidence authentication.
![Briefly on Authentication of ESI
• [T]he inability to get evidence admitted
because of a failure to authenticate is almost
always a self-inflicted injury which can be
avoided by thoughtful advance preparation.
Lorraine v. Markel American Ins. Co., 241
F.R.D. 534, 542 (D.Md.2007).
• In re Vinhnee, 336 B.R. 437, 444 (9th Cir.
BAP 2005)](https://image.slidesharecdn.com/2016-12-08usingsocialmediaethically-161222133006/85/Using-Social-Media-Ethically-27-320.jpg)