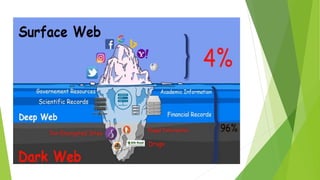
This document provides an overview of the topic of ethical hacking. It is divided into six units that cover concepts like footprinting, scanning networks, enumeration, system hacking, password cracking, malware threats, sniffing, social engineering, and session hijacking. It defines ethical hacking as hacking performed by white hat hackers to find security vulnerabilities and prevent attacks from black hat hackers. In comparison, unethical or black hat hacking is done illegally and maliciously by cybercriminals. The document also distinguishes between the surface web, deep web, and dark web, with the dark web requiring special software and protocols to access anonymously.