The document discusses various aspects of transport layer protocols:
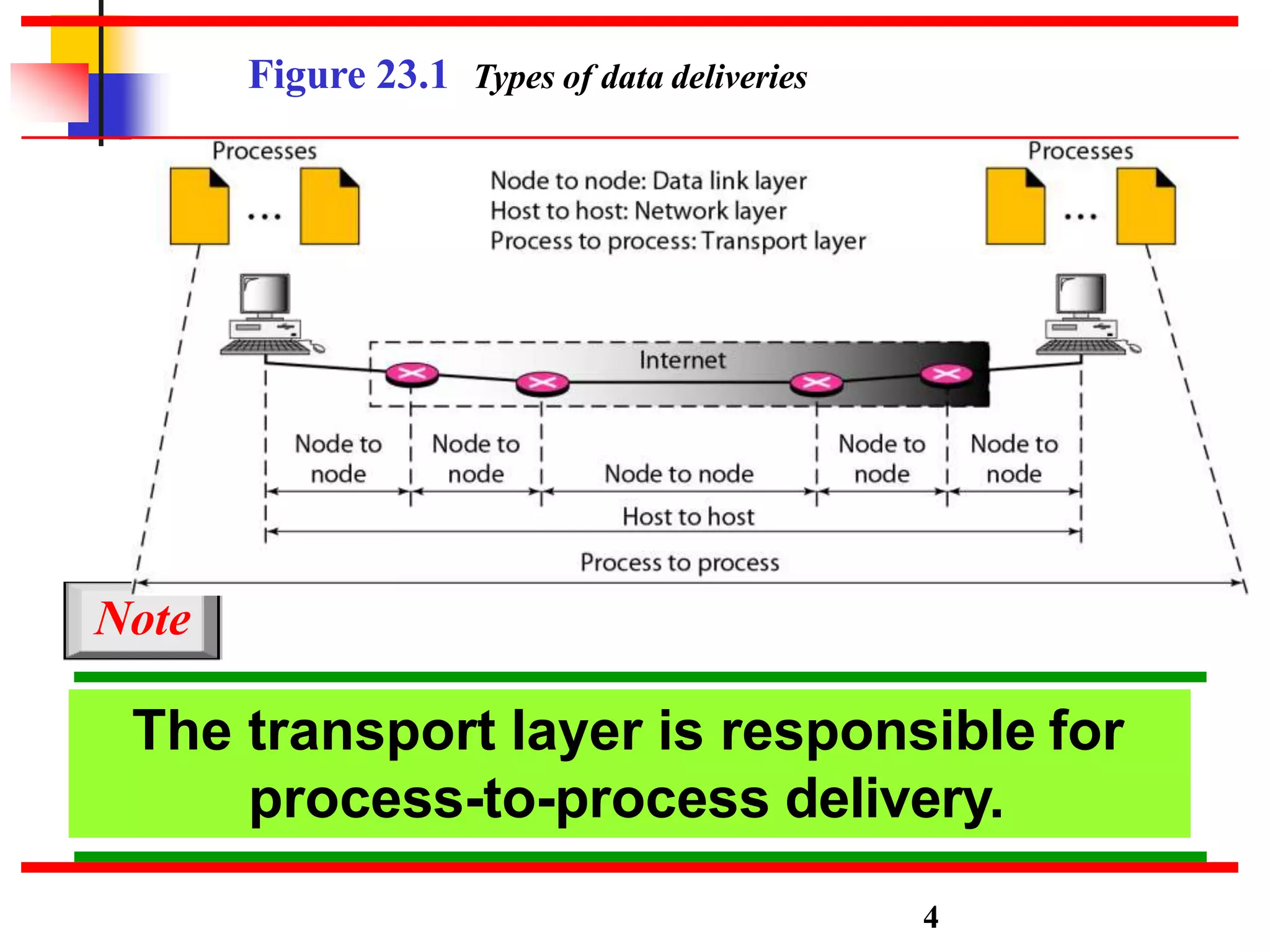
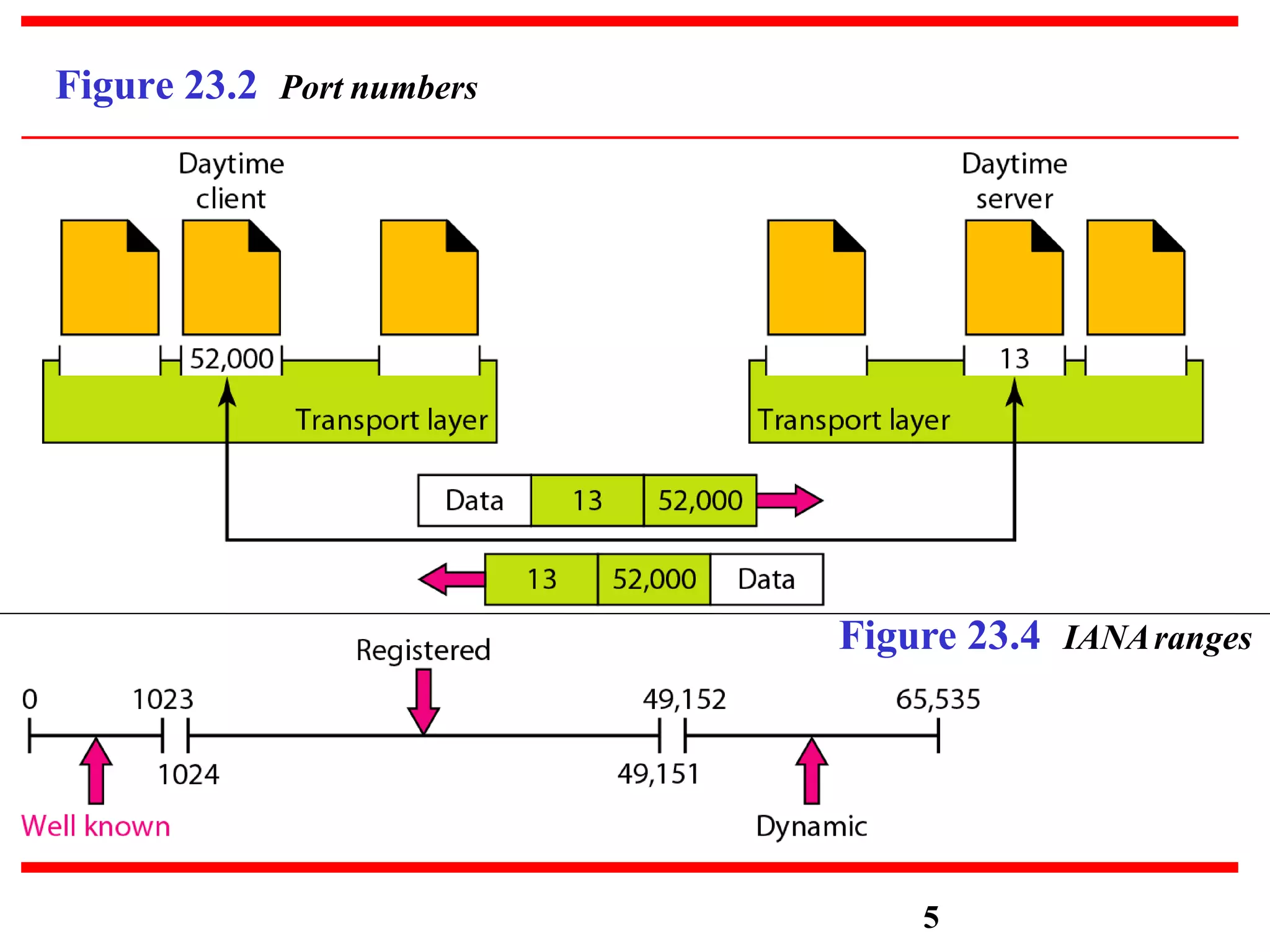
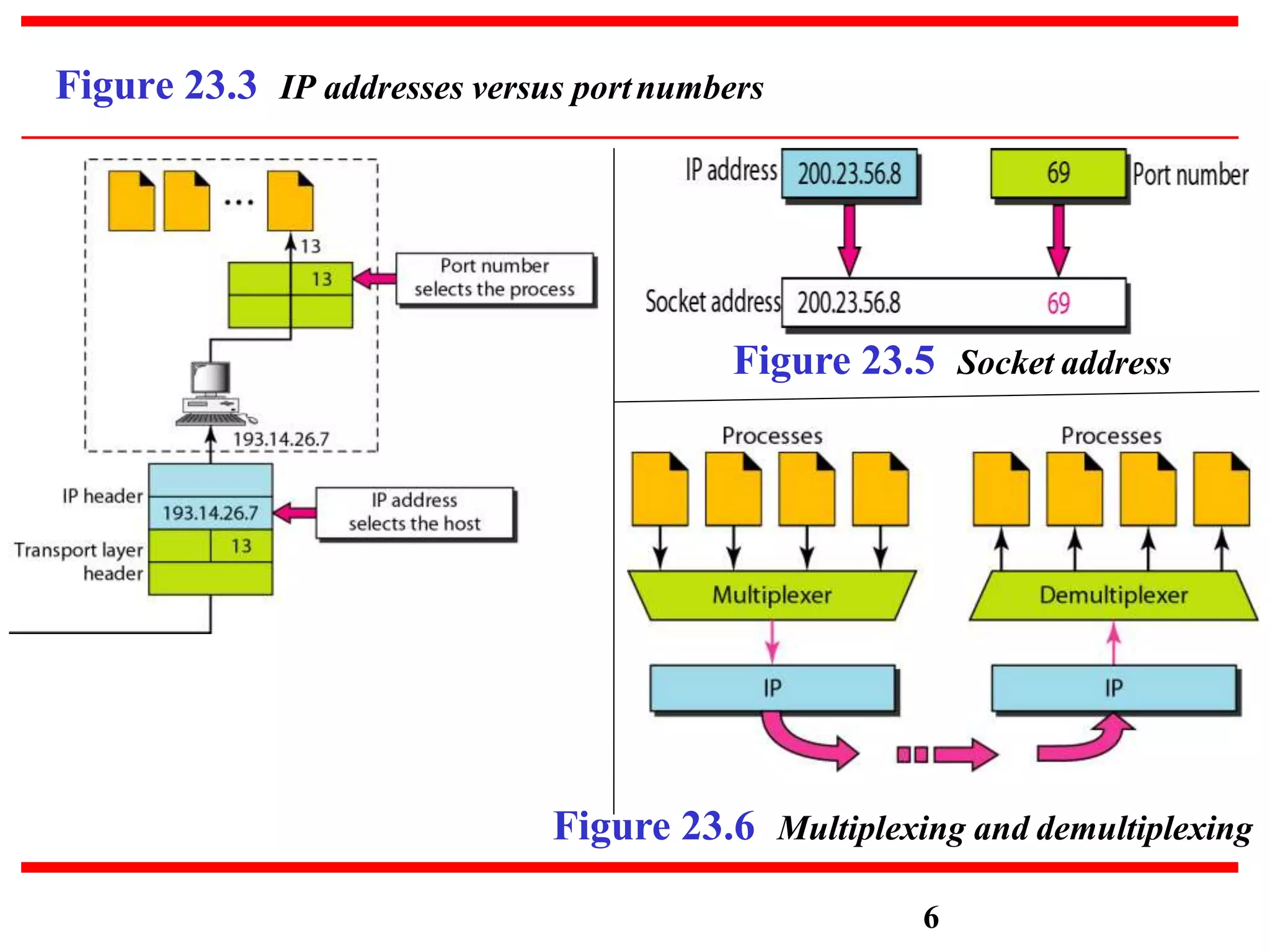
- It introduces the transport layer and its responsibility for process-to-process delivery between two communicating processes.
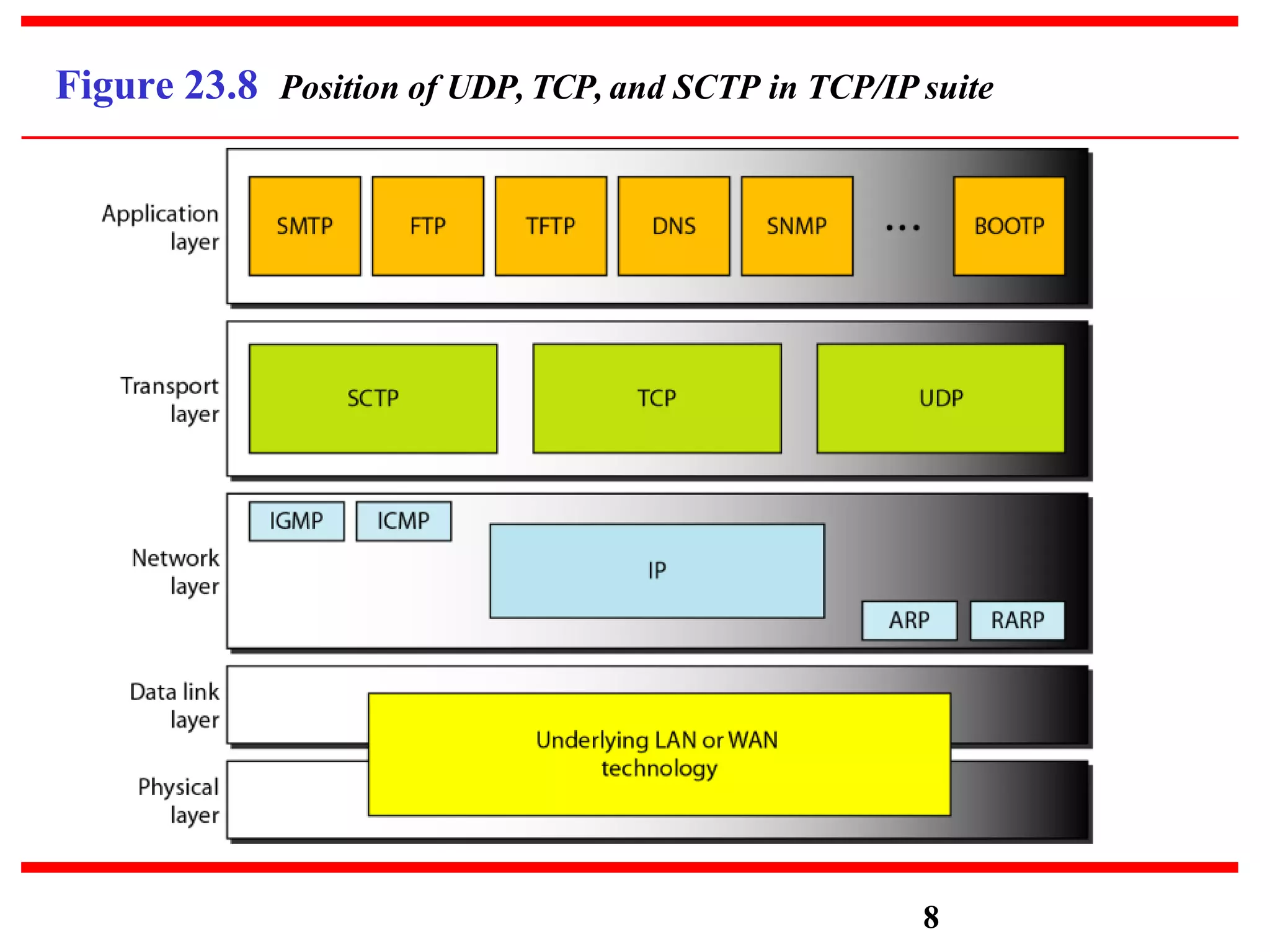
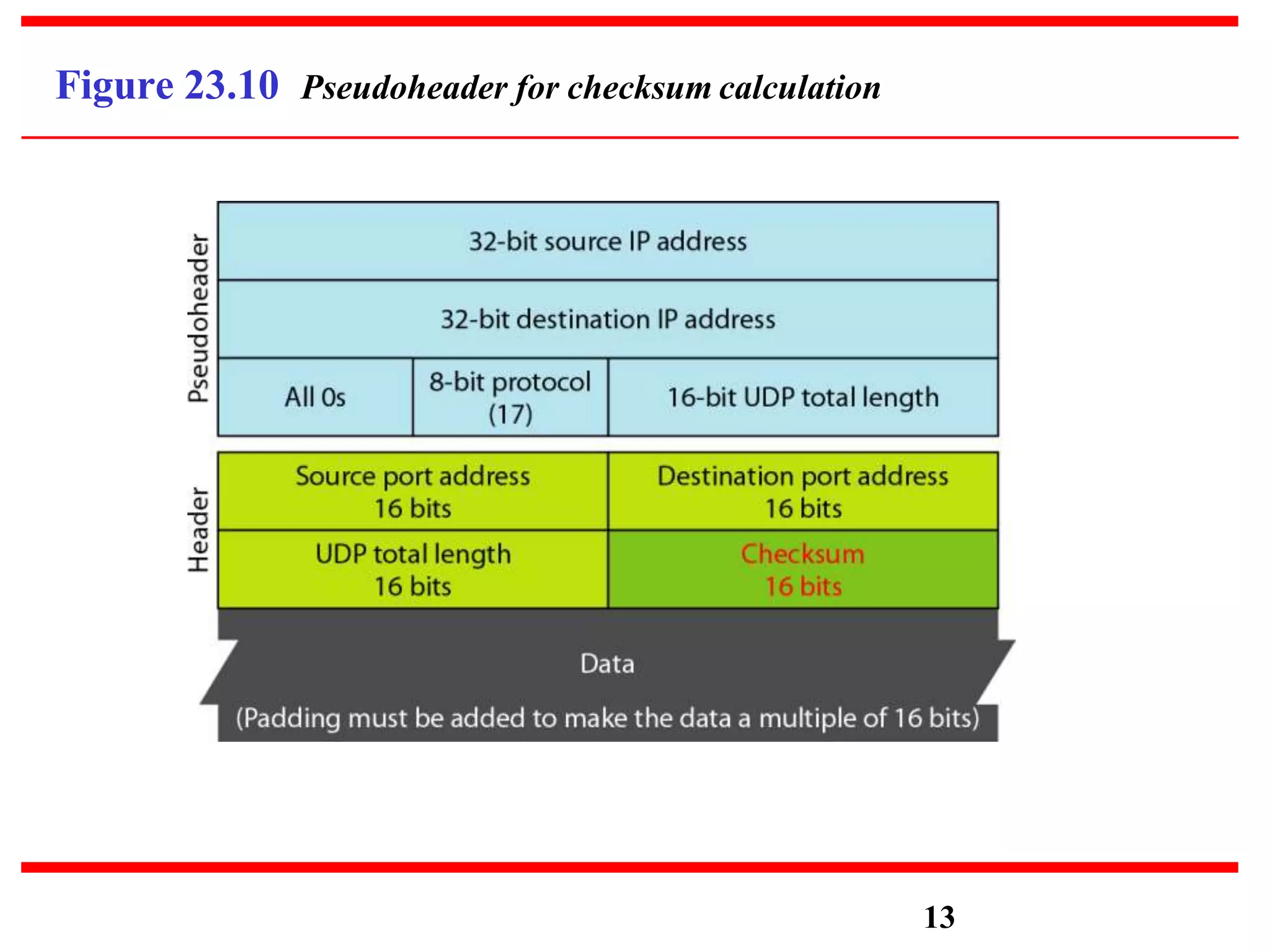
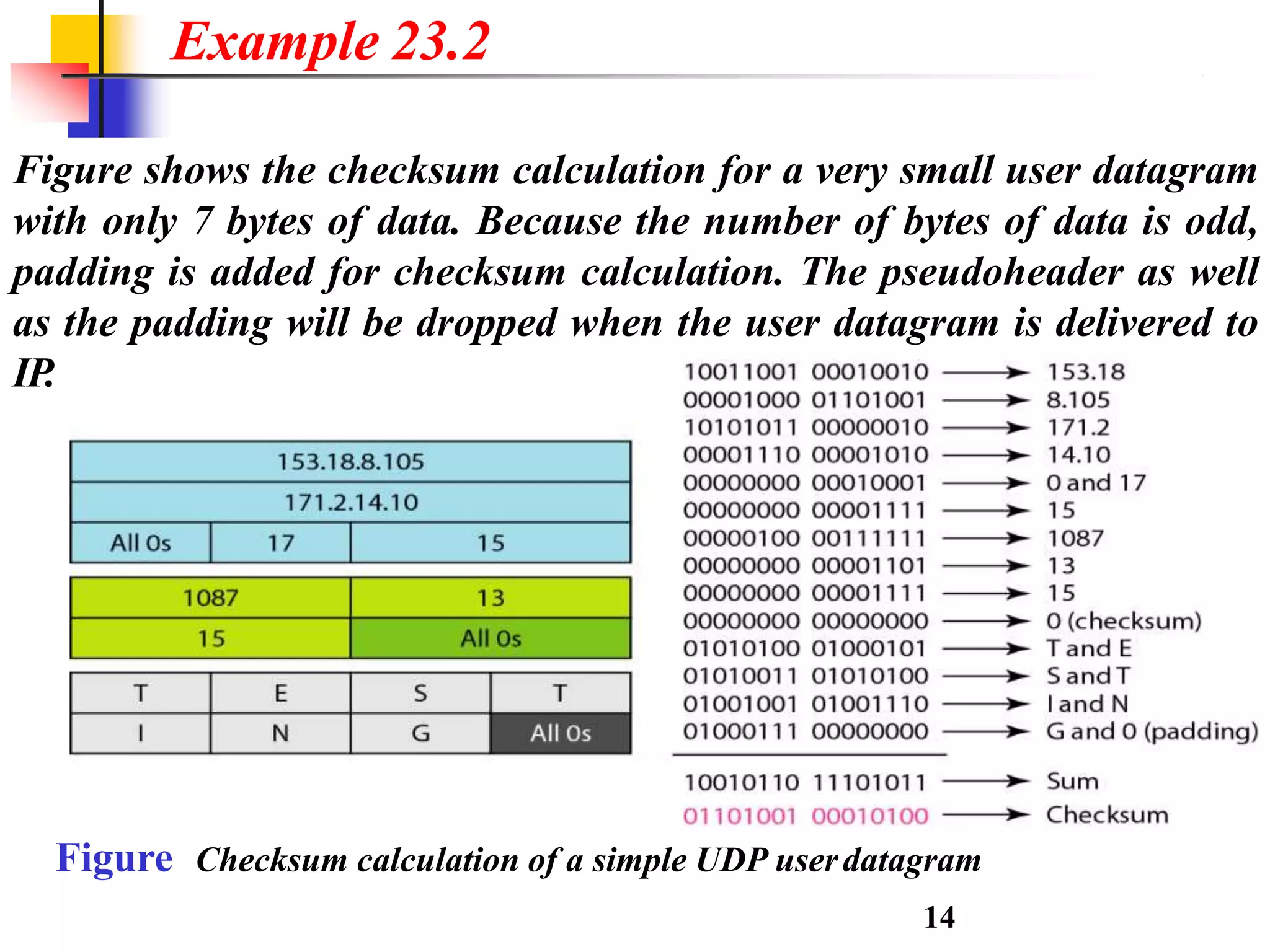
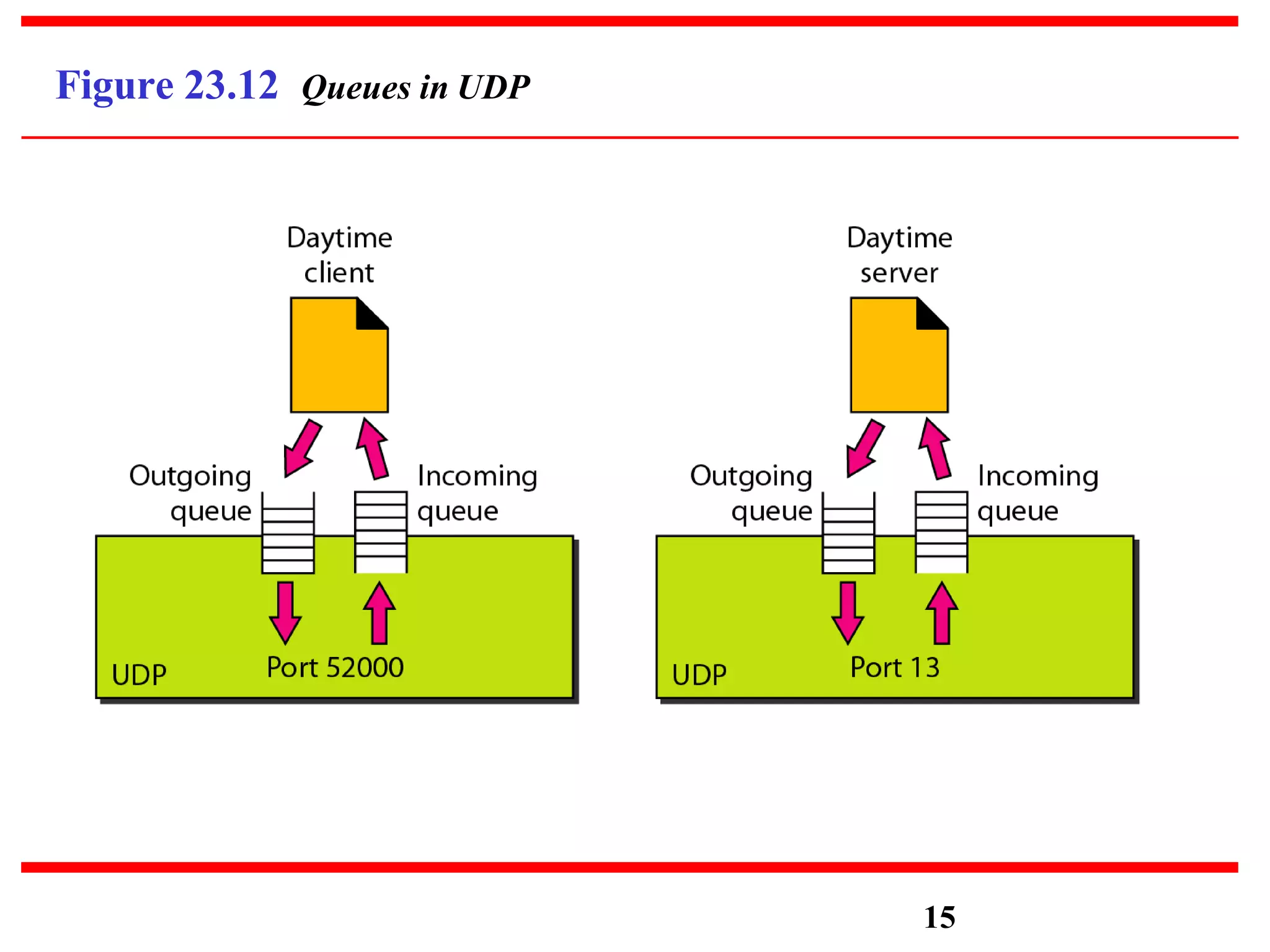
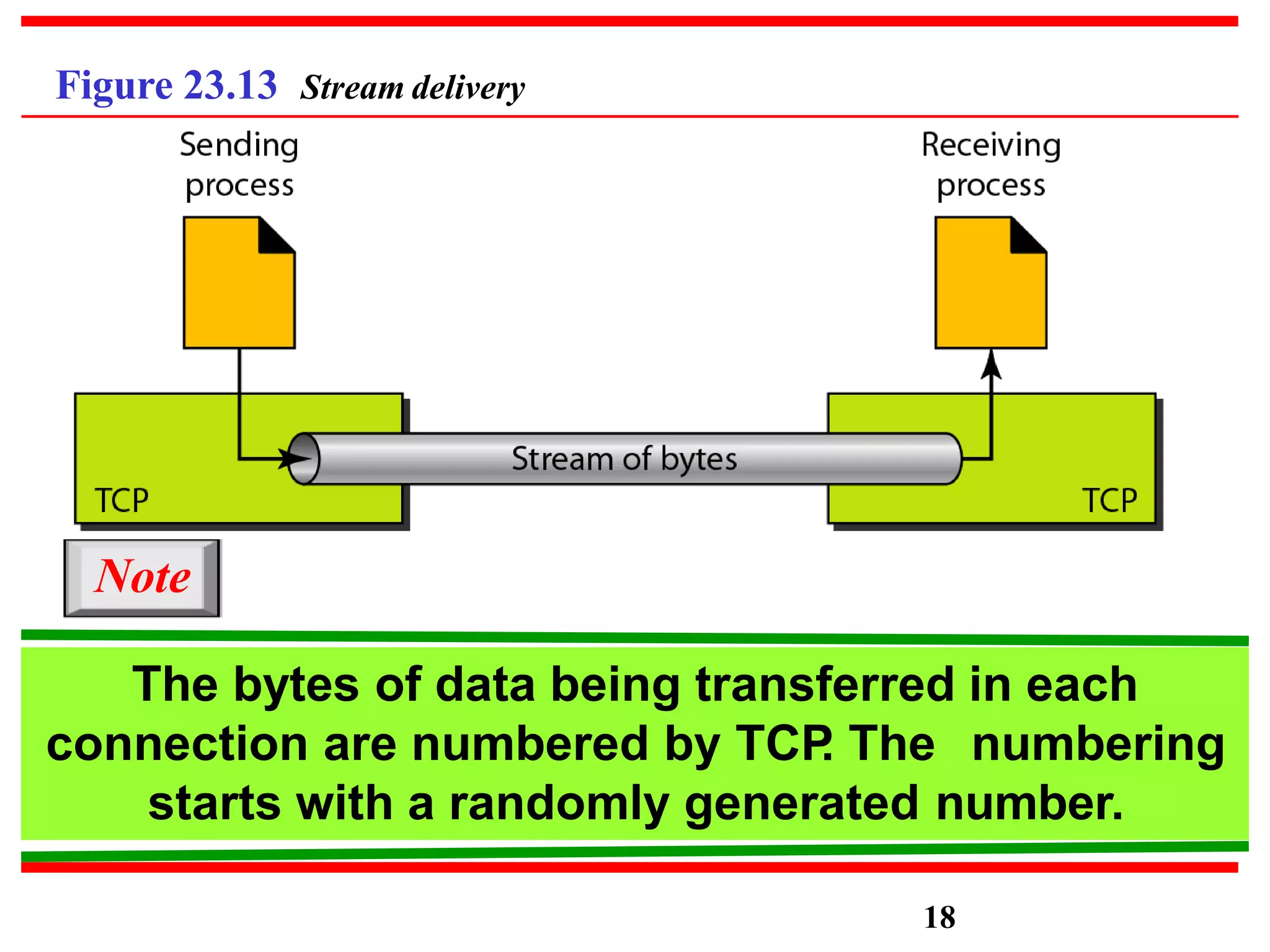
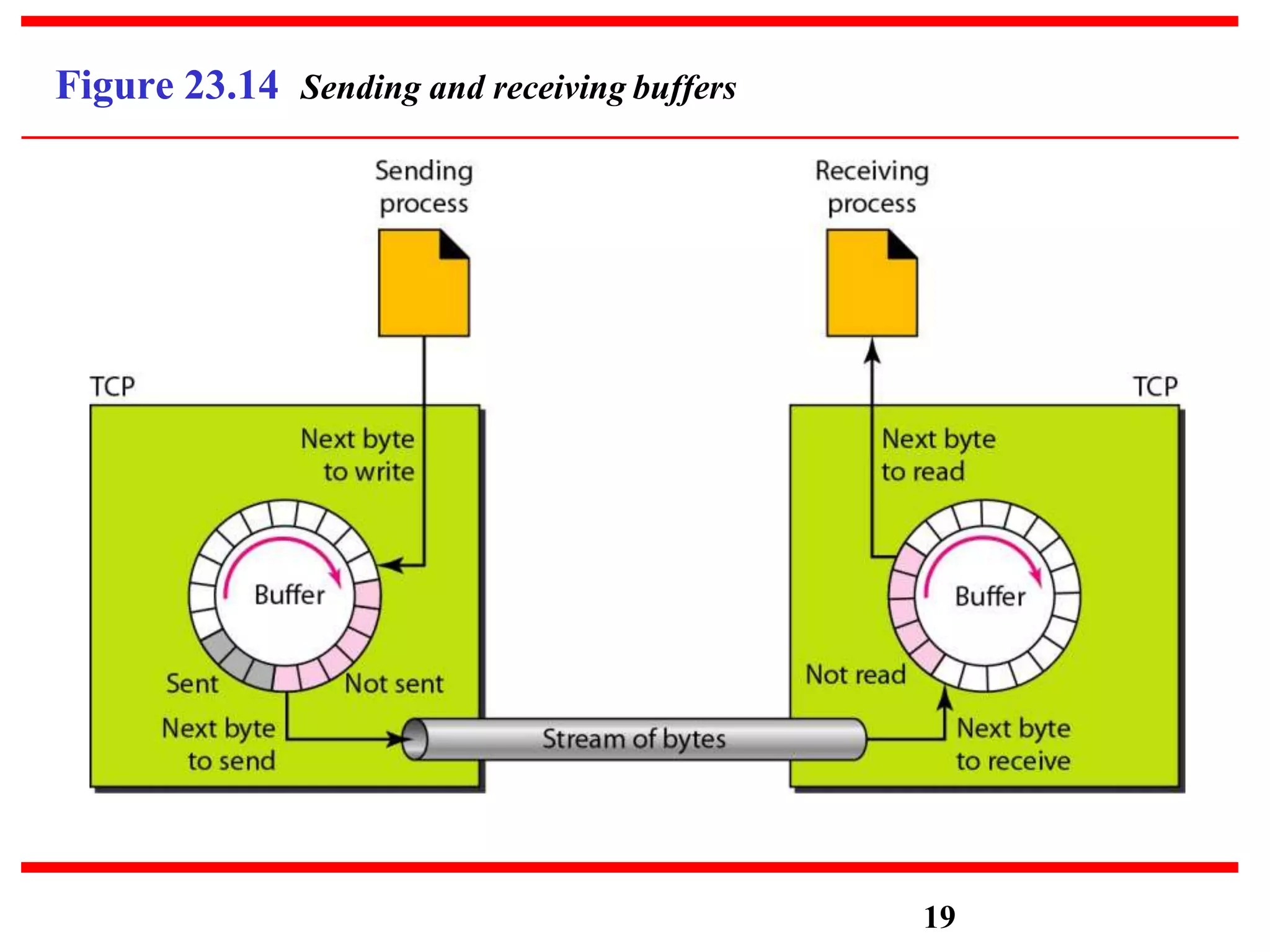
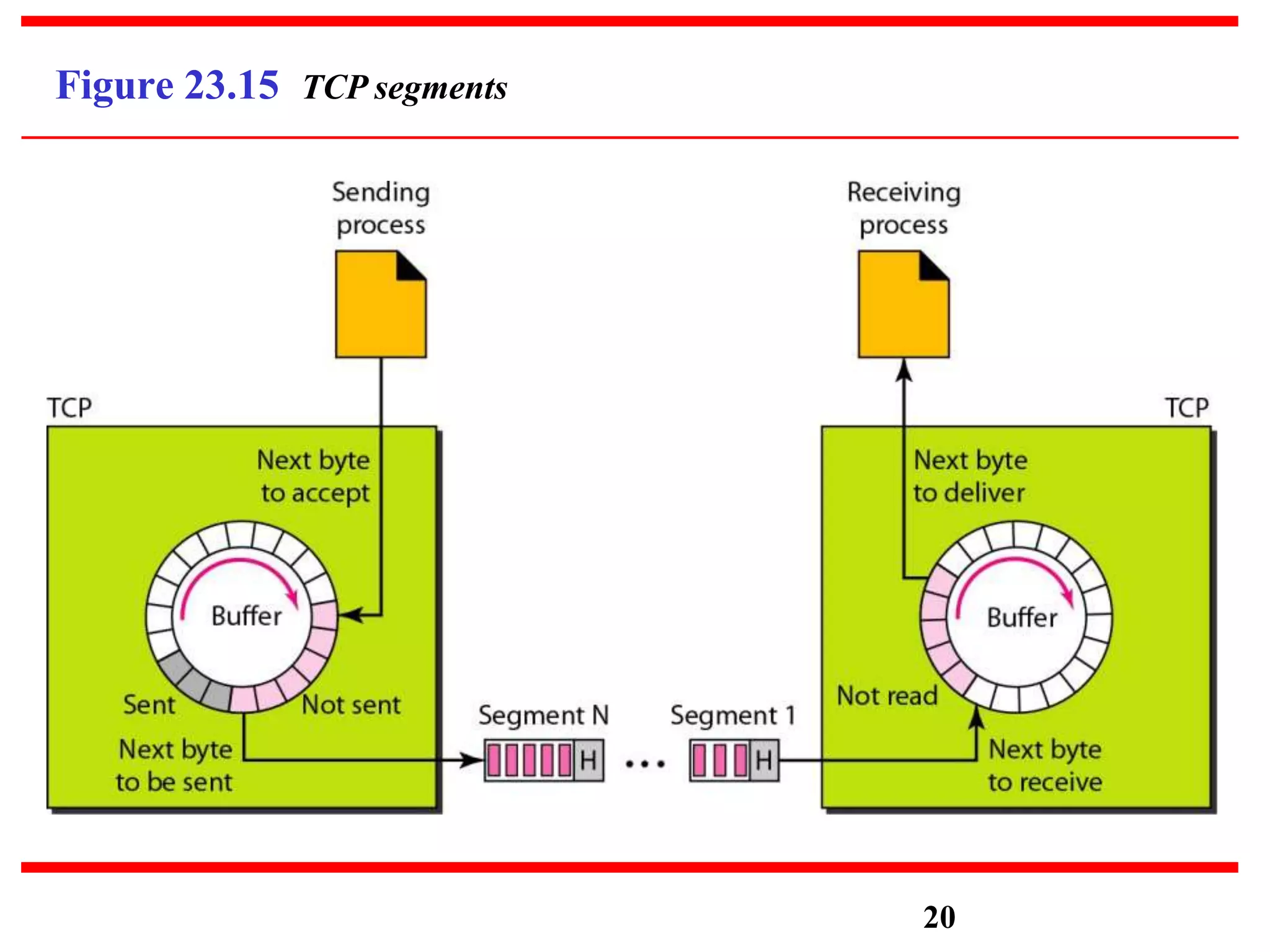
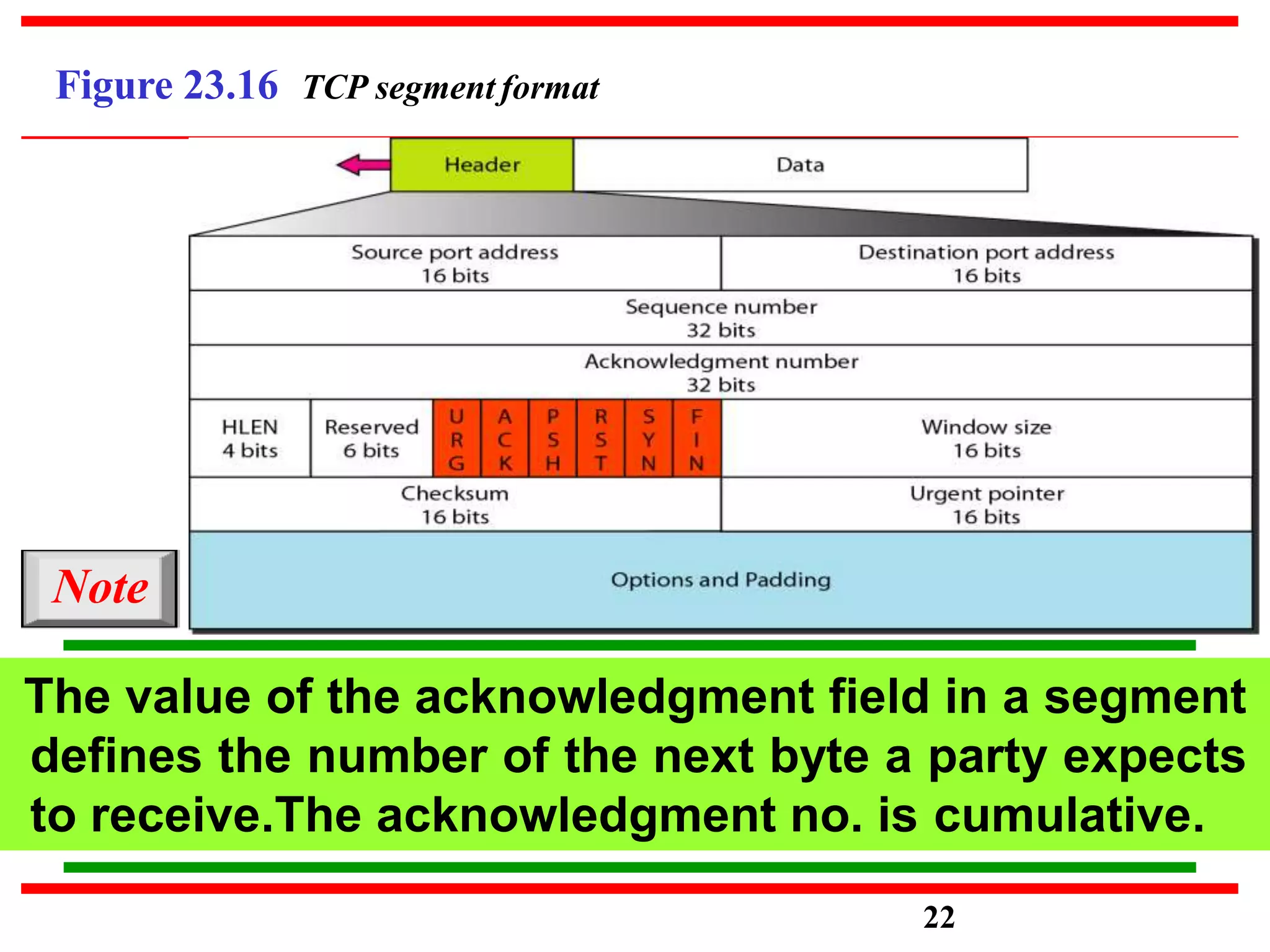
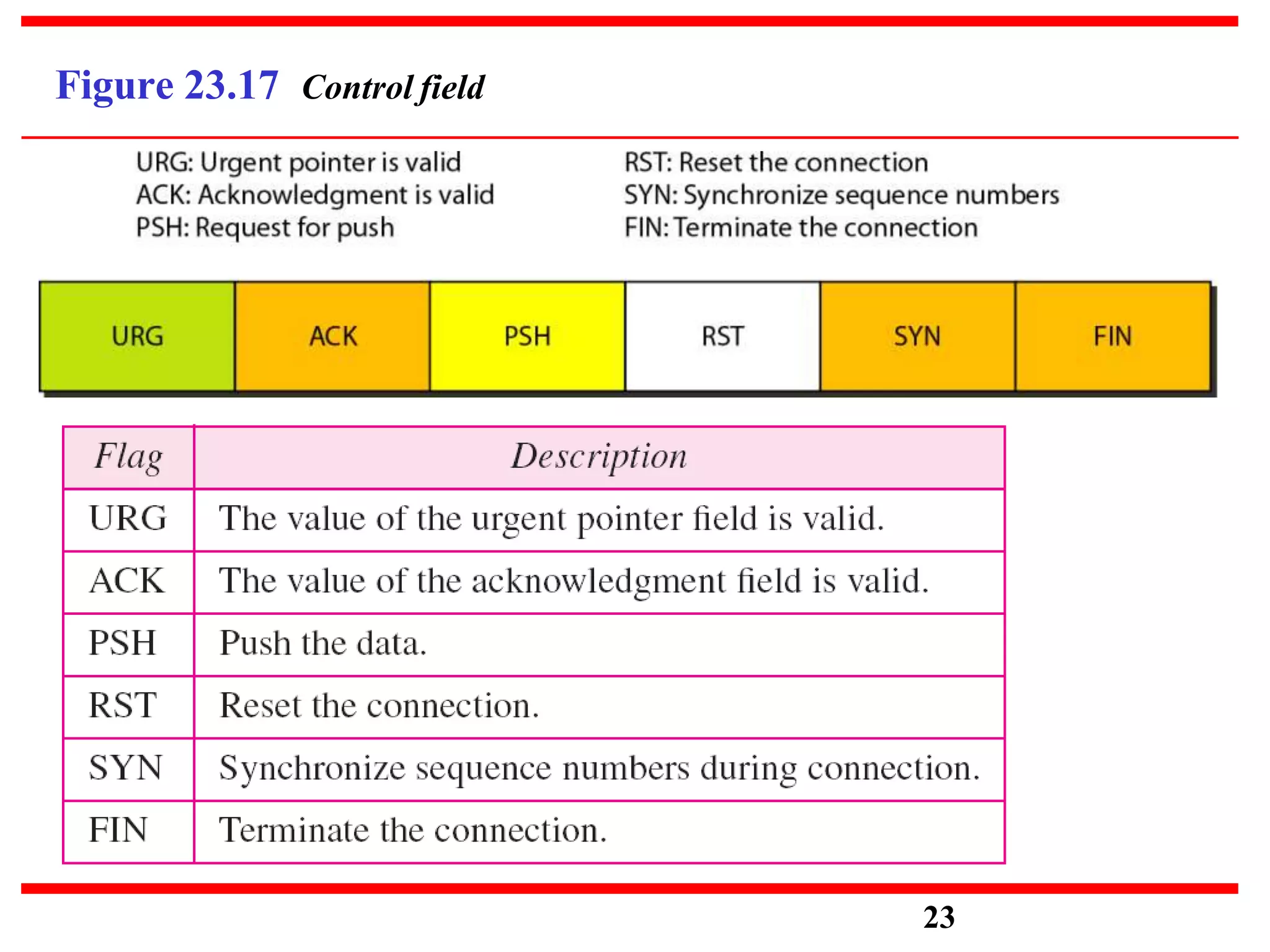
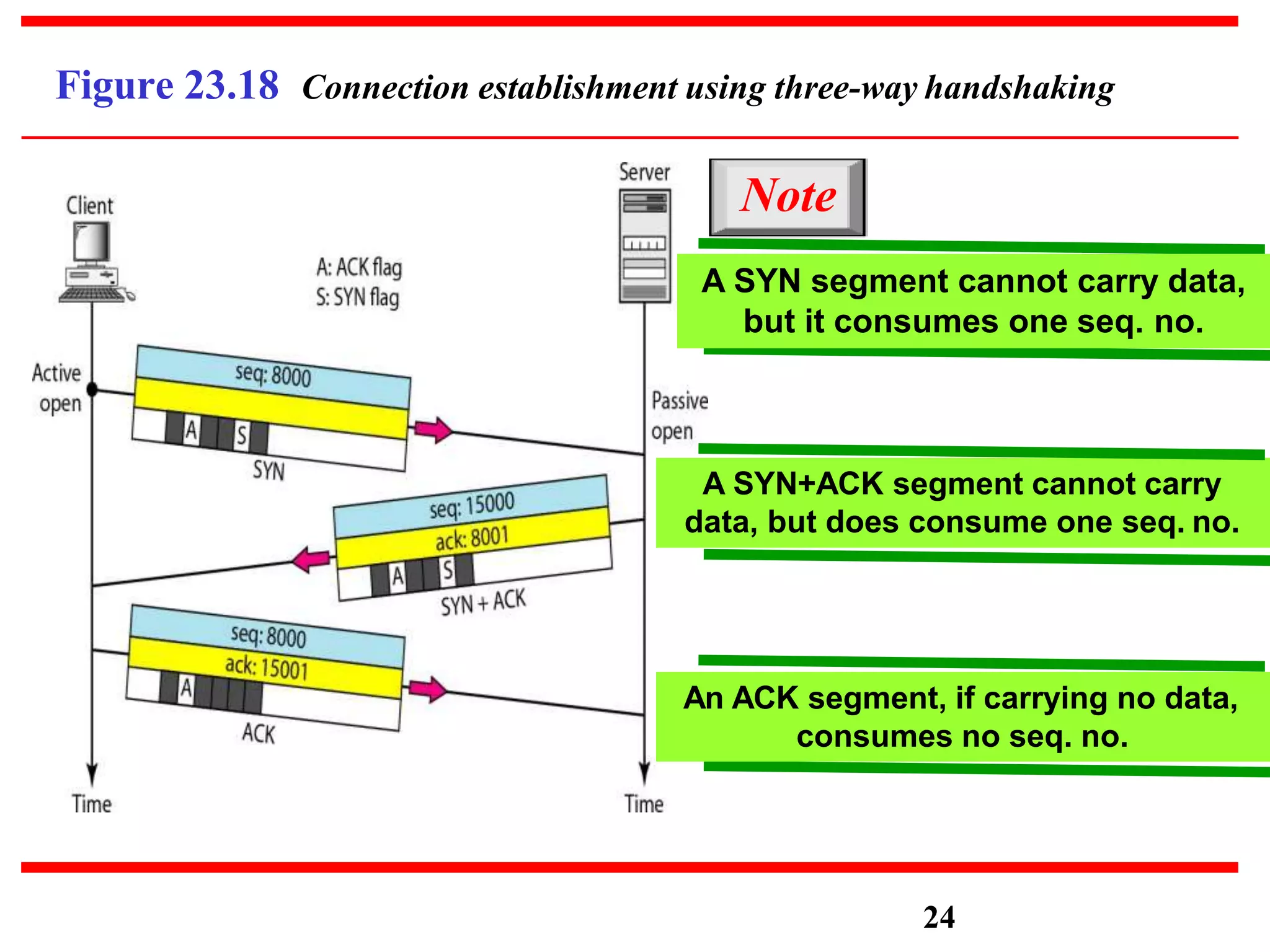
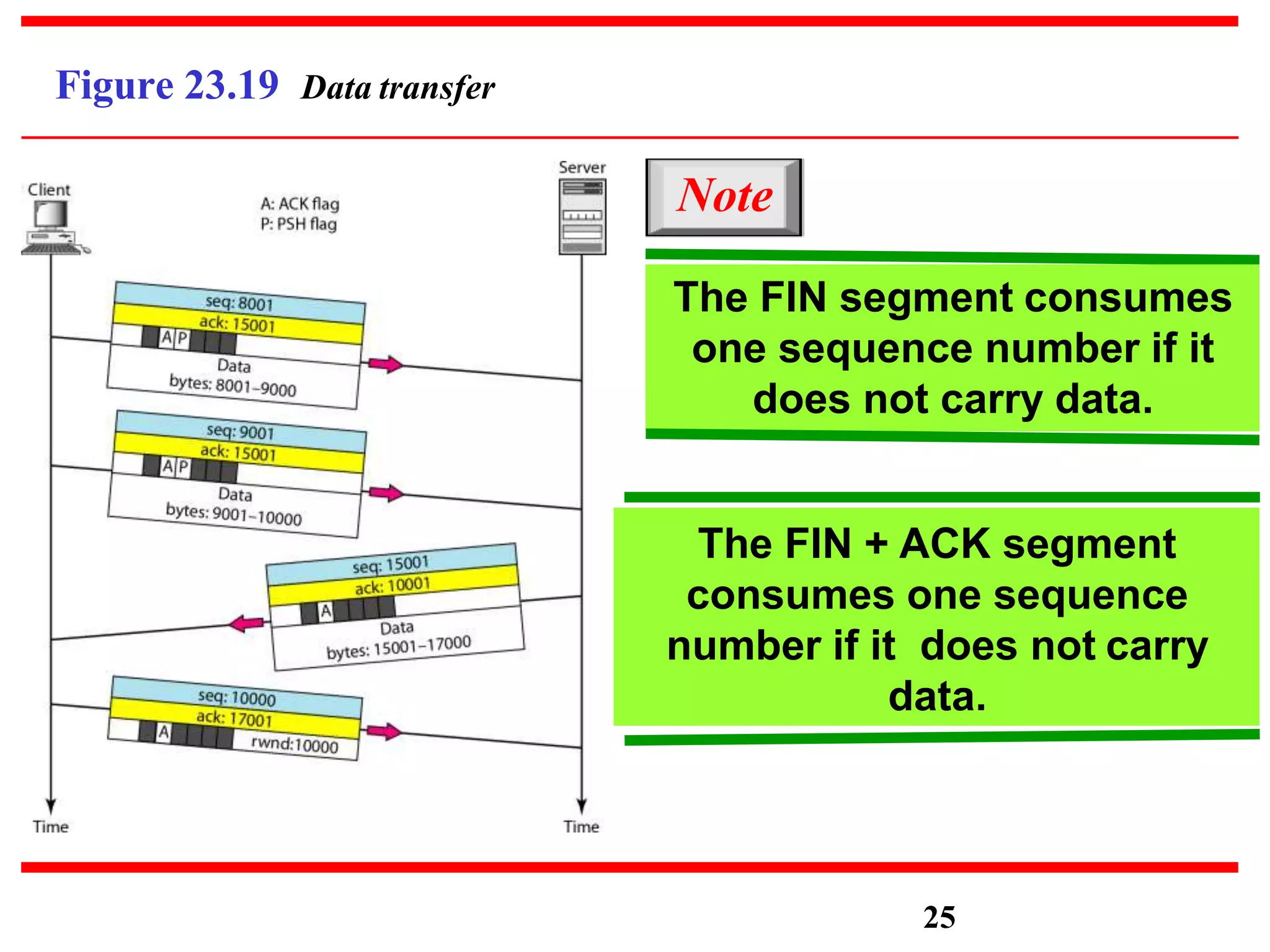
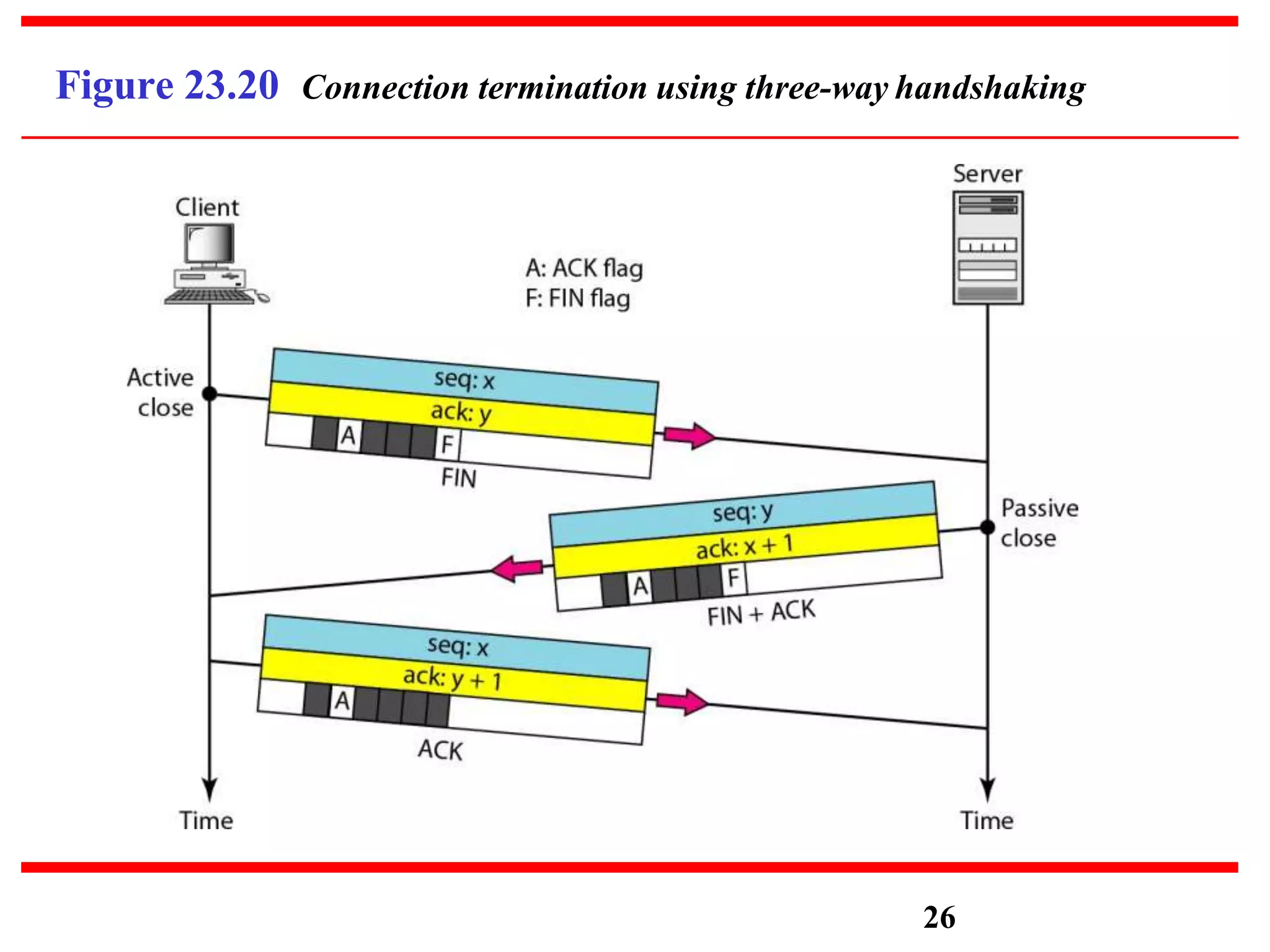
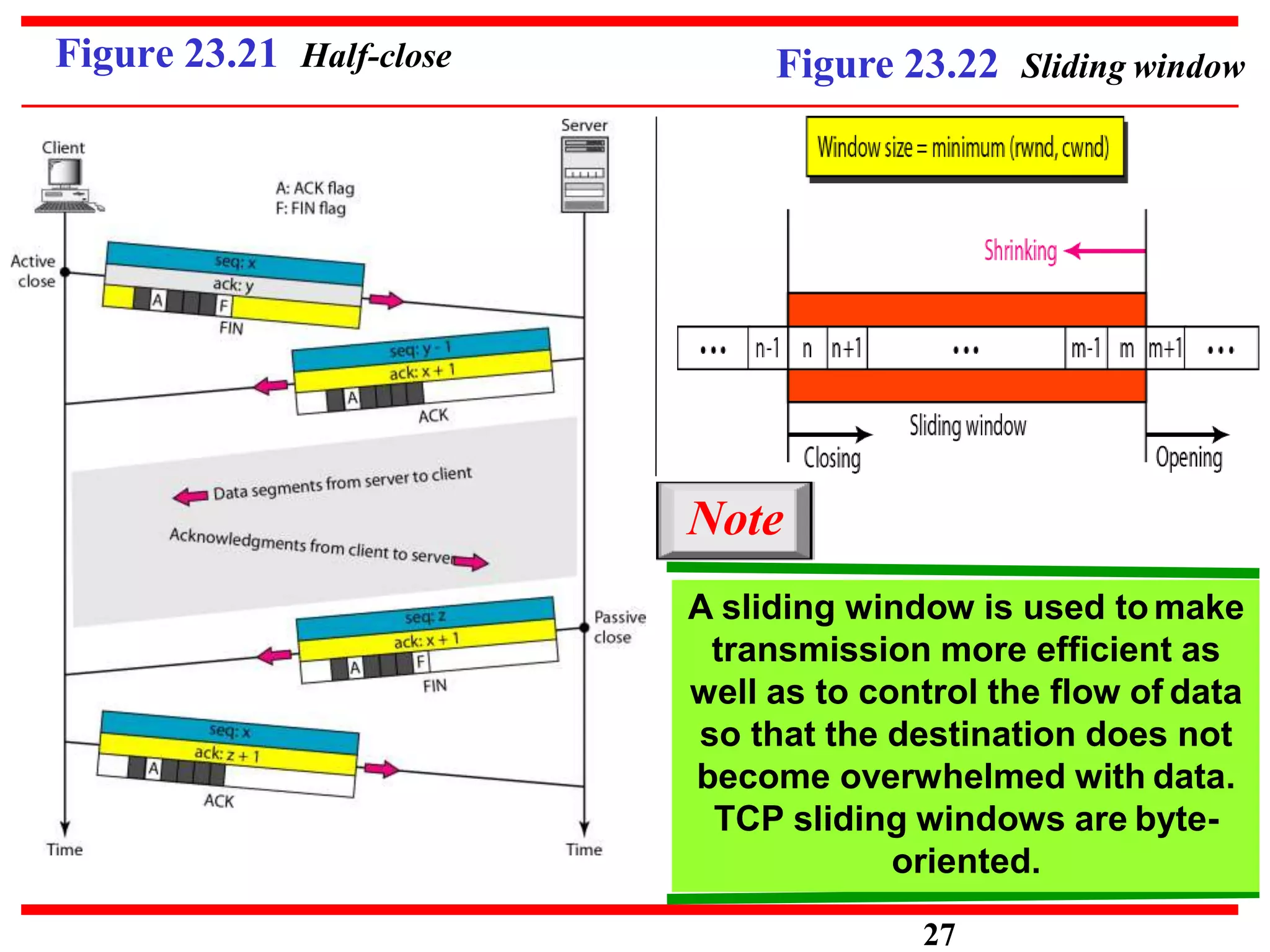
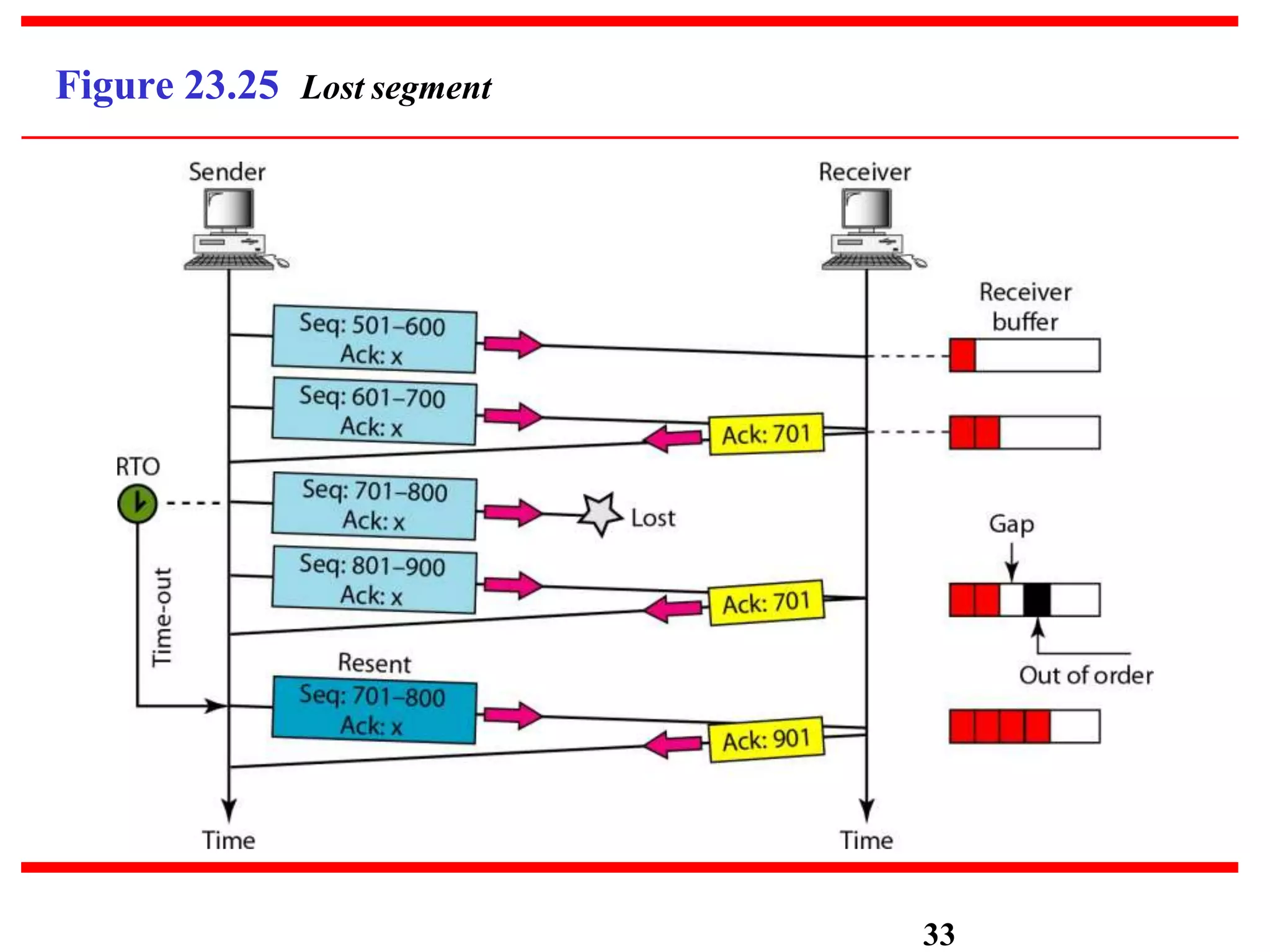
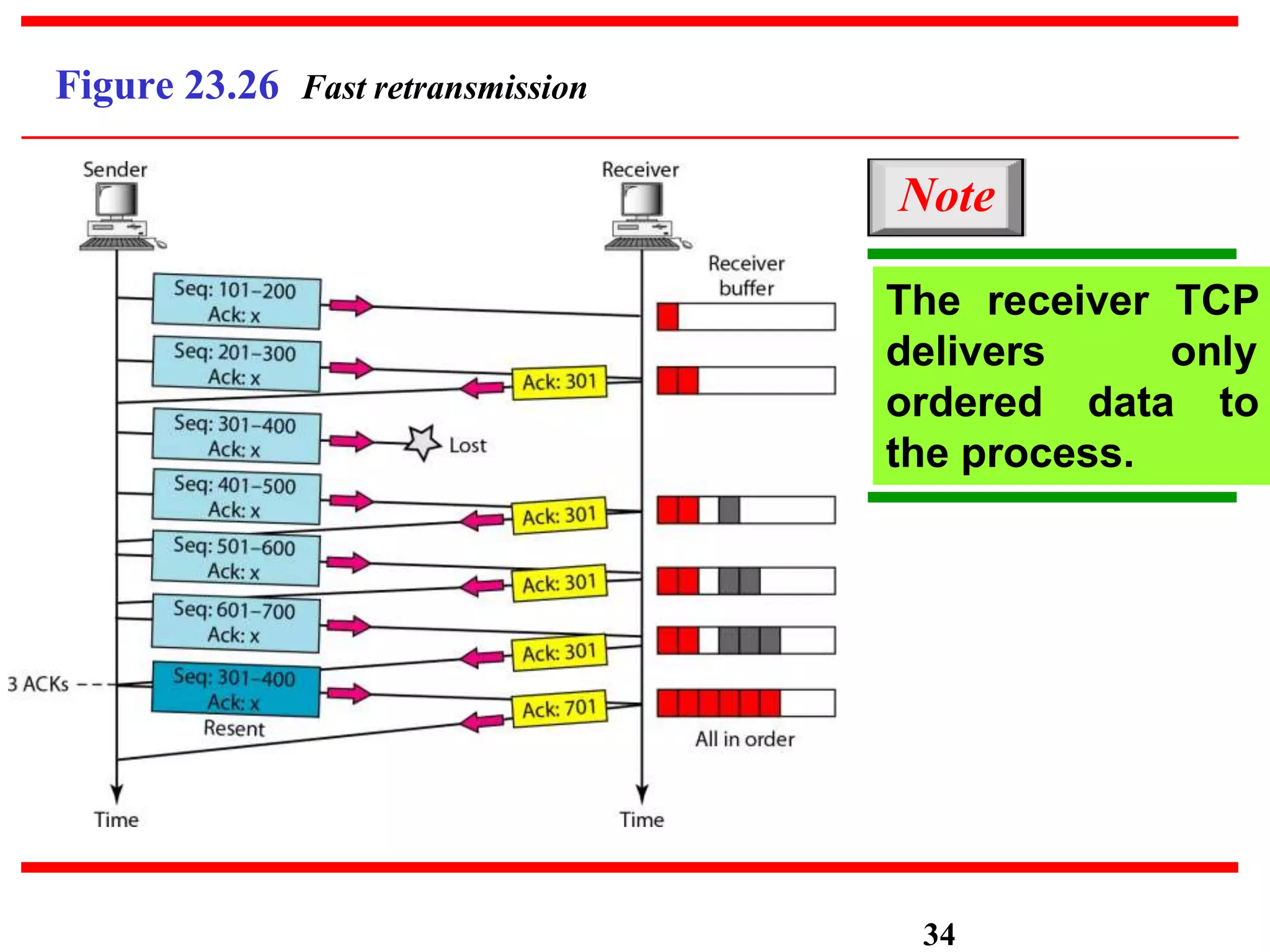
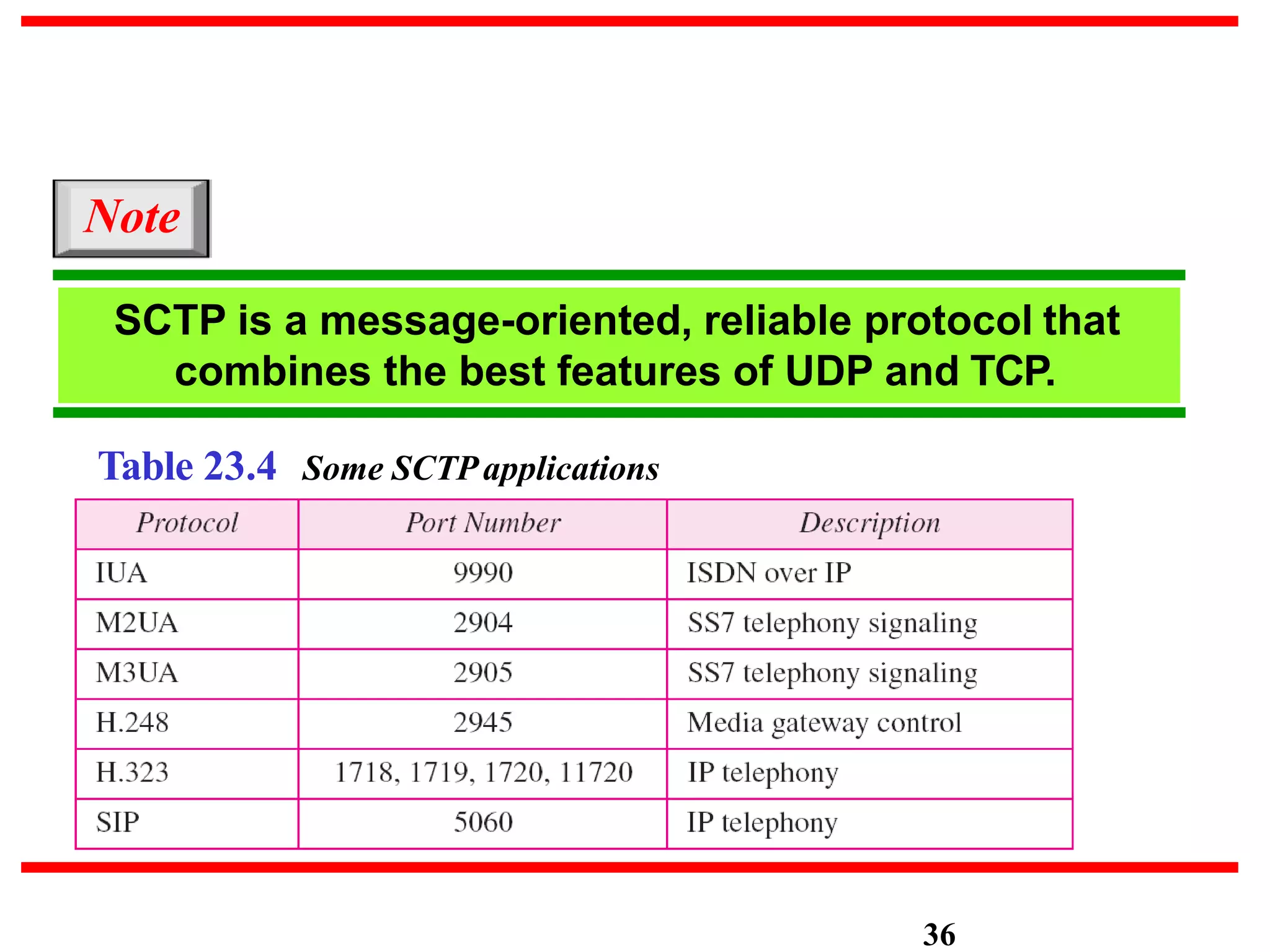
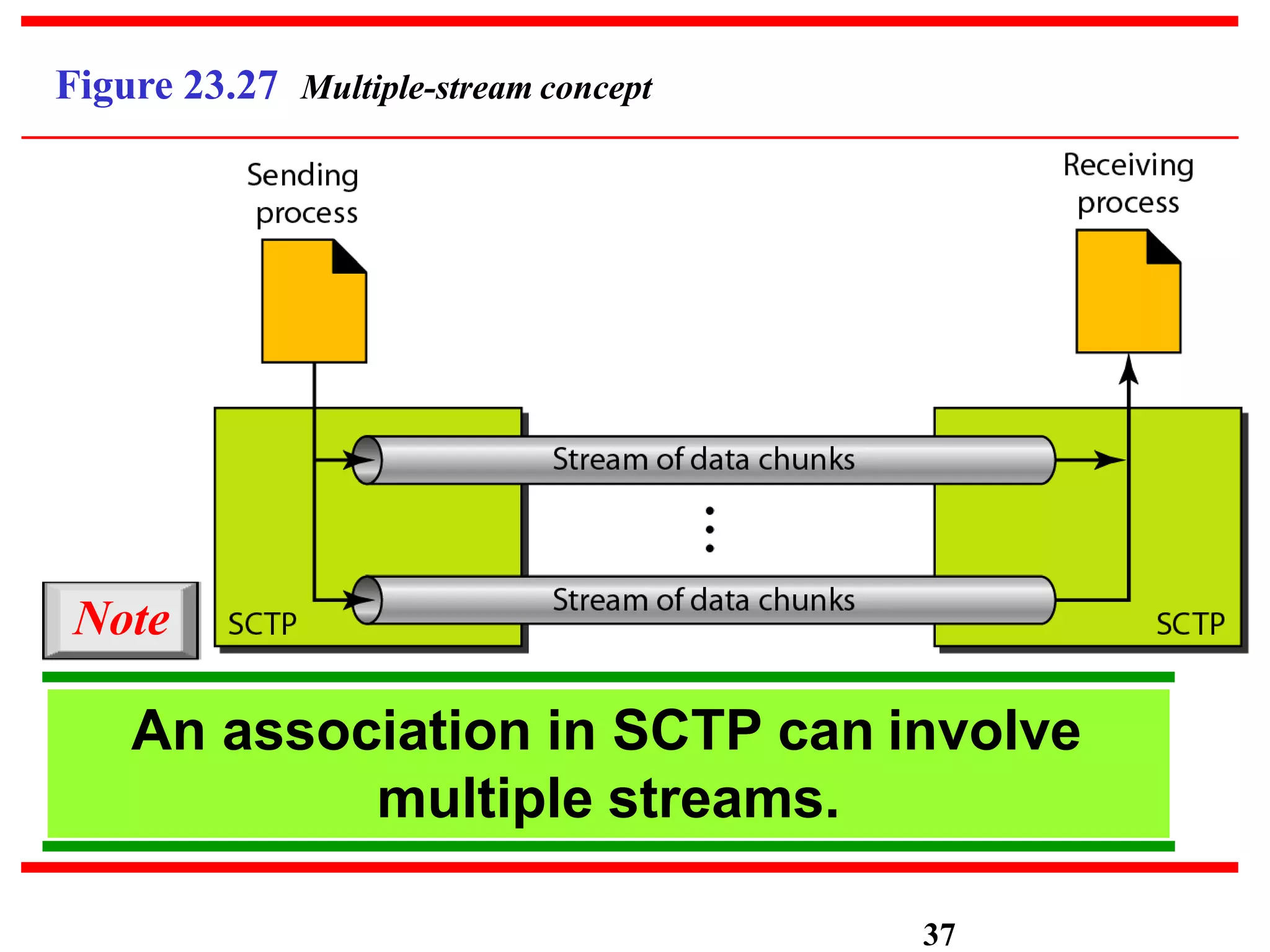
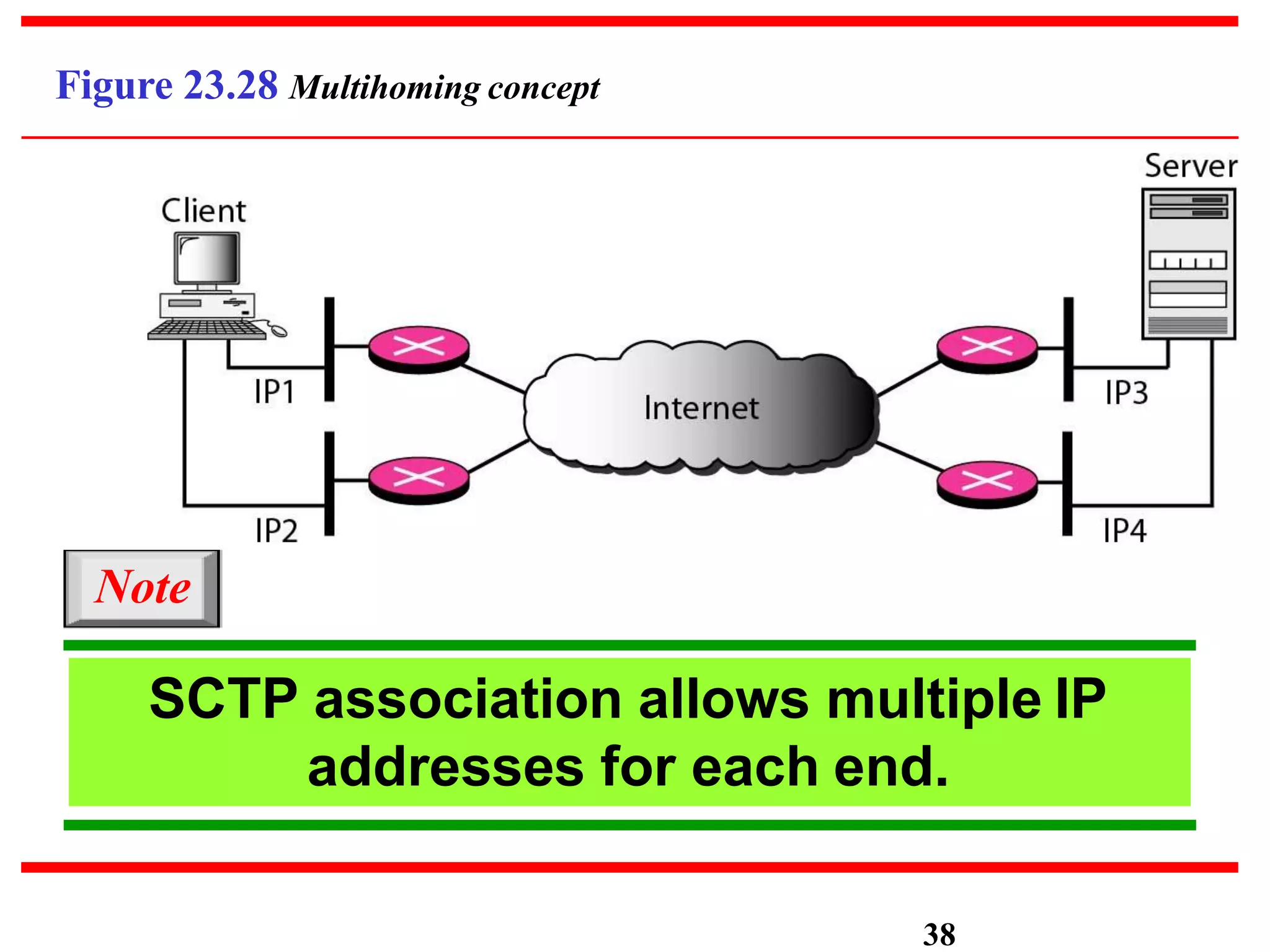
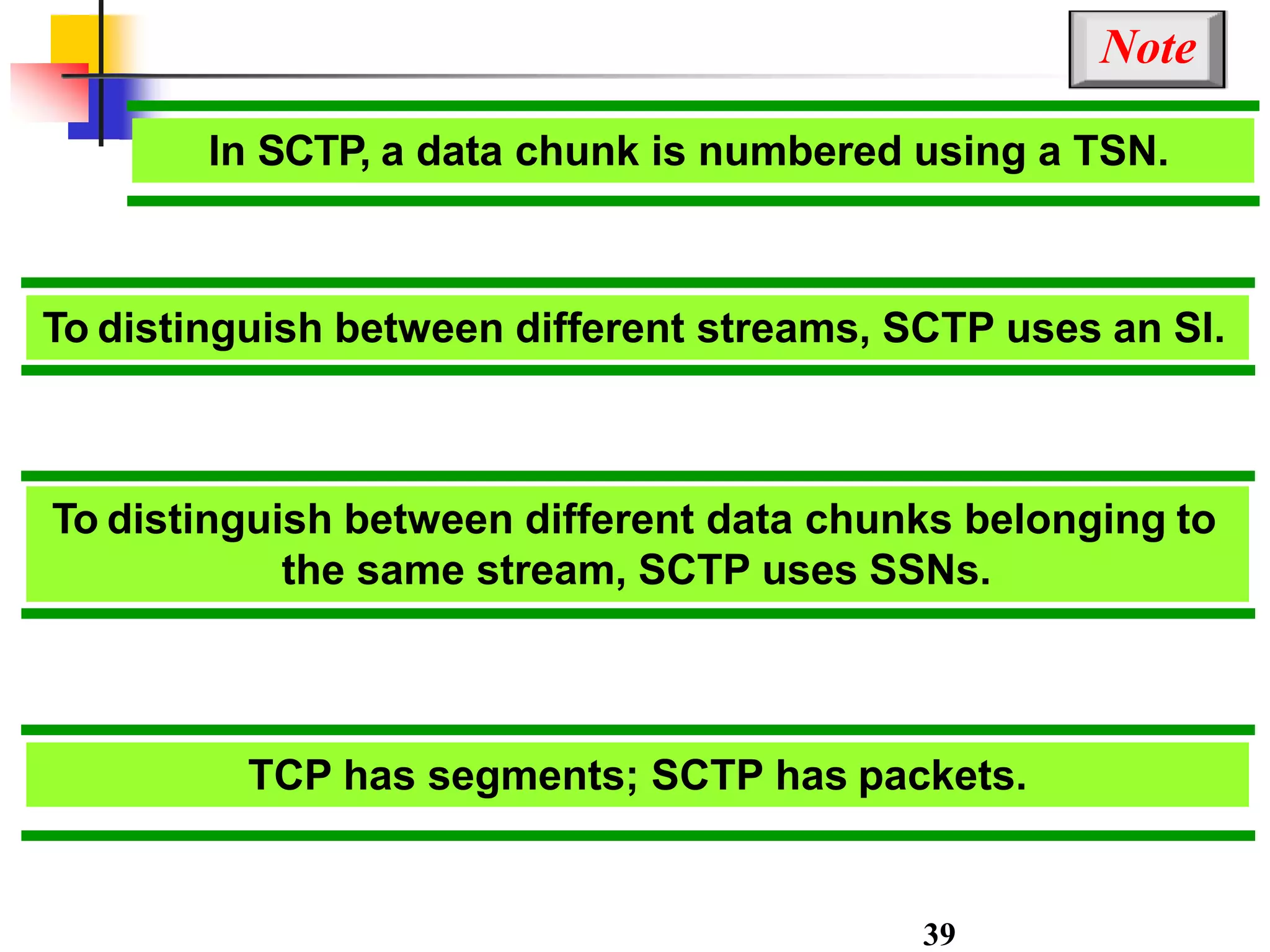
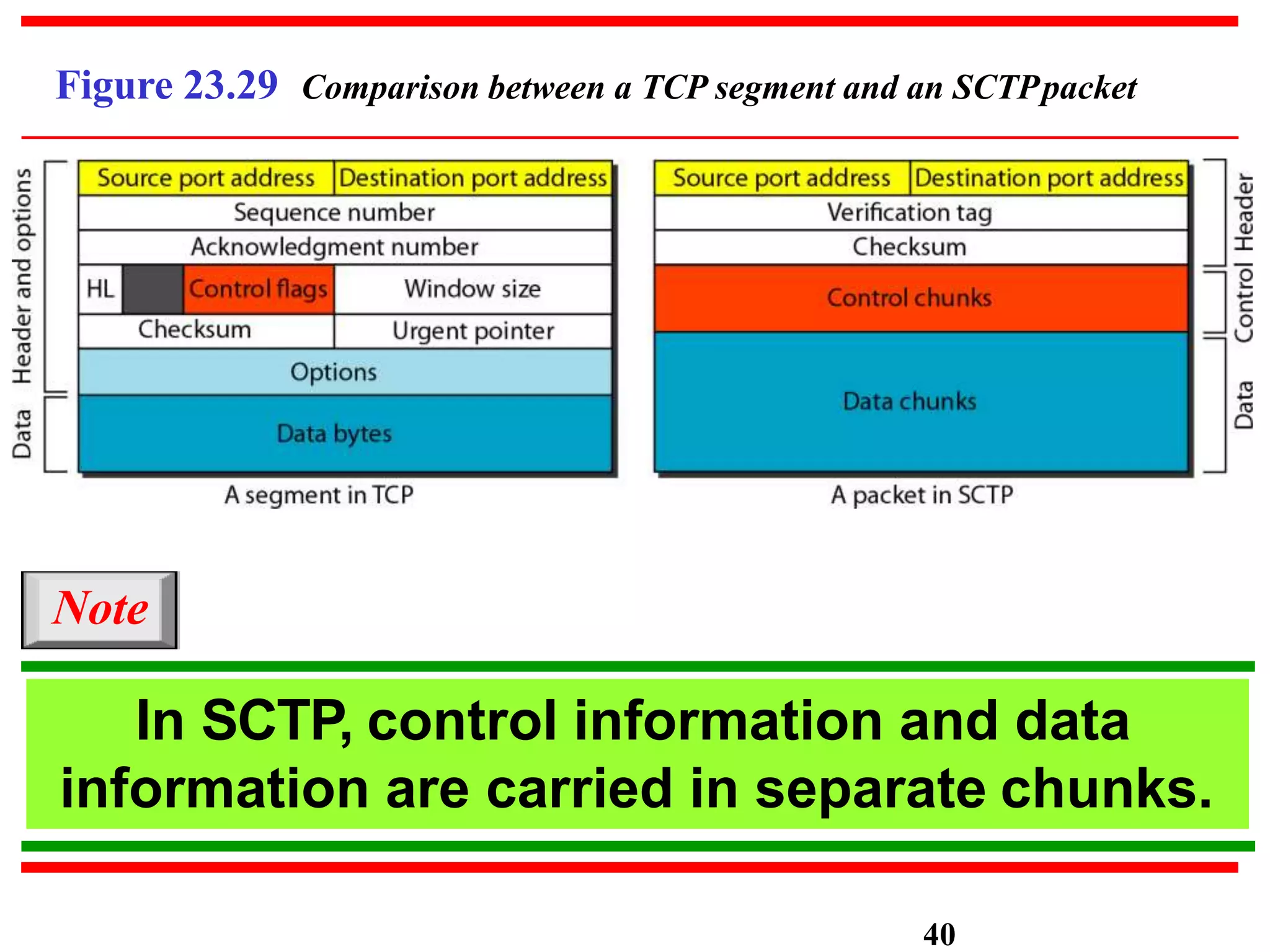
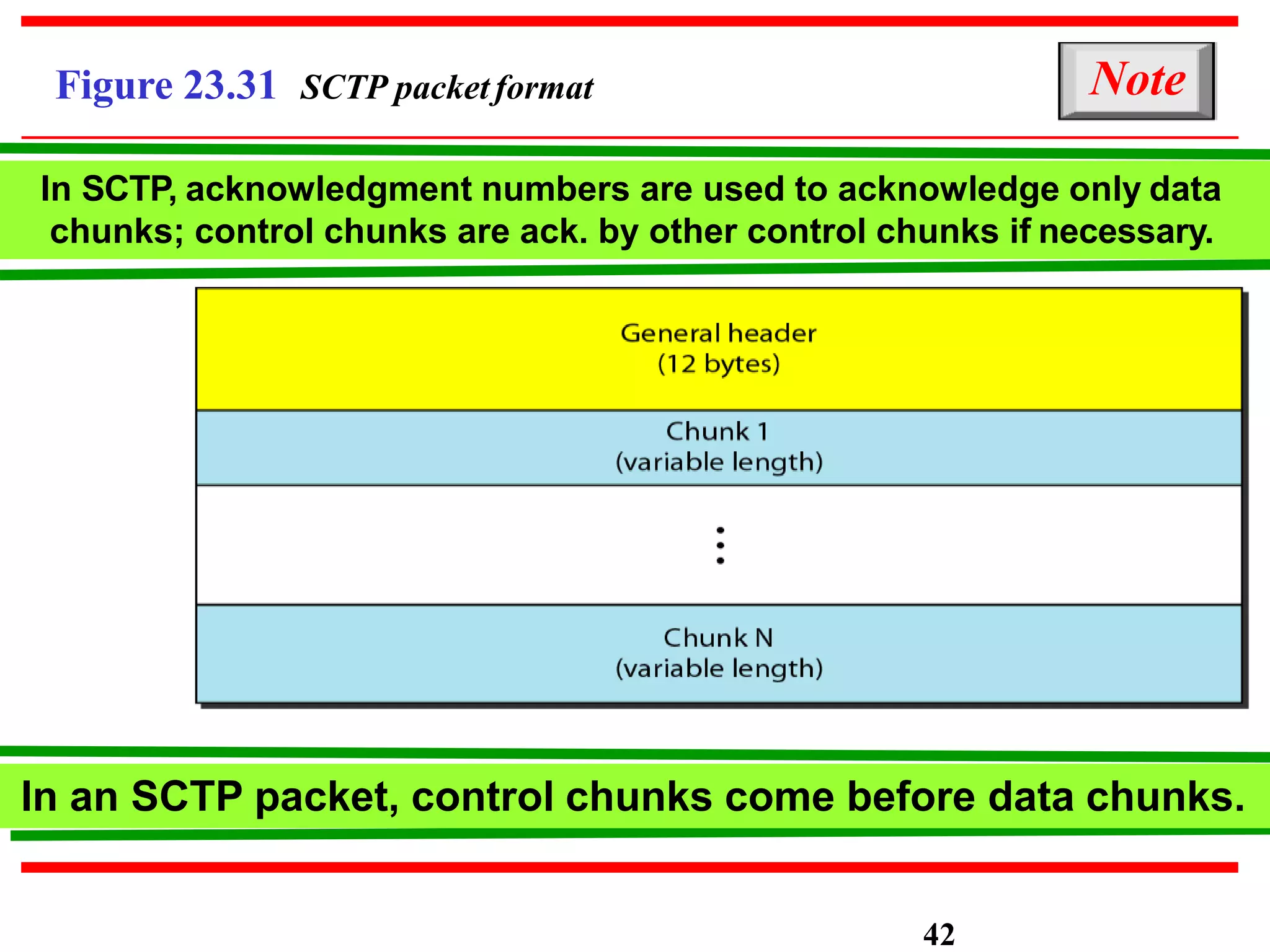
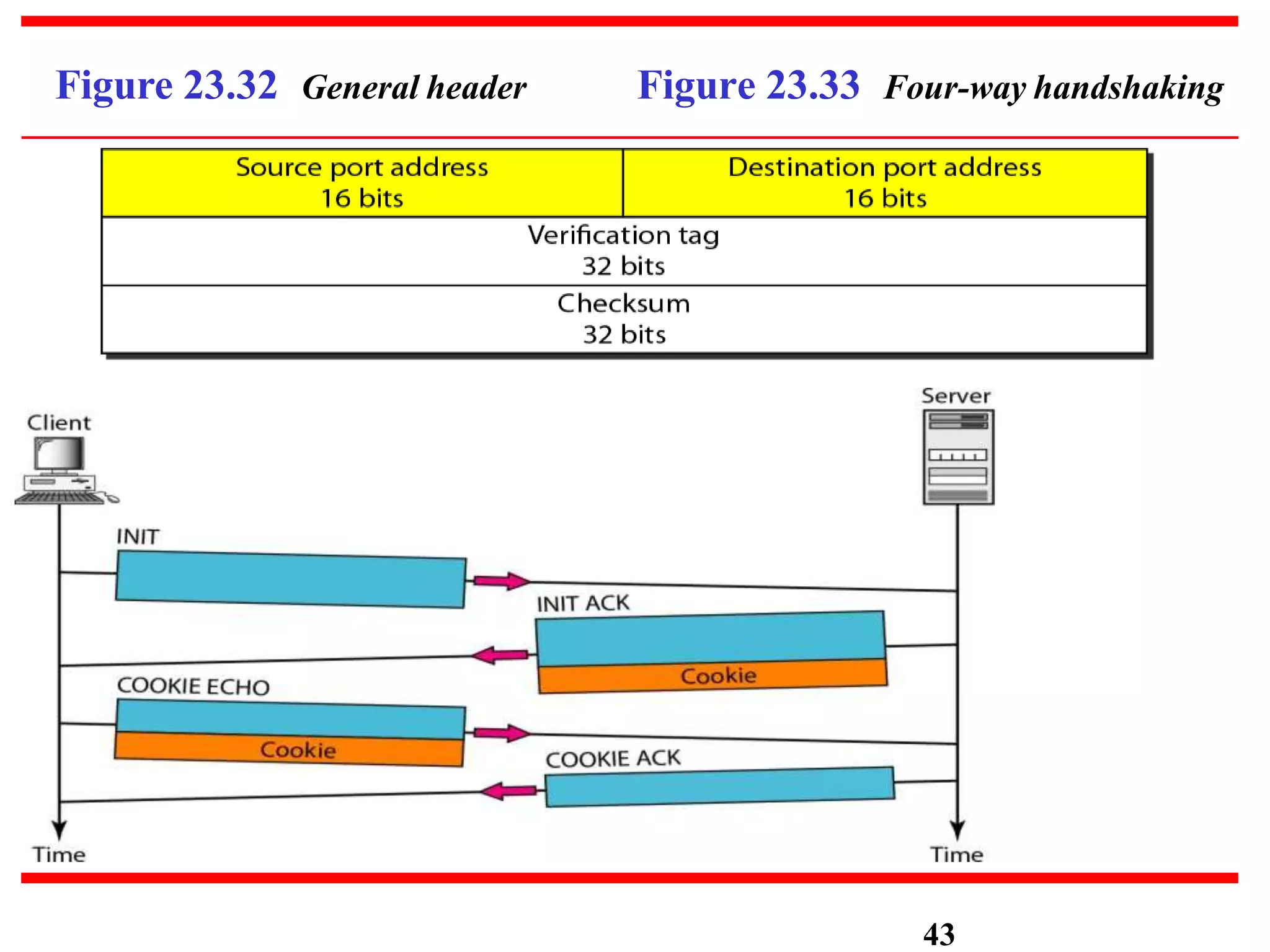
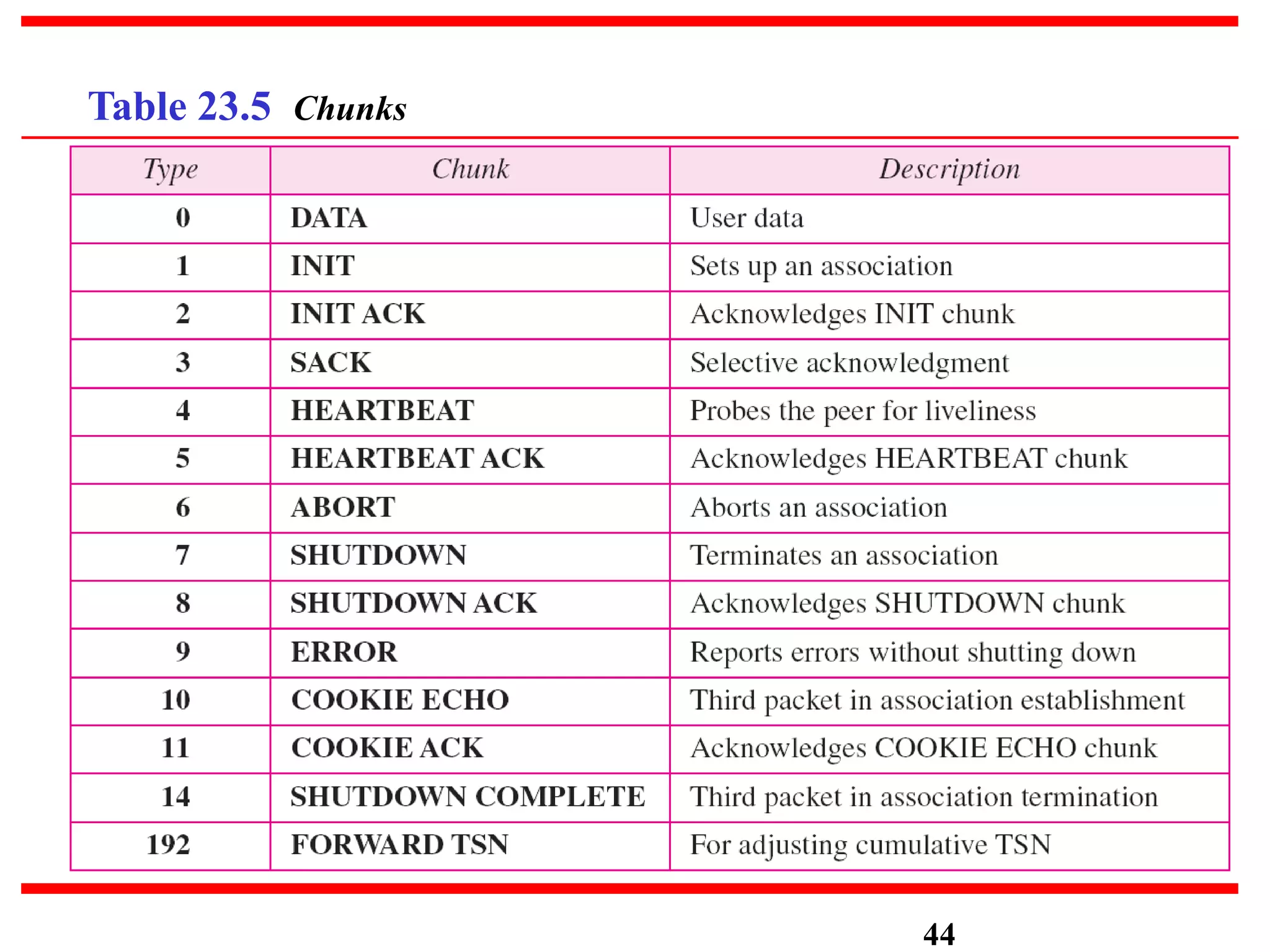
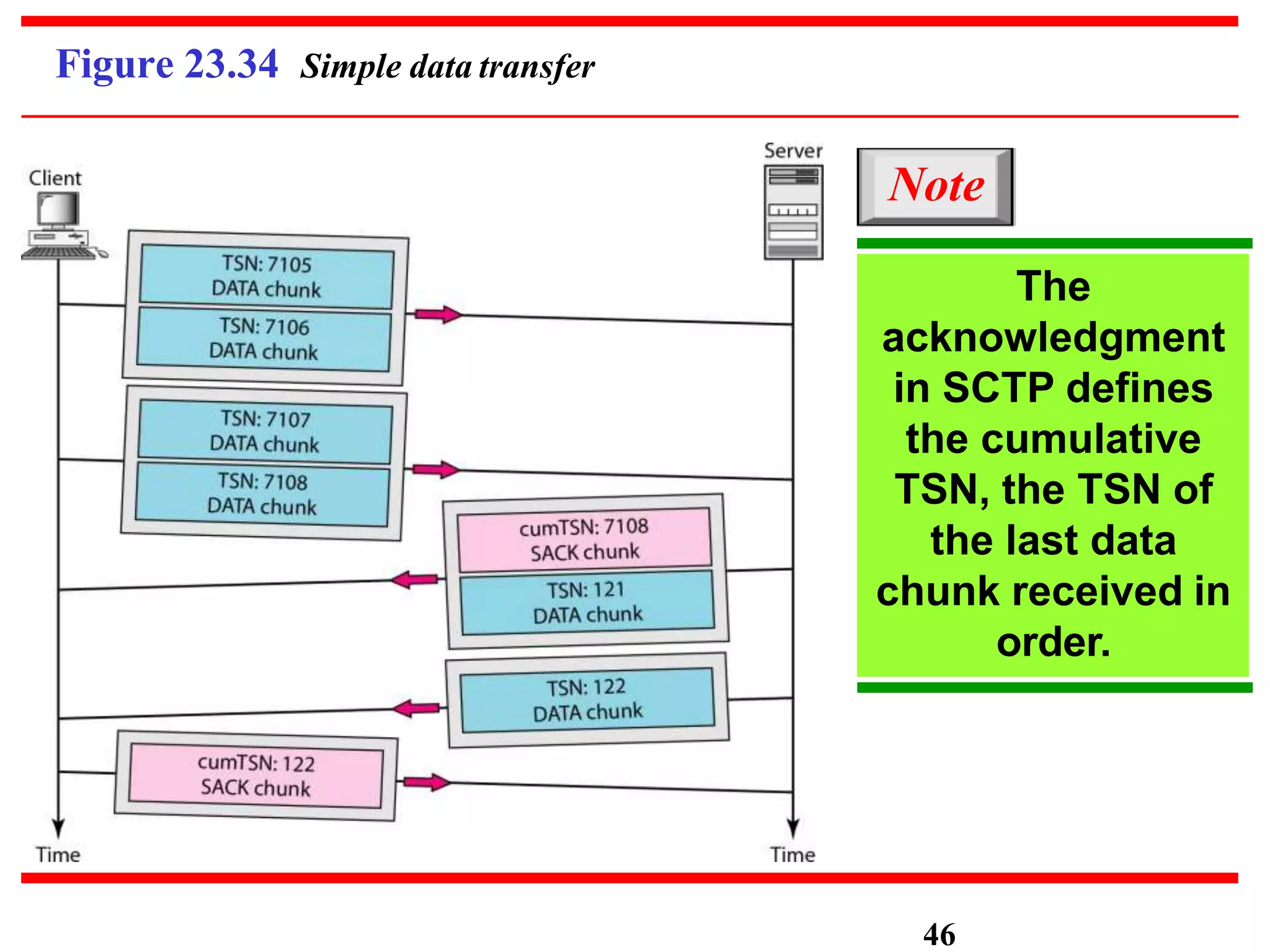
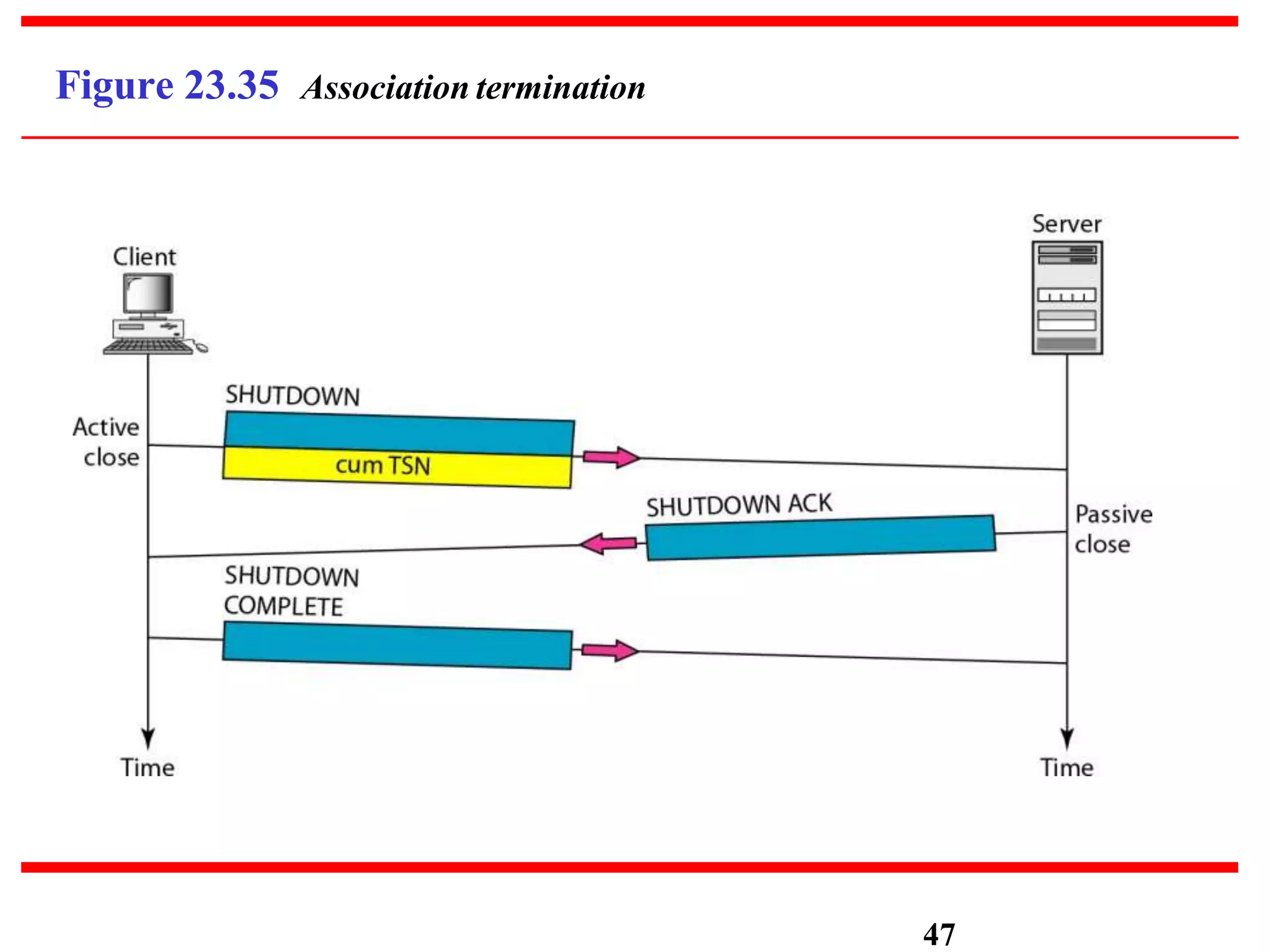
- Three main transport layer protocols are discussed: UDP, which provides connectionless and unreliable data transfer. TCP, which provides connection-oriented and reliable data transfer. And SCTP, which provides message-oriented, reliable transfer and supports features like multi-homing.
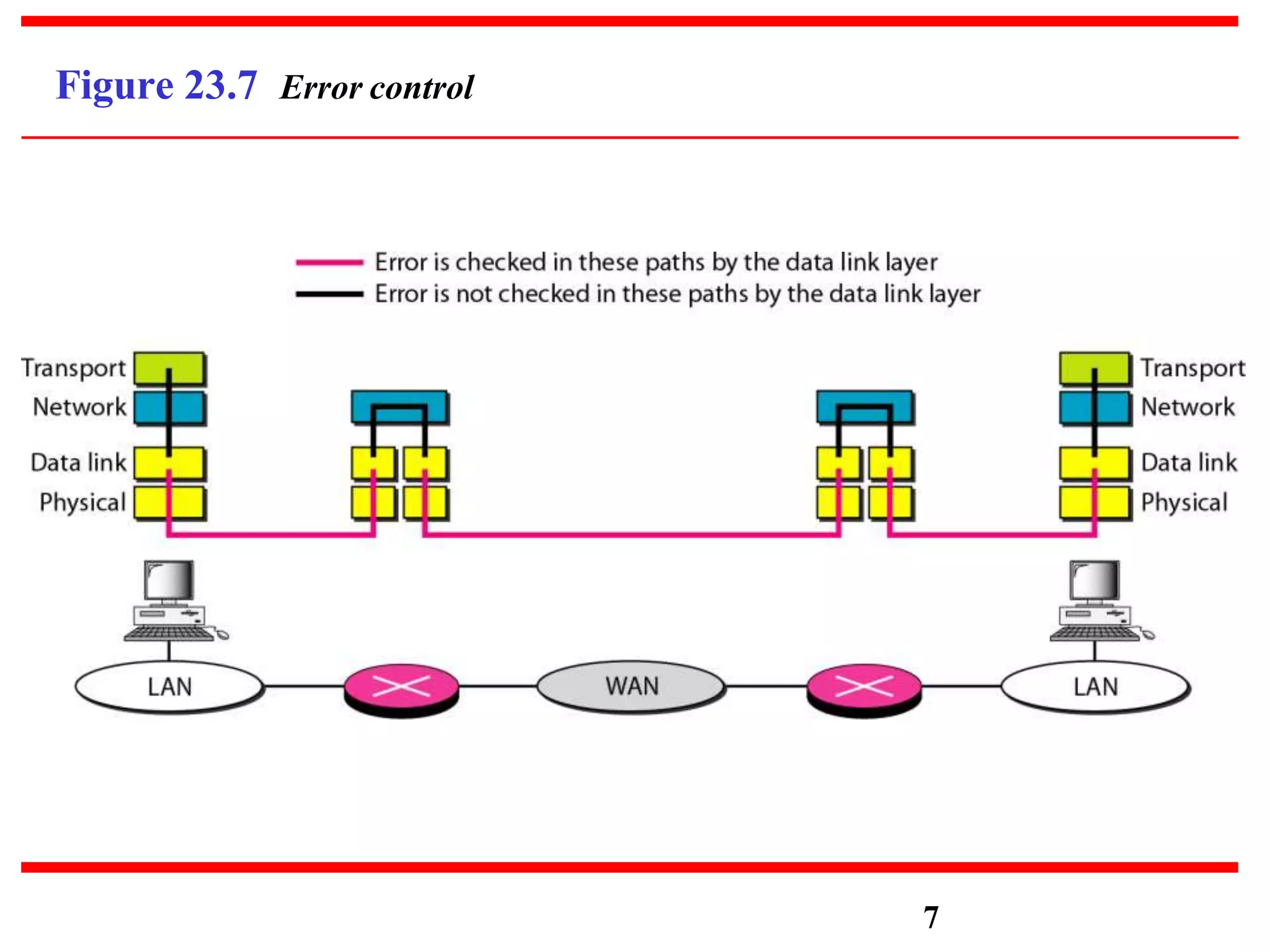
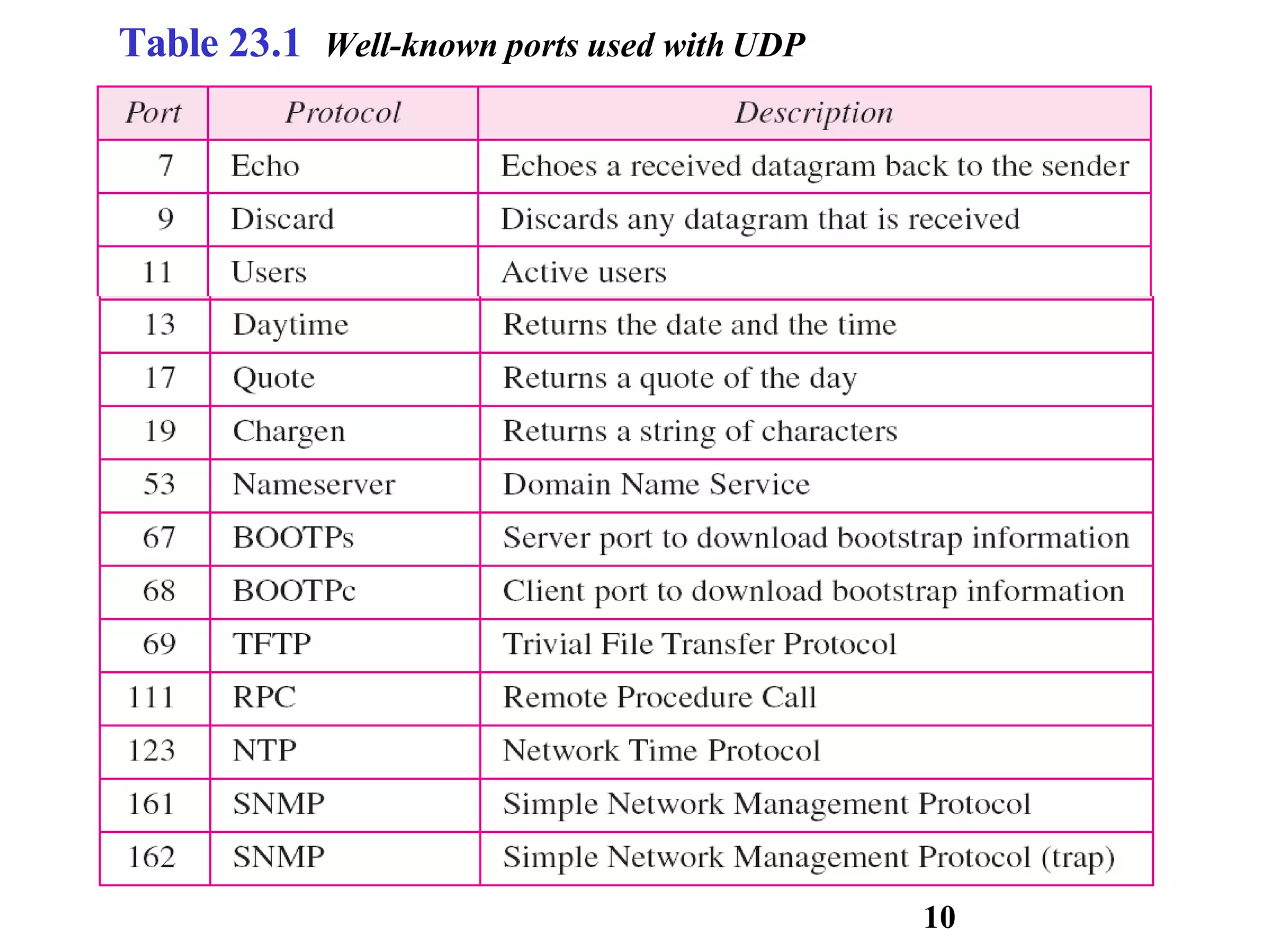
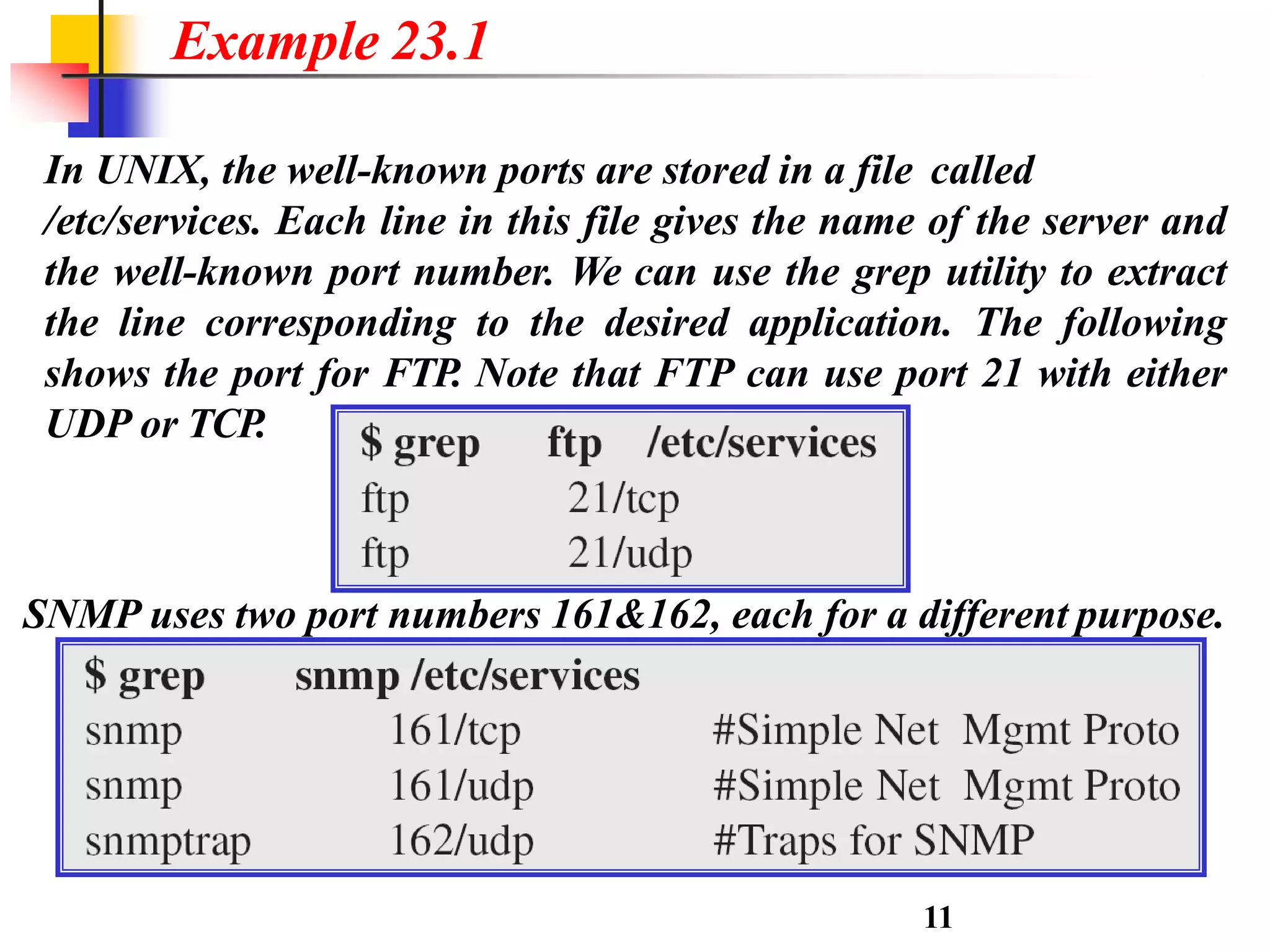
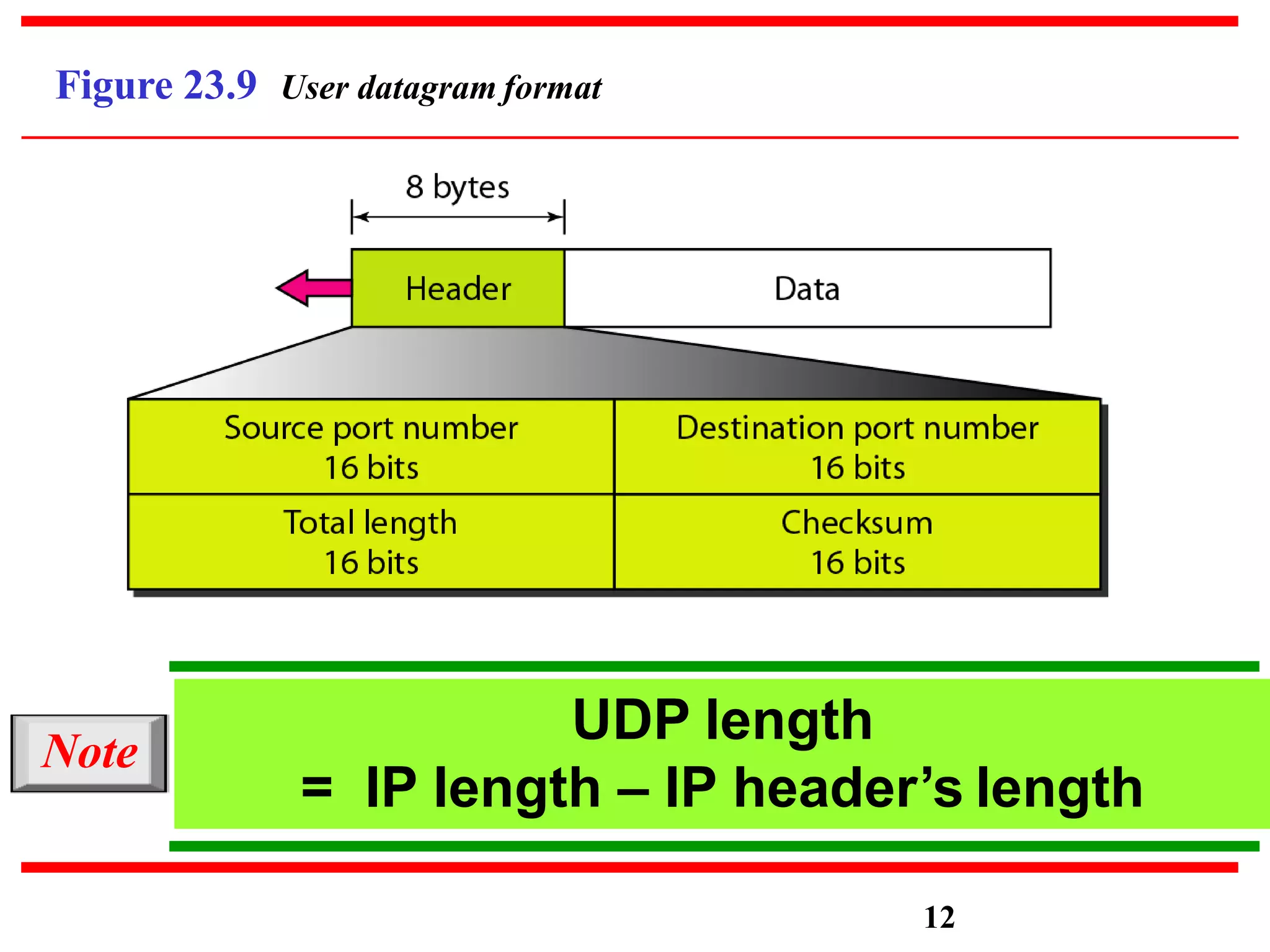
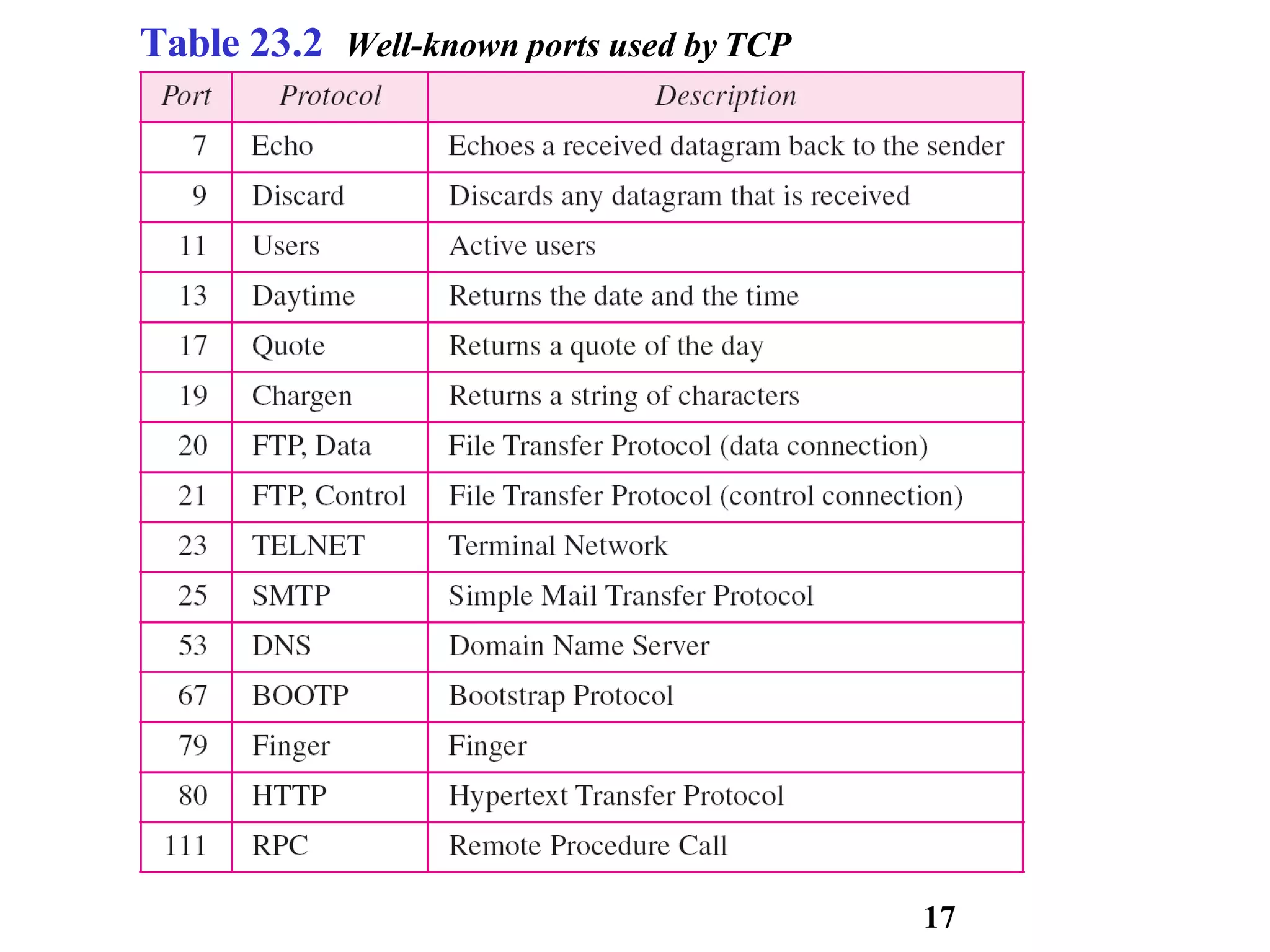
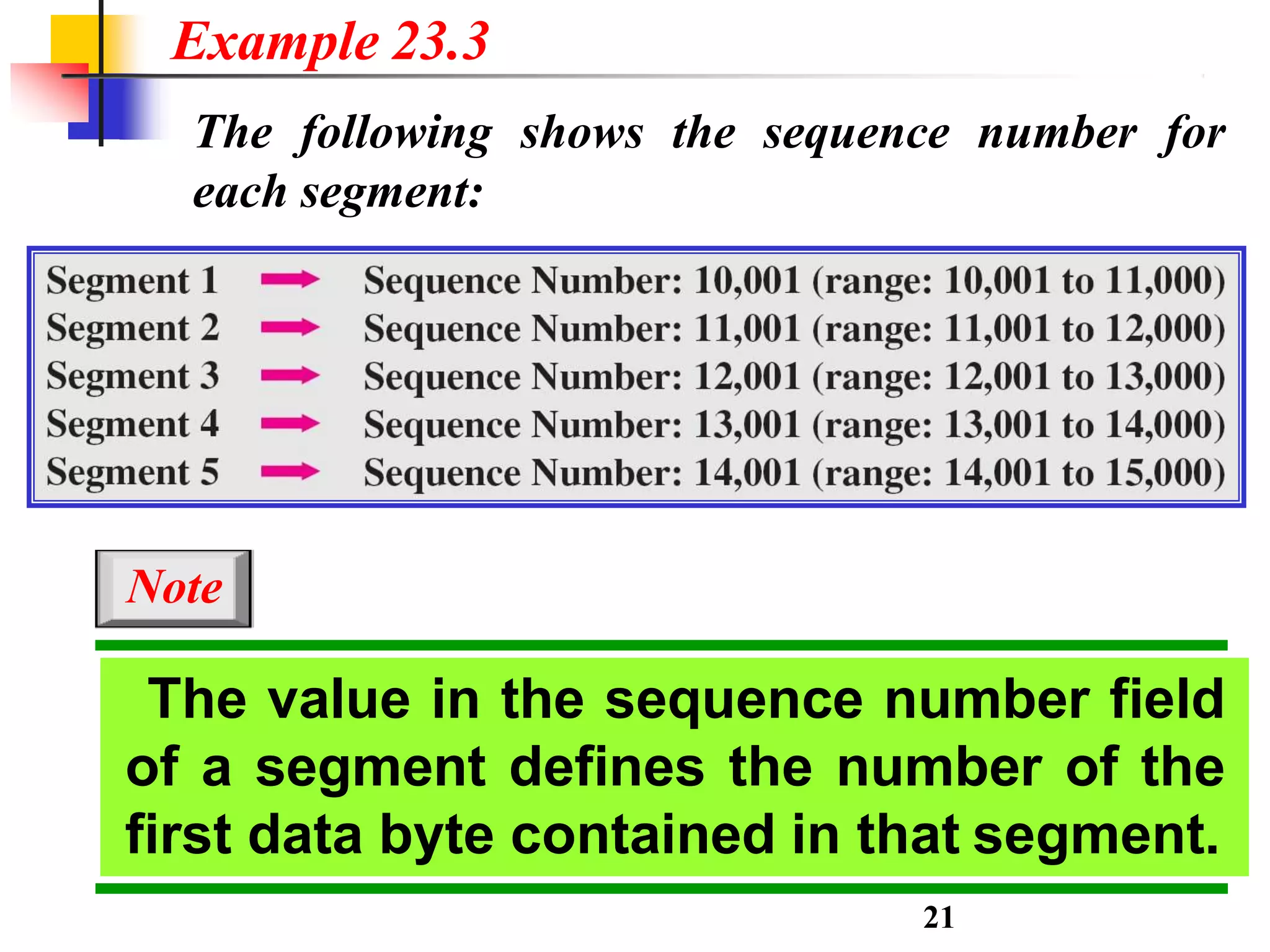
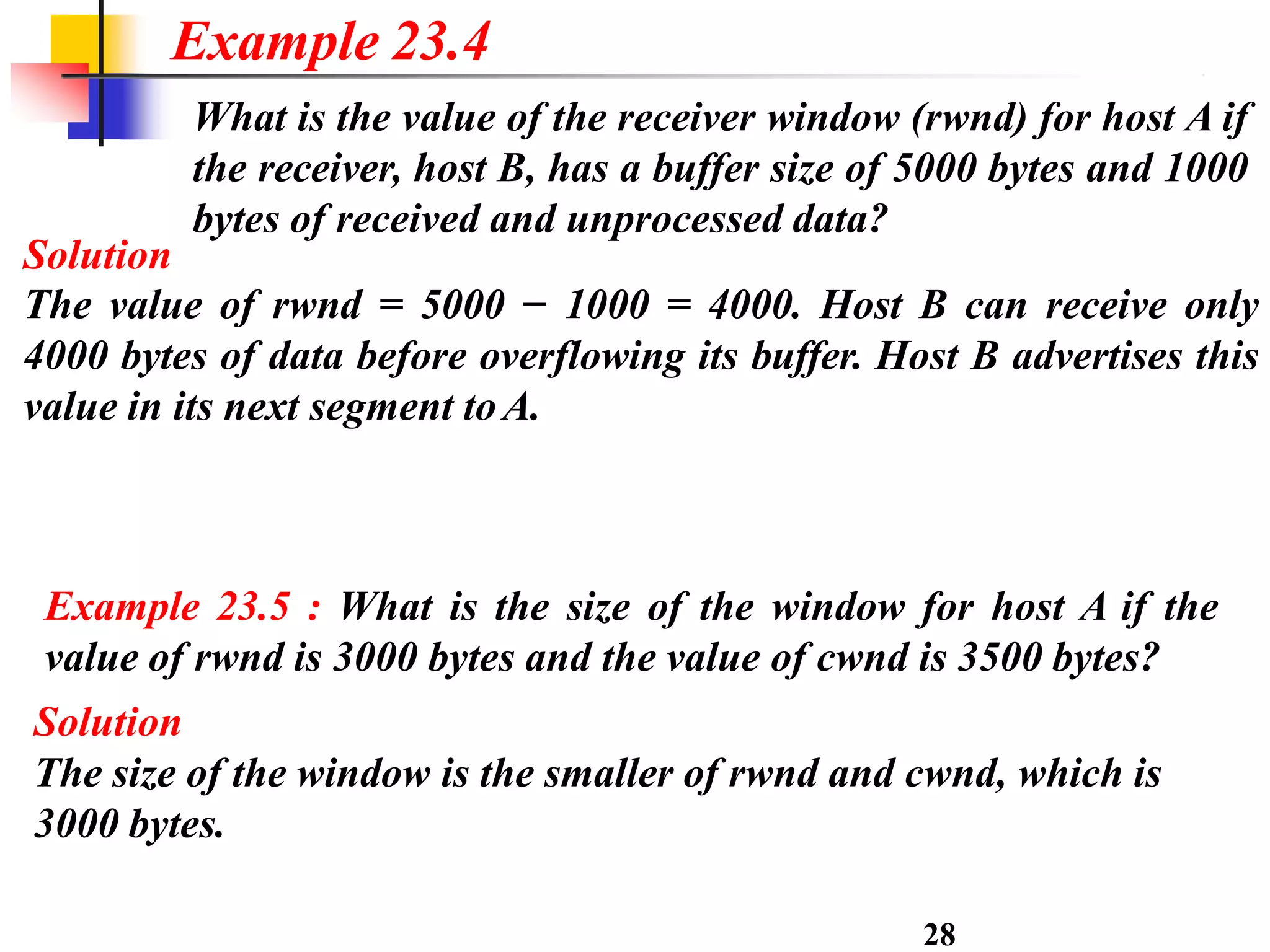
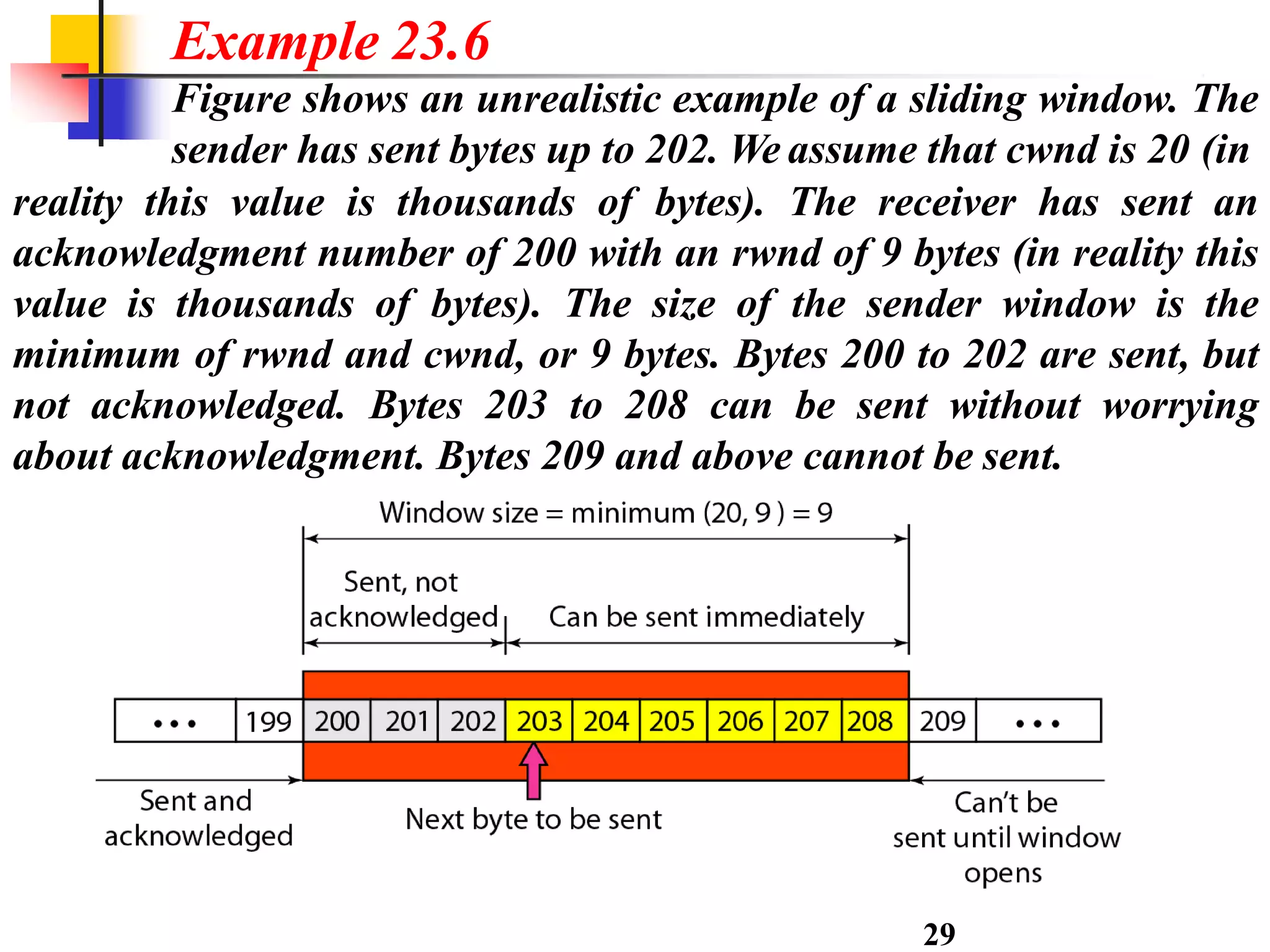
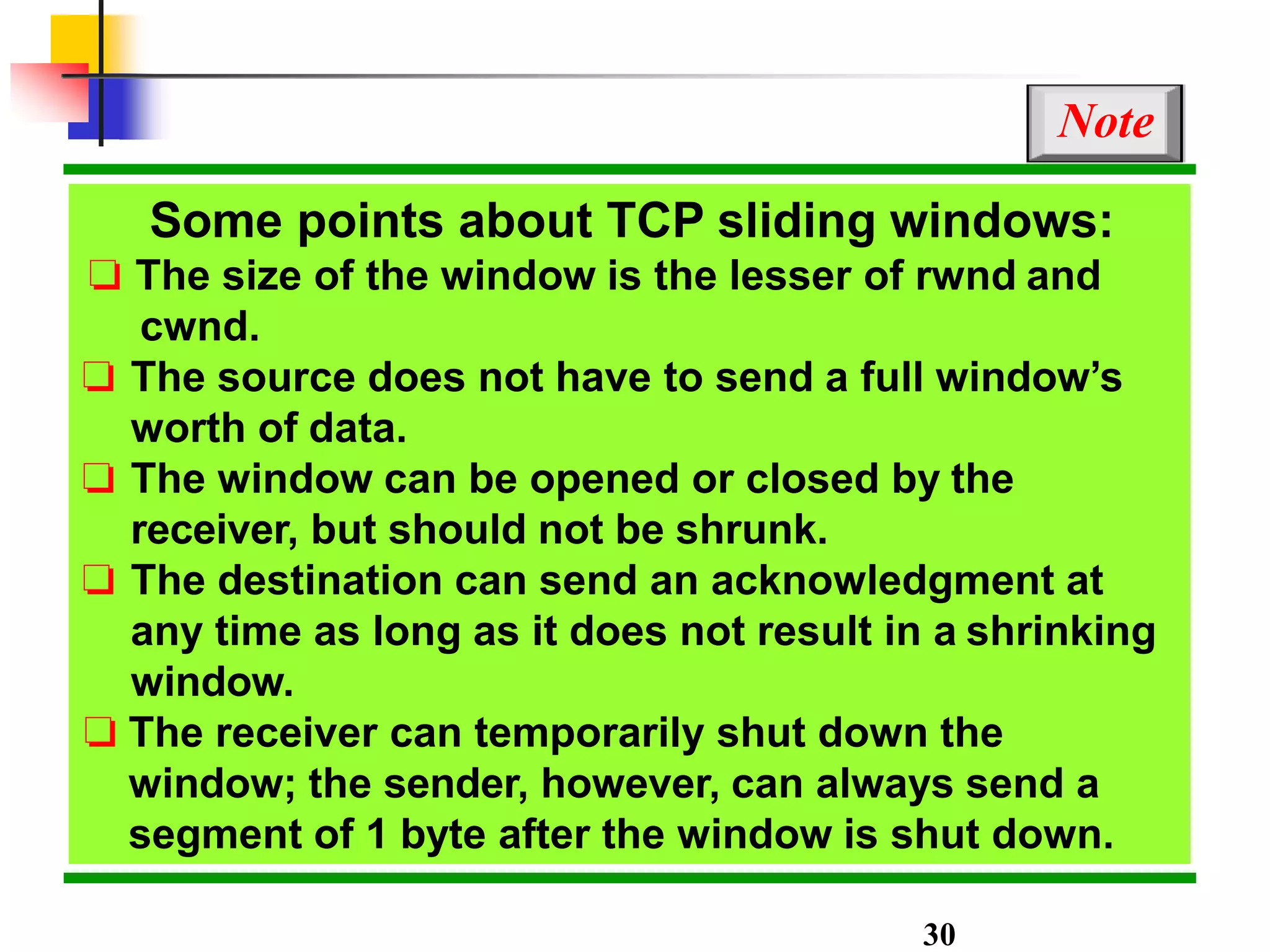
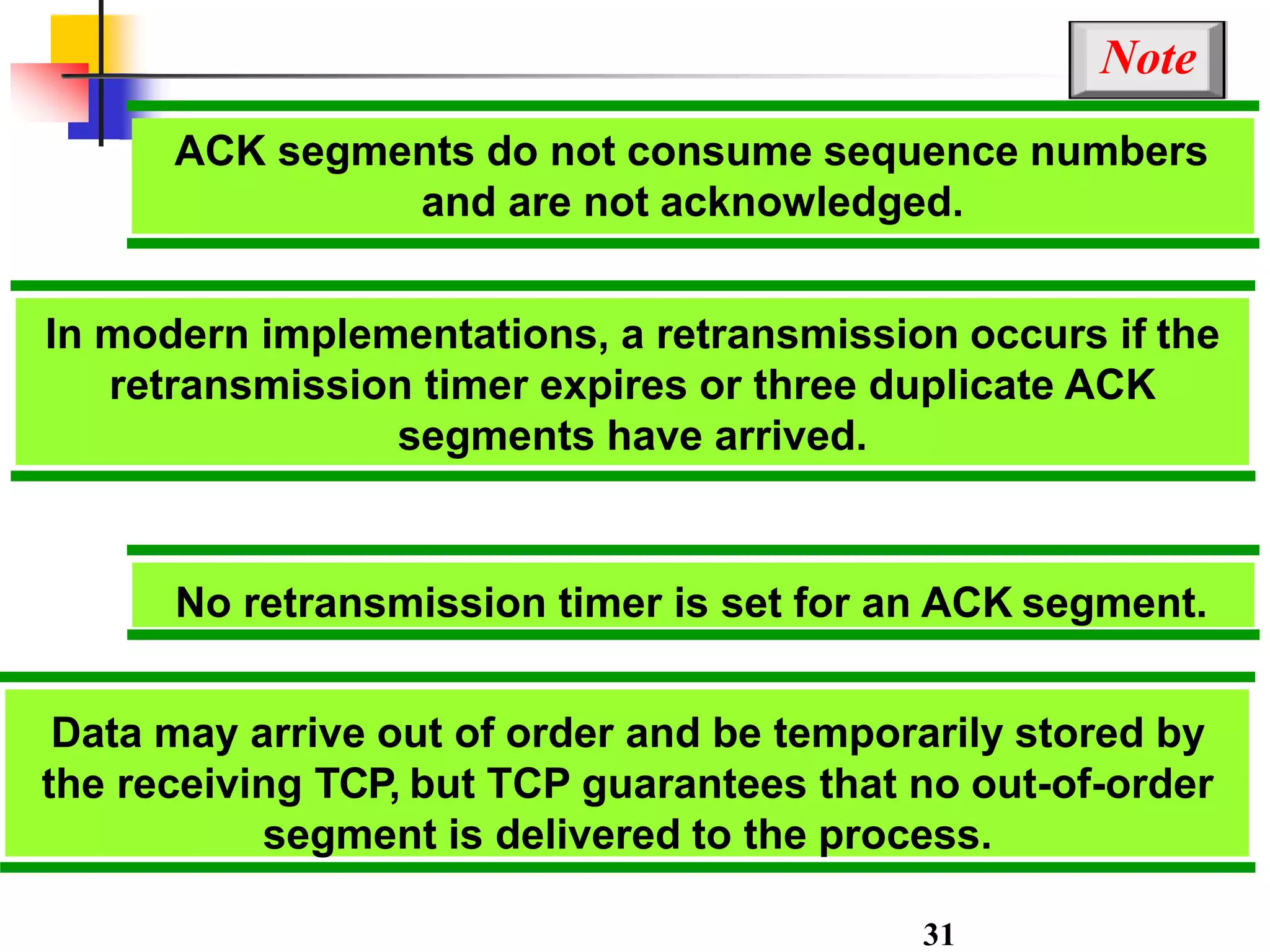
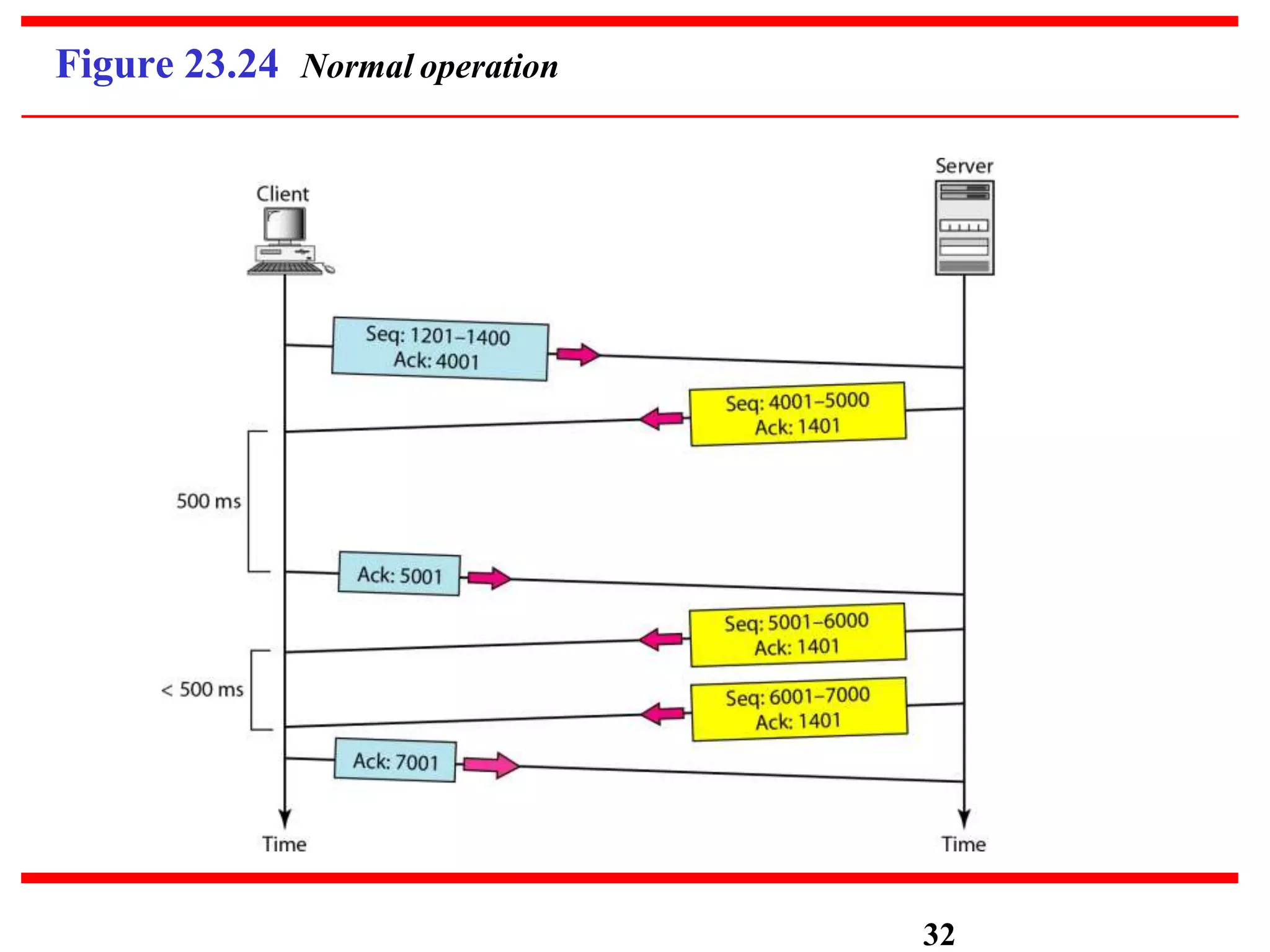
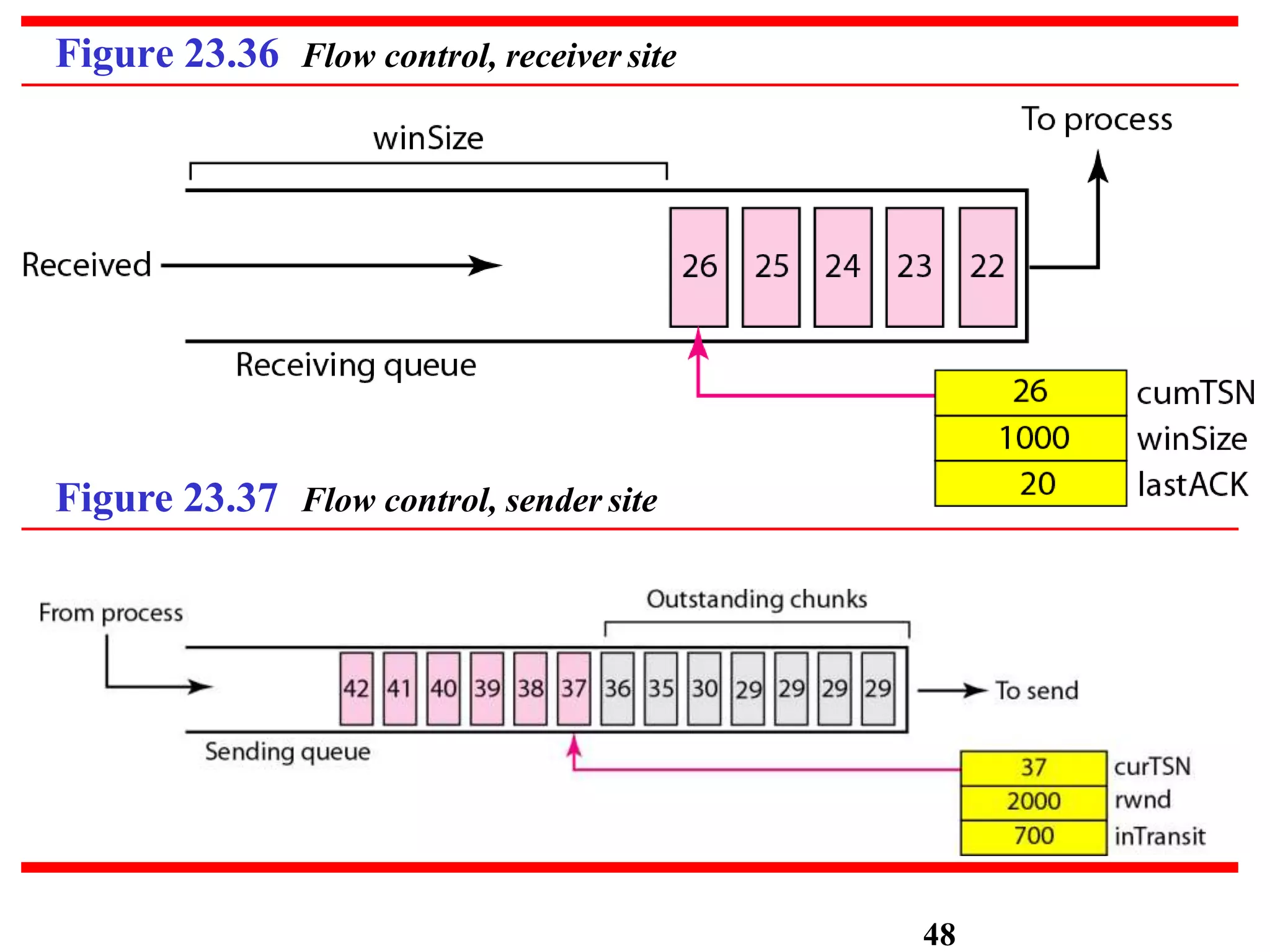
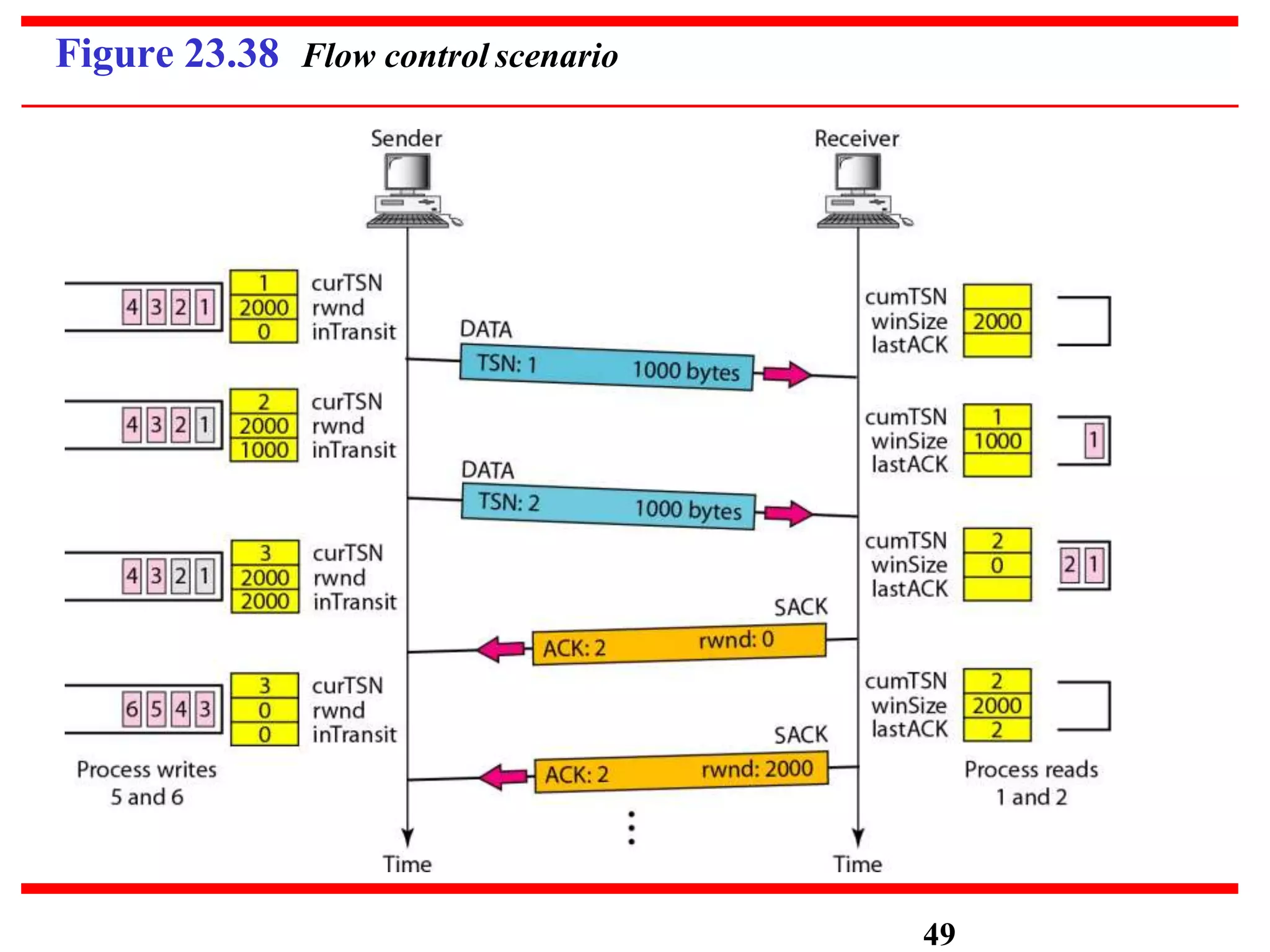
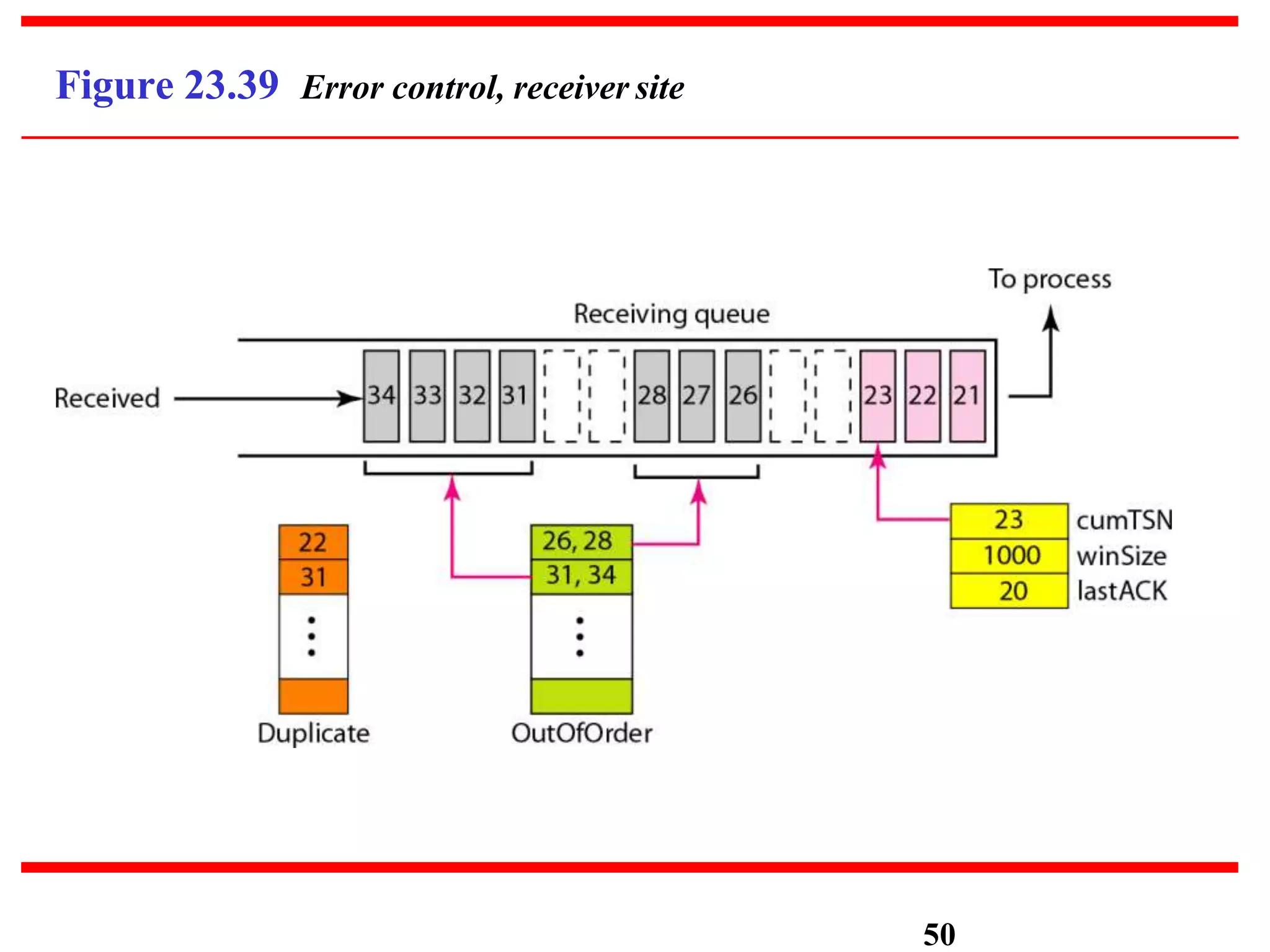
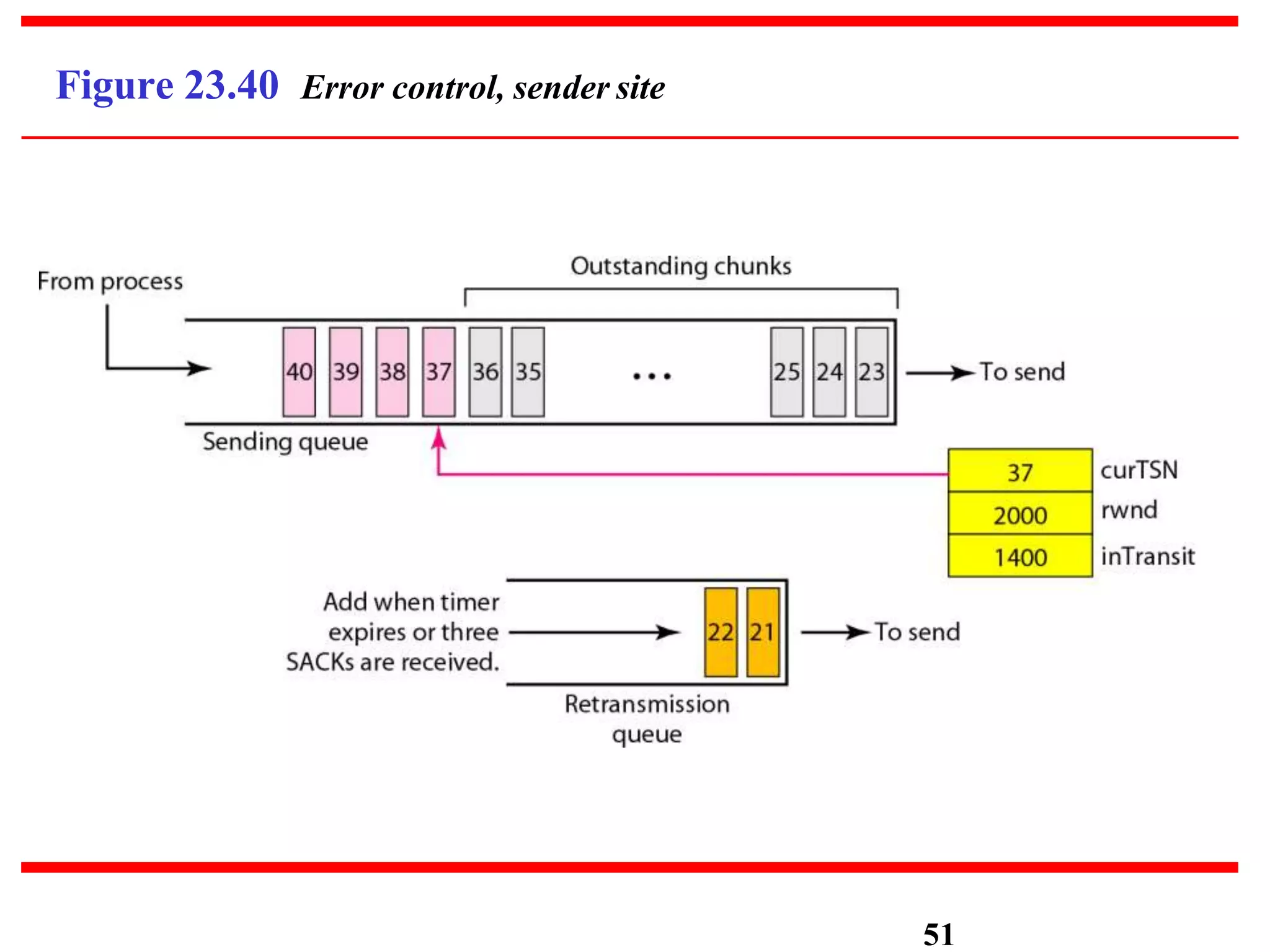
- Key concepts like multiplexing, demultiplexing, connectionless vs connection-oriented services, ports, and transport layer functions like flow control and error control are explained for each protocol.