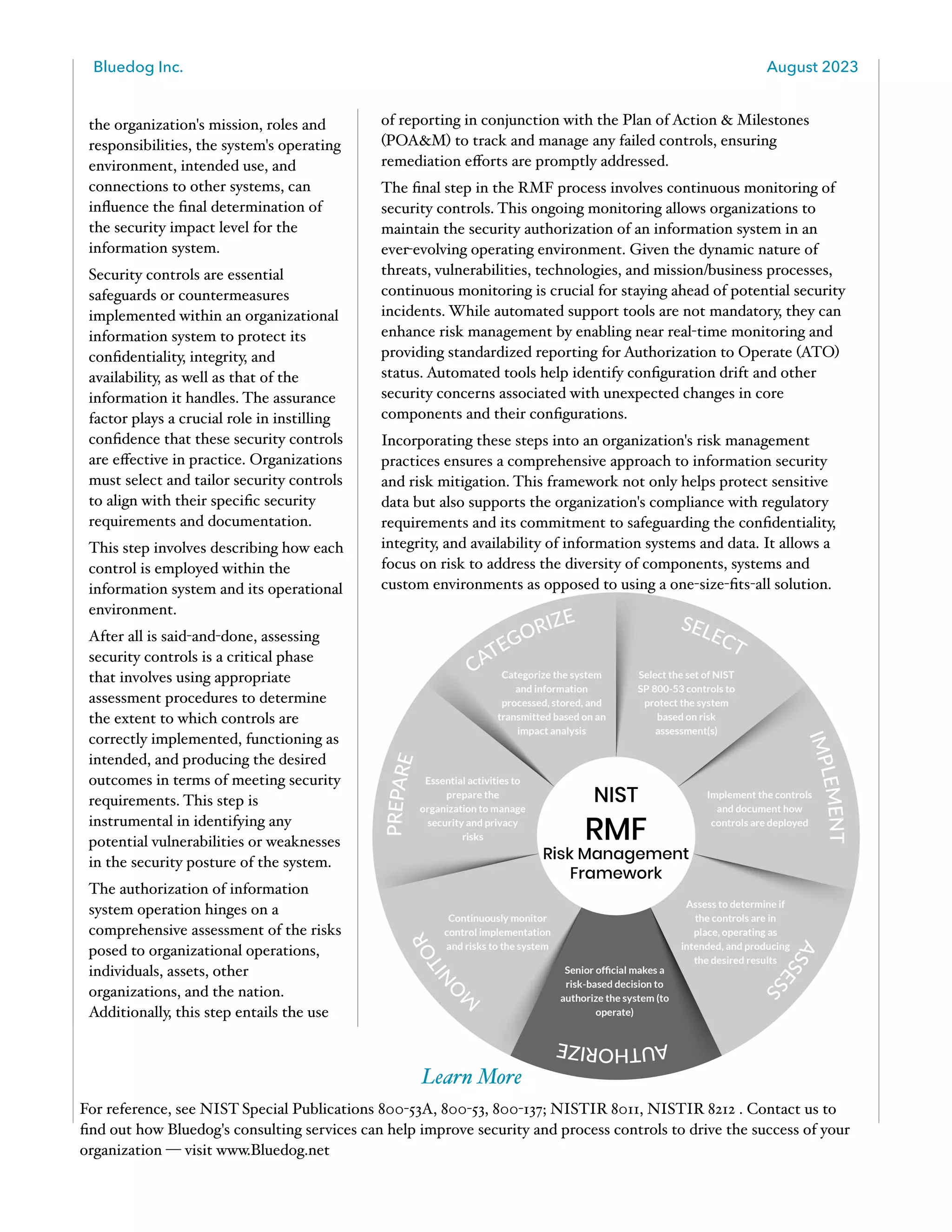
The Risk Management Framework (RMF) is a critical component of information security management linked to NIST's SP 800-37 guide, designed to enhance the management of electronic government services through a seven-step process. RMF Revision 2 introduces an integrated approach to managing both privacy and security risks, with a new 'prepare' step aimed at optimizing resource allocation and prioritizing security activities. The framework emphasizes continuous monitoring and tailored security controls to maintain compliance and protect data confidentiality, integrity, and availability across federal agencies.