Embed presentation
Download as PDF, PPTX
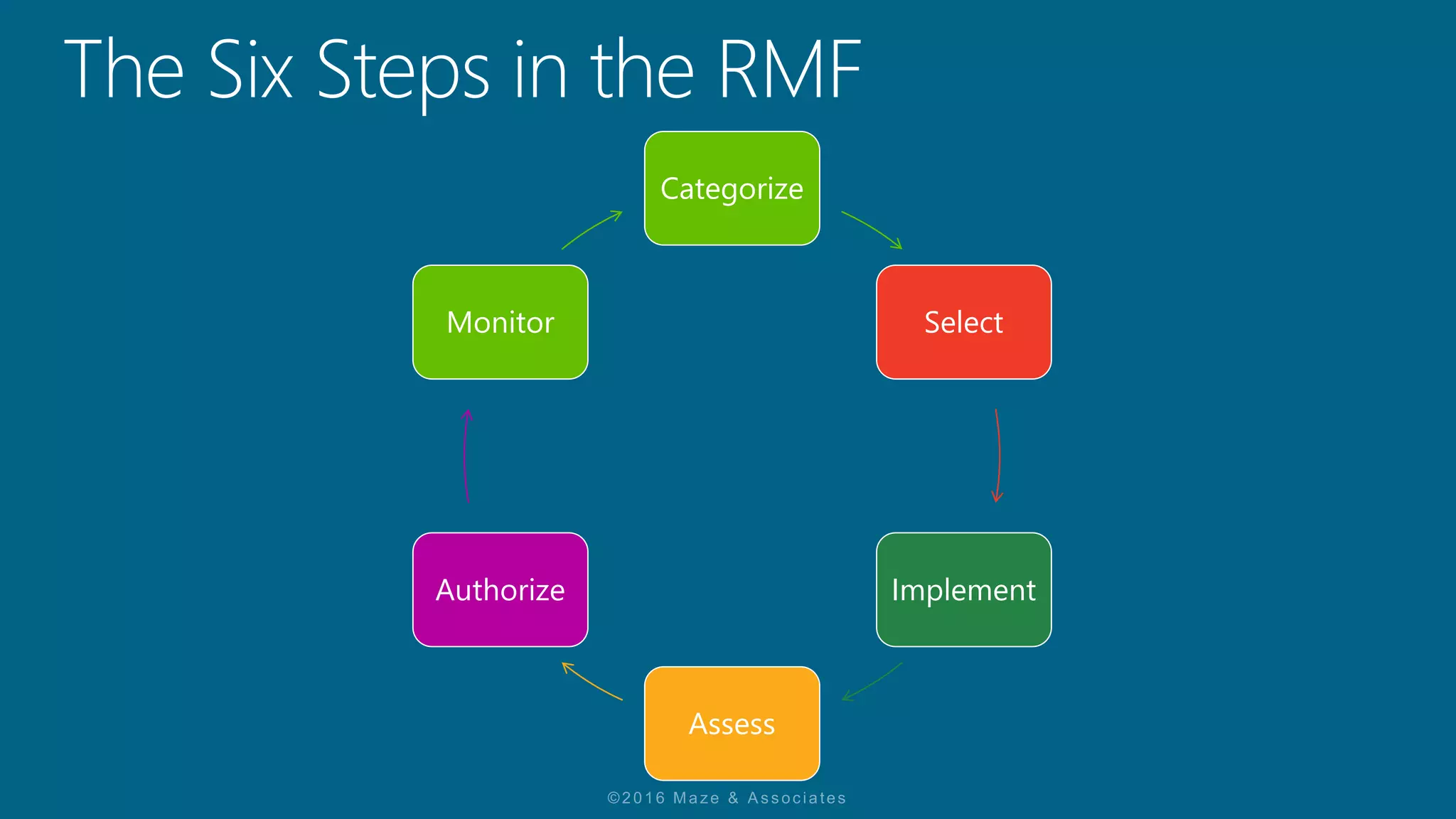

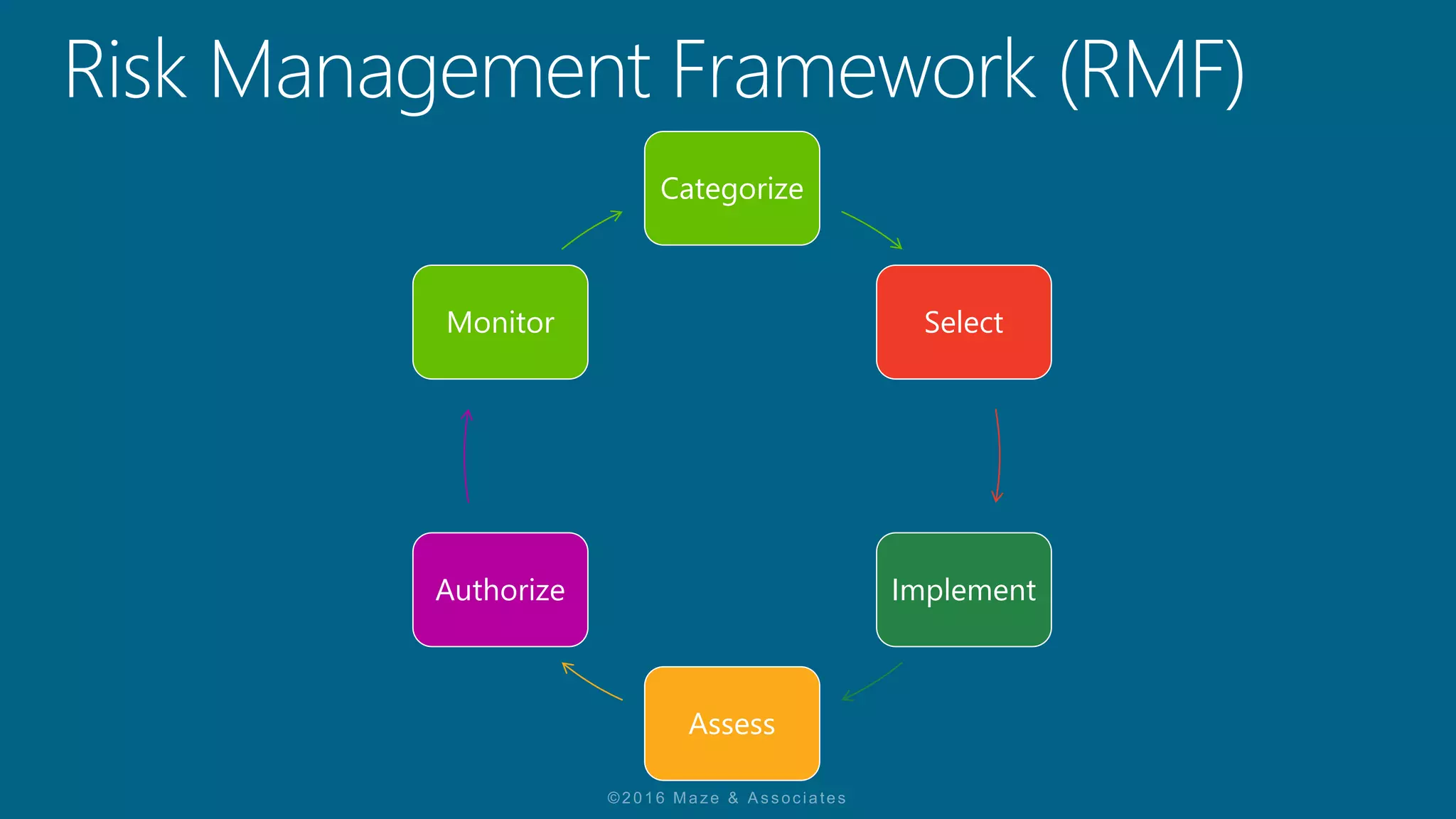
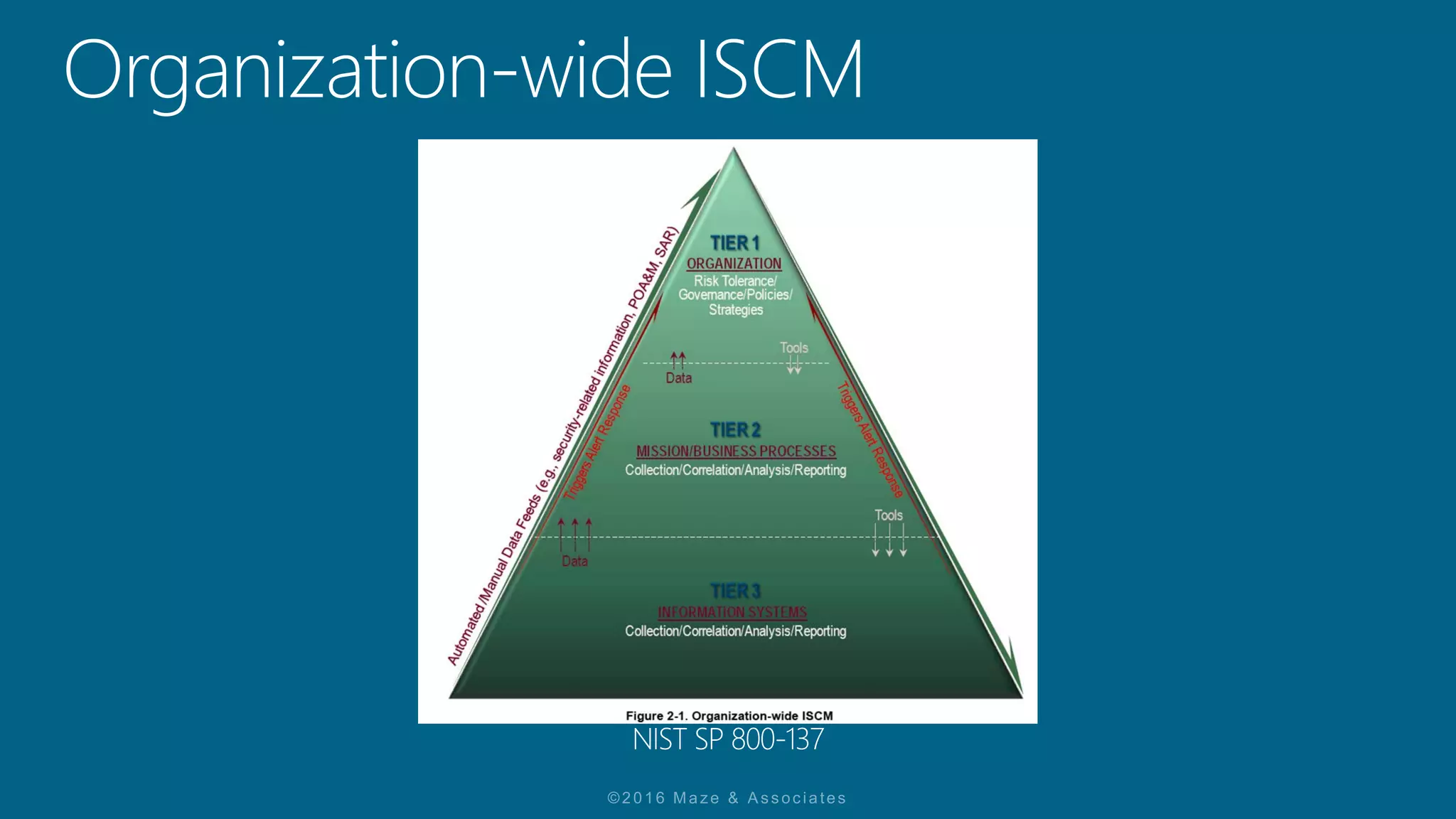
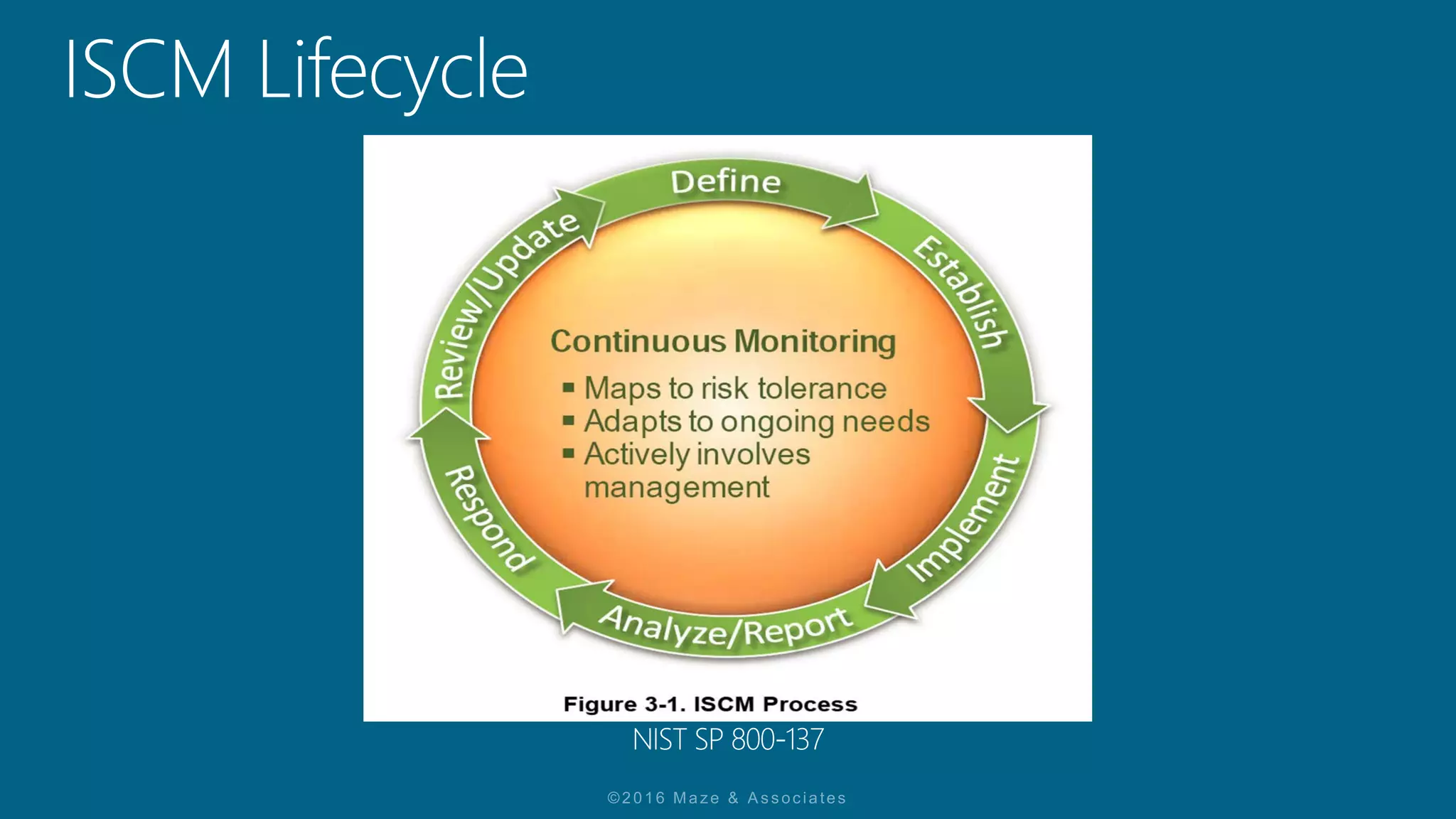

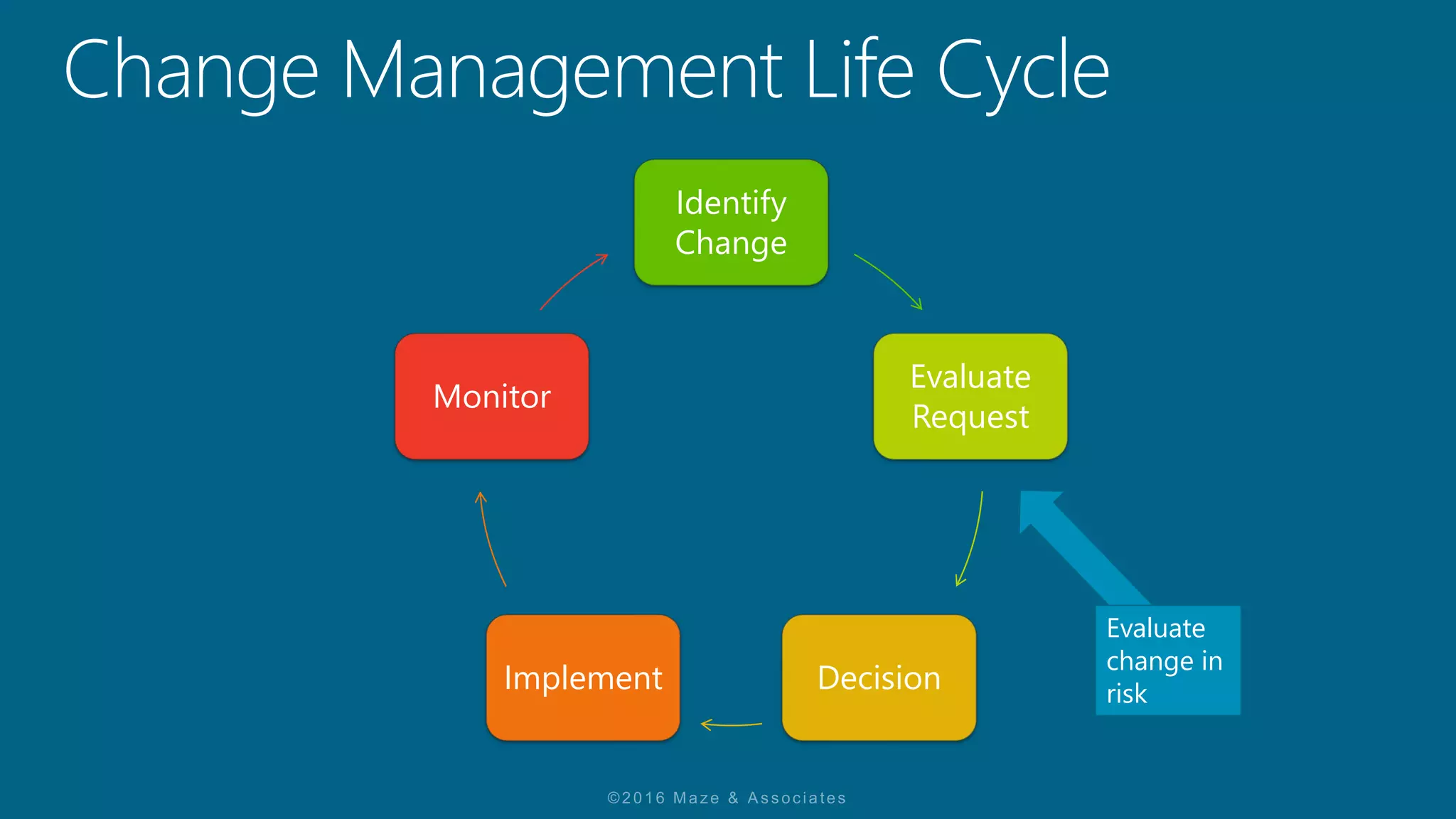



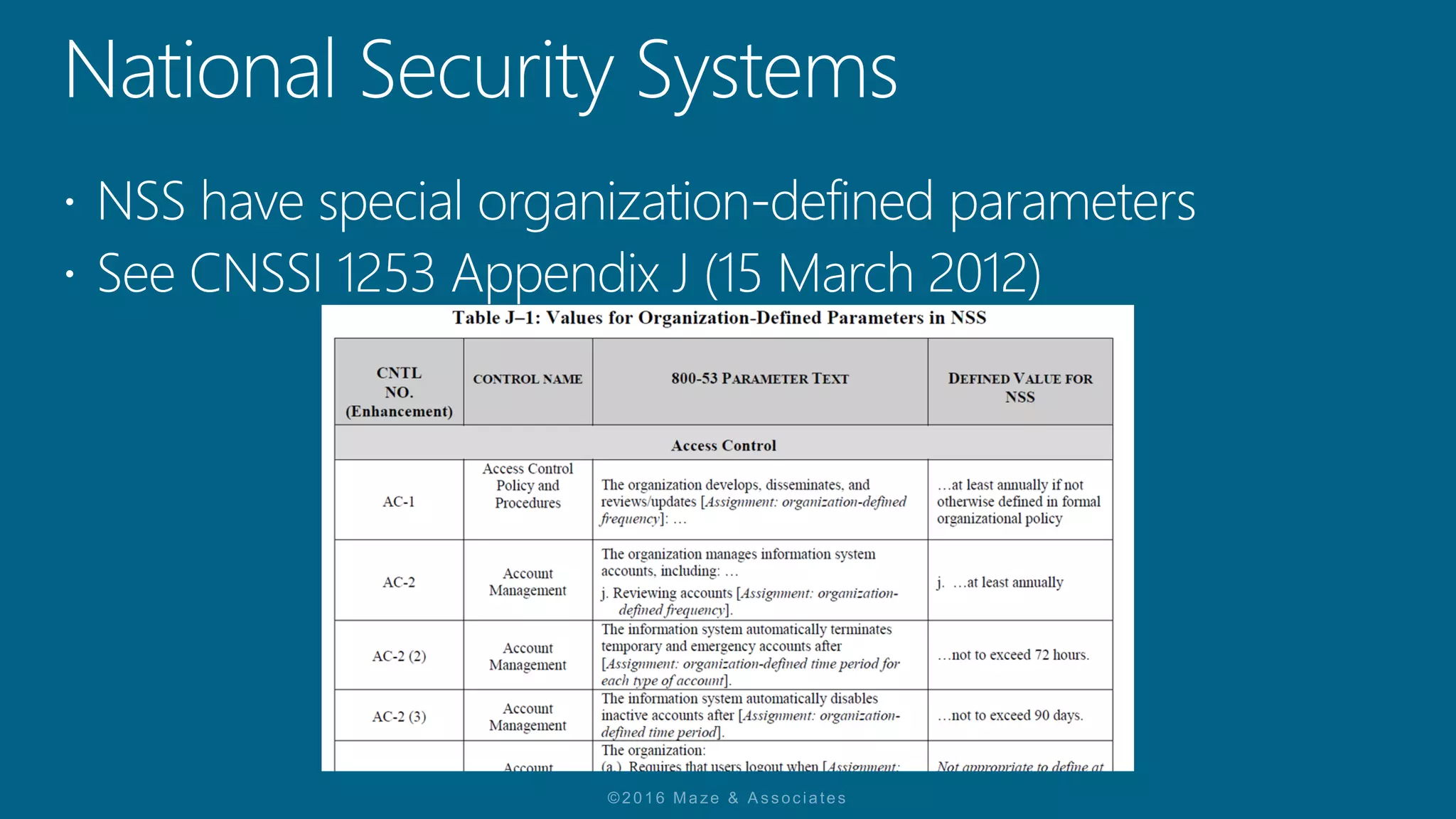



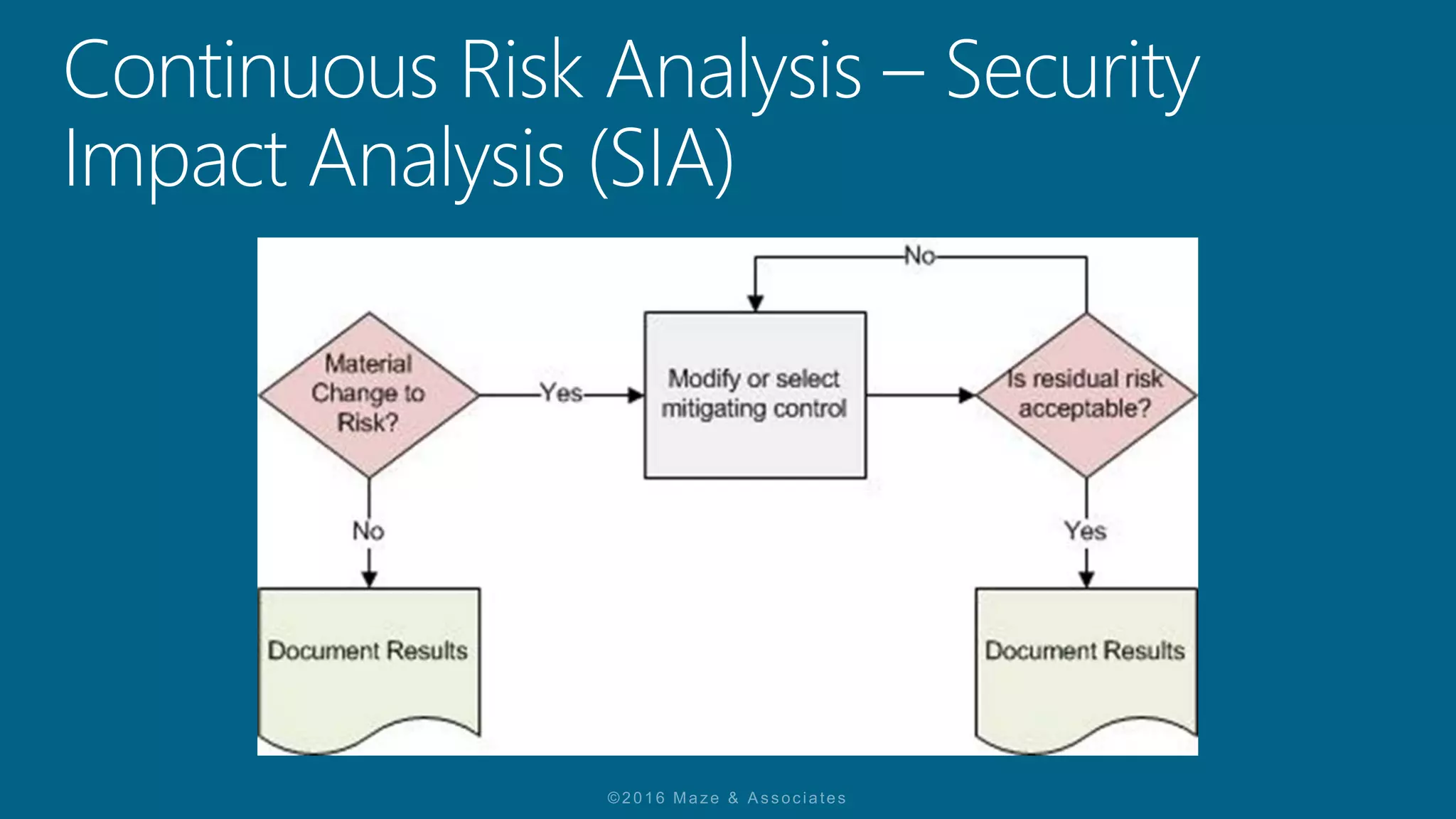


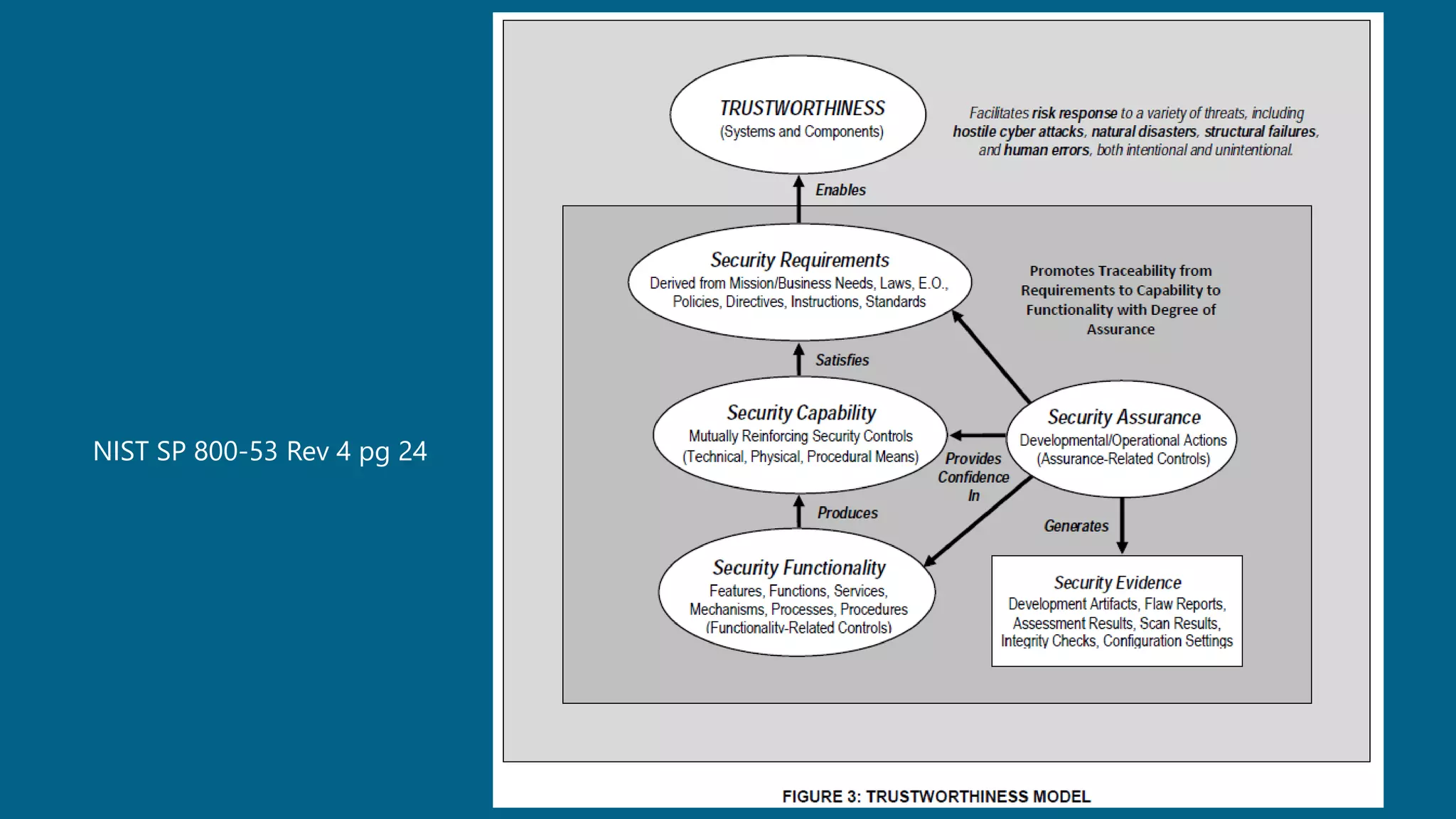

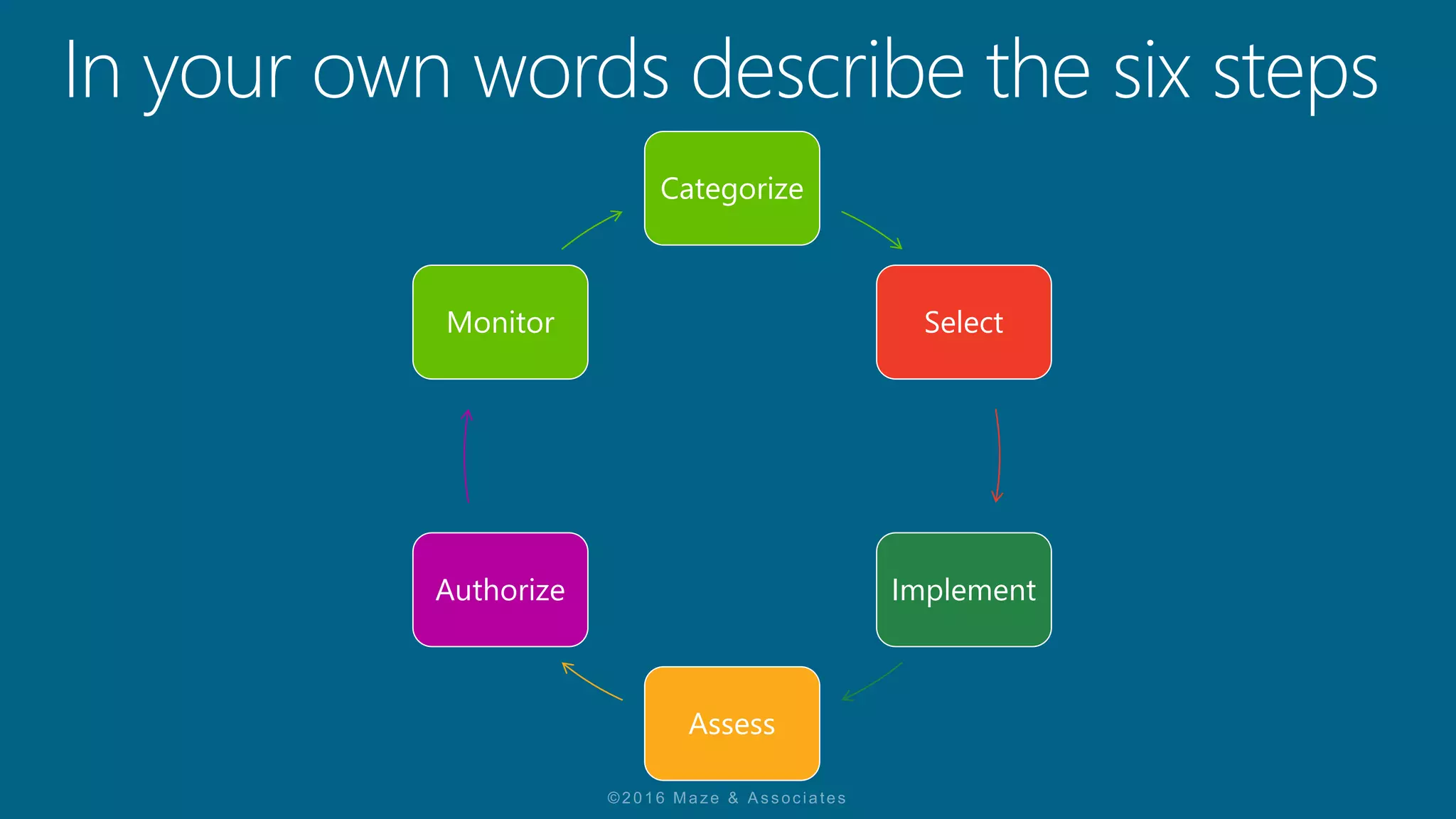
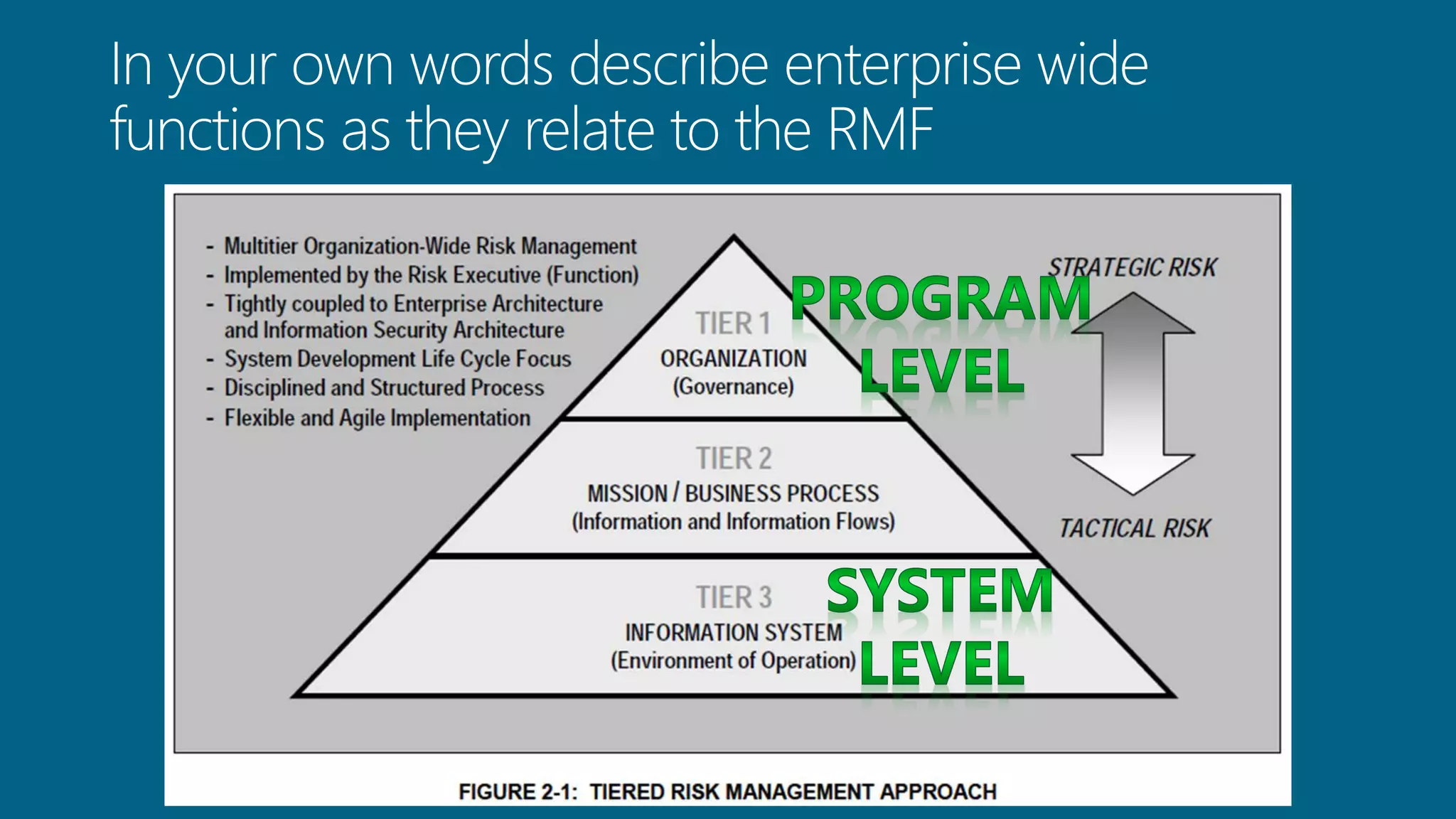
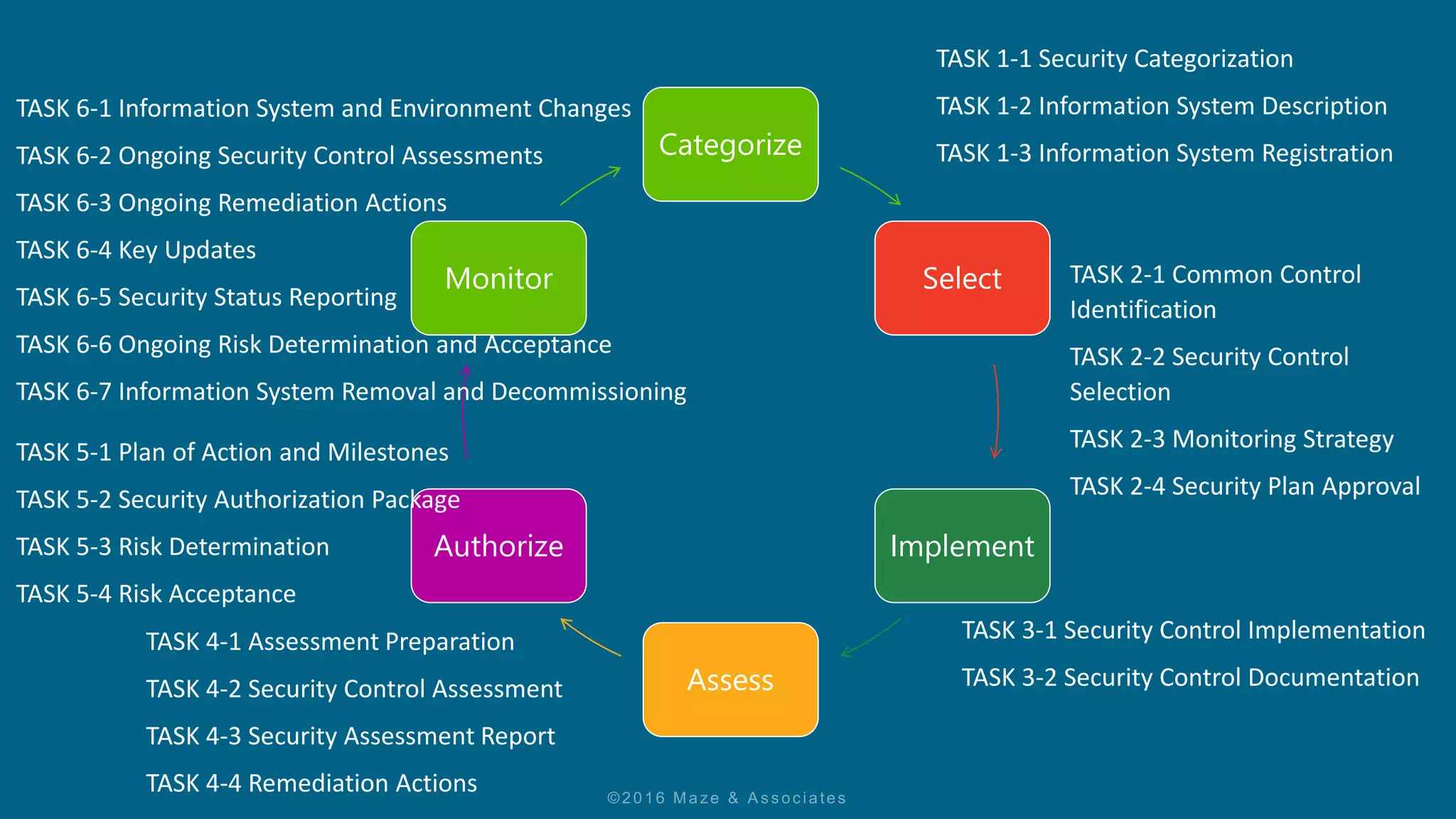

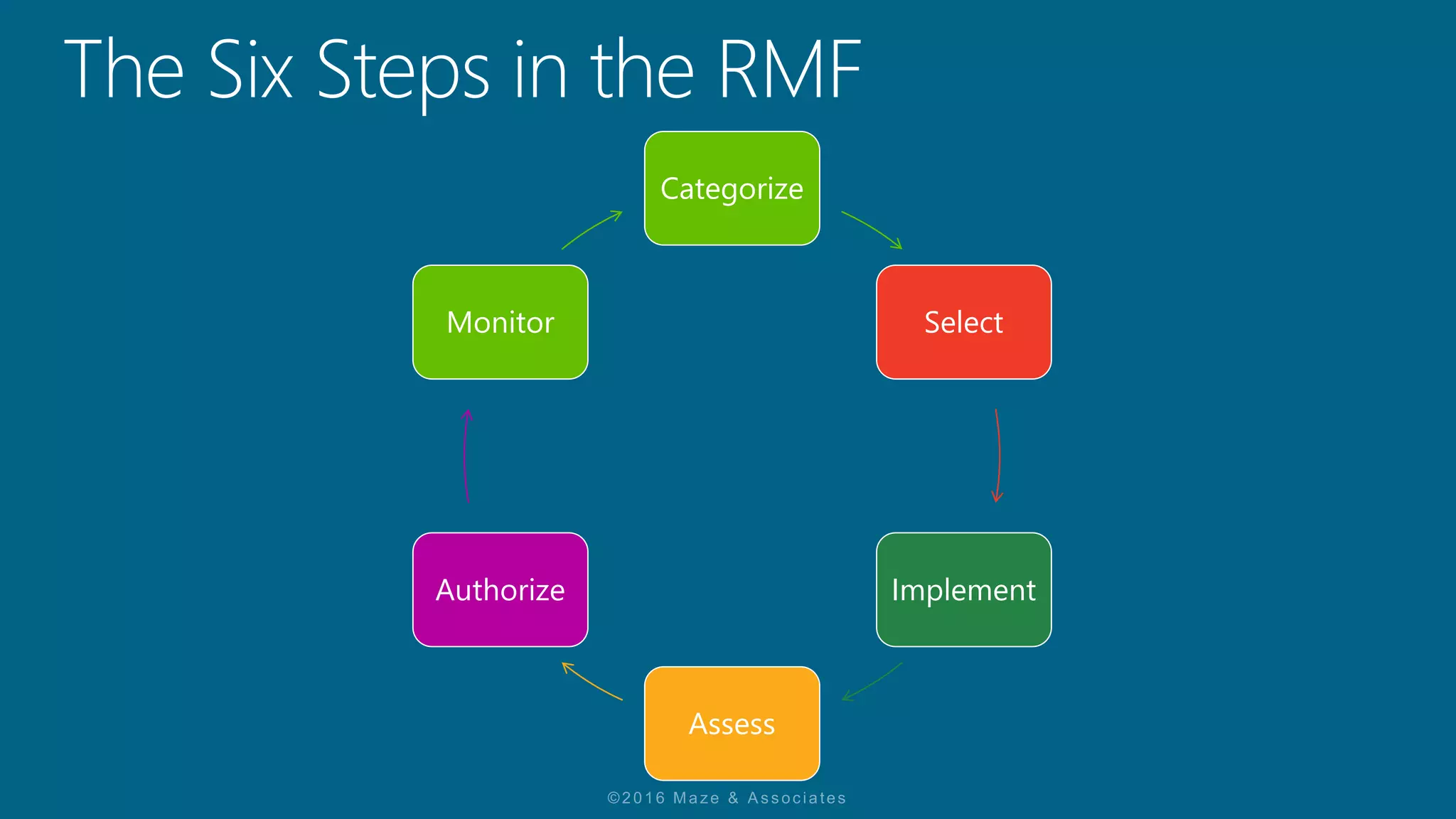
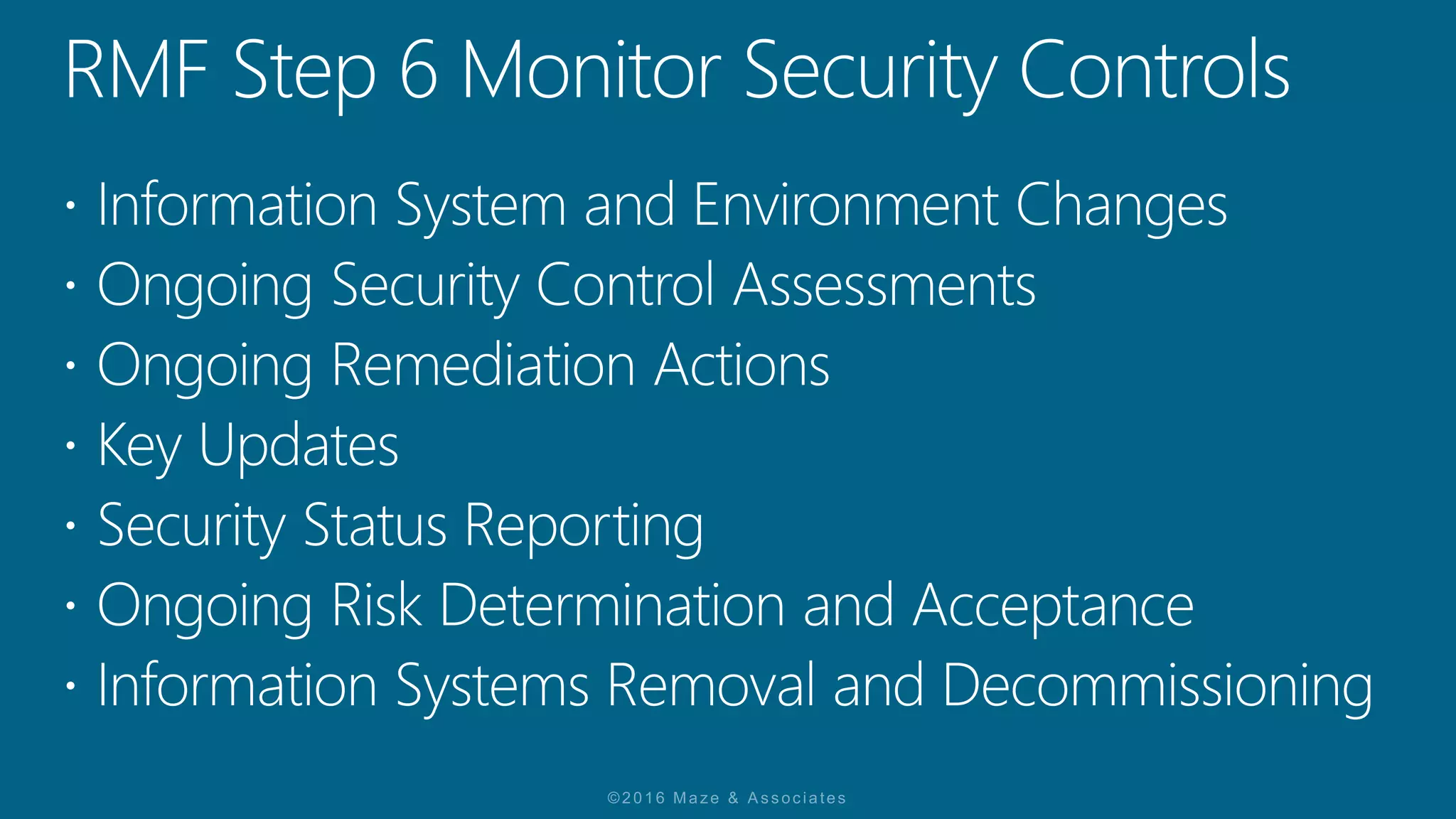
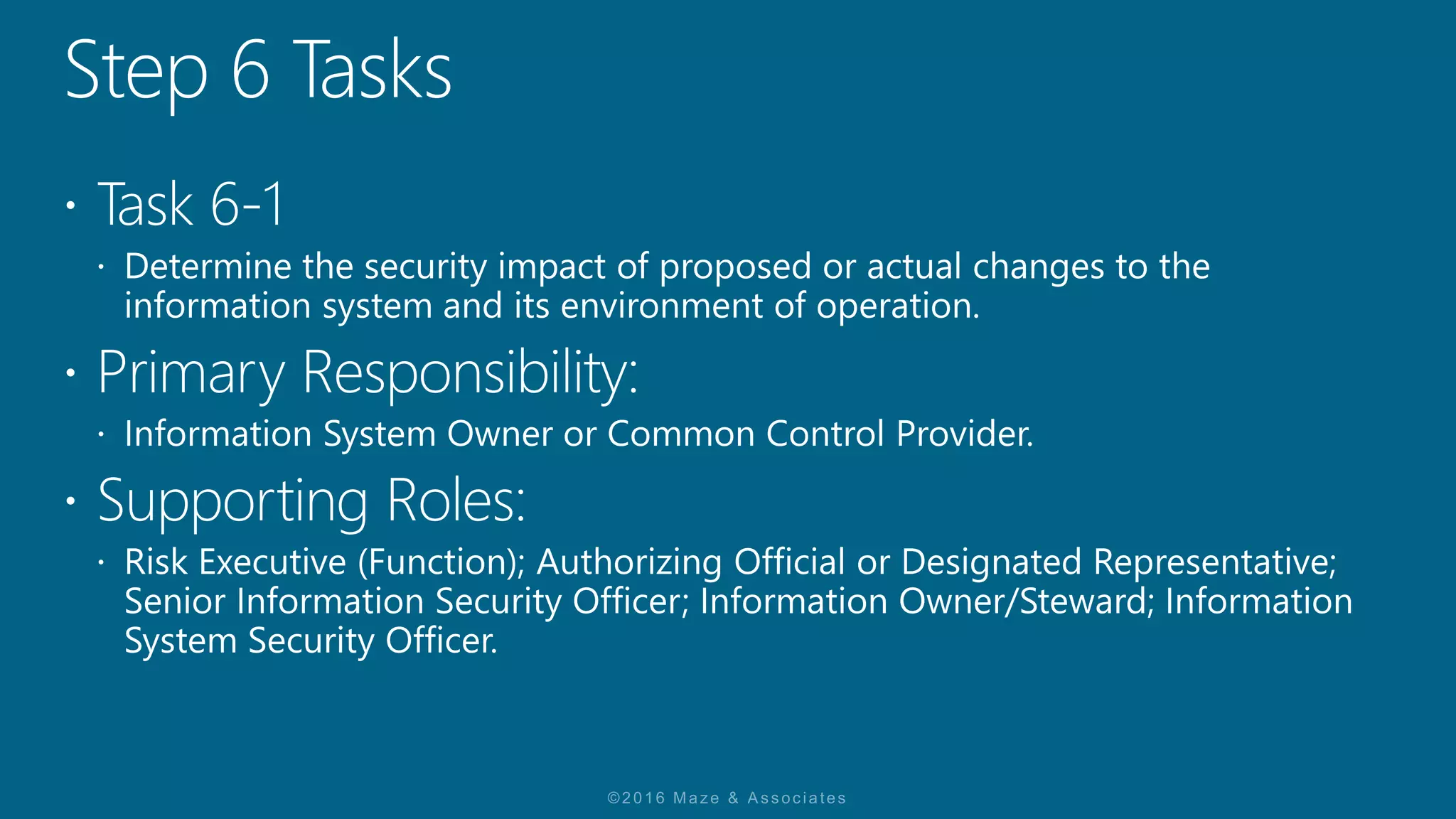
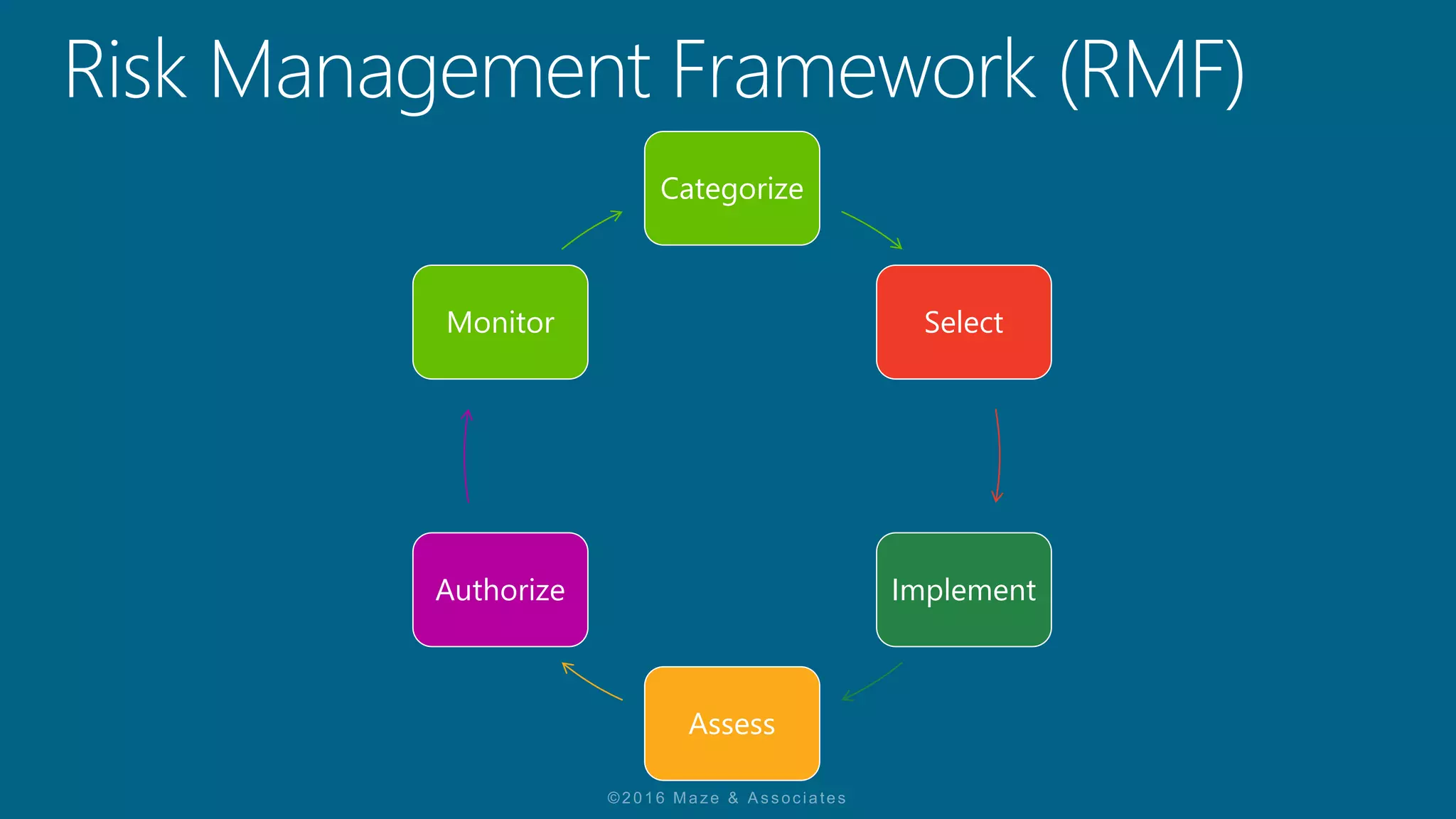
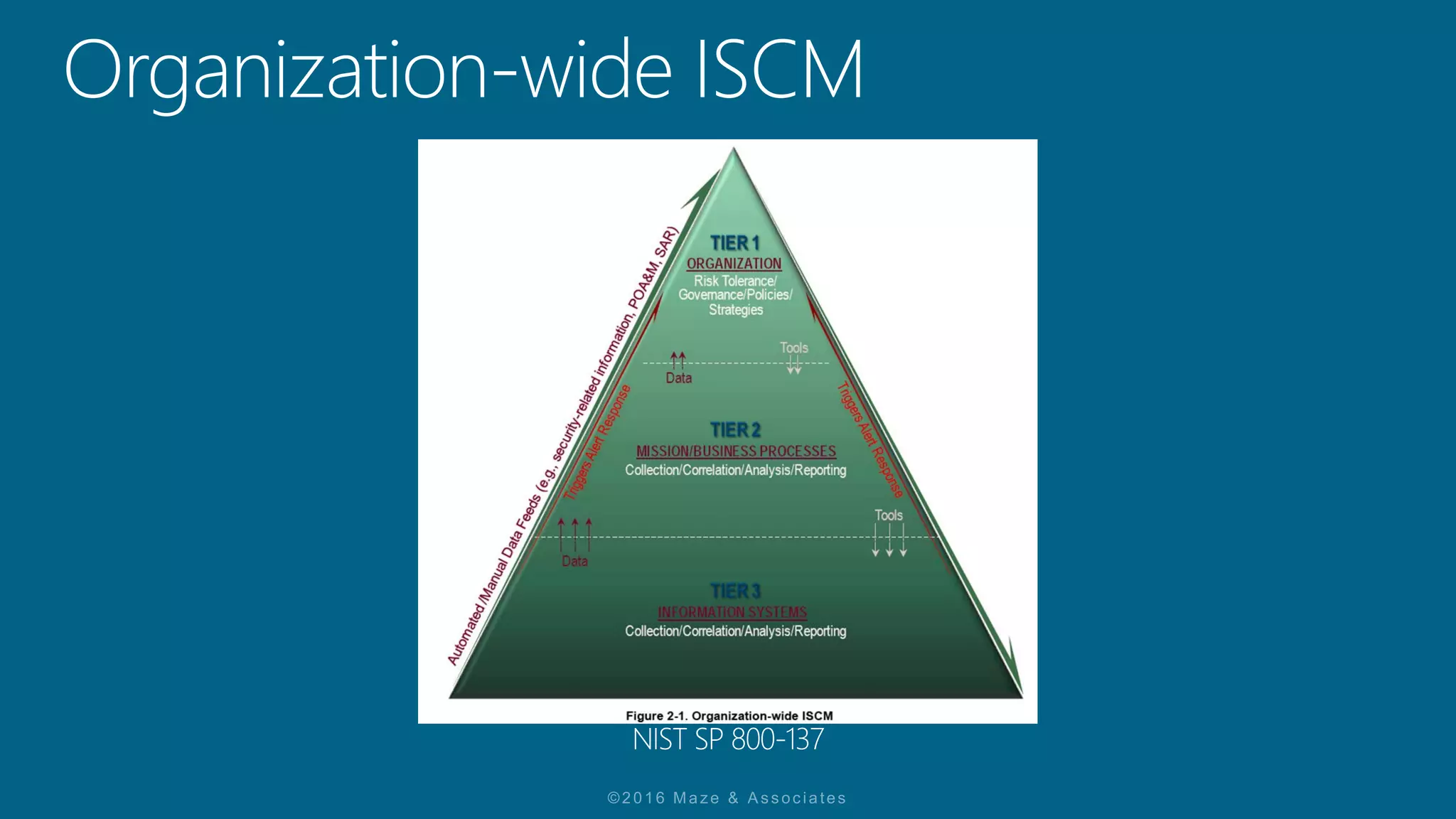
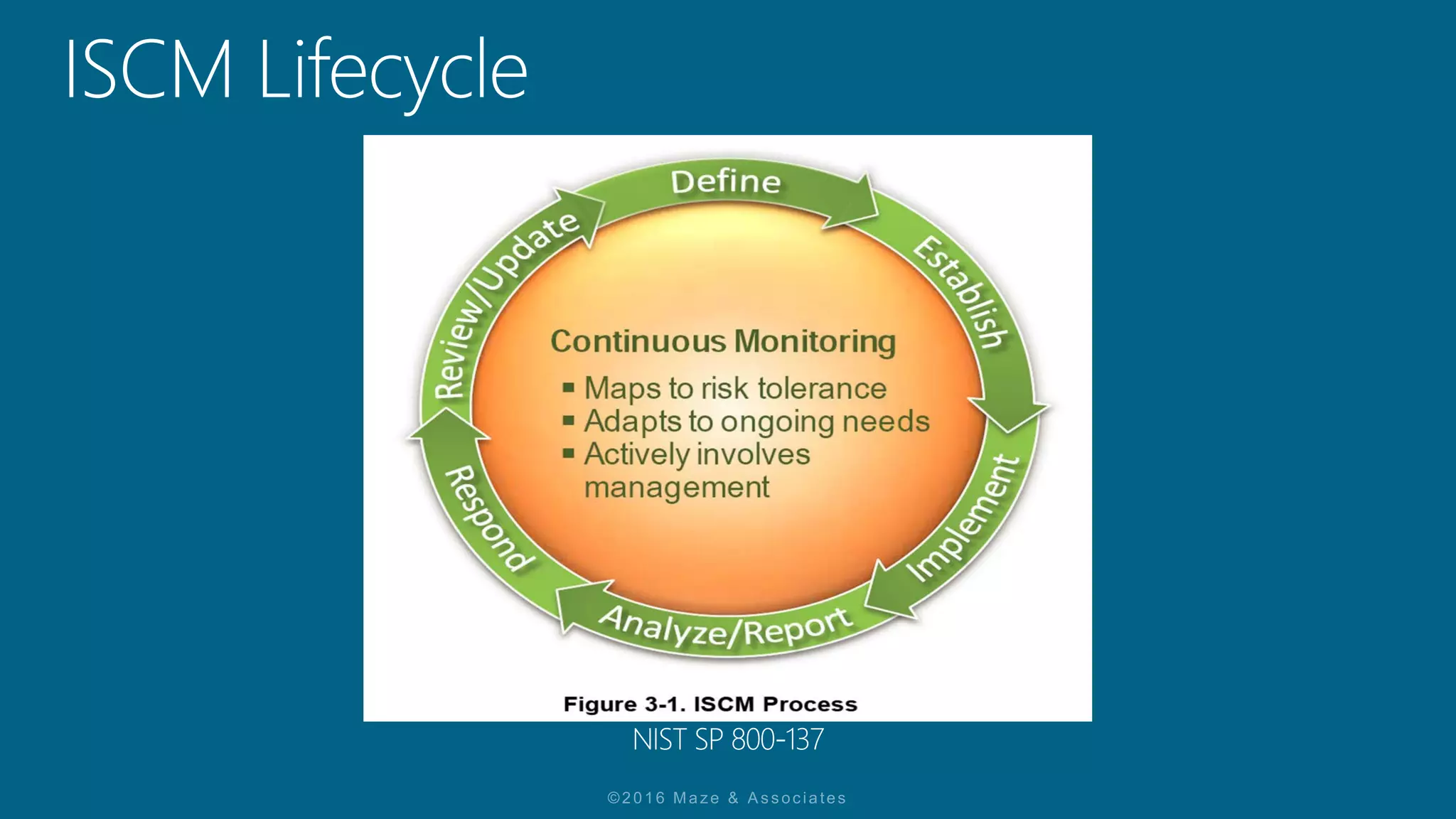
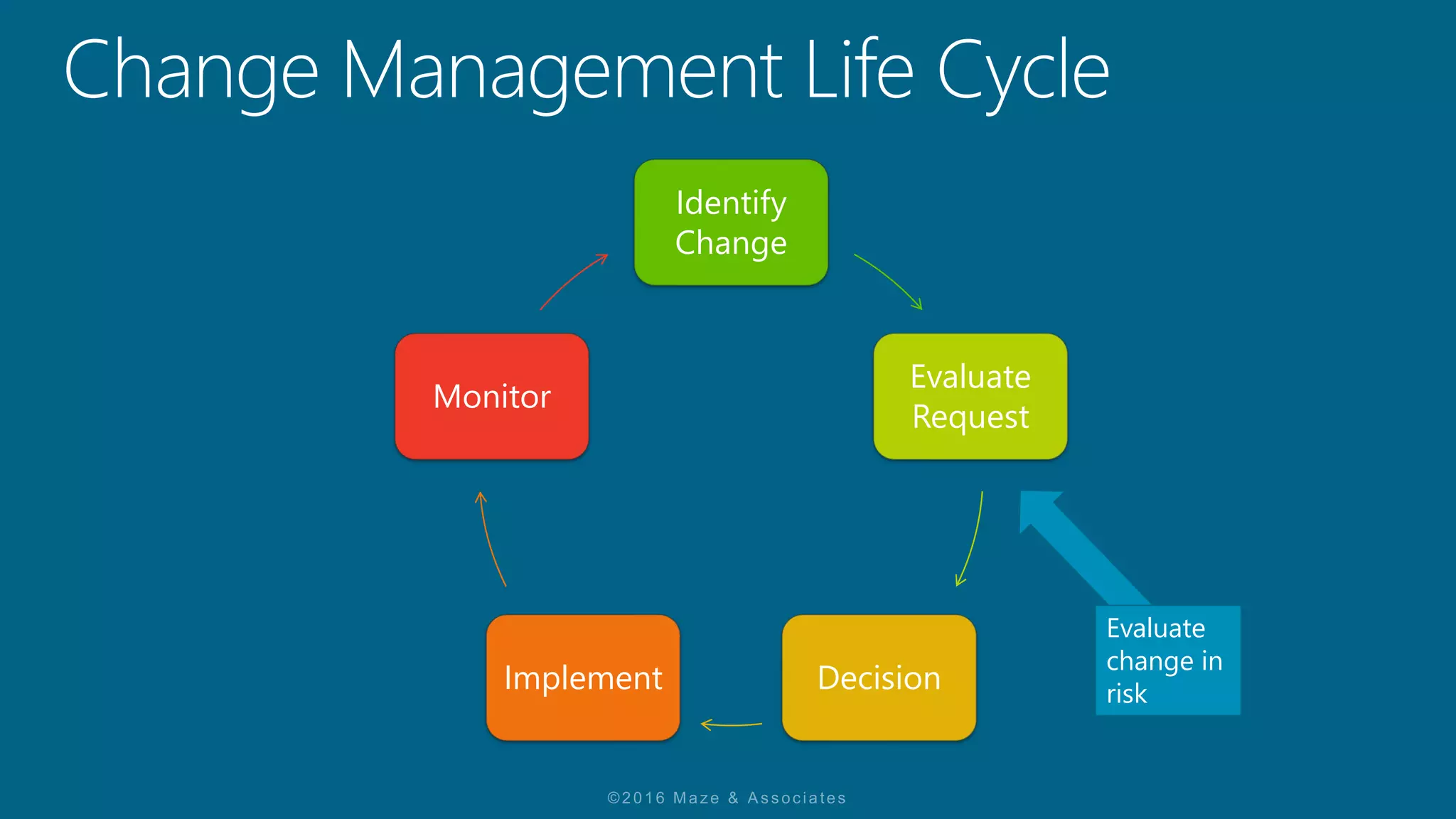
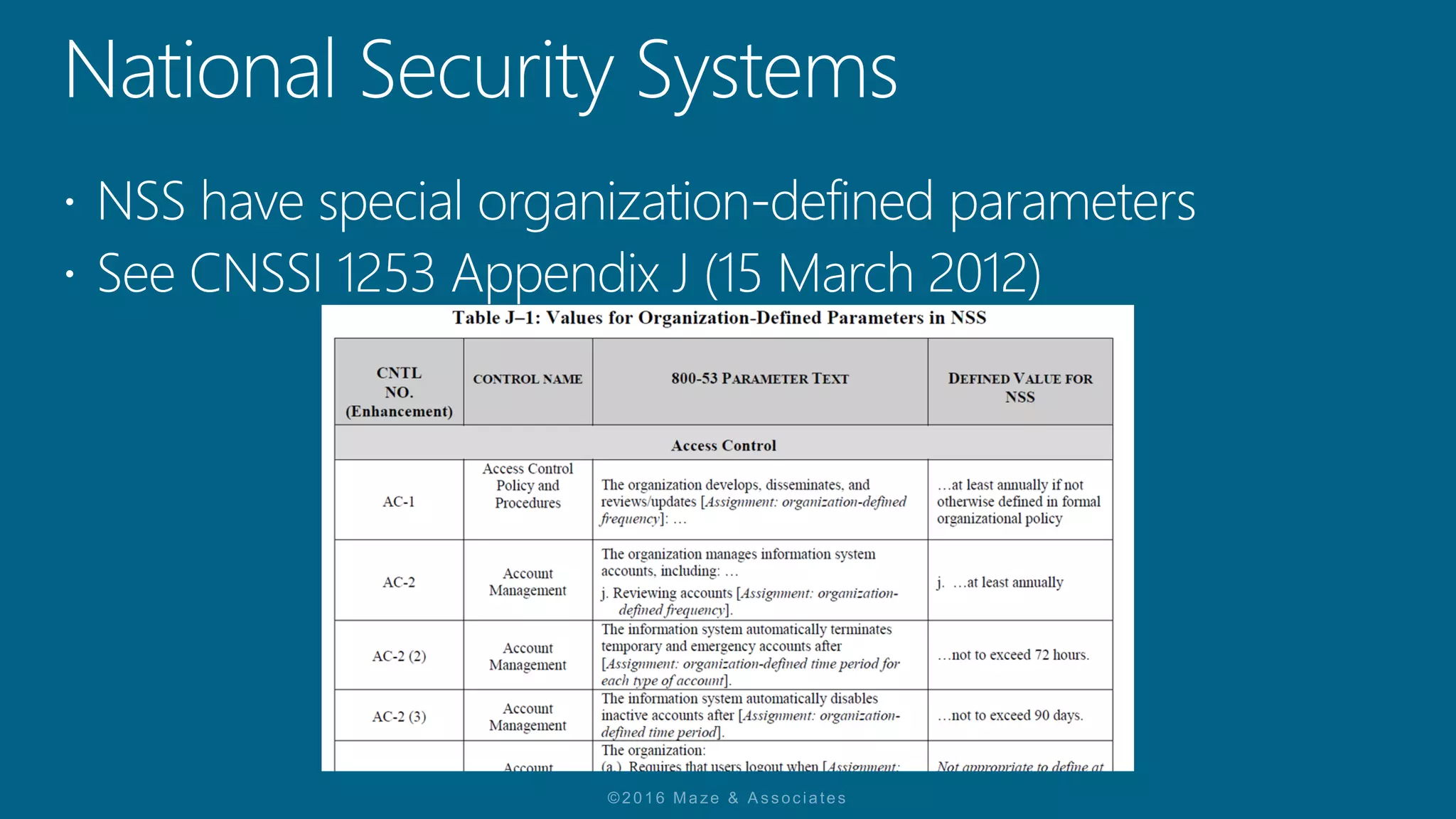
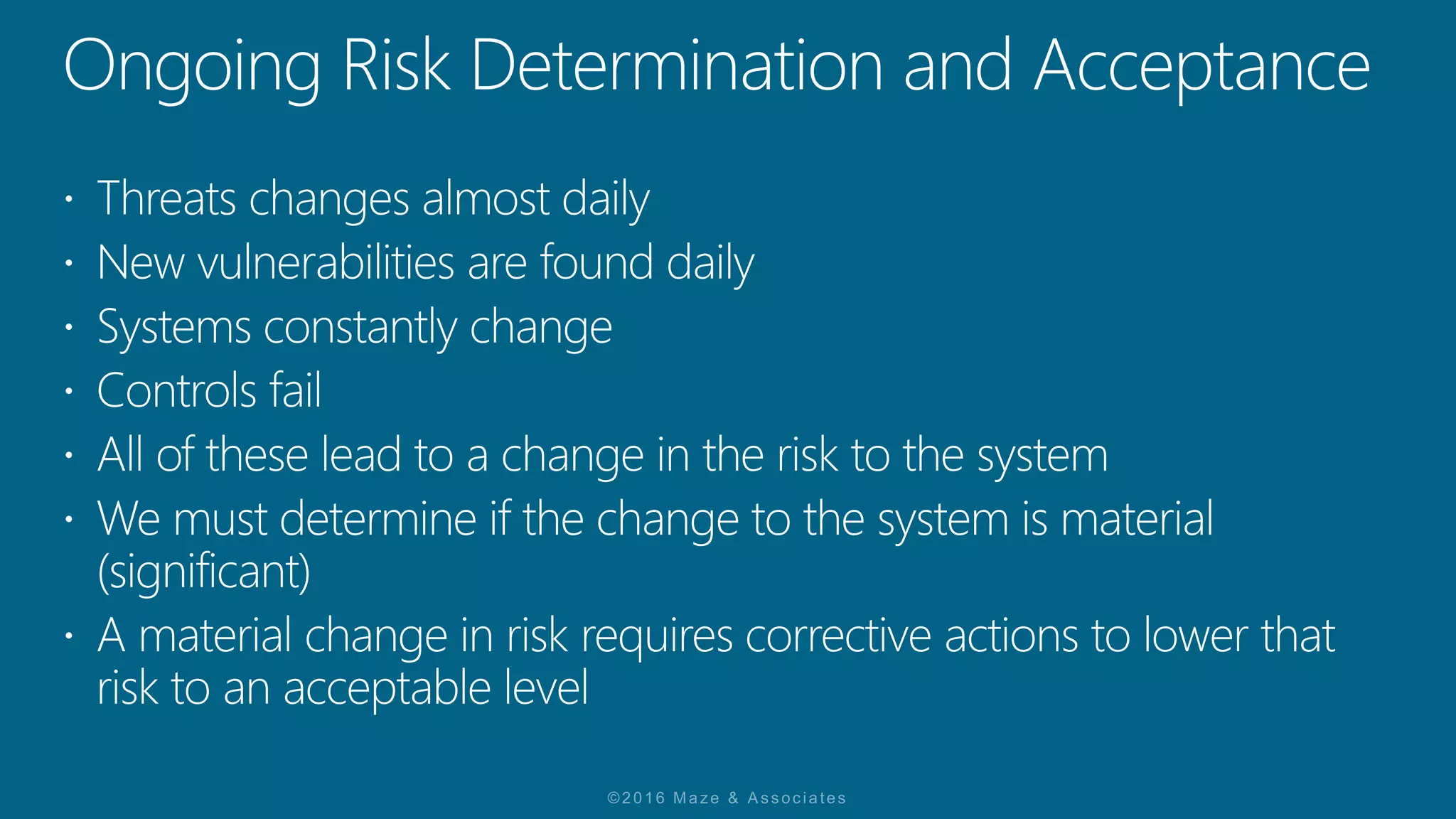
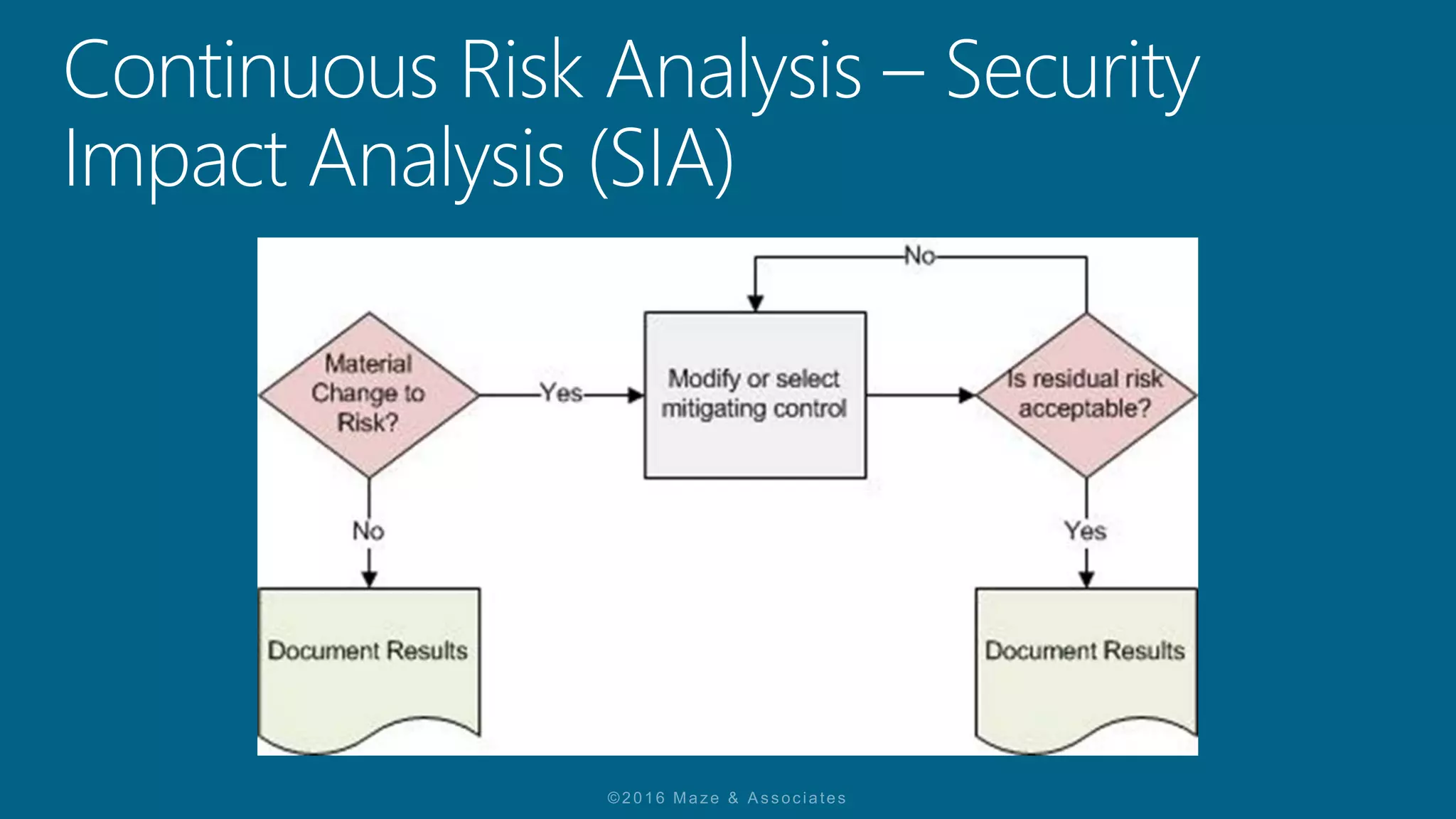
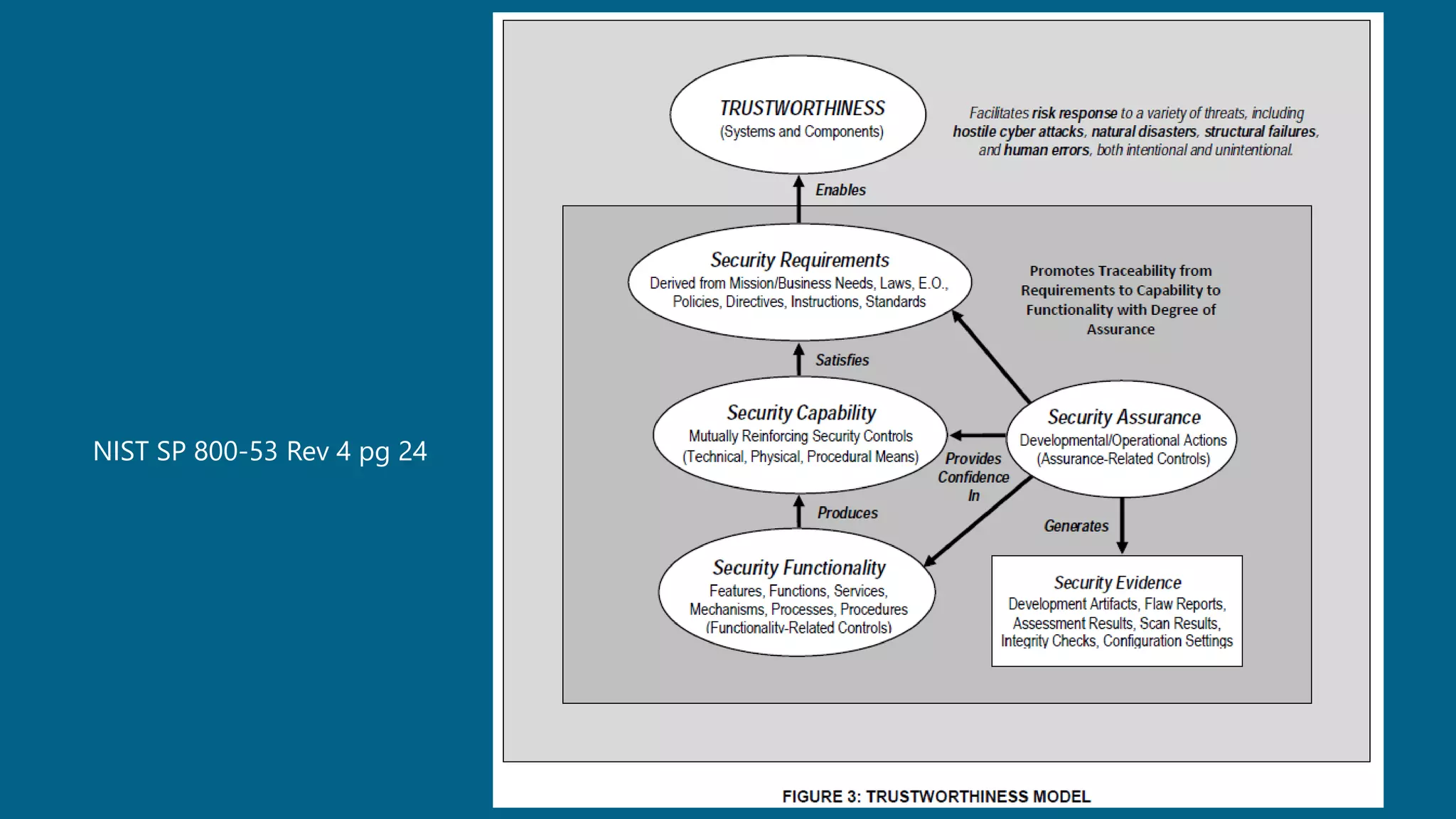
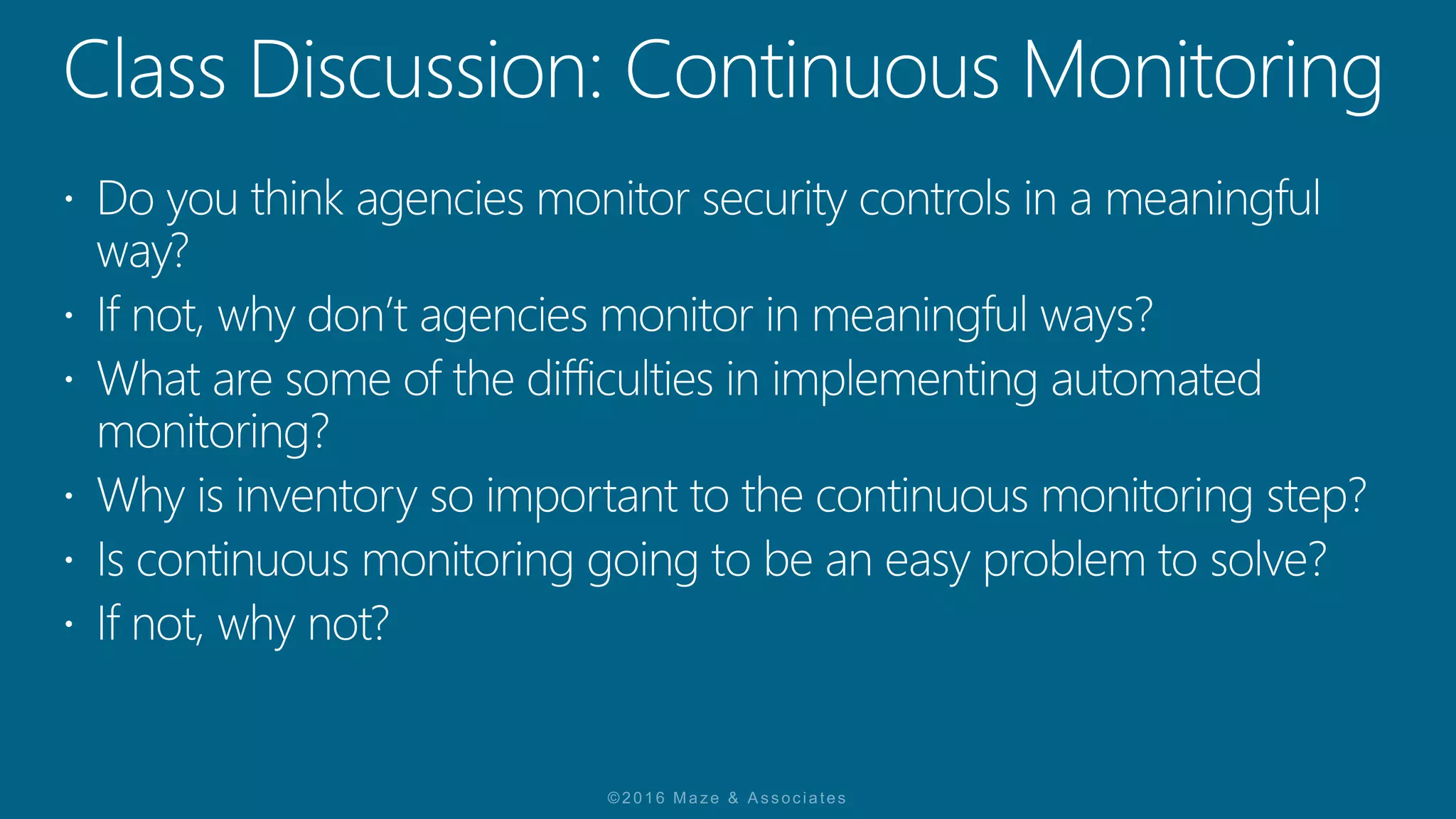
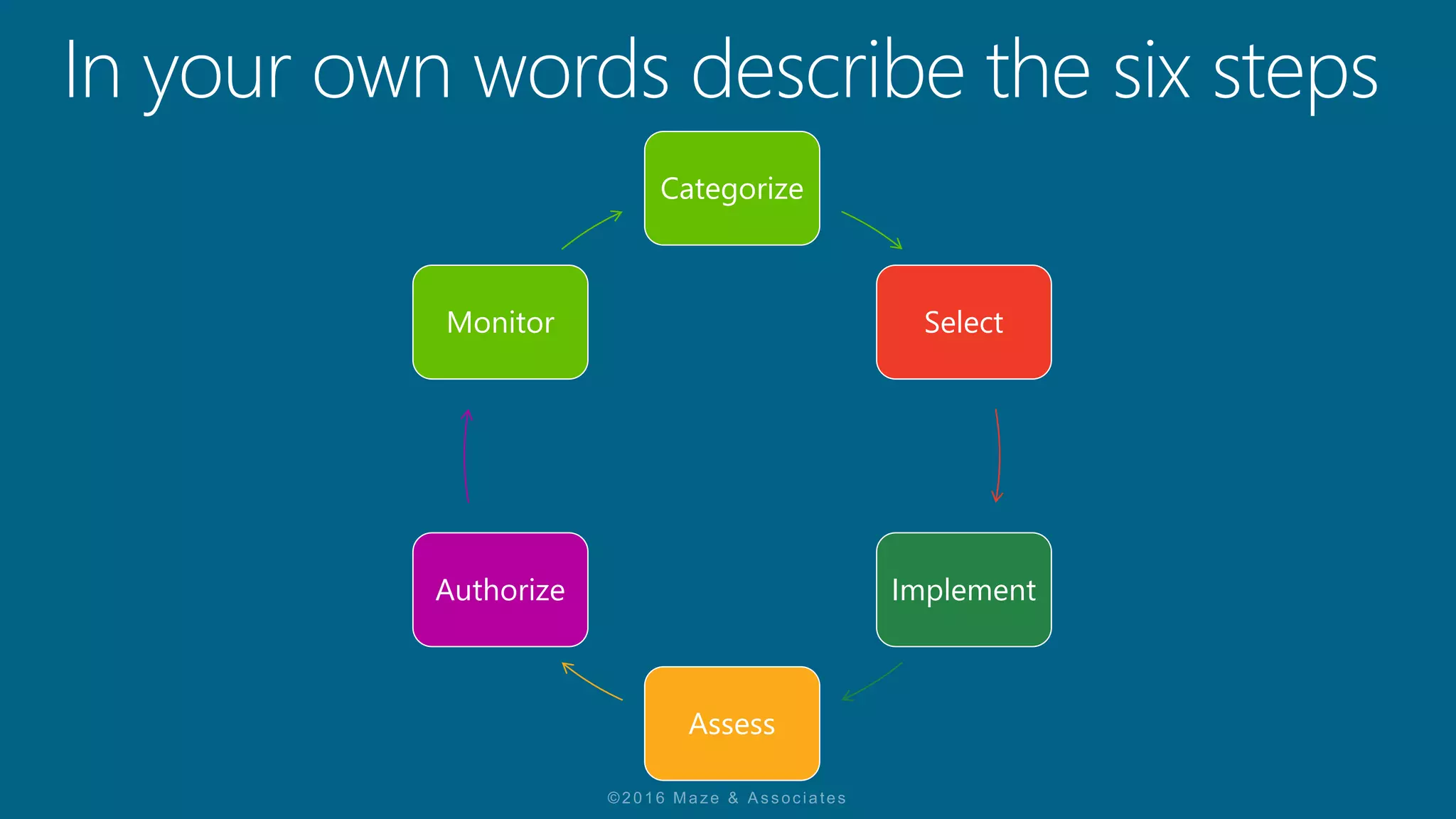
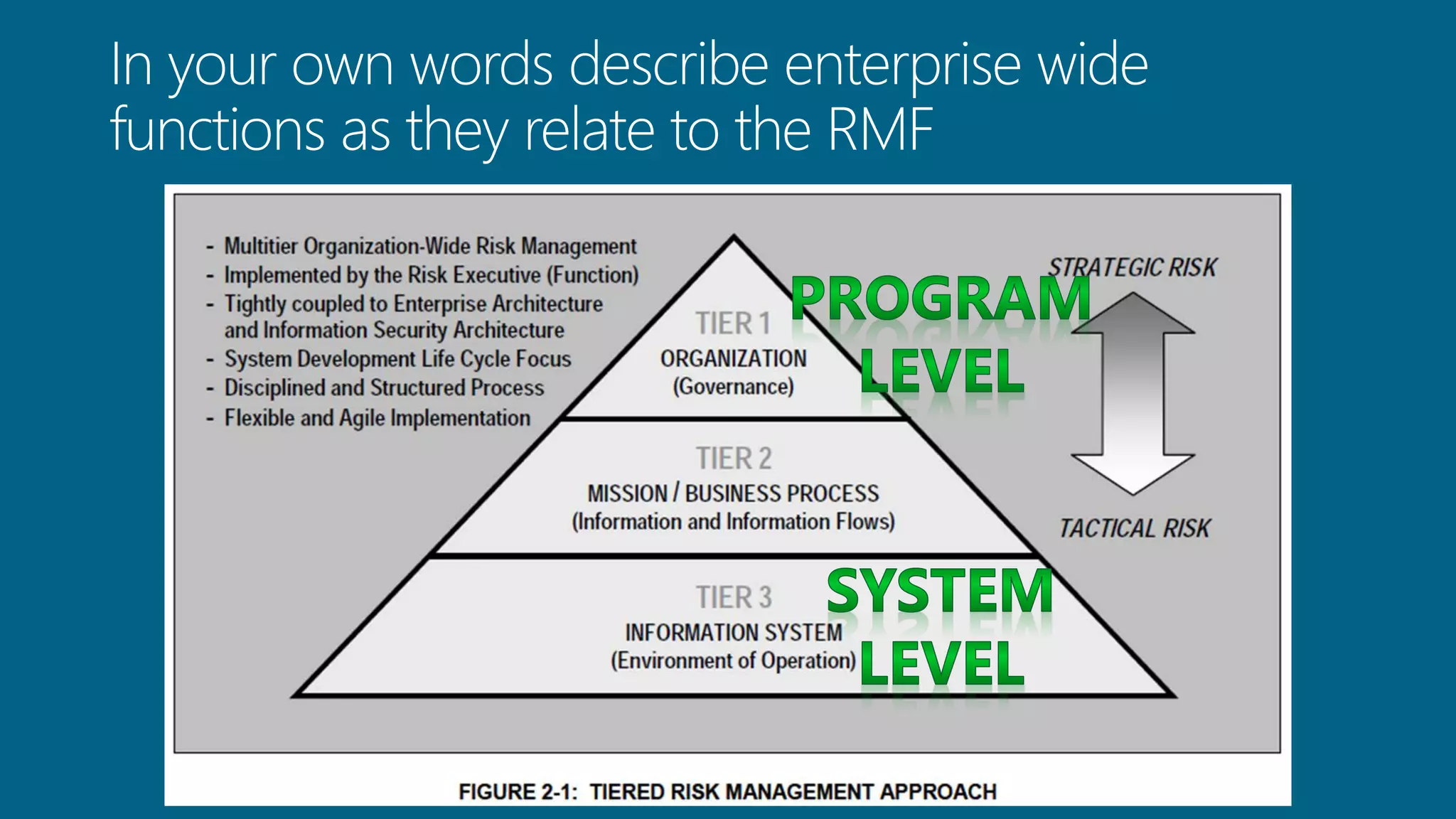
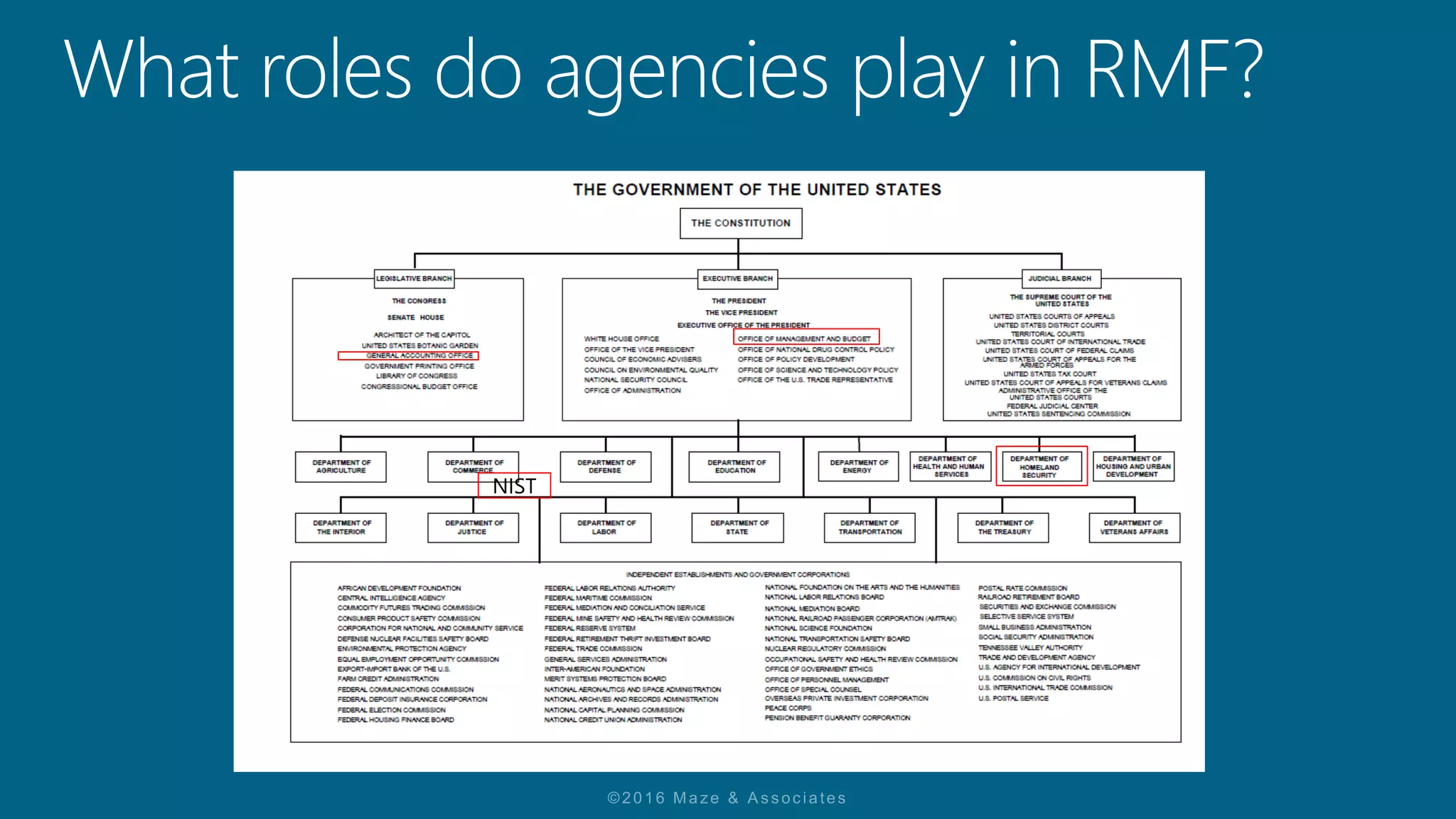
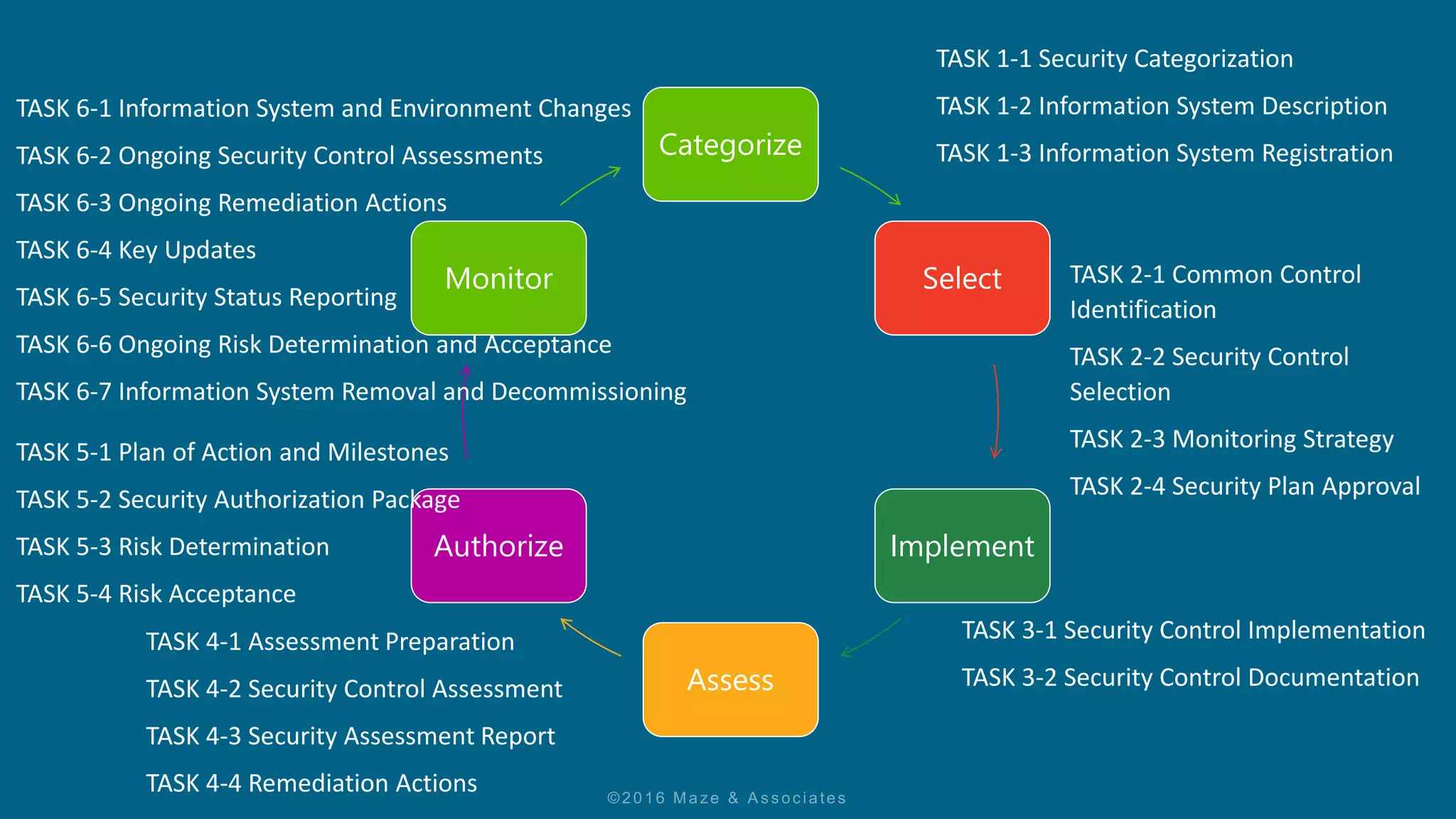
The document discusses the Risk Management Framework (RMF) process for authorizing information systems and maintaining ongoing security authorization. It outlines the six steps of the RMF process - Categorize, Select, Implement, Assess, Authorize, Monitor. The ultimate goal is to achieve ongoing authorization where the authorizing official has sufficient knowledge of the system's security state to determine if continued operation is acceptable based on ongoing risk assessments. Any changes to the system may change the risk, and the RMF process includes tasks for evaluating changes and their impact on risk.