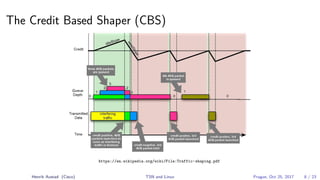
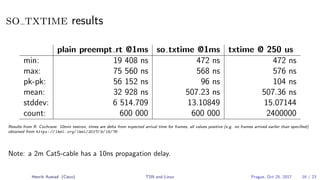
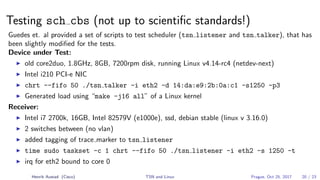
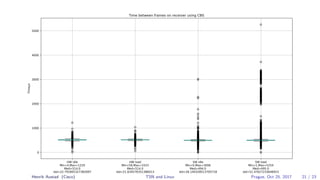
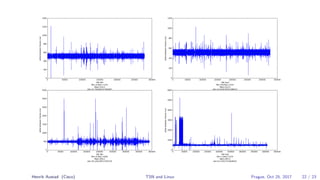
Henrik Austad's presentation discusses the challenges of implementing deterministic networking for real-time systems using Time-Sensitive Networking (TSN) and Deterministic Networking (DetNet). The document highlights critical issues such as stringent timing requirements, reliability in packet-switched networks, and the need for improved support in Linux for TSN technologies. Additionally, it covers advancements in hardware and software, including the time-triggered transmission approach and credit-based shapers, aimed at enhancing the performance of real-time applications over existing network infrastructures.