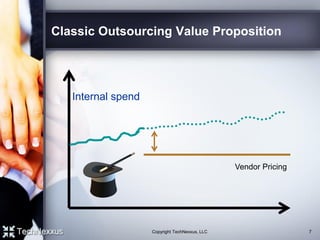
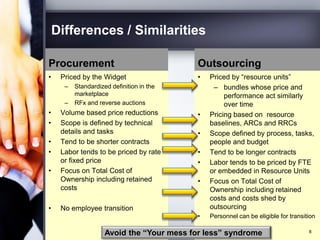
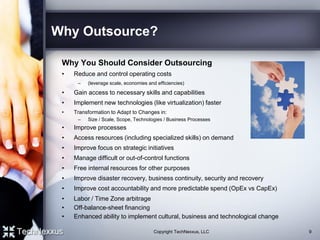
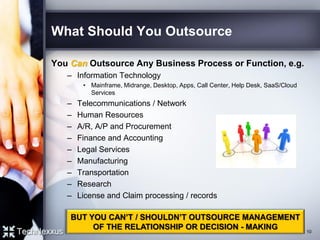
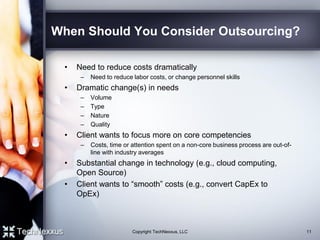
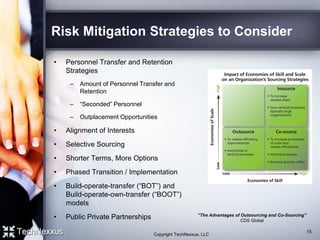
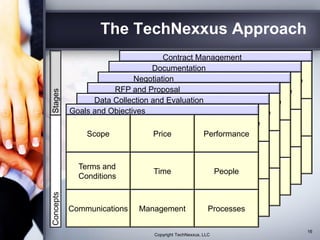
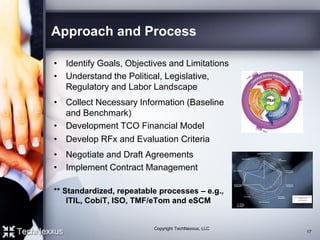
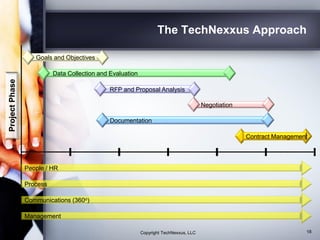
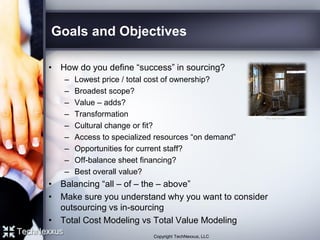
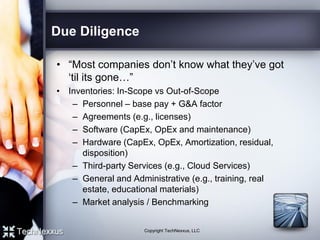
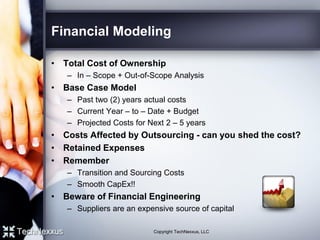
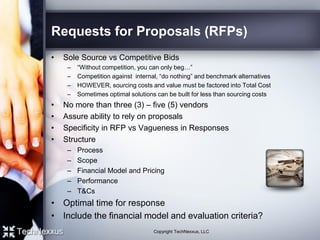
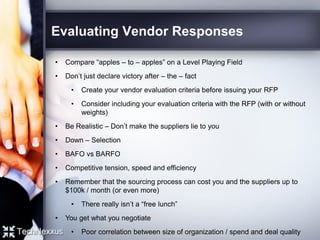
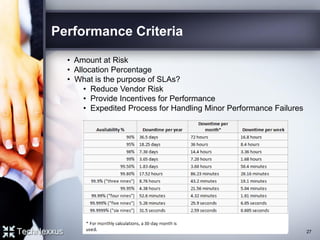
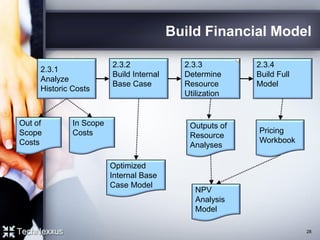
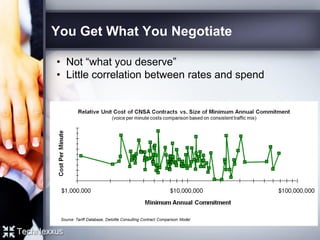
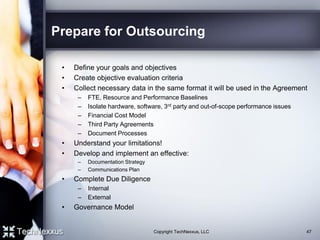
The document provides a comprehensive overview of outsourcing and strategic sourcing, highlighting definitions, advantages, disadvantages, and key success factors. It discusses when to consider outsourcing, what to outsource, and potential risks and errors to avoid, alongside strategies for financial modeling and vendor selection. The text emphasizes the importance of effective governance, communication, and preparation in achieving successful outsourcing outcomes.