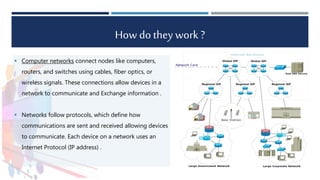
The presentation discusses computer networking, defined as the interconnection of multiple computers to share data and resources. It introduces Tech Link, an Egyptian company specializing in network solutions and services since 1997, and highlights its vision to be a premier provider in the Middle East and North Africa. Additionally, the document details Tech Link's partners such as Sophos, Grandstream, and Cisco Systems, showcasing the company's range of products and services, including network security and VoIP systems.