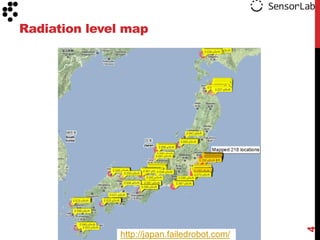
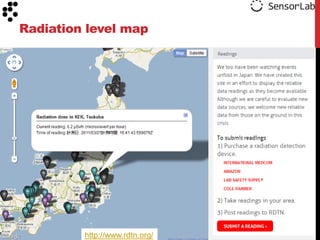
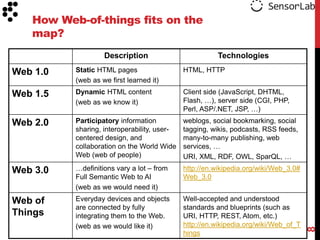
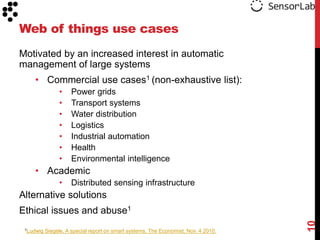
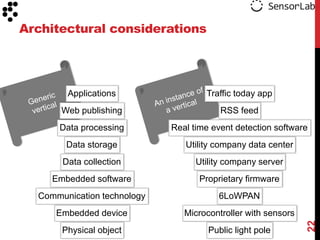
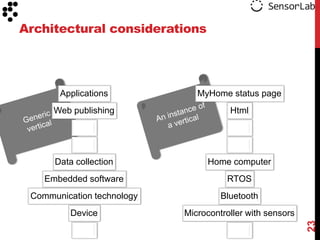
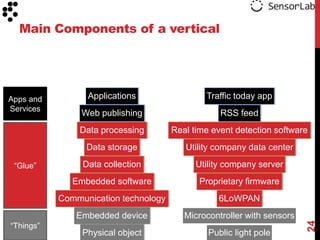
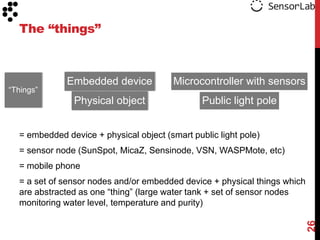
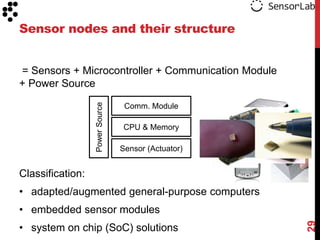
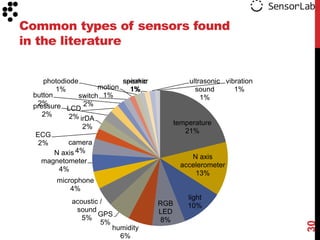
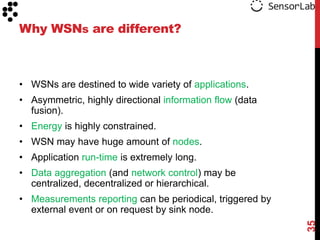
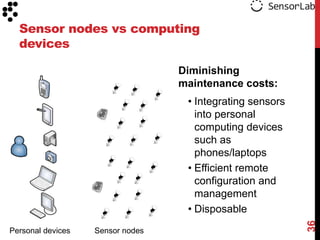
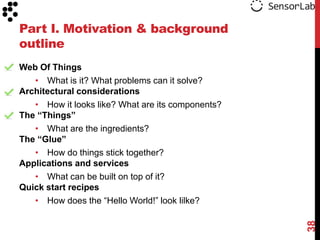
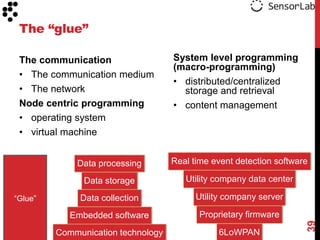
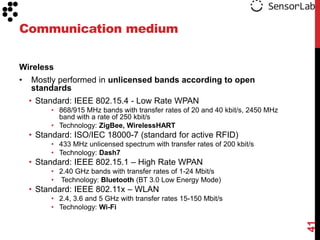
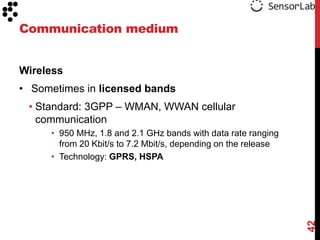
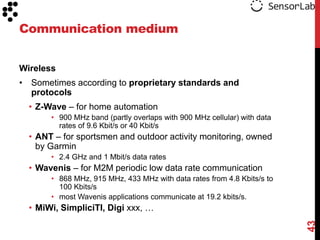
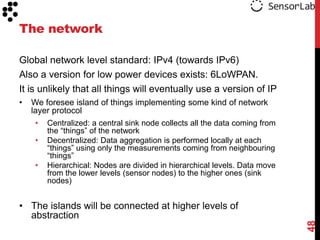
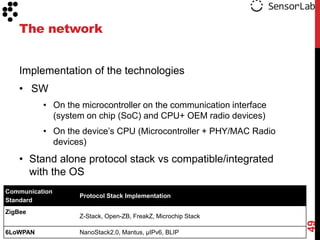
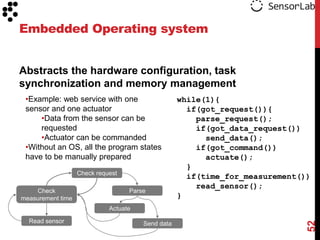
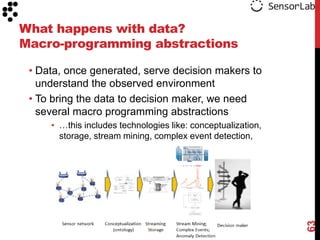
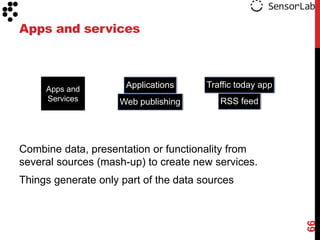
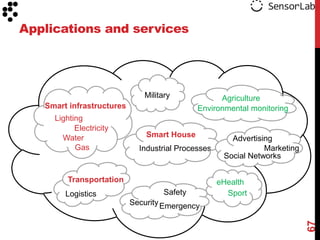
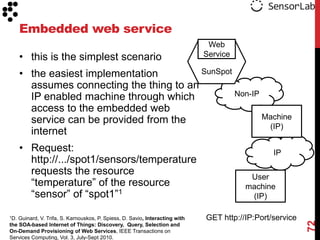
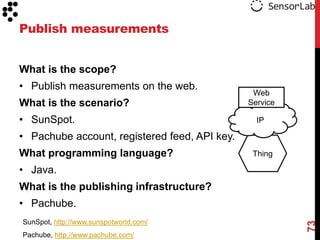
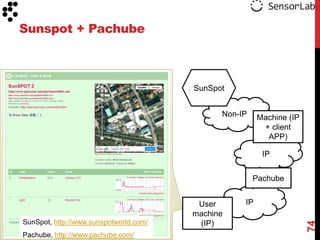
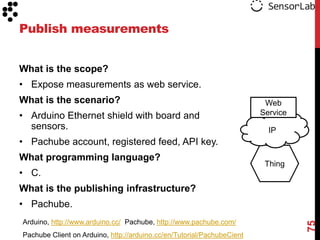
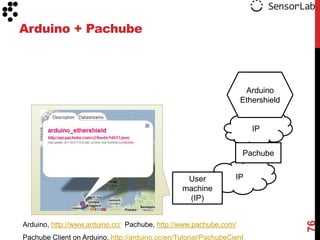
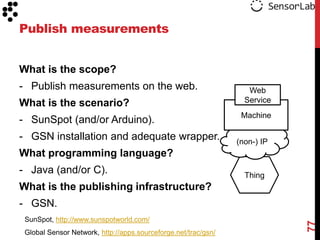
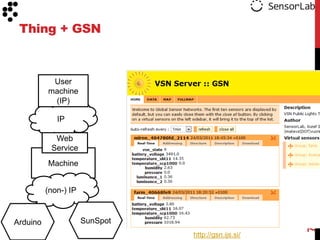
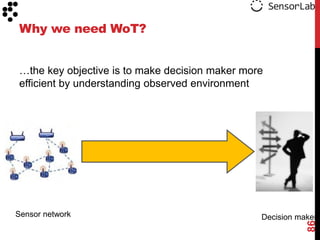
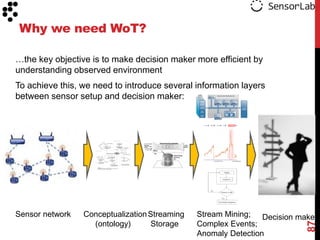
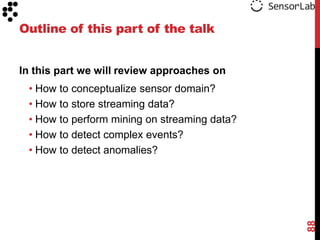
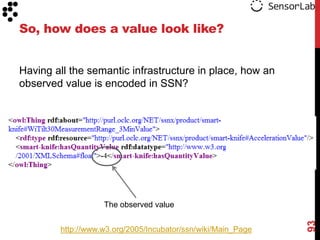
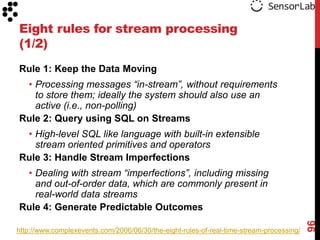
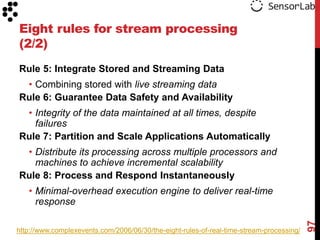
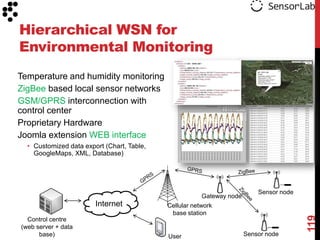
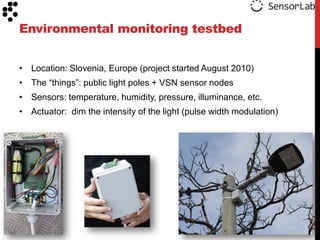
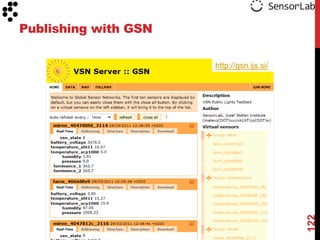
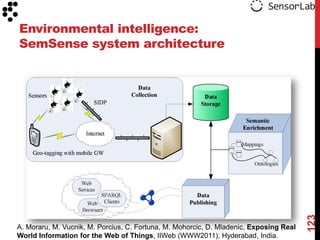
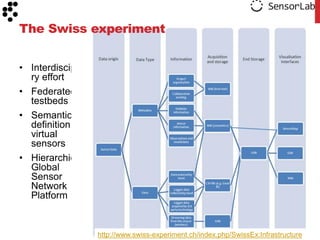
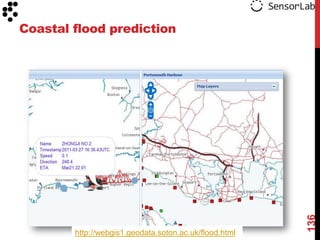
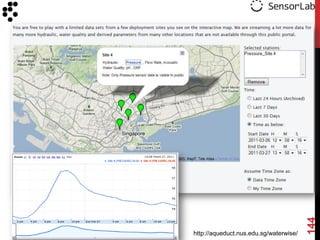
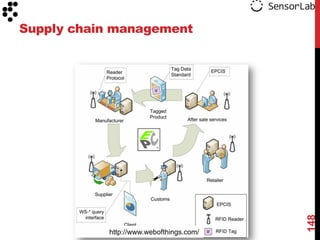
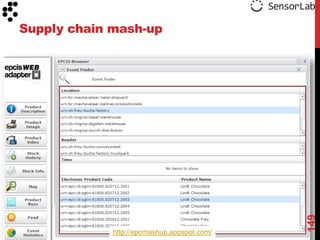
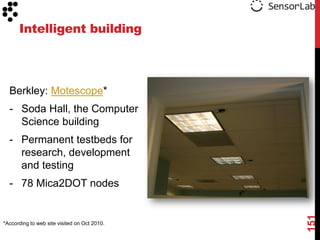
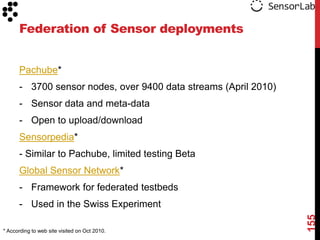
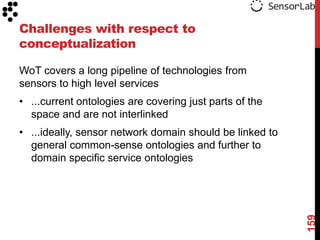
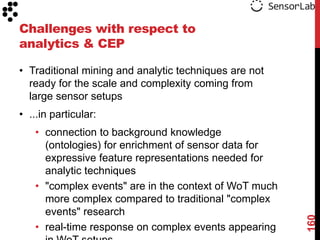
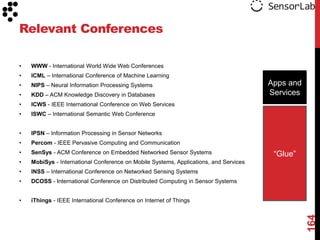
The document discusses the potential of a web of things (WoT) using sensor data. It provides examples of how a WoT was used after the 2011 Tōhoku earthquake and tsunami in Japan to share radiation level maps in real-time. The document outlines several potential commercial and academic uses of a WoT, including monitoring power grids, transportation systems, industrial automation, health, environment, and distributed sensor networks. It also discusses the main components, applications, and technologies that could enable a WoT, such as embedded devices, physical objects, communication standards, and data collection/processing services.