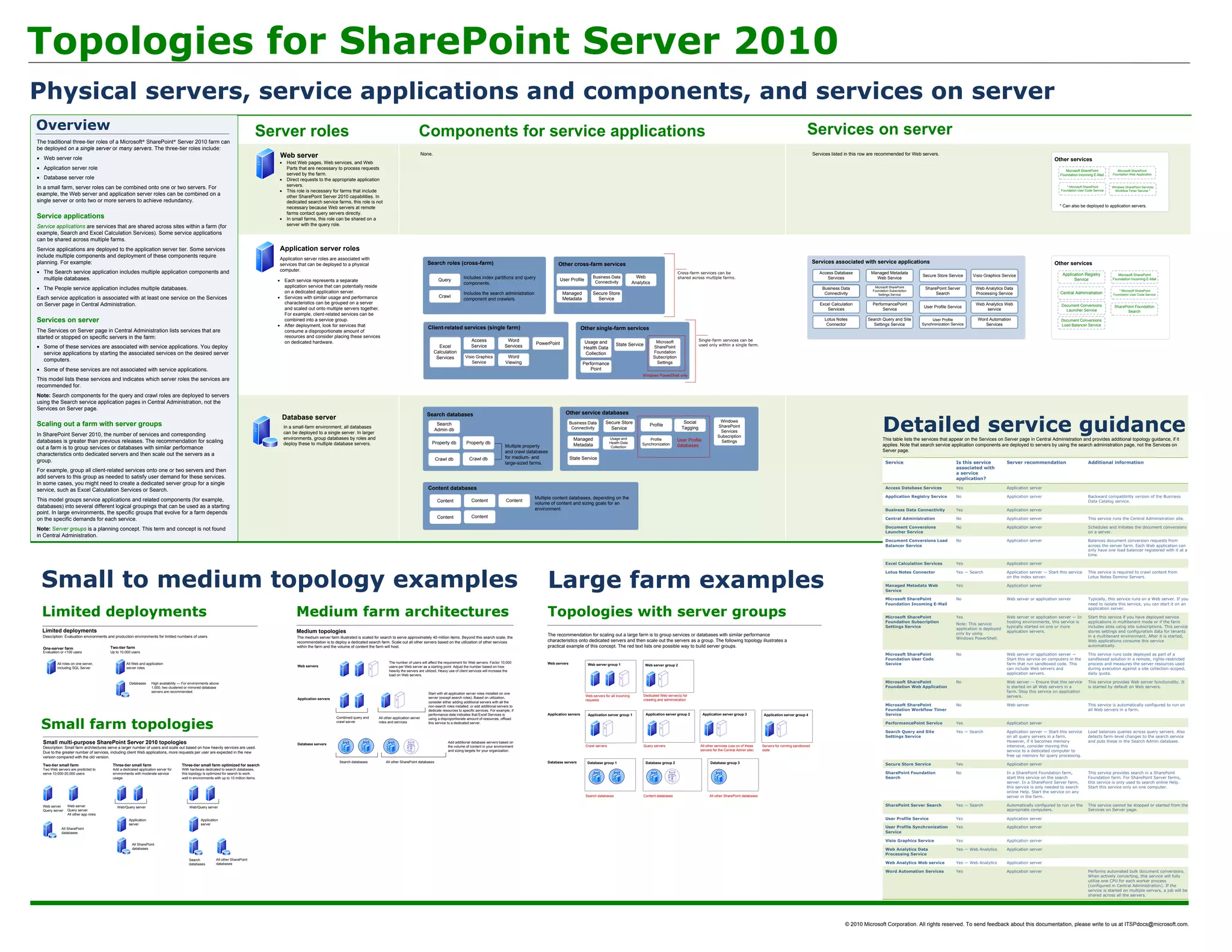
This document provides an overview of topologies for SharePoint Server 2010, including:
1) Server roles like web, application, and database servers that can be combined on small farms or separated on larger farms with dedicated servers.
2) Service applications that are deployed to application servers and include multiple components.
3) Services associated with service applications or that run independently on servers.
4) Recommendations for grouping services and databases with similar performance onto server groups that can be scaled out.
3) Examples of small, medium, and large farm topologies with different server configurations.