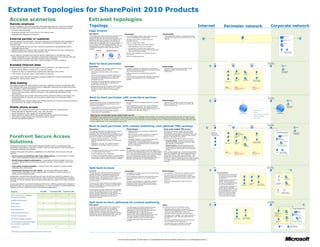
An extranet topology allows remote employees and external partners to access corporate resources securely over the internet. There are two main topology options:
1) An edge firewall topology places a reverse proxy server at the edge of the corporate network to intercept requests and forward them to internal web servers. This is the simplest option but has a single point of access.
2) A back-to-back perimeter topology isolates an extranet web server farm in a separate perimeter network, requiring more network infrastructure but providing additional isolation of extranet content and users.