2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
•
5 likes•3,600 views
Check Point Software Technologies Ltd. - 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
Report
Share
Report
Share
Download to read offline
Recommended
Cyber & Process Attack Scenarios for ICS

Presented at the OPC Foundation's "The Information Revolution 2014" in Redmond, WA August 5-6, 2014
This presentation discusses the modes and methodologies an attacker may use against an industrial control system in order to create a complex process attack. The presentation then discusses some specific examples, both real and hypothetical. The presentation finishes with a description of some common ways in which an organization could defend itself against these types of attacks.
Cybersecurity for modern industrial systems

Cybersecurity for Modern Industrial Systems
Attaining reliable safety in cyber infrastructure.
Cybersecurity in Industrial Control Systems (ICS)

Presented at ISACA's EuroCACS 2015 (Copenhaguen).
Understand the impact of Industrial Control Systems (ICS) on the security ecosystem.
Expand the knowledge on SCADA systems and how cyberattacks can have physical consequences, bridging the cyber and physical worlds.
Hacker Halted 2016 - How to get into ICS security

This talk is about how to get into ICS security, whether you’re a control system engineer or an IT security analyst. It will cover the basic paths you can take to get involved, including some helpful resources and standards to help get you started. The ICS Security industry needs more people to help protect Critical Infrastructure!
SANS ICS Security Survey Report 2016 

Presentation on findings of the annual survey of ICS Security professionals. Includes participant demographics, greatest ICS security threats, and security initiatives.
Protecting Infrastructure from Cyber Attacks

The Department of Homeland Security (DHS) has become more concerned with cyber attacks on infrastructure such as supervisory control and data acquisition (SCADA) systems. An attack in Iran has proven that the landscape of cyber warfare is continually evolving. As the SCADA systems are the systems that autonomously monitor and adjust switching among other processes within critical infrastructures such as nuclear plants, and power grids DHS has become concerned about these systems as they are unmanned frequently and remotely accessed. A vulnerability such as remote access could allow anyone to take control of assets to critical infrastructure remotely. There has been increasing mandates, and directives to ensure any system deployed meets stringent requirements. As the Stuxnet worm has become a reality, future attacks could be malicious code directly targeting specific locations of critical infrastructure. This paper will address methods to protect infrastructure from cyber attacks using a hybrid of certification & accreditation (C&A) processes and information assurance (IA) controls.
Recommended
Cyber & Process Attack Scenarios for ICS

Presented at the OPC Foundation's "The Information Revolution 2014" in Redmond, WA August 5-6, 2014
This presentation discusses the modes and methodologies an attacker may use against an industrial control system in order to create a complex process attack. The presentation then discusses some specific examples, both real and hypothetical. The presentation finishes with a description of some common ways in which an organization could defend itself against these types of attacks.
Cybersecurity for modern industrial systems

Cybersecurity for Modern Industrial Systems
Attaining reliable safety in cyber infrastructure.
Cybersecurity in Industrial Control Systems (ICS)

Presented at ISACA's EuroCACS 2015 (Copenhaguen).
Understand the impact of Industrial Control Systems (ICS) on the security ecosystem.
Expand the knowledge on SCADA systems and how cyberattacks can have physical consequences, bridging the cyber and physical worlds.
Hacker Halted 2016 - How to get into ICS security

This talk is about how to get into ICS security, whether you’re a control system engineer or an IT security analyst. It will cover the basic paths you can take to get involved, including some helpful resources and standards to help get you started. The ICS Security industry needs more people to help protect Critical Infrastructure!
SANS ICS Security Survey Report 2016 

Presentation on findings of the annual survey of ICS Security professionals. Includes participant demographics, greatest ICS security threats, and security initiatives.
Protecting Infrastructure from Cyber Attacks

The Department of Homeland Security (DHS) has become more concerned with cyber attacks on infrastructure such as supervisory control and data acquisition (SCADA) systems. An attack in Iran has proven that the landscape of cyber warfare is continually evolving. As the SCADA systems are the systems that autonomously monitor and adjust switching among other processes within critical infrastructures such as nuclear plants, and power grids DHS has become concerned about these systems as they are unmanned frequently and remotely accessed. A vulnerability such as remote access could allow anyone to take control of assets to critical infrastructure remotely. There has been increasing mandates, and directives to ensure any system deployed meets stringent requirements. As the Stuxnet worm has become a reality, future attacks could be malicious code directly targeting specific locations of critical infrastructure. This paper will address methods to protect infrastructure from cyber attacks using a hybrid of certification & accreditation (C&A) processes and information assurance (IA) controls.
Should I Patch My ICS?

The answer is no for about 90% of the cyber assets due to the very minimal risk reduction achieved. Spend your effort elsewhere. Presentation goes over categories of security patching in ICS and recommends prioritized security patching.
Scada security presentation by Stephen Miller

SCADA Security presentation by Stephen Miller of the Cyber Security Center of Excellence for InduSoft.
NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler

Kevin Wheeler, Founder and Managing Director, InfoDefense
Securing Industrial Control Systems
Our nation’s critical infrastructure is controlled by SCADA and other industrial control technologies. Water utilities, petroleum refineries, oil pipelines, food processors, manufacturers and power companies all use SCADA systems to control and monitor operations. The vast majority of these industrial control systems have been in place for decades with few, if any, enhancements to effectively protect against today’s advanced threats. As a result, industrial control system vulnerabilities are currently a major concern.
Legacy SCADA systems can be secured using many of the same best practices that are used to protect the enterprise. This presentation provides an overview of SCADA threats as well as practical solutions for protecting industrial control systems.
Securing Industrial Control Systems

This slideshow was presented February 2, 2016 and developed for the Iowa Infragard team and discusses the Importance of Security Cyber-Physical Control systems, Elements of a control system, the manufacturing supply chain and consequences of cyber attacks in industrial environments. Please feel free to reach out with questions or comments.
Industrial Control System Security Overview

Industrial Control System Security Overview
5th World Cyber Security Summit Belfast, March 2015
ICS (Industrial Control System) Cybersecurity Training

ICS Cybersecurity training is intended for security professionals and control system designs in order to give them propelled cybersecurity aptitudes and learning in order to ensure the Industrial Control System (ICS) and keep their mechanical task condition secure against digital dangers.
Audience:
Control engineers, integrators and architects
System administrators, engineers
Information Technology (IT) professionals
Security Consultants
Managers who are responsible for ICS
Researchers and analysts working on ICS security
Vendors, Executives and managers
Information technology professionals, security engineers, security analysts, policy analysts
Investors and contractors
Technicians, operators, and maintenance personnel
Price: $3,999.00 Length: 4 Days
Training Objectives:
Understand fundamentals of Industrial Control Systems (ICS)
Recognize the security architecture for ICS
Identify different kinds of vulnerabilities in ICS network, remote devices, software, or control servers
Learn about active defense and incident response for ICS
Learn the essentials for NERC Critical Infrastructure Protection (CIP)
Understand policies and procedures for NERC critical infrastructure protection (CIP)
List strategies for NERC CIP version 5/6
Apply risk management techniques to ICS
Describe ICS Active Defense and Incident Response
Describe techniques for defending against the new ICS threat matrix
Assess and audit risks for ICS
Apply IEC standard to network and system security of ICS
Implement the ICS security program step by step
Protect the ICS network from vulnerabilities
Understand different types of servers in ICS and protect them against attacks
Apply security standards to SCADA systems based on NIST SP 800-82
Detect different types of attacks to SCADA systems
Tackle all the security challenges related to ICS cybersecurity
Training Outline:
ICS Cybersecurity training course consists of the following lessons, which can be revised and tailored to the client’s need:
Fundamentals of Industrial Control Systems (ICS)
ICS Security Architecture
Common ICS Vulnerabilities
ICS Threat Intelligence
NERC Critical Infrastructure Protection (CIP)
Risk Management and Risk Assessment
ICS Auditing and Assessment
IEC 62443: Network and System Security for ICS
Implementation of ICS Security Program Development
ICS Incident Response
Network Protection for ICS
ICS Server Protection
SCADA Security Policies and Standards
Detection of Cyber Attacks on SCADA Systems
Our instructors at Tonex will assist you with mastering every one of the ICS Cybersecurity plan strategies by presenting the hazard administration framework, chance evaluation methods, episode reaction, constant monitoring, SCADA security change, and network security approaches for ICS.
ICS Cyber security Training
https://www.tonex.com/training-courses/ics-cybersecurity-training/
Industrial Control Cyber Security Europe 2015 

The Industrial Control Cybersecurity conference consists of presentations and debate from some of the energy industry’s leading end users from Operational and IT backgrounds, Government influencers, leading cybersecurity authorities and some of the world’s most influential solution providers.
Key topics of discussion will pivot on convergence of operational and information technology transformation, design, implementation, integration and risks associated with enterprise facing architecture.
Further review includes the development of policy, operational and cultural considerations, maturity models, public and private information sharing and the adoption of cybersecurity controls.
2015 will provide further insight into how industry can further develop organisational priorities, effective methodologies, benchmark return on investment for cybersecurity procurement, supplier relationships and how to effectively deploy defense in-depth strategies.
We will introduce discussion on the latest attacks and hear from those who are responsible for identifying them. The conference will further address penetration testing, the art of detection and threat monitoring, incident response and recovery.
IT vs. OT: ICS Cyber Security in TSOs

by G. Caroti
Corporate Security – Head of Information Security - TERNA
SCADA Security: The Five Stages of Cyber Grief

Every time a new information technology finds its way into production, it seems as though we end up repeating the same process – security vulnerabilities will be discovered and disclosed in that technology, and users and vendors will deny that the risks are significant. Only after major attacks occur do we really start to see efforts to address the inherent risks in a systematic way.
We’re falling into this exact same trap again with Industrial Control and SCADA systems, but in this case the problem is worse, because the inherent nature of control systems prevents us from applying many of the strategies that have been used to protect other kinds of computer networks.
Join Lancope’s Director of Security Research, Tom Cross, for a look at the five stages of grief that organizations seem to pass through as they come to terms with security risks, and how far we’ve come regarding Industrial Control Systems.
Hear about:
The state of Control Systems security vulnerabilities
Attack activity that is prompting a change in perspective
The unique, long-term challenges associated with protecting SCADA networks
How anomaly detection can play a key role in protecting SCADA systems now
Robust Cyber Security for Power Utilities

The security of critical networks is at the center of attention of industry and government regulators alike. Check Point and RAD offer a joint end-to-end cyber security solution that protects any utility operational technology (OT) network by eliminating RTU and SCADA equipment vulnerabilities, as well as defends against cyber-attacks on the network’s control and data planes. This solution brief explains how the joint solution enables compliance with NERC-CIP directives, provides deep visibility and control of ICS/SCADA communications, and allows secure remote access into OT networks.
The journey to ICS - Extended 

This presentation was given at BSides Las Vegas 2015.
The modern times that we live in, the gentle shift that we are making towards the Internet of Things (IoT) is slowly but surely getting a grip on our day to day lives. The same goes for securing our Industrial Control Systems (ICS). We see that the demand for ICS security is raising and governmental regulations are being established and implement. However, this also means that the need for ICS security professionals is raising as well. More and more security professionals/firms are starting to perform security assessments such as penetration testing on an ICS level. Two years ago I got the question if I was up for the challenge, converting myself from a ‘normal’ security professional to a ICS specific security professional.
The purpose of this talk would be to provide a starting point for security professionals that want to make the shift towards ICS Security, just like I did two years ago. While the term starting point might be a bit misleading, the goal would be to provide an ICS 001 talk instead in contrast to an ICS 101 talk.
SCADA Security Webinar

SCADA Security Presented by Vern Williams, Chief Security Officer, CyberDefenses, Inc (CDI)
Nozomi Fortinet Accelerate18

Nozomi Networks extends the Fortinet Cybersecurity Fabric with innovative ICS/OT protocol intelligence and network visualization capabilities.
DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...

DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 and ICS Security IEC62443 standards
Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...

Presented @ Emerson Exchange
October 7, 2014
Industrial control systems (ICS) are large information technology (IT) systems. Office IT systems, failure of ICS can cause plant outages and even physical damage. Management of ICS needs to be different and smarter. IT vendors frequently recommend patches and configuration changes. Most have no impact to the ICS, which cannot implement changes in real time. ICS typically get one chance every few years to make changes - the turnaround. This paper describes optimization of ISC turnaround work, using cyber-vulnerability assessment to focus turnaround work to only what is necessary.
Nozomi Networks Q1_2018 Company Introduction

Nozomi Networks is the leader of industrial cybersecurity, delivering real-time visibility to manage cyber risk & improve resilience for industrial operations. With one solution, customers gain advanced cybersecurity, improved operational reliability & easy IT/OT integration. Innovating the use of artificial intelligence, the company helps the largest industrial sites around the world See and Secure™ their critical industrial control networks. Today Nozomi Networks supports over a quarter of a million devices in the critical infrastructure, energy, manufacturing, mining, transportation & utility sectors, making it possible to tackle the escalating cyber risks to operational networks (OT).
Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...

There are new threats to cybersecurity for HMI/SCADA applications every week, and it can be difficult to stay on top of current threats and concerns. InduSoft is here to help, with an analysis of recent cybersecurity threats and how to take steps to protect SCADA/HMI systems from the vulnerabilities they seek to exploit. We will also be discussing the security features available in InduSoft Web Studio and how to take advantage of them to create the most stable, secure HMI or SCADA application possible.
Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...

ICS SCADA Cyber Security Solutions and Challenges
Cyber Security Threats to Industrial Control Systems

Every day we are hearing in the media of potential Cyber Security threats to Critical National Infrastructure such as power grids, airlines and nuclear power stations. David has spent over 40 years working in the ICS environments. He was invited to speak in London at the British Computer Society cyber event these are the slides.
More Related Content
What's hot
Should I Patch My ICS?

The answer is no for about 90% of the cyber assets due to the very minimal risk reduction achieved. Spend your effort elsewhere. Presentation goes over categories of security patching in ICS and recommends prioritized security patching.
Scada security presentation by Stephen Miller

SCADA Security presentation by Stephen Miller of the Cyber Security Center of Excellence for InduSoft.
NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler

Kevin Wheeler, Founder and Managing Director, InfoDefense
Securing Industrial Control Systems
Our nation’s critical infrastructure is controlled by SCADA and other industrial control technologies. Water utilities, petroleum refineries, oil pipelines, food processors, manufacturers and power companies all use SCADA systems to control and monitor operations. The vast majority of these industrial control systems have been in place for decades with few, if any, enhancements to effectively protect against today’s advanced threats. As a result, industrial control system vulnerabilities are currently a major concern.
Legacy SCADA systems can be secured using many of the same best practices that are used to protect the enterprise. This presentation provides an overview of SCADA threats as well as practical solutions for protecting industrial control systems.
Securing Industrial Control Systems

This slideshow was presented February 2, 2016 and developed for the Iowa Infragard team and discusses the Importance of Security Cyber-Physical Control systems, Elements of a control system, the manufacturing supply chain and consequences of cyber attacks in industrial environments. Please feel free to reach out with questions or comments.
Industrial Control System Security Overview

Industrial Control System Security Overview
5th World Cyber Security Summit Belfast, March 2015
ICS (Industrial Control System) Cybersecurity Training

ICS Cybersecurity training is intended for security professionals and control system designs in order to give them propelled cybersecurity aptitudes and learning in order to ensure the Industrial Control System (ICS) and keep their mechanical task condition secure against digital dangers.
Audience:
Control engineers, integrators and architects
System administrators, engineers
Information Technology (IT) professionals
Security Consultants
Managers who are responsible for ICS
Researchers and analysts working on ICS security
Vendors, Executives and managers
Information technology professionals, security engineers, security analysts, policy analysts
Investors and contractors
Technicians, operators, and maintenance personnel
Price: $3,999.00 Length: 4 Days
Training Objectives:
Understand fundamentals of Industrial Control Systems (ICS)
Recognize the security architecture for ICS
Identify different kinds of vulnerabilities in ICS network, remote devices, software, or control servers
Learn about active defense and incident response for ICS
Learn the essentials for NERC Critical Infrastructure Protection (CIP)
Understand policies and procedures for NERC critical infrastructure protection (CIP)
List strategies for NERC CIP version 5/6
Apply risk management techniques to ICS
Describe ICS Active Defense and Incident Response
Describe techniques for defending against the new ICS threat matrix
Assess and audit risks for ICS
Apply IEC standard to network and system security of ICS
Implement the ICS security program step by step
Protect the ICS network from vulnerabilities
Understand different types of servers in ICS and protect them against attacks
Apply security standards to SCADA systems based on NIST SP 800-82
Detect different types of attacks to SCADA systems
Tackle all the security challenges related to ICS cybersecurity
Training Outline:
ICS Cybersecurity training course consists of the following lessons, which can be revised and tailored to the client’s need:
Fundamentals of Industrial Control Systems (ICS)
ICS Security Architecture
Common ICS Vulnerabilities
ICS Threat Intelligence
NERC Critical Infrastructure Protection (CIP)
Risk Management and Risk Assessment
ICS Auditing and Assessment
IEC 62443: Network and System Security for ICS
Implementation of ICS Security Program Development
ICS Incident Response
Network Protection for ICS
ICS Server Protection
SCADA Security Policies and Standards
Detection of Cyber Attacks on SCADA Systems
Our instructors at Tonex will assist you with mastering every one of the ICS Cybersecurity plan strategies by presenting the hazard administration framework, chance evaluation methods, episode reaction, constant monitoring, SCADA security change, and network security approaches for ICS.
ICS Cyber security Training
https://www.tonex.com/training-courses/ics-cybersecurity-training/
Industrial Control Cyber Security Europe 2015 

The Industrial Control Cybersecurity conference consists of presentations and debate from some of the energy industry’s leading end users from Operational and IT backgrounds, Government influencers, leading cybersecurity authorities and some of the world’s most influential solution providers.
Key topics of discussion will pivot on convergence of operational and information technology transformation, design, implementation, integration and risks associated with enterprise facing architecture.
Further review includes the development of policy, operational and cultural considerations, maturity models, public and private information sharing and the adoption of cybersecurity controls.
2015 will provide further insight into how industry can further develop organisational priorities, effective methodologies, benchmark return on investment for cybersecurity procurement, supplier relationships and how to effectively deploy defense in-depth strategies.
We will introduce discussion on the latest attacks and hear from those who are responsible for identifying them. The conference will further address penetration testing, the art of detection and threat monitoring, incident response and recovery.
IT vs. OT: ICS Cyber Security in TSOs

by G. Caroti
Corporate Security – Head of Information Security - TERNA
SCADA Security: The Five Stages of Cyber Grief

Every time a new information technology finds its way into production, it seems as though we end up repeating the same process – security vulnerabilities will be discovered and disclosed in that technology, and users and vendors will deny that the risks are significant. Only after major attacks occur do we really start to see efforts to address the inherent risks in a systematic way.
We’re falling into this exact same trap again with Industrial Control and SCADA systems, but in this case the problem is worse, because the inherent nature of control systems prevents us from applying many of the strategies that have been used to protect other kinds of computer networks.
Join Lancope’s Director of Security Research, Tom Cross, for a look at the five stages of grief that organizations seem to pass through as they come to terms with security risks, and how far we’ve come regarding Industrial Control Systems.
Hear about:
The state of Control Systems security vulnerabilities
Attack activity that is prompting a change in perspective
The unique, long-term challenges associated with protecting SCADA networks
How anomaly detection can play a key role in protecting SCADA systems now
Robust Cyber Security for Power Utilities

The security of critical networks is at the center of attention of industry and government regulators alike. Check Point and RAD offer a joint end-to-end cyber security solution that protects any utility operational technology (OT) network by eliminating RTU and SCADA equipment vulnerabilities, as well as defends against cyber-attacks on the network’s control and data planes. This solution brief explains how the joint solution enables compliance with NERC-CIP directives, provides deep visibility and control of ICS/SCADA communications, and allows secure remote access into OT networks.
The journey to ICS - Extended 

This presentation was given at BSides Las Vegas 2015.
The modern times that we live in, the gentle shift that we are making towards the Internet of Things (IoT) is slowly but surely getting a grip on our day to day lives. The same goes for securing our Industrial Control Systems (ICS). We see that the demand for ICS security is raising and governmental regulations are being established and implement. However, this also means that the need for ICS security professionals is raising as well. More and more security professionals/firms are starting to perform security assessments such as penetration testing on an ICS level. Two years ago I got the question if I was up for the challenge, converting myself from a ‘normal’ security professional to a ICS specific security professional.
The purpose of this talk would be to provide a starting point for security professionals that want to make the shift towards ICS Security, just like I did two years ago. While the term starting point might be a bit misleading, the goal would be to provide an ICS 001 talk instead in contrast to an ICS 101 talk.
SCADA Security Webinar

SCADA Security Presented by Vern Williams, Chief Security Officer, CyberDefenses, Inc (CDI)
Nozomi Fortinet Accelerate18

Nozomi Networks extends the Fortinet Cybersecurity Fabric with innovative ICS/OT protocol intelligence and network visualization capabilities.
DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...

DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 and ICS Security IEC62443 standards
Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...

Presented @ Emerson Exchange
October 7, 2014
Industrial control systems (ICS) are large information technology (IT) systems. Office IT systems, failure of ICS can cause plant outages and even physical damage. Management of ICS needs to be different and smarter. IT vendors frequently recommend patches and configuration changes. Most have no impact to the ICS, which cannot implement changes in real time. ICS typically get one chance every few years to make changes - the turnaround. This paper describes optimization of ISC turnaround work, using cyber-vulnerability assessment to focus turnaround work to only what is necessary.
Nozomi Networks Q1_2018 Company Introduction

Nozomi Networks is the leader of industrial cybersecurity, delivering real-time visibility to manage cyber risk & improve resilience for industrial operations. With one solution, customers gain advanced cybersecurity, improved operational reliability & easy IT/OT integration. Innovating the use of artificial intelligence, the company helps the largest industrial sites around the world See and Secure™ their critical industrial control networks. Today Nozomi Networks supports over a quarter of a million devices in the critical infrastructure, energy, manufacturing, mining, transportation & utility sectors, making it possible to tackle the escalating cyber risks to operational networks (OT).
Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...

There are new threats to cybersecurity for HMI/SCADA applications every week, and it can be difficult to stay on top of current threats and concerns. InduSoft is here to help, with an analysis of recent cybersecurity threats and how to take steps to protect SCADA/HMI systems from the vulnerabilities they seek to exploit. We will also be discussing the security features available in InduSoft Web Studio and how to take advantage of them to create the most stable, secure HMI or SCADA application possible.
What's hot (20)
Guide scada and_industrial_control_systems_security

Guide scada and_industrial_control_systems_security
NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler

NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler
ICS (Industrial Control System) Cybersecurity Training

ICS (Industrial Control System) Cybersecurity Training
Industrial Control Security USA Sacramento California Oct 13/14

Industrial Control Security USA Sacramento California Oct 13/14
DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...

DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...
Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...

Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...
Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...

Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...
Viewers also liked
Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...

ICS SCADA Cyber Security Solutions and Challenges
Cyber Security Threats to Industrial Control Systems

Every day we are hearing in the media of potential Cyber Security threats to Critical National Infrastructure such as power grids, airlines and nuclear power stations. David has spent over 40 years working in the ICS environments. He was invited to speak in London at the British Computer Society cyber event these are the slides.
Hacking Critical Infrastructure Like You’re Not a N00b

This presentation is targeted towards an audience that already understands how to compromise the embedded systems that run a process and now is looking at manipulating the physics of the process itself. In as much as time allows, it will cover all the things necessary to accomplish more than exercising the automatic shutdown logic of a process.
(Source: RSA USA 2016-San Francisco)
VIVA LA COMPLEJIDAD ! BIG DATA Y TECNOLOGÍA : ELEFANTES EN CIUDADES DE PORCE...

Professor Carlos Moreno
Consejero Cientifico del Presidente de COFELY INEO, Grupo GDF SUEZ
Miembro del Consejo Francés Superior de la Formacion e Investigacion Esratégica
�
Madrid 2014
Evaluating System-Level Cyber Security vs. ANSI/ISA-62443-3-3

With the recent publication of ANSI/ISA-62443-3-3-2013, it is possible for end-users, system integrators, and vendors to qualify the capabilities of their systems from an ICS cyber security perspective. This process is not as simple as it may seem, though. In many cases, the capabilities of individual components of a system can be determined from specifications and manuals. The capabilities of the system also needs to be evaluated as a whole to determine how those individual components work together. Component-level and System-level certifications are common practice in the safety environment, and will eventually become common in the ICS cyber security environment as well. Certification bodies, like the ISA Security Compliance Institute (ISCI), have begun the process to develop certification efforts around ISA-62443-3-3. Until many more groups of components and systems have been officially certified, third-party assessments and evaluations will be common. This presentation will discuss an example of how Kenexis Consulting has evaluated a particular vendor’s components and systems to determine compliance with ISA-62443-3-3. The presentation will go through the evaluation methodology used and describe how Kenexis used the evaluation to develop a series of real-world use-cases of the components and system in the ICS environment.
Critical Infrastructure and Cybersecurity Transportation Sector

Workshop on Critical Transport Infrastructure and Cybersecurity - UNECE Working Party on Transport Trends and Economics
Pöyry ICS Cyber Security brochure (English)

A successful cyber attack on a plant’s Industrial Control Systems (ICS) can be catastrophic. It can impact the plant’s operations, finances, damage reputation and even threaten lives. A resilient cyber security programme is essential in order to mitigate against potential cyber attacks. To help ensure that your plant is fully prepared to defend against potential cyber attacks, we provide a range of ICS Cyber Security services, each customised for your plant’s unique requirements, based on the latest international cyber security standards and best practice. Pöyry is active in designing, assessing and supervising the implementation of ICS cyber security programmes to both operating and greenfield facilities.
CuSRF. OWASP AppSecUS 2014

The research for the CuSRF attack was done by my friend and colleague Mr. Tal Be'ery and Imperva's CTO Mr. Amichai Shulman.
The presentation covers the CuSRF attack vector in detail with examples of exploitation in several well known online services.
City Infrastructure Cybersecurity

“Posiblemente la ciberseguridad de las infraestructuras urbanas no ha tenido la atención que se merece: cuestiones como una planificación cortoplacista o restricciones económicas han puesto de relieve múltiples vulnerabilidades de gestión en los servicios básicos de la ciudad. Por ello se ha abierto una gran oportunidad para desplegar soluciones tecnológicas relacionadas con la ciberseguridad industrial que mejoran la seguridad de estas infraestructuras urbanas. Bajo este prisma hablaremos de dispositivos de campo, comunicaciones M2M, integridad y disponibilidad de datos… hasta llegar a las mismísimas plataformas que gestionan toda la información en tiempo real.”
SCADA Security Presentation

Presentation on the growing challenge of information security in critical infrastructures.
Symantec 2010 Critical Infrastructure Protection Study

Symantec 2010 Critical Information Infrastructure Protection (CIP) Survey found, among other things, that 53 percent of critical infrastructure providers report that their networks have experienced what they perceived as politically motivated cyber attacks. Participants claimed to have experienced such an attack on an average of 10 times in the past five years, incurring an average cost of $850,000 during a period of five years to their businesses.
Viewers also liked (20)
Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...

Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...
Cyber Security Threats to Industrial Control Systems

Cyber Security Threats to Industrial Control Systems
French acreditation process homologation 2010-01-19

French acreditation process homologation 2010-01-19
Cybersecurity Guide for the State of Washington Critical Infrastructure_9_2015

Cybersecurity Guide for the State of Washington Critical Infrastructure_9_2015
ISACA - China Cybersecurity Law Presentation - Kyle Lai - v3.2

ISACA - China Cybersecurity Law Presentation - Kyle Lai - v3.2
Hacking Critical Infrastructure Like You’re Not a N00b

Hacking Critical Infrastructure Like You’re Not a N00b
Cybersecurity: Critical Infrastructure Threats from Main Street to Wall Street

Cybersecurity: Critical Infrastructure Threats from Main Street to Wall Street
VIVA LA COMPLEJIDAD ! BIG DATA Y TECNOLOGÍA : ELEFANTES EN CIUDADES DE PORCE...

VIVA LA COMPLEJIDAD ! BIG DATA Y TECNOLOGÍA : ELEFANTES EN CIUDADES DE PORCE...
Evaluating System-Level Cyber Security vs. ANSI/ISA-62443-3-3

Evaluating System-Level Cyber Security vs. ANSI/ISA-62443-3-3
Critical Infrastructure and Cybersecurity Transportation Sector

Critical Infrastructure and Cybersecurity Transportation Sector
Industrial Cybersecurity and Critical Infrastructure Protection in Europe

Industrial Cybersecurity and Critical Infrastructure Protection in Europe
Symantec 2010 Critical Infrastructure Protection Study

Symantec 2010 Critical Infrastructure Protection Study
Similar to 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
INTERVIEW QUESTION FOR IT AUDITOR

Information technology is an essential component of any modern business;
therefore, many businesses or organizations hire IT Auditors. IT Auditors are
professionals who analyze a company’s systems to protect the firm’s information.
They guarantee that processes and systems operate correctly and efficiently while
being secure
Owasp top 10 & Web vulnerabilities

Brief of #OWASP top 10
#Hacking jargons
#hackers classification
#VAPT
#Web security overview
#vulnerabilities
#Importance of web security
#application attack
#network attack brief
Reveelium Smart Predictive Analytics - Datasheet EN

First European behavior analysis solution, capable of detecting weak signals and, ultimately, occurring anomalies within an information system. Reveelium can pinpoint with great precision security flaws that would, otherwise, remain unidentified.
Securing Industrial Control System

How securing ICS/SCADA/Critical Infrastructure is different from conventional Information Technology System.
3.8 Ways to Establish Secure Protocols in a Digital Organization.pdf

How to establish secure protocols in a digital organization? In recent years, massive cybercrimes have targeted businesses all around the world. Organizations are constantly subjected to security breaches, including data leaks, broken authentication, database hacking, malware infestations, and denial of service attacks on their networks, web applications, and servers.
https://itphobia.com/8-ways-to-establish-secure-protocols-in-a-digital-organization/
The Top Cloud Security Issues

There are many threats to cloud security. The main treats arise from account hijacking, data breaches, inadequate cloud security architecture and strategy, insecure interfaces and APIs, insider threats, limited visibility with regard to cloud usage etc.
12 IoT Cyber Security Threats to Avoid - CyberHive.pdf

As IoT (Internet of Things) devices weave into the fabric of our daily lives, from smart thermostats to connected cars, the need for robust IoT cyber security measures has never been more pressing. Let’s dive into 12 IoT cyber security threats that pose significant risks and offer guidance on navigating these digital waters safely. please visit: https://www.cyberhive.com/insights/12-iot-cyber-security-threats-to-avoid/
A talk on OWASP Top 10 by Mukunda Tamly

OWASP Top 10 by Mukunda Tamly, at null/OWASP Kolkata Meetup on 09 December 2023
Deep Dive into Operational Technology Security - USCSI®.pdf

Deep Dive into Operational Technology Security - USCSI®.pdfUnited States Cybersecurity Institute (USCSI®)
Become the best version of most in-demand cybersecurity experts with the best cybersecurity certifications to guide OT security frameworks. Foresee cybersecurity threats as a specialized OT security professional and gain big!
Read more: https://shorturl.at/jsuGSLinux Security best Practices with Fedora

These are the slides that I used for the "Linux Security best Practices with Fedora", one of my talks in FUDCon 2012 Kuala Lumpur.
8 Top Cybersecurity Tools.pdf

Top encryption tools like McAfee are popular among business users. McAfee provides full disk encryption for desktops, laptops, and servers. The algorithm uses Advanced Encryption Standard(AES) with 256-bit keys. McAfee AES is certified by US Federal Information Processing Standard. There is also ready integration of multi-layer authentication.
Module 3-cyber security

Ethical Hacking Concepts and Scopes, Threats and Attack Vectors, Information Assurance, Threat Modelling
Enterprise Information Security Architecture, Vulnerability
Assessment and Penetration Testing
Types of Social Engineering, Insider Attack, Preventing Insider
Threats, Social Engineering Targets and Defence Strategies
What Is Cyber Security? | Cyberroot Risk Advisory 

The technique of protecting networks, computers, servers, mobile devices, electronic systems, and data from hostile intrusions is known as cyber security
Similar to 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats (20)
Reveelium Smart Predictive Analytics - Datasheet EN

Reveelium Smart Predictive Analytics - Datasheet EN
3.8 Ways to Establish Secure Protocols in a Digital Organization.pdf

3.8 Ways to Establish Secure Protocols in a Digital Organization.pdf
12 IoT Cyber Security Threats to Avoid - CyberHive.pdf

12 IoT Cyber Security Threats to Avoid - CyberHive.pdf
Deep Dive into Operational Technology Security - USCSI®.pdf

Deep Dive into Operational Technology Security - USCSI®.pdf
Recently uploaded
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Recently uploaded (20)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
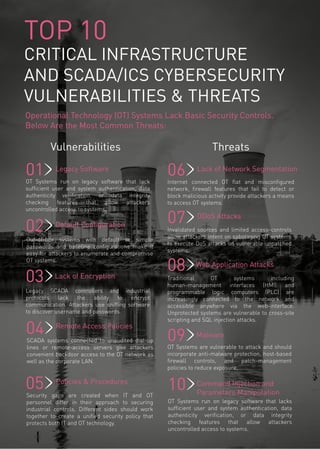
- 1. TOP 10 CRITICAL INFRASTRUCTURE AND SCADA/ICS CYBERSECURITY VULNERABILITIES & THREATS Operational Technology (OT) Systems Lack Basic Security Controls. Below Are the Most Common Threats: OT Systems are vulnerable to attack and should incorporate anti-malware protection, host-based firewall controls, and patch-management policies to reduce exposure. OT Systems run on legacy software that lack sufficient user and system authentication, data authenticity verification, or data integrity checking features that allow attackers uncontrolled access to systems. Legacy Software 01 02 DDoS Attacks Invalidated sources and limited access-controls allow attackers intent on sabotaging OT systems to execute DoS attacks on vulnerable unpatched systems. 03 Malware04 05 Lack of Encryption Legacy SCADA controllers and industrial protocols lack the ability to encrypt communication. Attackers use sniffing software to discover username and passwords. Lack of Network Segmentation 06Internet connected OT flat and misconfigured network, firewall features that fail to detect or block malicious activity provide attackers a means to access OT systems. 07 Policies & Procedures Security gaps are created when IT and OT personnel differ in their approach to securing industrial controls. Different sides should work together to create a unified security policy that protects both IT and OT technology. 08 Web Application Attacks Traditional OT systems including human-management interfaces (HMI) and programmable logic computers (PLC) are increasingly connected to the network and accessible anywhere via the web-interface. Unprotected systems are vulnerable to cross-site scripting and SQL injection attacks. 09 Remote Access Policies SCADA systems connected to unaudited dial-up lines or remote-access servers give attackers convenient backdoor access to the OT network as well as the corporate LAN. 10 Default Configuration Out-of-box systems with default or simple passwords and baseline configurations make it easy for attackers to enumerate and compromise OT systems. Vulnerabilities Threats OT Systems run on legacy software that lacks sufficient user and system authentication, data authenticity verification, or data integrity checking features that allow attackers uncontrolled access to systems. Command Injection and Parameters Manipulation
- 2. ©2016 Check Point Software Technologies Ltd. All rights reserved. January 2016 CONTACT US Worldwide Headquarters | 5 Ha’Solelim Street, Tel Aviv 67897, Israel | Tel: 972-3-753-4555 | Fax: 972-3-624-1100 | Email: info@checkpoint.com U.S. Headquarters | 959 Skyway Road, Suite 300, San Carlos, CA 94070 | Tel: 800-429-4391; 650-628-2000 | Fax: 650-654-4233 | www.checkpoint.com Industrial Control Systems (ICS) used in critical infrastructure and manufacturing industries are targets of sophisticated cyberattacks. The Check Point 1200R rugged appliance line delivers proven, integrated security for deployment in harsh environments as part of a complete end-to-end ICS security solution. WE SECURE THE FUTURE To learn more about Check Point’s Solutions for Critical Infrastructure, please visit www.checkpoint.com/products/industrial-control-systems-appliances
