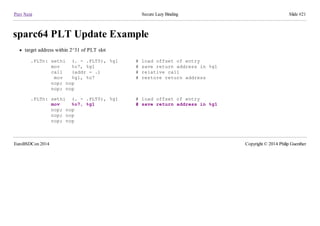
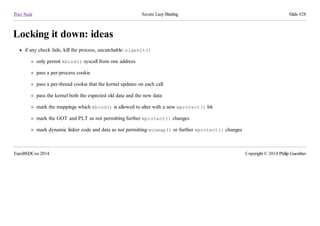
The document discusses secure lazy binding, a method in dynamic linking that defers symbol lookups until a function is first called, aiming to improve efficiency while minimizing vulnerabilities. It outlines various aspects of lazy binding, including its goals, implementation details for different architectures (amd64 and sparc64), and the costs associated with memory protection changes. The presentation ultimately suggests the use of a new system call, kbind, to enhance the security and performance of lazy binding in shared libraries.