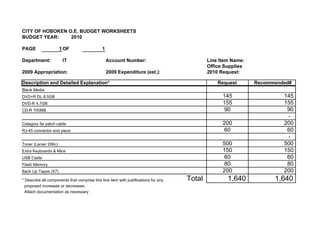
The IT Department of the City of Hoboken has submitted its proposed budget for 2010. The budget includes line items for office supplies, office equipment, annual subscriptions, software, and Channel 78 equipment. Some of the largest requests are $3,500 for an intrusion detection appliance, $2,600 for a SAN storage device, $2,500 for Norton's anti-virus licensing, and $2,474 for a Sony DV camcorder. If approved, the total IT Department budget request for 2010 would be $27,446.