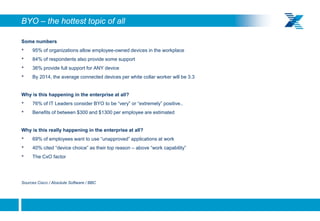
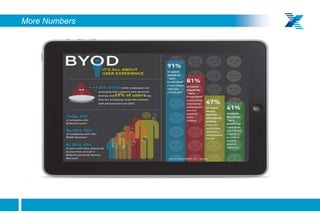
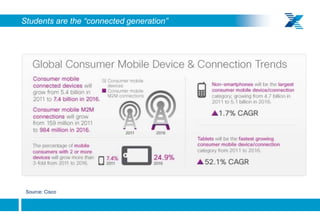
This document discusses how higher education institutions have led the way in addressing emerging IT issues like BYOD, cloud computing, big data, and mobility with limited budgets. It provides examples of how universities have supported a wide variety of student-owned devices and driven innovation through large research projects involving collaboration and data sharing. The document suggests enterprises can learn lessons from higher education's experiences in areas like policy, productivity focus, multi-tenancy infrastructure sharing, and driving technology innovation through ambitious projects.